Tsar ransomware – a file locking virus that threatens to delete decryption key after five days
Tsar ransomware is a file locking virus which is also a variant of BlackHeart malware
Tsar ransomware is a file locking virus which is also a variant of BlackHeart malware
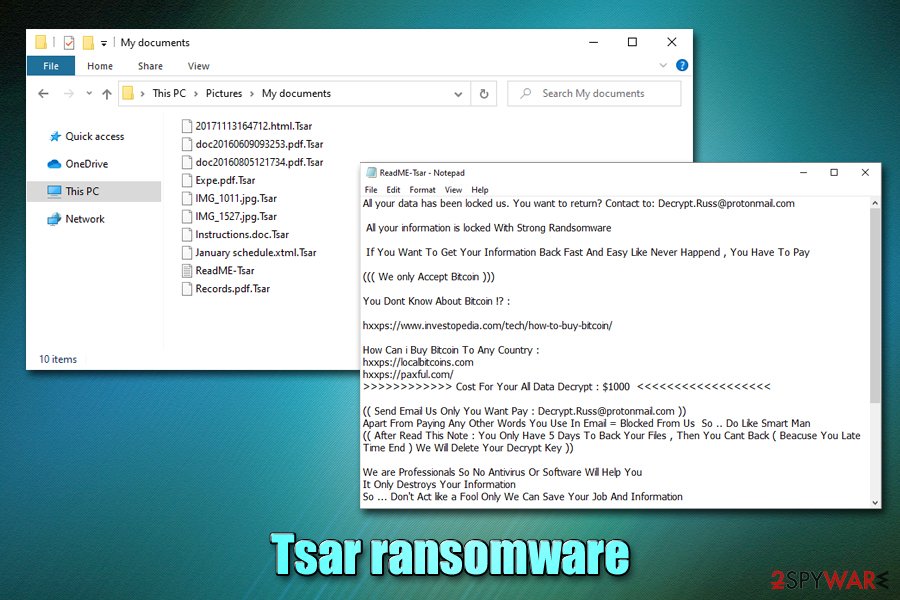
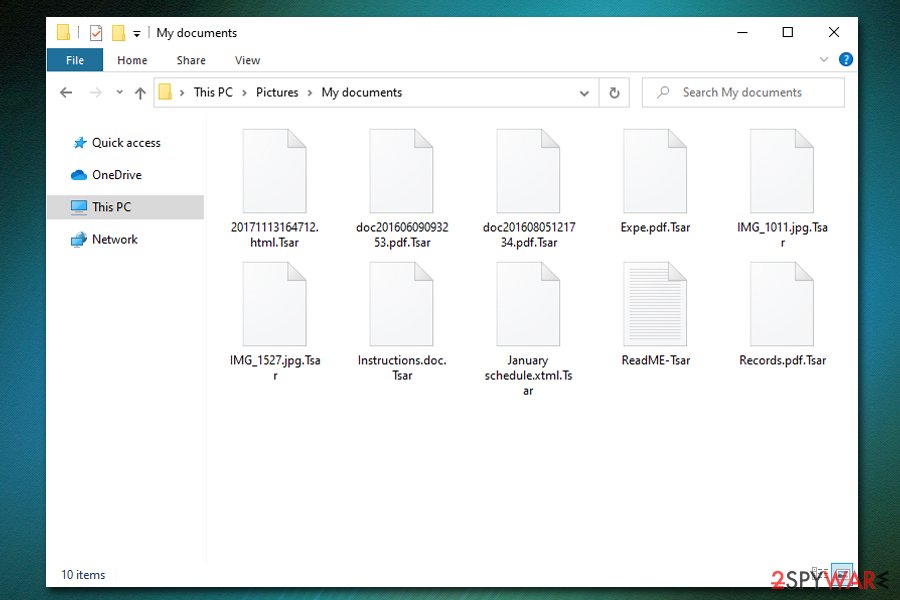
Tsar ransomware is a type of malware that focuses on money extortion from victims after encrypting all pictures, documents, videos, music, databases, and other files on the targeted computers. As pointed out by security researcher dnwls0719 on Twitter who first spotted the threat in the wild, it appends .Tsar extension to each of the files, and then drops “ReadME-Tsar.txt” ransom note on the desktop, as well as other folders on the system. Additionally, Tsar virus also shows a pop-up window – it claims that the data was locked with the combination of RSA, AES, and ChaCha20 algorithms[1] and that the only way to recover it is by paying the ransom of $1,000 in Bitcoin cryptocurrency.
Crooks behind Tsar ransomware claim that if they are not contacted via [email protected] or [email protected] emails within five days, the unique decryption key will be permanently deleted. While it is unclear whether such a scenario is plausible, paying threat actors is not recommended, and they might not send the required Tsar ransomware decryption tool.
| Name | Tsar ransomware |
| Type | File locking virus, crypro-malware |
| Family | BlackHeart ransomware |
| First spotted | The virus was first spotted by security researcher dnwls0719 in late February 2020 |
| File extension | Each of the files is appended with .tsar marker after the encryption process with AES is complete |
| Main executable | SF.exe |
| Ransom note | A pop-up window shows up upon file encryption completion – it includes a timer which, upon expiration, will double the ransom demand. Additionally, ReadME-Tsar.txt is also dropped on the desktop – it includes more details about the attack |
| Contact | [email protected] and [email protected] |
| Data decryption |
The only secure way to retrieve data without paying the attackers is using backups. If none are available other solutions include:
|
| Malware removal | To get rid of malware and all its components, scan your computer with anti-virus software such as SpyHunter 5Combo Cleaner or Malwarebytes. If unsuccessful, access Safe Mode with networking as explained in the instructions below |
| System fix | In case your Windows operating system starts crashing, lag, or suffer from other stability issues after malware elimination, use Reimage Reimage Cleaner to fix virus damage |
Tsar ransomware stems from the BlackHeart malware family, which was first spotted back in April 2018. While the strain is not extremely prevalent, the attackers released a few versions over the years, including BlackRouter, Prodecryptor, and a few others. Despite low prevalence, those infected with Tsar ransomware can suffer devastating consequences, as the encryption algorithm used is secure, and no known free decryption tools are currently available.
Tsar file virus targets Windows operating systems and uses a variety of methods to reach them. For example, the attackers might employ malicious spam email attachments/hyperlinks to deliver the payload, as well as exploits, fake updates, software cracks, and other ways. To protect yourself from ransomware infections in the future, check the tips in our malware distribution paragraph below.
Before performing the data locking process, the Tsar virus also modifies Windows in a variety of ways, e.g., deletes Shadow Volume Copies to prevent easy data recovery, modifies Windows registry for persistence, drops a variety of malicious files, disables certain processes and services, etc.
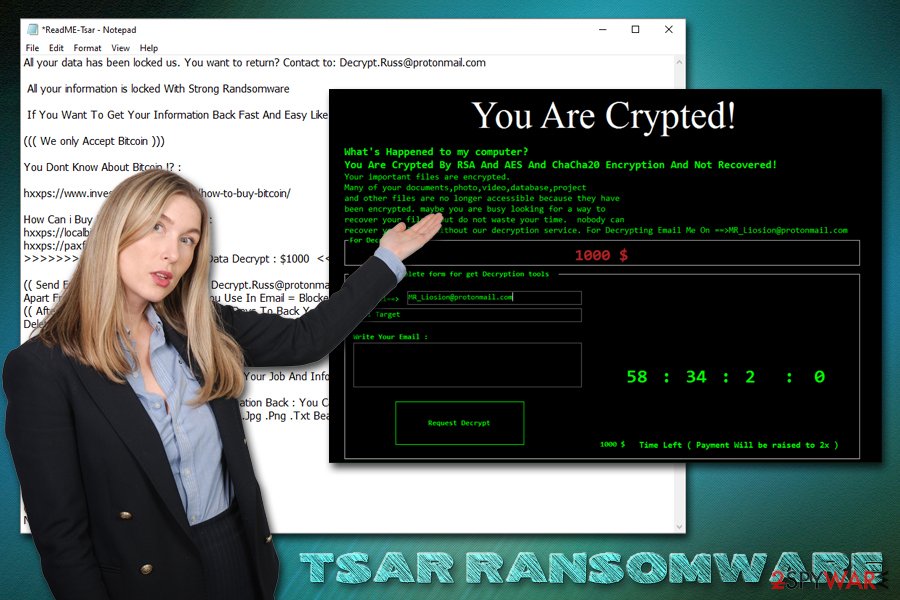
Tsar ransomware typically targets the most common file types, such as .doc, .jpg, .txt, .dat, .mp4, .html, and others, although it skips the most vital Windows system files for it to operate. After the data locking process, a pop-up message shows up immediately, which reads:
You Are Crypted!
What’s Happened to my computer?
You Are Crypted By RSA And AES And ChaCha20 Encryption And Not Recovered!
Your important files are encrypted.
Many of your documents,photo,video,database,project
and other files are no longer accessible because they have
been encrypted. maybe you are busy looking for a way to
recover your files, but do not waste your time. nobody can
recover your files without our decryption service. For Decrypting Email Me On ==>[email protected]
For Decrypt pay
1000 $Step 2: Complete form for get Decryption tools
My Email==>[email protected]
mail Target
Write Your Email:
Request Decrypt1000 $ Time Left ( Payment Will be raised to 2x )
While it is unknown whether the decryption tool will actually be deleted, many security experts recommend not trusting ransomware authors, as they might demand money after the first payment, or ignore the request completely. Instead, it is better to focus on the Tsar ransomware deletion process.
Tsar ransomware is crypto-malware that locks all personal files with a strong encryption algorithm and then asks for $1,000 in Bitcoin for the decryption software
Tsar ransomware is crypto-malware that locks all personal files with a strong encryption algorithm and then asks for $1,000 in Bitcoin for the decryption software
Most of the anti-malware solutions recognize the malicious executable SF.exe that populates the Tsar virus as follows:[2]
- Trojan-Ransom.FileCrypter
- Ransomware-GMZ!E6491ED91A5A
- Mal/Ramsil-T
- Ransom.Tsar
- Generic.Ransom.WCryG.256E2920
- Trojan:MSIL/Filecoder.DSK!MTB
- Win32:RansomX-gen [Ransom], etc.
It goes without saying that a comprehensive anti-malware can not only remove Tsar ransomware from the system but also protect it from its intrusion in the first place. As previously stated, there is no working decryption tool available, so the only safe method of data recovery is via backups.
Nevertheless, it is also important to mention that Tsar ransomware removal will not recover your data, as encryption is a separate process that occurs due to malware infection, but it is not reversible unless a unique key is acquired. Thus, simply backup locked files, get rid of malware with anti-virus software and only then try alternative recovery methods listed below. If your system suffered significant damage and Windows starts crashing or malfunctioning otherwise, use Reimage Reimage Cleaner repair tool to fix virus damage.
Apply comprehensive security measures to avoid ransomware infections
Ransomware is most definitely one of the most devastating malware types in the wild. It is not only dangerous for home users who might lose precious personal photos or work files but also disastrous for corporations, businesses, and local governments. While the spread of the threat and the popularity of it has been rising in the past years, cybercriminals are constantly coming up with new ways of making victims pay ransoms.
For example, major ransomware distributors behind Maze, Sodinokibi, DoppelPaymer, Nemty, and others are now threatening to publish stolen sensitive information from its victims.[3] Therefore, ransomware has huge implications, and the recovery process might be complicated (in some cases, data recovery might be completely impossible), so it is best not to get infected in the first place.
Security experts from Novirus.uk[4] advice users to practice these precautionary measures in order to reduce the infection chances to a minimum:
- Employ next-gen security software with machine-learning and other advanced features that can prevent ransomware from entering;
- Update your operating system and all the installed apps as soon as security patches are deployed;
- Never download software cracks/keygens or pirated program installers;
- Do not allow an attachment acquired via a suspicious email to run macro commands (“Allow content”) on your system;
- Enable anti-spam and anti-phishing tools, as well as ad-blocking extension;
- Protect all your accounts with secure alphanumeric passwords or use a password manager;
- Never use default TCP port for your Remote Desktop connections and disable the feature as soon as it is not used anymore.
Additionally, make sure you backup all your most important files on a cloud or an external storage device such as USB/external HDD.
Unfortunately, once Tsar ransomware performs the encryption process, recovering data without having backups is difficult
Unfortunately, once Tsar ransomware performs the encryption process, recovering data without having backups is difficult
Delete Tsar ransomware securely
In many cases, users who get infected with ransomware do not know how to proceed next, and whether their files can be saved. Because the Tsar virus does not have a working decryption tool, recovering data without paying criminals is highly unlikely, although not impossible. Therefore, you should remove Tsar ransomware and then try applying alternative methods we provide below; maybe ransomware failed to delete Shadow Volume Copies, and you will be able to retrieve everything with ShadowExplorer.
Nevertheless, before you perform Tsar ransomware removal, you should copy over all the encrypted data, as malware termination might permanently damage your data, and even threat actors will not be able to help you. For that, employ anti-malware software – scan your computer in Safe Mode if the normal mode does not suffice. Note that while there are many AV engines that detect the threat, not every anti-malware will be able to terminate the virus, so you might have to employ several removal tools.
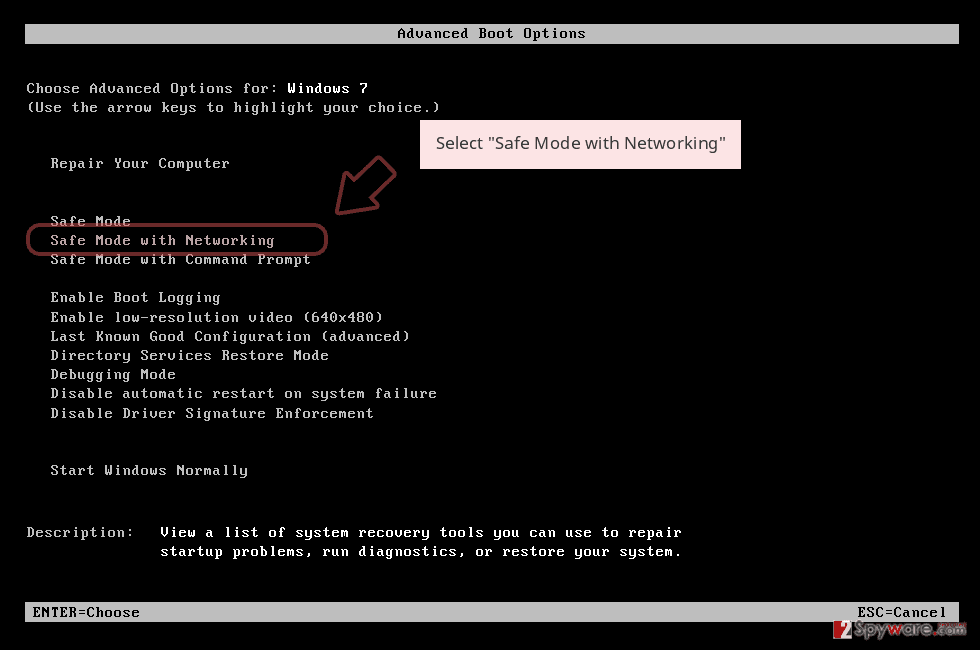
Remove Tsar using Safe Mode with Networking
In case of Tsar ransomware is tampering with your security software, access Safe Mode with networking as explained below:
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
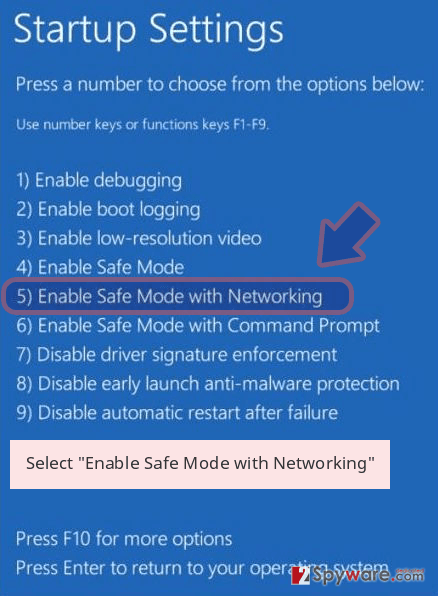
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Tsar removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Tsar using System Restore
System Restore can also be used when trying to get rid of the infection:
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Tsar from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by Tsar, you can use several methods to restore them:
Data Recovery Pro method may be successful in some cases
Data recovery software may sometimes be effective, as it may be able to extract working copies of some of your files on the hard drive.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Tsar ransomware;
- Restore them.
Previous Windows Versions feature can help you with individual files
This method can only be used on files one-by-one, and only works if the System Restore point was established before ransomware struck.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer method might suffice
In case of Tsar file virus failed to get rid of Shadow Volume Copies, this still should be able to retrieve most, if not all, of your files.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption software is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Tsar and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-03-03 at 07:01 and is filed under Ransomware, Viruses.

