Razor ransomware – a Garrantydecrypt ransomware family member that is programmed to append the .razor extension to each filename
Razor ransomware is a damaging cyber threat that has emerged in the first half of February 2020
Razor ransomware is a damaging cyber threat that has emerged in the first half of February 2020
Razor ransomware is a malicious string that has emerged in the first half of February 2020. It was found to come from the Garrantdecrypt malware family. Even though this parasite is not that famous as Djvu ransomware or Phobos ransomware, that does not mean that it is not dangerous. .razor files virus operates exactly as other similar threats – by running unique encryption codes, locking all detected files, and providing payment rules. When this notorious infection appears on Windows, it heads for all the files that are stored on the device.
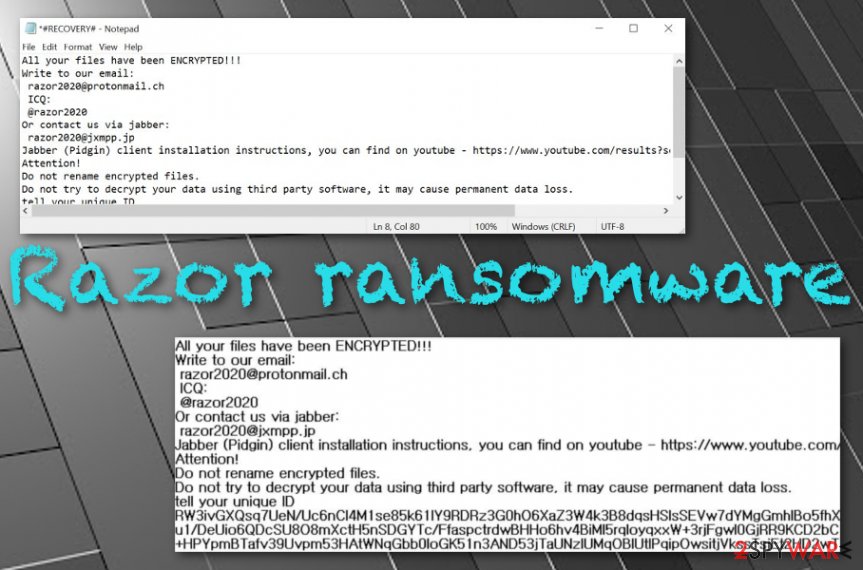
Once they are captured and locked by a strong cipher, the .razor appendix appears near to each filename. Additionally, Razor virus displays the #RECOVERY#.txt text message in a Notepad blank. This piece of information includes criminals’ contacts such as [email protected] email address, @razor2020 via ICQ, and [email protected] for contacting them through Jabber.
| Name | Razor ransomware |
|---|---|
| Category | Ransomware/malware |
| Family | Garrantydecrypt ransomware |
| Encryption | Once the virus appears on the targeted computer system, it starts scanning the device for encryptable material. When all the files and documents are detected, the malware launches a strong encryption cipher, e.g. (AES or RSA) and locks up all the components with the .razor appendix |
| Ransom note | The ransomware brings the #RECOVERY#.txt text message to the Windows computer screen which includes criminals’ contact information such as [email protected] email address, @razor2020 via ICQ, and [email protected] for contacting them through Jabber |
| Delivery | The malicious payload is mostly delivered through email spam campaigns when the criminals pretend to be from reliable shipping, healthcare or banking organizations and send messages together with attachments that are infected with the ransomware |
| Other dangers | Besides encrypting all the files that are found on the computer, Razor virus can make the system more vulnerable to other infections and let malware such as trojans escape security barriers |
| Elimination | To complete full malware removal, you have to employ reliable security software |
| File recovery | Rather than completing the criminals’ demands and paying some type of price for the decryption tool, go to the end of this page and try out the data recovery alternatives that are provided there |
| Fix software | If the malware has brought any type of damage to the computer system, you should try repairing the machine with the help of a tool such as Reimage Reimage Cleaner |
Razor ransomware is a virus that targets English-speaking users and appears on computers that are running the Windows operating system. Once the target is reached and the device gets infected, the malicious payload alters some locations on it, including the Windows Registry, Task Manager, Control Panel, User’s folder, etc.
These areas can be filled with suspicious keys, files, and processes. Beware that Razor ransomware will likely enable its module to run within every computer startup process and scan the entire system for encryptable components in a repeated amount of time. Nevertheless, the malware can end up deactivating your antivirus software in order not to get detected.
Razor ransomware is a file-encrypting cyber threat that applies the .razor appendix to each filename after the encryption process
Razor ransomware is a file-encrypting cyber threat that applies the .razor appendix to each filename after the encryption process
Furthermore, Razor ransomware will use unique encryption ciphers such as AES, RSA, or SHA to code up files. The malware can reach any types of components such as images, audios, videos, databases, excel sheets, powerpoints, etc. When these files and documents get locked, the user is not able to access them properly anymore.
Afterward, Razor ransomware stores both encryption and decryption keys on remote servers so that they would not be reachable for the victims. Another way how the malware might try to harden the data recovery process is by permanently damaging or eliminating the Shadow Volume Copies[1] by running specific PowerShell commands.
Criminals in the ransom note warn victims not to rename the encrypted files or try recovering them with third-party software as they can get lost forever. However, this is just a way for Razor ransomware developers to scare their victims and speed up the ransom payment process that is usually urged in exchange for the decryption tool:
All your files have been ENCRYPTED!!!
Write to our email:
[email protected]
ICQ:
@razor2020
Or contact us via jabber:
[email protected]
Jabber (Pidgin) client installation instructions, you can find on youtube – hxxps://www.youtube.com/results?search_query=pidgin+jabber+install
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
tell your unique ID
–
Even though Razor ransomware does not provide any particular ransom demands, this does not mean that crooks will not ask for some money after you contact them. These people are very likely to urge for a sum anywhere from $50 to $2000 or more and require it to be paid in some type of cryptocurrency, for example, Bitcoin.
You should stay away from the required payments and even from contacting crooks. Razor ransomware has been created only for hackers’ benefits and these people might decide to run away after you transfer the demanded price or provide you with fake decryption software that does not truly work. However, the choice is yours.
A piece of advice would be to remove Razor ransomware from your Windows computer system with the help of reliable software. Choose an antimalware tool that is capable of detecting some type of malware and getting rid of all the malicious products that it has brought to the computer system. This includes various files, keys, and processes.


If you are having some trouble to perform Razor ransomware removal, you should boot your computer in Safe Mode with Networking first. Afterward, continue with your task. Another reason to speed up the elimination process is the possibility that you might end up with additional dangerous malware on your computer system.
When Razor ransomware is permanently gone, now you can try some data recovery techniques for bringing your files back to their primary states. Rather than taking risks while paying the ransom, you should go to the end of this article and try some file restoring software that can be very helpful if used as required.
Email spam – a source that is at a high risk of ransomware infections
Malicious payload is aimed to be sneaked in unknown, otherwise, it would not make its way through various security barriers. Criminals who distribute ransomware viruses camouflage the infection as some type of a legitimate-looking file so that it would not raise any concern before opening. Such components often come attached to email spam messages.[2] Criminals pretend to be from reliable organizations, e.g. shipping, banking, healthcare and trick people into believing that the email is truly reliable and the clipped attachment should be opened or even downloaded.
If you have already opted for the downloading process of the unknown attachment, you should still not view the content inside unless your antimalware software says that it is safe after completing a full scan. Some ways to identify misleading email messages are the following ones:
- Always check the sender. If the email letter is coming from some type of unknown address such as [email protected], it definitely is not a reliable one as well-known companies do not use such emails.
- Investigate the text message for grammar mistakes. When you have opened the letter and read the content inside, you should try to discover any possible grammar mistakes. If there are some, this is very likely to be a sign that the email is not coming from a trustworthy sender.
- Evaluate the expectations of such an email. If you have not been waiting for an email lately but still have received some type of urgent or important message, there might be hackers trying to trick you. If you have any concerns about the received email, you can always try contacting the company, which has supposedly written the letter, via mobile phone.
NoVirus.uk specialists[3] claim that there are also some other ways of how ransomware can be delivered to computers. Malicious actors can use software cracks to hide the infectious payload, they can create fake Adobe Flash Player o JavaScript updates to camouflage the ransomware, and so on. You should know that everything you do online should be completed with big care and responsibility. Also, owning a reliable antivirus tool will increase your chances of avoiding malware greatly.
Razor ransomware removal requires strong software
If you are looking forward to getting rid of the cyber threat once and for all, you need to make sure that you employ tools that are strong enough. Razor ransomware is a dangerous virtual parasite that scatters malicious payload all over the computer system, including locations such as the Control Panel, Registry,[4] and Task Manager. Only by cleaning these directories properly you will be able to terminate the infection in a way that it will not return in the upcoming feature.
Note that completing Razor ransomware removal manually is not a way to make things right. While performing the elimination in such a way, you take risks of completing mistakes that might appear damaging to your computer system. You also might skip some malicious keys or files. So, go to the Internet and read all about recommendable antimalware programs and choose a piece of software that has collected the best user and expert reviews.
If you see that you are having a hard time to remove Razor ransomware from your infected Windows device, the malware might be executing a malicious command to blog your AV tool or your removal attempts. Regarding this fact, look down below and follow the steps that teach how to boot in Safe Mode. Afterward, you can start viewing data recovery alternatives some of which have also been included to the end of this article.
Remove Razor using Safe Mode with Networking
To diminish malicious settings on your Windows computer and deactivate the parasite, apply the following guiding steps and execute Safe Mode with Networking
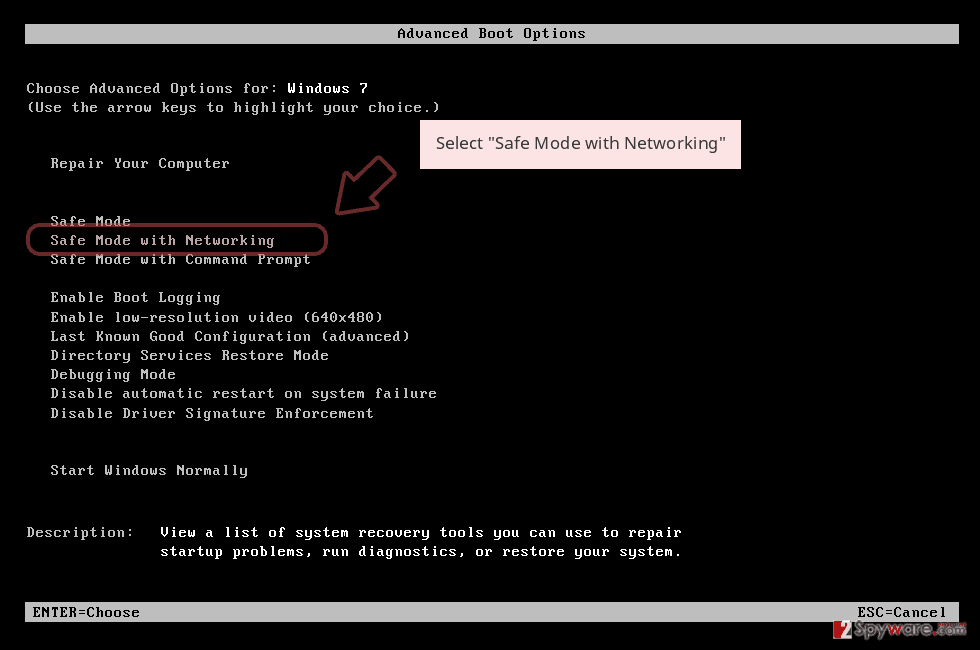
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
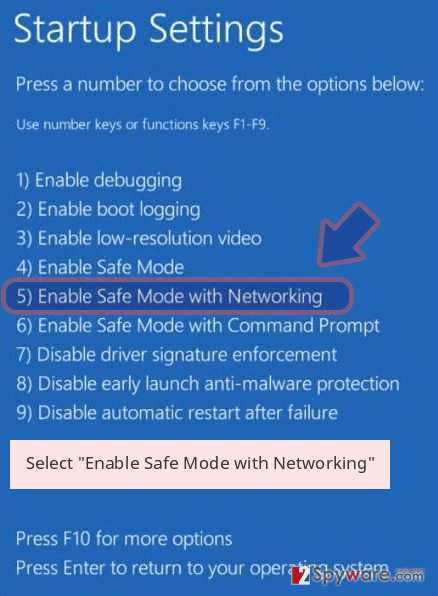
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Razor removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Razor using System Restore
To deactivate the ransomware virus which has been recently running on your Windows device, you should launch the System Restore feature. Complete the task by following these instructions
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Razor from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If you have discovered that your files and documents have received the .razor appendix, it is a sign of data encryption that prevents the user from properly accessing the components. Criminals will definitely provide you with ransom demands and require to transfer the payment in exchange for the decryption tool.
However, we recommend that you avoid paying these people as there is a big risk of getting ripped off for nothing. After receiving the payment, crooks might not even provide you with the promised key. Alternatively, you can try recovering your blocked data with the help of the below-provided material.
If your files are encrypted by Razor, you can use several methods to restore them:
Employing Data Recovery Pro might increase your chances of restoring locked files
Try downloading and installing this piece of software as it can bring you satisfying results when trying to restore data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Razor ransomware;
- Restore them.
Windows Previous Versions feature might be the right tool for file recovery
If you have been looking for some type of software that could reverse your encrypted files back to their previous states, this one might just be the exact one. However, you should have enabled System Restore in the past for this tool to operate properly
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use Shadow Explorer to restore some components that are locked by ransomware
If the file-encrypting virus has locked all of your files and documents but has not deleted or permanently damaged the Shadow Volume Copies, you should give this software a try
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
The .razor files decrypter is still in the development mode
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Razor and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-02-13 at 05:04 and is filed under Ransomware, Viruses.

