$$$ ransomware – a malicious infection threatening victims that the demanded price will rise if they do not make contact as soon as possible
$$$ ransomware is a notorious virus that travels with the help of suspicious emails and their malicious attachments, software cracks, malvertising, etc.
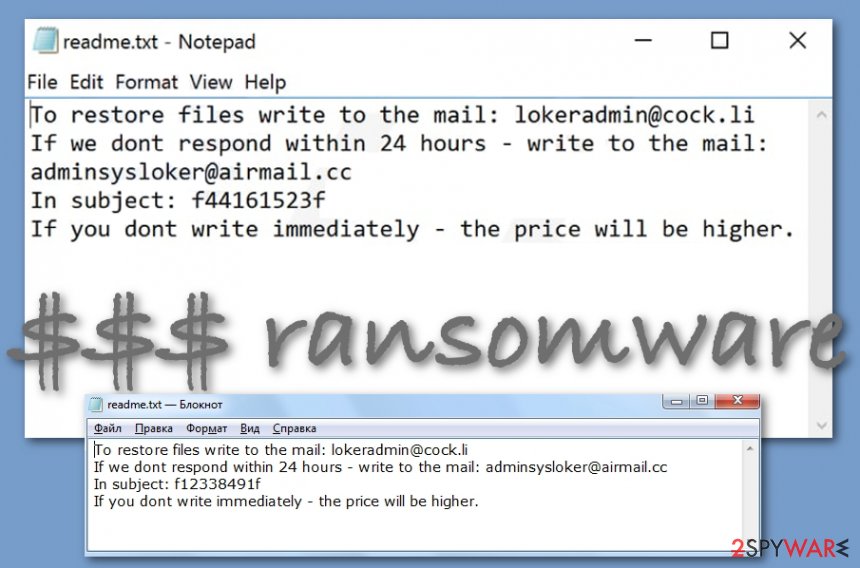
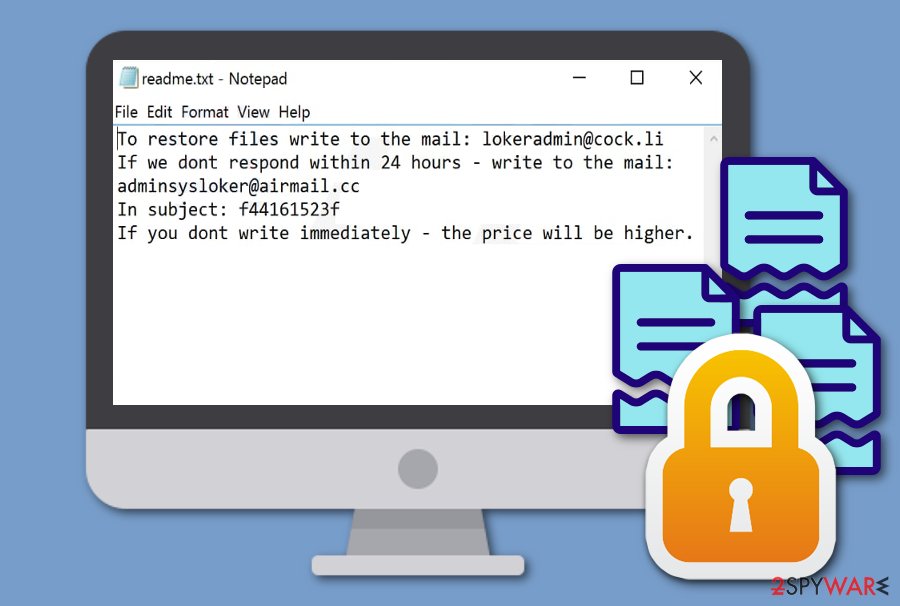
$$$ ransomware is a file-encrypting and ransom-demanding cyber threat that uses an encryption cipher such as AES or RSA to lock up files and demands an immediate money transfer. When all the found documents and files are locked, the malware adds the .$$$ appendix to each filename and the users are not able to access the components properly anymore. Afterward, $$$ ransomware provides the readme.txt Notepad message that holds the [email protected] and [email protected] email addresses that are placed there for making contact with the victims. Furthermore, the hackers try to scare the users by claiming that the demanded ransom price will slightly increase if they do not receive an immediate response after the victim views the ransom note.
| Name | $$$ ransomware |
|---|---|
| Category | Ransomware virus/malware |
| Emerging period | This virtual parasite has been discovered in the second half of January 2020 |
| Danger | This malware holds the danger level of high as it finds all encryptable files and locks them with a unique encryption cipher such as AES or RSA. Nevertheless, the ransomware makes the computer system vulnerable to other infections and can bring trojans and other malware to the computer system |
| Extension | Once all of the files and documents are locked, they all get the .$$$ appendix added to their names. For example, if you had a file named presentation.pptx, it is converted to presentation.pptx.$$$ |
| Ransom message | The cybercriminals drop the readme.txt ransom message that encourages the victims to transfer the payment as soon as possible, otherwise, the price will slightly increase |
| Crooks’ emails | The hackers provide the [email protected] and [email protected] email addresses as a way to make contact |
| Spreading | Ransomware infections are commonly spread through software cracks, email spam messages and their malicious attachments, malvertising ads, and other unprotected sources |
| Elimination | If you have discovered this infection on your Windows computer, you should clean the machine as soon as possible by employing trustworthy removal software |
| Fix process | If you have found any damaged or altered areas on your device that appeared after the malware infection, there is a chance that you will be able to recover it with the help of Reimage Reimage Cleaner |
$$$ virus is ransom-demanding malware that has appeared at the end of January, 2020. According to the ransom note’s language, the criminals are targetting English-speaking people. As long as English is the most popular language worldwide, this gives the hackers a chance of infecting a wider range of users.
By employing specific encryption keys such as AES and RSA,[1] $$$ ransomware locks up all types of files and documents such as powerpoints, word documents, excel sheets, zip files, audio and video files, etc. The malware might inject a specific process in the Task Manager that allows scanning the system for encryptable components.
Continuously, $$$ ransomware might also alter the Windows Registry and Task Manager[2] in order to boot itself up within every computer startup process. Additionally, the malware might be able to disable antivirus protection and evade getting detected. This way the ransomware virus can stay on the Windows system unnoticed for a longer amount of time.
$$$ ransomware is a file-encrypting parasite that threatens the users to increase the price if they do not respond to the message immediately after receiving it
$$$ ransomware can try to harden the file recovery process for the users by deleting the Shadow Volume Copies of encrypted components with the help of PowerShell commands. This way the infected victims will not be able to use data recovery software that requires the Shadow Copies to remain safe and untouched.
To add, $$$ ransomware might also target the Windows hosts file. The malware can badly damage it in order to prevent the users from visiting cybersecurity-related websites, forums, and other places that might provide reliable and relevant information on the virus’s removal process and some data recovery tips.
If you are thinking of paying $$$ ransomware developers, you should overthink everything twice. Even though these people are rushing you to transfer the money as fast as possible, they can seek to scam you:
To restore files write to the mail: [email protected]
If we dont respond within 24 hours – write to the mail: [email protected]
In subject: –
If you dont write immediately – the price will be higher.
Our recommendation would be not to fall for believing in these people as $$$ ransomware is distributed only to benefit the hackers. These people will likely urge some type of cryptocurrency transfer, e.g. Bitcoin that allows them to stay safe and untrackable during the entire process and also after the payment sessions.
You should opt for the $$$ ransomware removal process and try some alternative data recovery techniques later on. First of all, employ reliable software that will be able to take care of the malware and all the malicious components that it has brought to the Windows computer system. If there are some parts that need fixing, you can try employing Reimage Reimage Cleaner .
Another reason to remove $$$ ransomware fastly is that the malware can bring other infections to the computer system. By disabling the antivirus protection the ransomware virus makes the machine vulnerable to other parasites and various trojans, other ransomware, worms, and spyware can easily infect the Windows device.
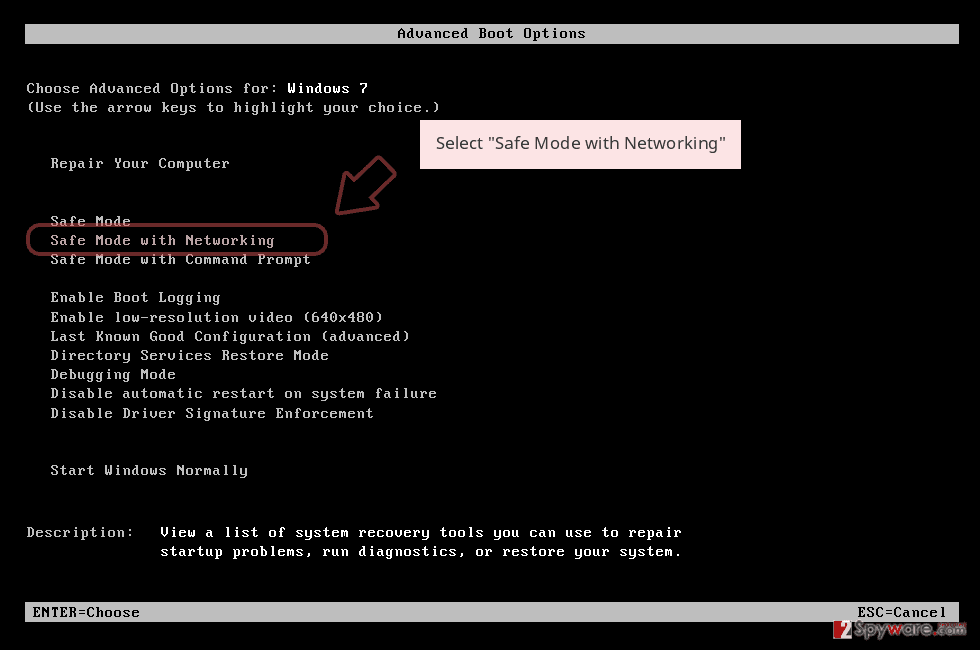
If you are having trouble to eliminate the malware, you should boot your machine in Safe Mode with Networking or activate the System Restore feature to disable all malicious tasks. After you uninstall $$$ ransomware from your machine, you can start thinking about data recovery techniques. For help, we have provided some possible methods at the end of this article.
Keep your computer safe from ransomware infections
Security specialists from NoVirus.uk[3] state that ransomware viruses are most frequently carried through email spam and the malicious attachments that come clipped to the messages. The cybercriminals might pretend to be from reliable shipping, healthcare, banking, or other companies and convince you that all of the provided material is completely legitimate and safe for opening.
However, we recommend being careful with all the received messages that you were not expecting to find in your email box. Always identify the sender – check if the person is sending you the email from a proper email address, go throughout the entire text and search for possible grammar mistakes, and do not open any downloaded attachments before scanning them with antimalware software.
Continuously, ransomware-related payload can get delivered through vulnerable RDP. If the port does not include a strong password or includes none protection at all, the hackers can easily connect to it and reach the targeted computer system remotely. So, always think about strong and reliable passwords that contain some letters, symbols, and numbers.
Also, ransom-demanding viruses can be distributed through malvertising ads that are lurking on unsecured third-party websites, cracked software that can be found on peer-to-peer[4] networks, and other places. It is very important to have a properly functioning antivirus tool that will inform you if something wrong is going on your PC.
Learn about proper data recovery techniques
All the developers of malware seek to convince their victims to pay the demanded ransom price. Some demand an inadequate amount and try to attract the users with promises of the decryption tools or threats that the ransom will rise if the victim does not transfer the payment on time.
Furthermore, the crooks store both encryption and decryption codes on remote servers that are reachable only for the owners. However, even though the hackers are likely to have the recovery key, that does not mean that you might transfer the price and receive nothing or just a fake tool as the hackers do not really care about their victims.
Our recommendation is that you should always think of other alternative techniques that you can use for the file recovery process. Do not listen to the crooks if they tell that other tools will cause permanent file damage as this is not true. Travel to the end of the article where you will find three methods that might help you with data recovery.
Terminate $$$ ransomware from your Windows OS
$$$ ransomware removal will be a hard process to complete if you choose to do it on your own. This is why we advise you to use reliable antivirus products that are capable of terminating the malware from Windows OS. If you have any trouble with detecting the ransomware virus, it might be disabling your tool. For this purpose, reboot your computer in Safe Mode with Networking or activate System Restore to diminish all malicious tasks on your device.
After you remove $$$ ransomware from the Windows machine, you can try using data recovery techniques that are provided at the end of this article. However, while choosing the software to use, make sure that your computer includes the right conditions for its operating process. Also, always remember that you need to get rid of the ransomware first, otherwise, the data recovery process will be useless as the malware can encrypt all of your files again.
Remove $$$ using Safe Mode with Networking
To diminish all malicious processes and deactivate the ransomware virus on your Windows computer, employ the following guiding steps to reboot your machine in Safe Mode with Networking.
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
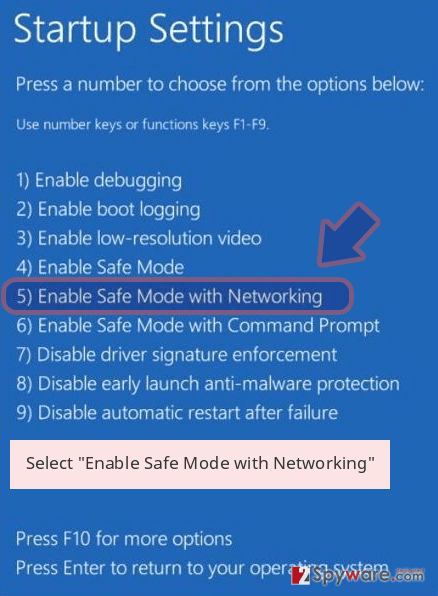
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete $$$ removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove $$$ using System Restore
To deactivate the dangerous cyber threat and disable all the malicious tasks that it has been carrying out, you should opt for the System Restore feature. This function can be activated by completing the following steps.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove $$$ from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by $$$, you can use several methods to restore them:
Use Data Recovery Pro for file restoring purposes.
If you have been searching for a tool that would help you to recover some of your files and documents, you can try out this piece of software.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by $$$ ransomware;
- Restore them.
Windows Previous Versions feature might be a good choice for file recovery.
If you have enabled the System Restore feature in the past, you can try this tool for restoring at least some of your individual files.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Employing Shadow Explorer is an option for data restore.
Try restoring some of the encrypted files with this tool. However, note that the software is likely not to work if the ransomware virus has permanently destroyed or eliminated the Shadow Volume Copies of locked components.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Security experts are currently working on the decrypter.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from $$$ and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-02-03 at 06:30 and is filed under Ransomware, Viruses.

