vCrypt1 ransomware – data locking malware that targets Russian-speaking computer users
vCrypt1 ransomware, also known as vCrypt ransomware, is a file locking virus that is considered to be a relatively primitive crypto-malware family, as it does not use any stealth techniques for the infiltration. Despite that, it can still be very effective, and several variants resurfaced since its discovery back in 2017. Researchers also believe that vCrypt virus authors are renting botnets in order to send phishing emails en masse.
In spring 2020, cybercriminals released new crypto-malware, which appended .vcrypt extension to files. However, this is a completely different malware that actually does not encrypt data but rather compresses it into archives, which is later locked with a password.
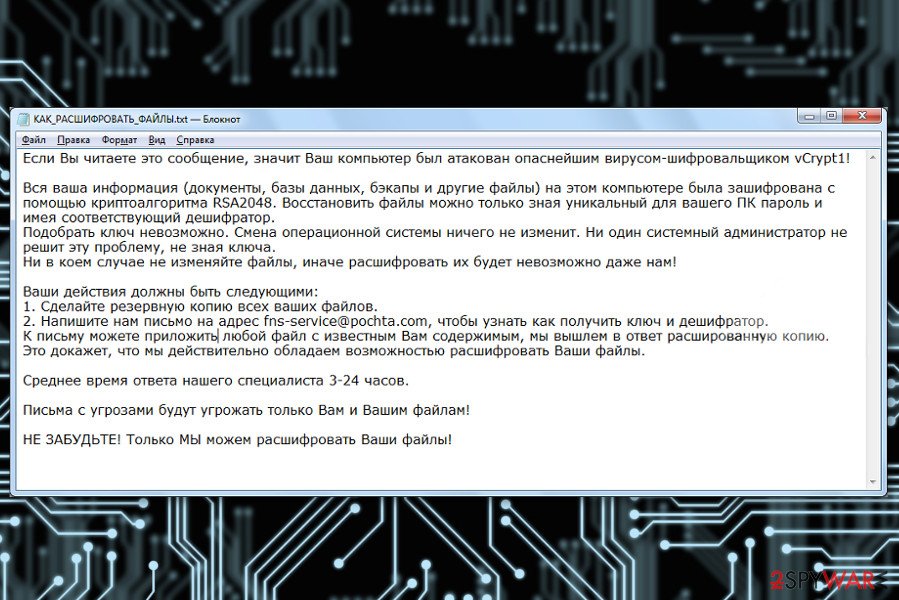
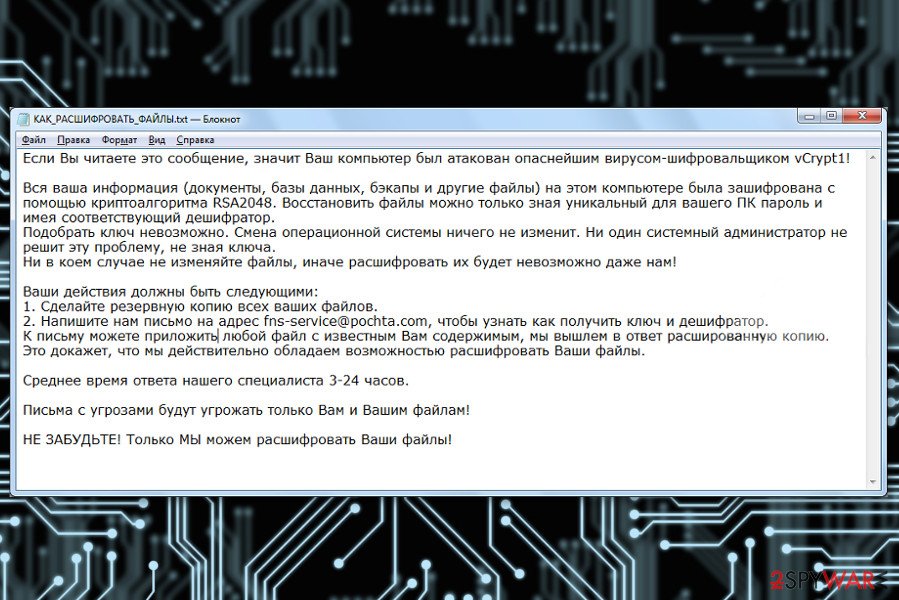
vCrypt1 ransomware uses XOR cipher to encrypt files,[1], although the attackers claim that the RSA-2048 encryption algorithm is used. Malware is designed to encrypt documents, databases, various images, audio, video, and other widely used files and appends a file extension to each – it varies based on the version (.vCrypt1, .aCrypt, .bCrypt, or .xcrypt). Additionally, vCrypt1 ransomware also drops a ransom note “КАК_РАСШИФРОВАТЬ_ФАЙЛЫ.txt,” which is written in Russian, which indicates that the attackers are Russian actors. The message claims that victims should email criminals via [email protected] to retrieve vCrypt1 ransomware decryptor – for a sum of money, of course.
| Name | vCrypt1 ransomware |
| Type | File locking virus, crypto-malware |
| Alternative name | vCrypt ransomware |
| Distribution | Malware is mainly delivered via spam email attachments or embedded links, although cybercriminals might employ other methods as well |
| Detection | Trojan.Ransom.vCrypt, HEUR:Trojan-Ransom.Win32.Encoder.gen, Ransom_VCRYPT.C, Ransom:Win32/Genasom, FileRepMalware and more on Virus Total |
| Encryption algorithm | XOR, although the attackers claim they are using RSA-2048 |
| File extension | .vCrypt1, .aCrypt, .bCrypt, or .xcrypt |
| Ransom note | КАК_РАСШИФРОВАТЬ_ФАЙЛЫ.txt (HOW_TO_DECODE_FILES.txt) |
| Removal | To terminate the infection, perform a full system scan with anti-malware software (in Safe Mode if required) |
| System fix | To remediate your computer after malware infection and prevent crashes, errors, as well as other stability issues, use Reimage Reimage Cleaner Intego |
As mentioned above, vCrypt1 ransomware developers mostly use malicious spam email attachments to deliver the payload to victims. However, other methods can also be used, which include:
- Exploits and vulnerabilities
- Weakly-protected Remote Desktop connections
- Fake updates
- Web injects
- Software cracks, etc.
Following data encryption, the malware drops a ransom note called, which translates as “HOW_TO_DECODE_FILES.txt. This ransom-demanding message is written in the Russian language, so vCrypt virus might be created to attack Russian-speaking computer users.
The ransom note provides misleading information about data encryption and reveals how users can get back access to them. There’s nothing new in ransomware business.[2] Victims are asked to contact cybercriminals and follow received instructions – email criminals via [email protected] and then transfer a particular sum of money (in Bitcoin or another cryptocurrency) and wait for the decryption software.
However, cybercriminals may not keep their promise and leave you without decryptor. Thus, we highly recommend focusing on vCrypt1 removal and thinking about recovery later. At the end of the article, you will find detailed instructions on how to delete the virus automatically by using professional software. Additionally, to recover the normal operation of Windows and prevent its reinstallation, employ the PC repair tool Reimage Reimage Cleaner Intego.
Crooks try their best to convince victims to send a message by saying that they are the only ones who have a decoder and can help. According to them, other attempts to restore files will end up with a failure or data loss. Hackers are also willing to give victims a guarantee that can actually decrypt data.

vCrypt1 ransomware virus encrypts files and demands to pay the ransom.

vCrypt1 ransomware virus encrypts files and demands to pay the ransom.
Thus, people can send one encrypted file, and hackers will provide a decrypted copy of it, as well as the price of decryptor and instructions on how to make the payment and use it. However, we do not recommend trusting these people.[3] Even if they can restore your files, they may not have intentions of doing it.
They may just take your money and never send decryption software. That’s why we suggest you remove vCrypt1 ransomware. It’s better to lose your files than experience a money loss too. Besides, if you backup your files regularly, you should not think about any other recovery option.
New ransomware Vcrypt does not encrypt files
As mentioned above, a new ransomware strain emerged in May 2020, which was called Vcrypt (mainly due to the extension that the malware appends to all files). This malware family, while called identically to vCrypt1 ransomware, is a completely different family, and its operation principles differ significantly – even from regular file locking viruses. First of all, it targets French users instead of Russian ones (it is also known that it spreads as video_driver.exe file that is placed to \AppData\Local\Temp location).
Secondly, Vcrypt ransomware does not encrypt files but rather places files into archives using the 7zip program. Additionally, not all data is encrypted, the malware particularly targets the following subfolders located in %Public% and %Userprofile% directories:
- Desktop
- Downloads
- Documents
- Pictures
- Videos
- Music
The ransom note “help.html” claims the following (translated from French):
Oooopppssss …
Q: What happened to my files?
A: All your files have been encrypted and placed in a security zone.Q: How to recover my documents !! ?
A: Follow the instructions available via this web page. If the page does not open, please check your internet connection.
As soon as the compressed folders are created, the original files are deleted from the system entirely and replaced with a fake copy of a file. For example, a “picture.jpg” would be turned into “picture.jpg.vcrypt” and, while the process imitates encryption, these are fake files that cannot be decoded. In this sense, the Vcrypt virus can be considered as a wiper – a type of ransomware that wipes out data from the targeted machines.
As usual, we do not recommend contacting the attackers or paying the ransom. Instead, remove Vcrypt ransomware from the computer and then proceed with alternative methods for data recovery we provide below.
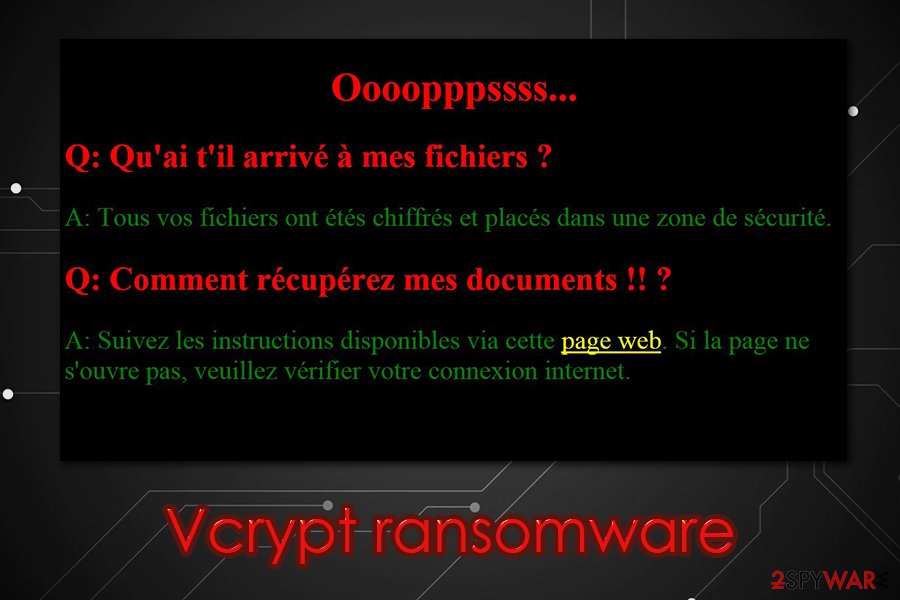
Vcrypt ransomware is a new malware that acts like a wiper – deletes files and places them into a password-protected archive
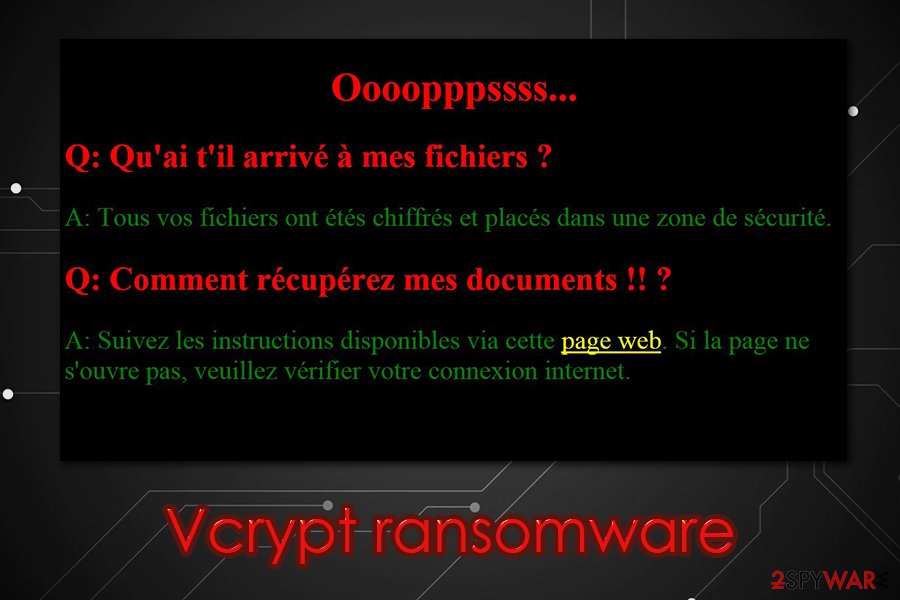
Vcrypt ransomware is a new malware that acts like a wiper – deletes files and places them into a password-protected archive
Ransomware spread using multiple distribution techniques
vCrypt1 ransomware might get inside the computer when a user clicks on malicious email attachment or link, downloads bogus software or update, visit a crafted site, or clicking on a malicious ad. The most common way to install malware payload is to open an infected document provided in a misleading email. Such kinds of emails might pretend to be sent from financial organizations, governmental institutions, or other well-known companies.
The attached document is often is an obfuscated Word or PDF document, so people are can easily be tricked that such a document cannot be harmful. Unfortunately, it’s not quite true. Thus, before opening the attached files, you should always make sure that it’s actually safe to open.[4]
vCrypt1 might also be hiding in P2P networks, Torrents, and various file sharing websites and pretend to be a legitimate program. Therefore, you should avoid downloading software from suspicious sources and do not install any programs or updates from ads. Usually, they are a part of the malvertising[5] campaign. As a result, you will install malicious payload instead of updates.
Terminate vCrypt1 ransomware virus effectively
vCrypt1 removal is performed using professional malware removal tools. We highly recommend scanning the device with one of these programs: SpyHunter 5Combo Cleaner or Malwarebytes. Of course, you can use any other preferred software. However, you should not forget to update your chosen software first. Besides, if you face some difficulties, for instance, cannot install a program, please have a look at our prepared instructions below. Indeed, malware can prevent from deleting it simply. Thus, by following the instructions, you will be able to disable the virus first and then remove vCrypt1 entirely.
Remove vCrypt1 using Safe Mode with Networking
Restart your computer to the Safe Mode with Networking in order to disable the virus. This step is necessary to install, update, or run an antivirus program.
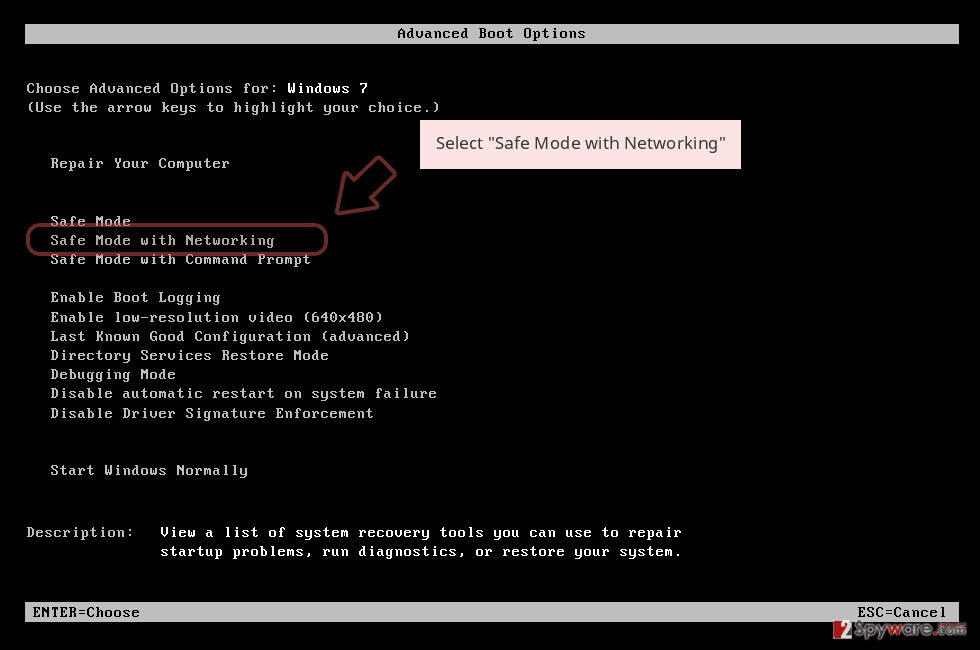
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
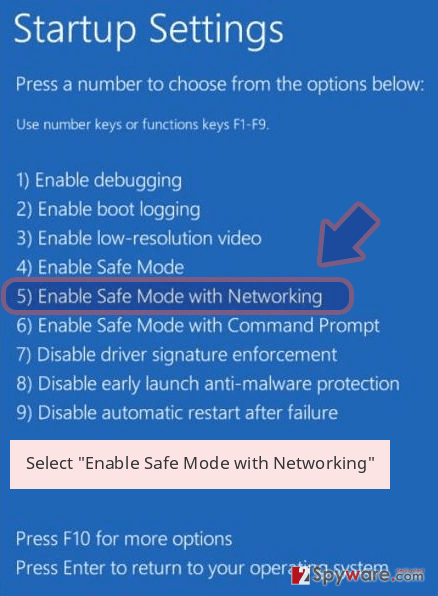
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete vCrypt1 removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove vCrypt1 using System Restore
If the previous method hasn’t helped to run automatic vCrypt1 removal, try System Restore method.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove vCrypt1 from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
Currently, data backups are the only option to restore encrypted files safely. Otherwise, you can try additional recovery methods. Hopefully, you will manage to rescue at least the most important files.
If your files are encrypted by vCrypt1, you can use several methods to restore them:
Data Recovery Pro – automatic way to restore files encrypted by vCrypt1 ransomware
It’s a simple to use tool which is designed to restore corrupted, deleted, and encrypted files.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by vCrypt1 ransomware;
- Restore them.
Windows Previous Versions feature might help to recover the most important files
Windows Previous Versions feature allows traveling back in time. However, this method is only helpful if System Restore function has been enabled before a ransomware attack.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be a helpful tool in data recovery
If vCrypt1 virus did not delete Shadow Volume Copies of the targeted file, follow the steps and use this tool to restore encrypted files:
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
vCrypt1 decryptor
We are sorry, but the official decryption software is not available yet.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from vCrypt1 and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-05-05 at 05:11 and is filed under Ransomware, Viruses.

