SearchBenny – a dubious site that claims to improve your time online by offering altered search results
 Search.searchbenny.com is the application powered by SearchBenny Software. This search engine might look like an entirely normal search website, but we do not recommend using it because of several different reasons. First of all, this website can replace your browser’s homepage without your consent.
Search.searchbenny.com is the application powered by SearchBenny Software. This search engine might look like an entirely normal search website, but we do not recommend using it because of several different reasons. First of all, this website can replace your browser’s homepage without your consent.
It means that the Search.searchbenny.com browser hijacker is capable of entering your system without a clear permission asked. Moreover, this search platform is NOT a safe search engine. Although it displays Yahoo search results, it does not mean that it is the real Yahoo search.
The program is not trustworthy, and anything related to SearchBenny can be considered malicious or potentially dangerous since the association with many thrid-party companies and commercial content creators. Make sure to ignore any of those redirects, pop-ups, banners, and other sites or layers that appear on the screen out of nowhere.
| Name | SearchBenny |
|---|---|
| Type | Browser hijacker/ mac virus[1] |
| Issues | The program triggers unwanted redirects, interferes with search results and affects the speed by opening pop-ups, banners with ads |
| Distribution | Freeware installations, deceptive sites, misleading content online triggers issues with direct PUP downloads. Also, pre-packed apps come when you skip through steps during the installation from random sources[2] |
| Elimination | SearchBenny mac removal process might get more difficult since AV tools are not common for these machines. Anti-malware scan is the best solution, but you can also try to find all the components manually with the help of the guide below |
| Tips for the system repair | To properly fix all the issues regarding the system damage, you need a tool that can possibly find, fix and repair any damaged files, affected programs or corrupted functions |
This bogus search site uses the Yahoo search outcomes and then supplements them with suspicious and misleading hyperlinks. Do not be deceived, because these Search.searchbenny.com search results can lead you to spam websites, which might promote questionable software.
Search.searchbenny.com redirects can end you up on dangerous web pages, and some of them can even be malicious. Remember that there is always a chance to infect your computer accidentally – even one click on an infected link can initiate the execution of malware.
So if you have noticed that the SearchBenny page has replaced your previous browser’s homepage, you should eliminate it from your system without a delay. For that, you can use a professional spyware removal program. The software that can easily detect computer parasites and threats and delete them from your system is the one for such programs.
When you rely on AV tools for processes like SearchBenny mac removal, you can quickly get back to a normal working device. So that is why most computer experts[3] recommend keeping the anti-malware tools on your system.
Searchbenny is the fake search engine that installs itself silently.
The issue with SearchBenny mac removal procedure
The biggest issue is the SearchBenny mac removal question because people still tend to believe that their devices based on Apple production cannot have malware issues of any sort. However, this is not the case, and some PUP developers aim for macOS machines with these shady tools, deceptive sites, and other dubious material.
Deceptive software installers assign various programs as extra pieces in bundles and deliver such packages via the web, by relying on pirating sites, torrent platforms, deceptive sites, shady software distribution sites. You can end up on such a misleading page without noticing and on install the PUP. Then you will need to perform the SearchBenny mac removal process.
Unfortunately, it is more common for potentially unwanted programs to spread on Windows-based machines, and it is easier to get a powerful anti-malware tool that eliminates all the components of the intruder and cleans the machine. However, it is possible to catch this PUP on macOS, so it is possible to get tools for SearchBenny mac removal. Also, remember to check the system for virus damage after virus termination and rely on trustworthy tools like Reimage Reimage Cleaner Intego.
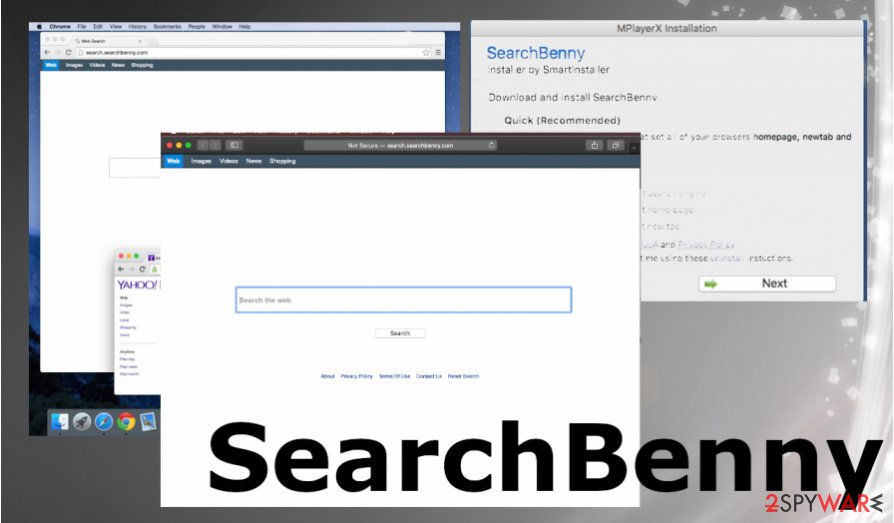
Search.searchbenny.com – the browser hijacker that claims to offer improved search results.
Hijacker distribution methods
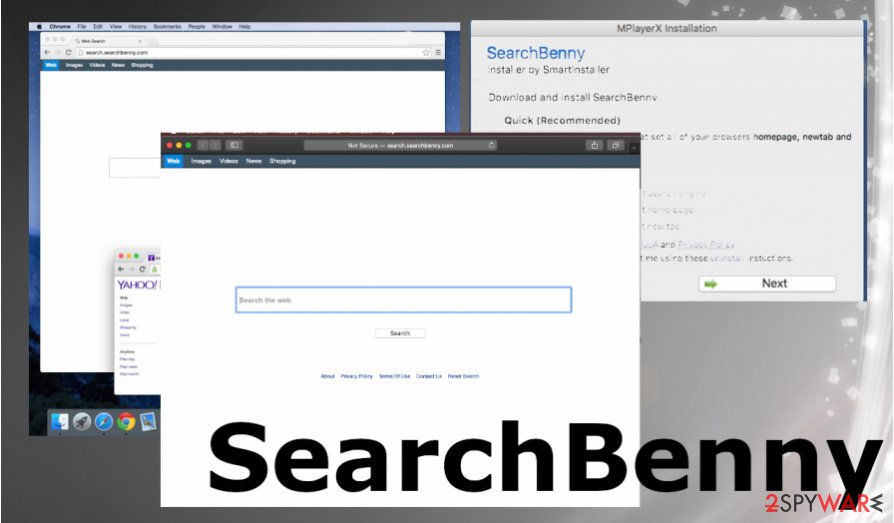
The shady search engine most likely took over your Internet browsers silently, if you have recently installed freeware or shareware without paying attention to the installation setup. Please remember that these PUPs can be spread seamlessly as an attachment to other free programs, so you have to be extremely attentive whenever you download and install new software on your PC.
The developers of freeware tend to use the bundling technique to spread their suspicious products, which allows them to pack several apps into a software bundle. The software bundle looks like a single program at first sight, and to find out whether it keeps additional attachments or not, you must review the installation settings.
So as you reach the Installation Settings step, opt out the Default/Standard installation mode and opt for Advanced/Custom one. After doing so, you should see another setup window that provides a list of additional software suggestions. Opt these suggestions out.
Ways to remove SearchBenny virus from various systems
To remove SearchBenny, you will need to uninstall Search.searchbenny.com PUP. If you want to do it manually, please follow our step-by-step guide that can be found below this article. However, for some inexperienced computer users, the manual removal technique might seem to be too difficult to apply.
In such a scenario, we recommend the automatic Search.searchbenny.com removal method that cleans the machine properly. PUP can be deleted automatically with one of our recommended spyware removal programs. AV engines can be compatible with pretty much any Windows version, so you can easily try a few programs for the PUP elimination and system repair.
As for the SearchBenny mac removal procedures, you should first remember that macOS devices are not immune to malware and can still catch intruders, get affected by these PUPs, malicious software. Attackers sometimes develop particular rogue tools compatible with macOS only.
You may remove virus damage with a help of Reimage Reimage Cleaner Intego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. It is a hassle when your website is protected from suspicious connections and unauthorized IP addresses.
The best solution for creating a tighter network could be a dedicated/fixed IP address. If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for server or network manager that need to monitor connections and activities. This is how you bypass some of the authentications factors and can remotely use your banking accounts without triggering suspicious with each login.
VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world. It is better to clock the access to your website from different IP addresses. So you can keep the project safe and secure when you have the dedicated IP address VPN and protected access to the content management system.
While much of the data can be accidentally deleted due to various circumstances, malware is also one of the main culprits that can cause loss of pictures, documents, videos, and other important files. Potentially unwanted programs may clear files that keep the application from running smoothly.
More serious malware infections lead to significant data loss when your documents, system files, or images get locked. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them. Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system.
In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.

