Ryuk – ransomware, actively targeting large organizations all over the world
Ryuk is a ransomware virus[1] that, since August 2018, has already attacked and encrypted data from several companies, data centers, and PCs. According to numerous speculations, the virus is hailing from the same family as Hermes ransomware which is attributed by an infamous Lazarus group. Recently, it shocked cyber security experts after they found out that the malware can misuse the Wake-on-Lan feature to turn the computer on and increase the amount of infected devices on the network.
After Ryuk ransomware encrypts systematically selected data, it generates a RyukReadMe.txt ransom note with the ransom fee that varies from 15 BTC to 50 BTC, depending on the amount of encrypted data via the provided Bitcoin wallet.[2] Ryuk ransomware returned to the headlines after performing several attacks during the Christmas time, including the DataResolution.net cloud hosting provider.[3] This new version has been named RYK ransomware due to the file extension appended. However, note that alternative it has been called as Cryptor2.0.
| Name | Ryuk |
|---|---|
| Also known as | Cryptor 2.0, RYK ransomware |
| Category | Ransomware/cryptovirus/malware |
| estimated income | Around $3.7 million |
| Encryption algorithms | AES-256; RSA-4096 |
| Ransom notes | RyukReadMe.txt, UNIQUE_ID_DO_NOT_REMOVE.txt, ReadMe.txt |
| Ransom amount | 15 – 50 BTC |
| Related files | horrible.exe, kIUAm.exe |
| Email addresses used for contacting | |
| Blocked services | Acronis VSS Provider, Sophos-related services, Veeam backup service, MBAM service, McAfeeEngine service, etc. |
| Decryptable | No |
| Elimination | Download anti-malware and run a full system scan. After Ryuk removal, follow the guide on how to decrypt encrypted files (at the end of the post) |
According to the latest news reports, Ryuk ransomware is still rapidly spreading throughout the Internet sphere and infecting users worldwide. The Federal Bureau of Investigation, also known as FBI, has made a research and found out that this cyber threat has launched dangerous attacks on more than 100 different types of businesses in The United States of America.[4]
Additionally, all of this took place starting from August 2018 until the middle of May 2019. This is a very big number of infected companies throughout such period of time. Experts think that the reason why Ryuk ransomware has been so successful is that it also delivers other destructive viruses such as TrickBot and Emotet. The variety of suffered organizations is wide, such as logistics companies, technology-based manufactures, and similar.
Researchers are still working on getting more knowledge about Ryuk ransomware distribution means. However, it has been speculated that it is distributed in the form of phishing email attachment which typically presents itself as an invoice, business report, etc. Additionally, hackers are likely to abuse insufficiently protected RDP[5] configurations to attack targeted companies.
To run on the computer, Ryuk malware needs to gain admin privileges. Therefore, each of the attacks needs to be carefully planned, credentials gathered, network mapped, etc. This led researchers from Check Point to believe[6] that the infection is carefully engineered by sophisticated hackers who are experienced in targeted attacks. According to Check Point experts, the malware has extreme similarities to Hermes 2.1 ransomware which belongs to the infamous Lazarus group who were formerly associated with the North Korean army.

Ryuk ransomware tends to attack both – regular users and high-profile organizations
The latest virus version, Cryptor2.0, hits Data Resolution and Tribune Publishing
After staying still for some time, the new version of Ryuk ransomware hit again during the Holiday 2018. Experts encountered the rise of its activity on December 24 and December 27. The first campaign was held on Data Resolution when ransomware gave control of the important data to the attacker. The data center domain was accessible until the company shut down the whole network. According to Data Resolution, no user data was accessed or compromised. The main purpose of this ransomware was to hijack the network not to steal the credentials.
On December 27, 2018, Ryuk hit Tribune Publishing newsprint organizations and disabled their ability to print papers. The incident was discovered late at night when one editor could not send finished pages to the printing service. The issue was quickly fixed and no more damage discovered on the network.
It is obvious that Ryuk ransomware is still active. According to the latest reports, both Data Resolution and Tribune Publishing were affected by Cryptor2.0 which is considered to be the newest variant of Ryuk virus. Once installed, this cyber threat encrypts files and marks them with the .RYK appendix. Additionally, it displays a ransom note explaining all conditions needed to get the decryption tool.
According to the note, victims are given a chance to recover two files for free, however, for the other ones, the users need to be a particular price. All details need to be discussed by email. Moreover, the criminals hiding behind Ryuk threaten users not to reset, shut down the computer, or delete any files because all data will be permanently deleted.
Cryptor 2.0 – another version of Ryuk ransomware virus
The functionality of the malware
Before infecting the device, Ryuk ransomware shuts down 180 services and more than 40 processes that are running on the system. The malware executes taskkill and net stop command on a predetermined list of processes and services.
The Ryuk virus then uses the kIUAm.exe executable file which is launched once the victim reboots the system. Right after that, it encrypts victim’s data, e.g., business documents, reports, photos, videos, databases, and other personal information with the specific file extension using the combination of RSA-4096 and AES-256 encryption algorithms.
Upon successful encryption, the virus generates ransom notes named RyukReadMe.txt and UNIQUE_ID_DO_NOT_REMOVE.txt. They read the following:
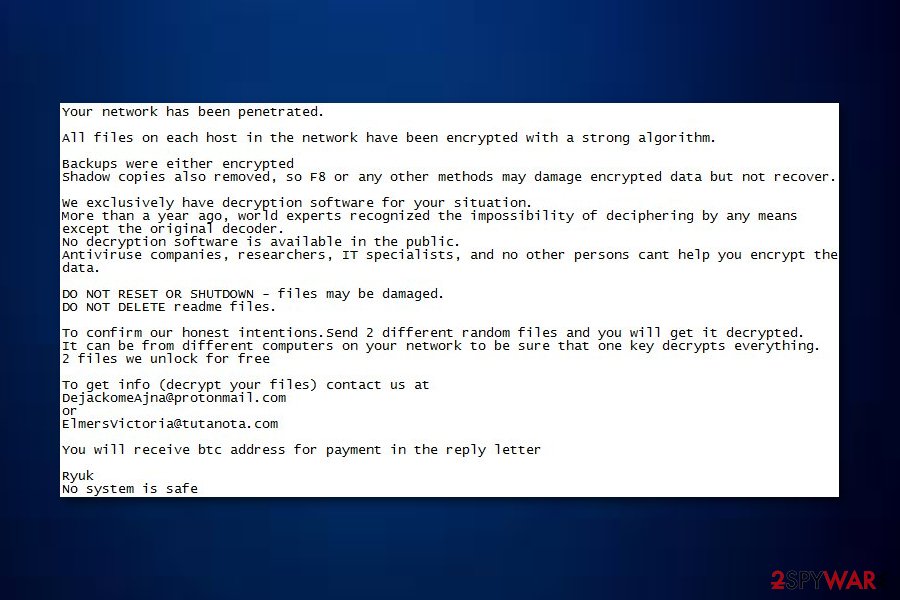
All files on each host in the network have been encrypted with a strong algorithm.
Backups were either encrypted or deleted or backup disks were formatted.
Shadow copies also removed, so F8 or any other methods may damage encrypted data but not recover.
We exclusively have decryption software for your situation
No decryption software is available in the public.
DO NOT RESET OR SHUTDOWN – files may be damaged.
DO NOT RENAME OR MOVE the encrypted and readme files.
DO NOT DELETE readme files.
This may lead to the impossibility of recovery of the certain files.
To get info (decrypt your files) contact us at
[email protected]
or
[email protected]
BTC wallet:
[link]
Ryuk
No system is safe
If the virus attacks a company or similar authority, it drops such note:
Gentlemen!
Your business is at serious risk.
There is a significant hole in the security system of your company.
We’ve easily penetrated your network.
You should thank the Lord for being hacked by serious people not some stupid schoolboys or dangerous punks.
They can damage all your important data just for fun.
Now your files are crypted with the strongest millitary algorithms RSA4096 and AES-256.
No one can help you to restore files without our special decoder.
Photorec, RannohDecryptor etc. repair tools are useless and can destroy your files irreversibly.
If you want to restore your files write to emails (contacts are at the bottom of the sheet) and attach 2-3 encrypted files
(Less than 5 Mb each, non-archived and your files should not contain valuable information
(Databases, backups, large excel sheets, etc.)).
You will receive decrypted samples and our conditions how to get the decoder.
Please don’t forget to write the name of your company in the subject of your e-mail.
You have to pay for decryption in Bitcoins.
The final price depends on how fast you write to us.
Every day of delay will cost you additional +0.5 BTC
Nothing personal just business
As soon as we get bitcoins you’ll get all your decrypted data back.
Moreover you will get instructions how to close the hole in security and how to avoid such problems in the future
+ we will recommend you special software that makes the most problems to hackers.
Attention! One more time !
Do not rename encrypted files.
Do not try to decrypt your data using third party software.
P.S. Remember, we are not scammers.
We don’t need your files and your information.
But after 2 weeks all your files and keys will be deleted automatically.
Just send a request immediately after infection.
All data will be restored absolutely.
Your warranty – decrypted samples.
contact emails
[email protected]
or
[email protected]
BTC wallet:
[link]
No system is safe
While Ryuk ransomware removal will not give users access to the files, it will get rid of the infection itself. We strongly recommend using reputable security software like Reimage Reimage Cleaner or SpyHunter 5Combo Cleaner which is capable of destroying all the traces of malware.
While hackers are actively trying to convince victims that paying ransom is a great idea (they even go as far claiming that they will reveal the security hole and show how to fix it), security researchers[7] advise not to. These people are from a high-profile crime organization and can not be trusted. Additionally, despite criminals’ warnings, you should remove Ryuk ransomware as soon as possible.
Ryuk ransomware is an infamous computer virus which appears to have relation with Hermes
New variant of Ryuk takes care that matching PCs could not be encrypted
A new version of Ryuk ransomware has been first spotted by experts from MalwareHunterTeam.[8] This latest variant of the ransomware operates by using a newly-discovered technique. Once inserted on the computer, the malware will start searching for IP strings such as 10.30.4, 10.30.5, 10.30.6, and 10.31.32.
If these IPs are found by Ryuk on the targeted computer system, the virus does not perform any encryption on stored files and documents. Nevertheless, this file-locking threat detects the computer name and searches for strings such as “MSK”, “Msk”, “msk”, “SPB”, “Spb”, and “spb”.
If these two components match, Ryuk ransomware will not encrypt the computer also. According to the opinions of cybersecurity researchers, hackers use such technique to prevent encryption of computer systems which are based in Russia. However, such a technique might not seem quite successful if worming activities are performed.
Distribution techniques evolve from spam email to trojan malware
According to PC experts, the virus is using phishing email messages to get into the target PC systems. Usually, a large amount of these messages is sent to businesses to increase the number of encrypted files and earn bigger ransoms. Beware that you need only to click on an infected email attachment to get infected with ransomware. Such messages can also be filled with trustworthy-looking logos, addresses, and similar information pretending to be from Lloyds Bank, HSBC, and similar companies that could increase chances to infect the victim with the ransomware virus.
To avoid the loss of important data, you need to be extremely careful with emails from unknown senders. Make sure you doublecheck every line included and use your mouse to check the trustworthiness of links you have been sent to.
There is a theory that Emotet and TrickBot are used to distribute this ransomware. After gaining the connection to the target network, these viruses bring additional malware to the system in exchange for a certain fee. Often, the Trickbot has been rented only to certain people.
Make sure to remove Ryuk ransomware from the system using professional tools
To perform Ryuk removal, make sure you do not consider using manual removal techniques. This is a serious virus which travels around with numerous components that can be found only by running a full system scan with anti-spyware. In this case, we recommend using SpyHunter 5Combo Cleaner or Malwarebytes which have been approved to be powerful enough to fight against such complicated malware. Additionally, check the system with Reimage Reimage Cleaner for altered registry entries and similar components (does not encrypt files).
Unfortunately, once you remove Ryuk ransomware from the system, your files will still be encrypted. That’s because the decryption key needed to recover locked data is saved on the remote servers that belong to the crew of this ransomware. However, don’t be desperate and think whether you have extra copies of your encrypted data saved on external devices. If no, use tips provided below to decrypt files encrypted by Ryuk.
This entry was posted on 2020-01-14 at 07:02 and is filed under Ransomware, Viruses.

