Satan Cryptor – dangerous virus that promises to delete personal files if the victim fails to pay a ransom
there are numerous versions of Satan Ransomware and the number will keep increasing
Satan ransomware is a crypto-virus which operates as Ransomware-as-a-service.[1] Alternatively, it is also known as Satan Cryptor and Satan Cryptor 2.0 which came back in 2020. Malware is spread via Server Message Block (SMB) exploit that was used by a scandalous Wannacry attack. However, it is still unknown if Satan Cryptor is related to the previously-released ransomware that was presented in the underground market[2].
| SUMMARY | |
| Name | Satan Cryptor/Satan/Satan Cryptor 2.0 |
|---|---|
| Type | Ransomware/crypto virus/malware |
| Extension | .satan file extension |
| Ransom note | The virus is using HELP_DECRYPT_FILES.html and # SATAN CRYPTOR #.hta files to warn the victim about the encrypted data |
| Danger Level | High. Encrypted files are unusable, the victim is demanded to pay a ransom |
| Targets users in | Korea, China and USA |
| Distribution | SMB exploit, spam emails, malicious websites |
| Elimination | Fully scan your system with SpyHunter 5Combo Cleaner or Malwarebytes. Manual removal not recommended. Virus damage can be fixed with Reimage Reimage Cleaner |
This crypto-malware appends .satan extension and drops the HELP_DECRYPT_FILES.html or similar file as the ransom note. Originally, Satan Cryptor required 0.5 BTC to be paid as the ransom. However, it seems like the amount of ransom decreased with the latest version, demanding 0.3 Bitcoin. The biggest chances to get infected is if you live in USA, China and Korea.
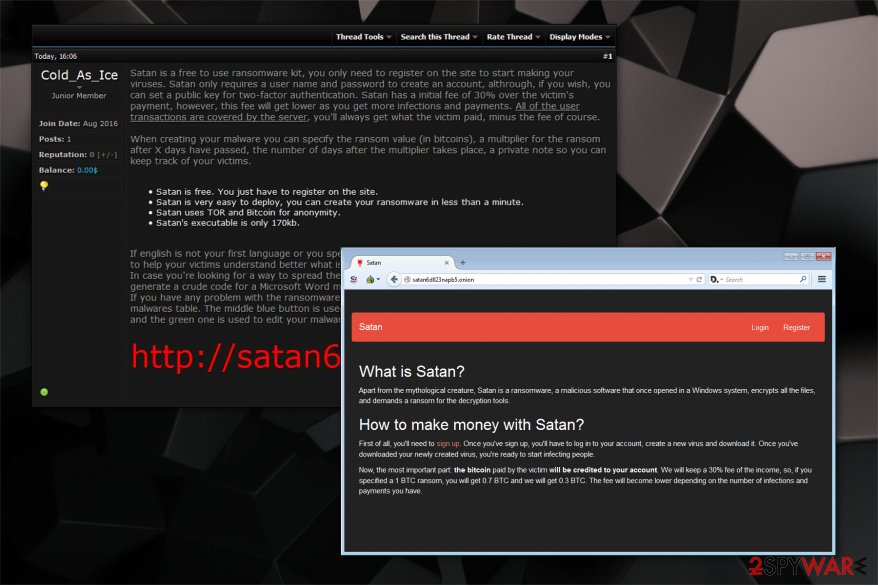
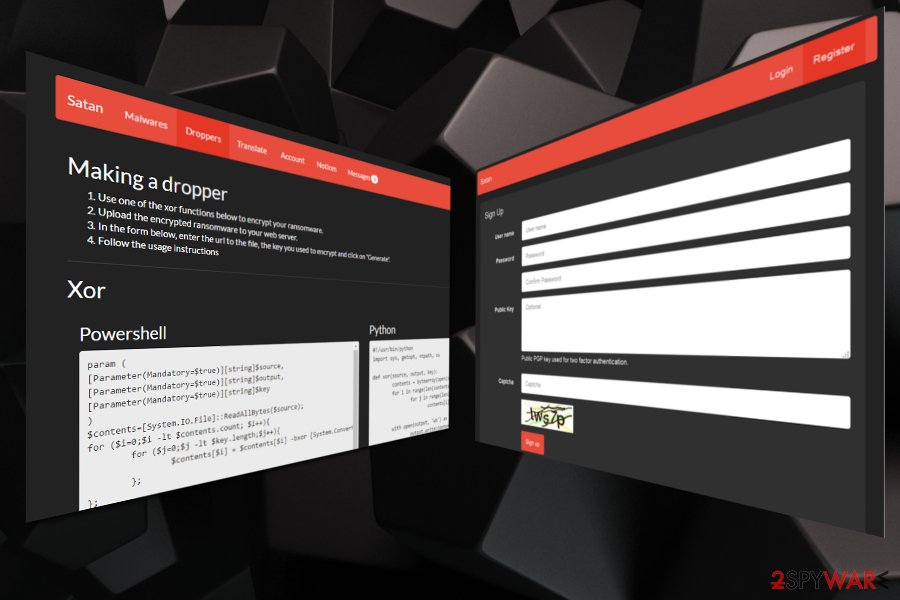
Previously, crooks were offered to design their own Satan ransomware and start generating illegal profits from this hazard. They were encouraged to sign up and create their individual file-encrypting variants of ransomware. The malware creation procedure consisted of the following parts:
- Malwares;
- Droppers;
- Translate;
- Account;
- Notices;
- Messages.
Malware allowed its users to specify their ransomware settings. They were allowed to set the amount of the ransom, indicate how much it should increase and the period of time after which it should happen. Once the user finished completing this page, it was allowed to create malicious MS Office macros or CHM installers in the Dropper section which were used to distribute Satan Cryptor.

Satan ransomware is offered as a service and its developers take 30% of the obtained profits.
Satan Cryptor ransomware has also been spread in multiple languages. Once inside the system, it starts displaying such warning message:
Payment Time Left: XXXX
Some files have been encrypted
Please send 0.5 bitcoins to this wallet address: XXXX
If you paid, send the machine code to my email address
I will of give you key
If there is no payment within three days,
we will no longer provide a decryption support
We can give you the test file.
send 3 files that are smaller than 3 MB to my email address
Btc Wallet: [1BEDcx8n4PdydUNC4gcwLSbUCVksJSMuo8]
Mail Address: [[email protected]]
Note that there could be numerous versions of Satan Cryptor and the number will keep increasing until people agree to pay the ransom. The developers of the file-encrypting virus promise to reduce their cut when the infection rate increases. It is clear that crooks are motivated to spread ransomware in order to gain a larger profit share.
Therefore, we recommend you to remove Satan Cryptor and do not pay the ransom under any circumstances. You should be aware that there are several reports on the Internet which inform that the decryption tool is ineffective and it is useless to spend such enormous amounts of money.
Be aware that Reimage Reimage Cleaner is the best option to complete Satan Cryptor removal for the regular computer user. Do not hesitate to do that since we also provide you alternative recovery methods at the end of this article to help recover data after ransomware attack.
Satan ransomware returns in 2020
Malware analyst Bart published a tweet[3] regarding recent recurrence of Satan Cryptor. The new variant of the virus kills database-related processes and attempts to stop SQL-related[4] services.
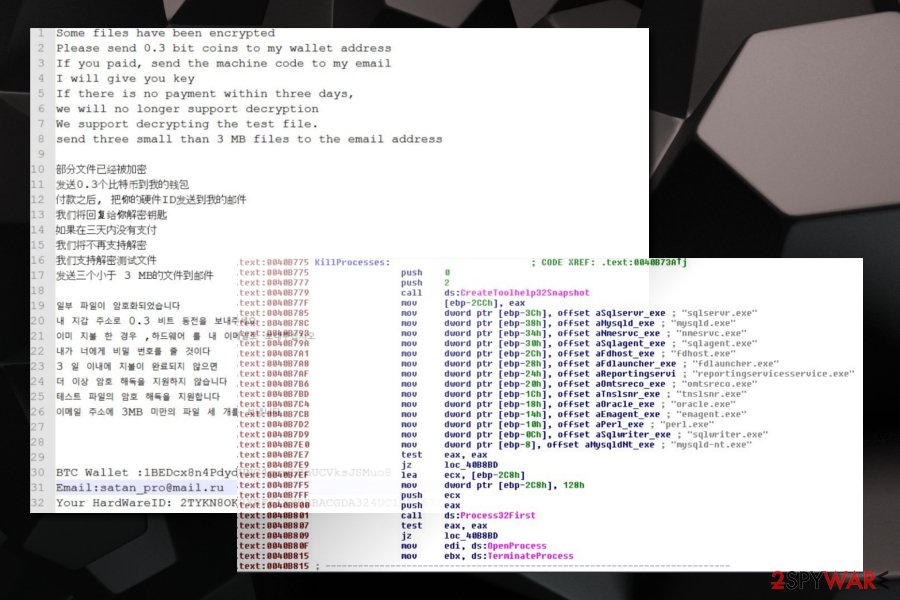
It seems like the extension applied to each of the infected files remains the same – .satan. The ransom note is also very similar to previous versions and is displayed in three different languages – English, Chinese and Korean. However, the amount of demanded ransom changed, which stands at 0.3 BTC.
Hackers are also accepting a personal file that can be sent to them, so they can show that decryption is possible. However, differently for its predecessors, Satan Cryptor does not provide support for the decryption after three days of infection. It seems like crooks are trying to speed up the process by using scare tactics.
However, you should never get tricked into paying cybercriminals, regardless of how scary the situation might seem. There is no guarantee you will get your files back, and you will also be promoting illegal activities by supporting hackers.
Ransomware can be distributed in various ways
Computer hazards are distributed via multiple techniques to help infect as many computers as possible. The most widely used ones are malicious emails and obfuscate software updates. Both of them possess a deceptive appearance which tricks gullible people to open bogus files and install ransomware.
Users should be aware of the hidden dangers in spam emails. Usually, they hold a malicious attachment of the executable which infects the computer once clicked. Hackers impersonate invoices or job spot responses from famous companies or even governmental authorities. Thus, do not open suspicious emails despite how genuine they may look. You should check some phishing email examples online so that you would be able to spot suspicious emails straight away.
Additionally, it is common to place ransomware as obfuscate software updaters which might pop-up during browsing sessions. Note that the false alerts to fix problems related to Adobe Flash Player might be merely an attempt to lure you into downloading ransomware[5].
Satan malware ransom note
You should remove Satan ransomware without a delay
Since Satan ransomware has been offered as a ransomware kit which allowed creating customized versions of it, regular computer users might not be able to detect all components of the malware and fail to terminate it. Also, in some cases, it is possible to damage your computer system permanently when trying to get rid of this high-risk computer infection.
Therefore, Satan Cryptor removal is only possible with the help of a certified IT technician or a profession security software. Note that it is vital to make sure that the antivirus tool is reputable and powerful enough to identify and eliminate this dangerous computer hazard.
You can remove Satan Cryptor ransomware with SpyHunter 5Combo Cleaner or Malwarebytes. Experts from LosVirus.es[6] assure you that these security programs are robust and able to terminate the ransomware within several minutes. Also, don’t forget to use the guide below which will help you to recover corrupted data. The easiest way – using Reimage Reimage Cleaner
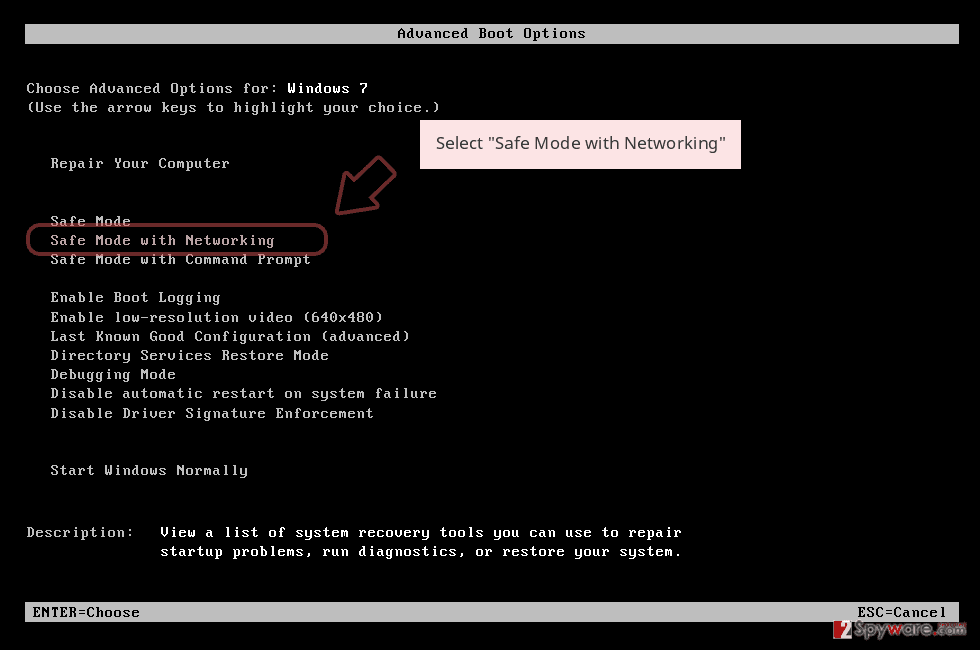
Remove Satan Ransomware using Safe Mode with Networking
To start Satan elimination, you must boot your computer into Safe Mode:
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
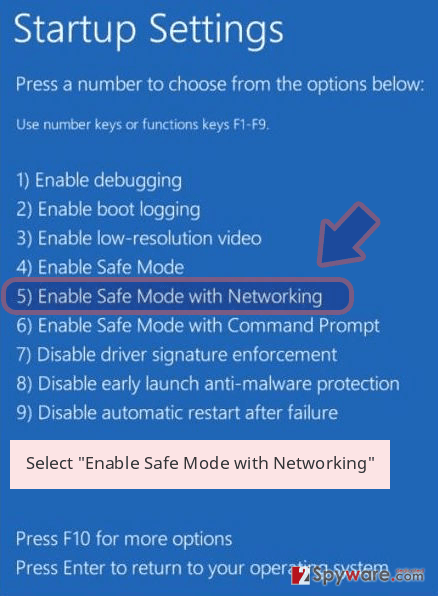
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Satan Ransomware removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Satan Ransomware using System Restore
Below you will find another method how to reboot PC to Safe Mode if the first one didn’t help.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Satan Ransomware from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by Satan Ransomware, you can use several methods to restore them:
Experts recommend Data Recovery Pro
This is a great tool to recover files after encryption and also you can use it when you have accidentally deleted important data.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Satan Ransomware ransomware;
- Restore them.
Use Windows Previous Versions feature
If you are a Windows user, it is advised to try the function which restores data from its previous versions. However, to use it, you must be sure that System Restore was enabled before Satan attack.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is another effective software
This program is based on the Shadow Volume Copies which are present on every PC. However, some types of ransomware are able to delete them. In this case, you would be unable to use this software.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Satan decryption tool is not available, use backups
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Satan Ransomware and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-01-13 at 04:53 and is filed under Ransomware, Viruses.

