Cerber ransomware is a multi-variant crypto-malware that avoids infecting users from Russia and other CIS countries
Cerber virus ransom sum is inadequate
Cerber ransomware is a file locking virus that was first spotted in the wild in March 2016. Operating Ransomware-as-a-service scheme, the malware became a diverse and high profile threat that targets regular users, as well as organizations and businesses, although it avoids infecting victims from the Commonwealth of Independent States (CIS). Security researchers believe that Cerber ransomware was developed in Russia,[1] as it is very prominent on Russian underground forums.
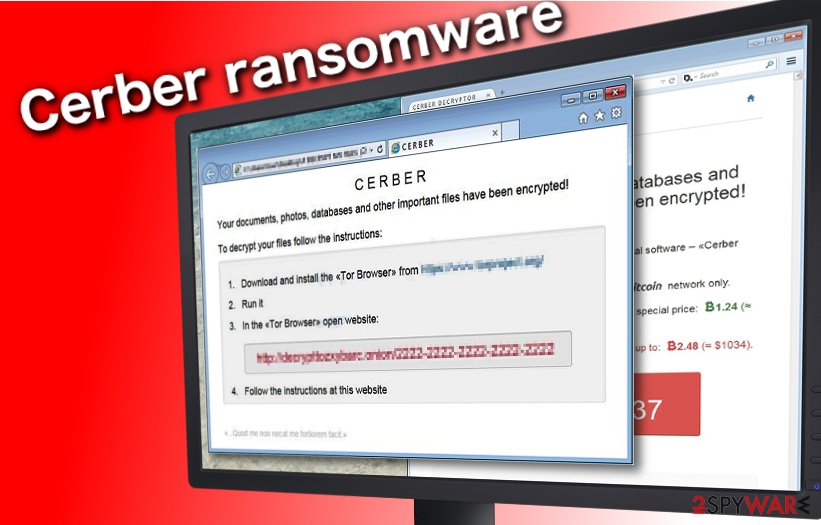
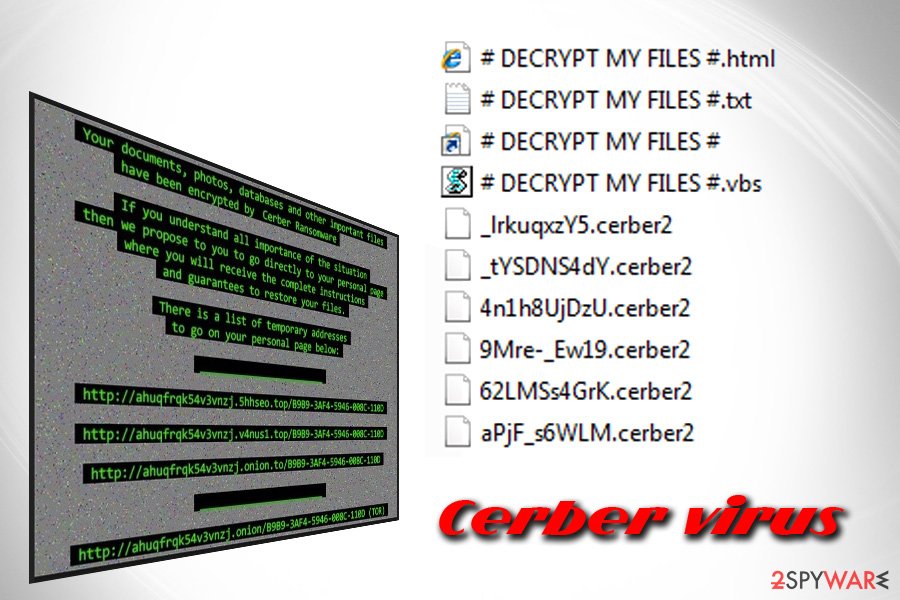
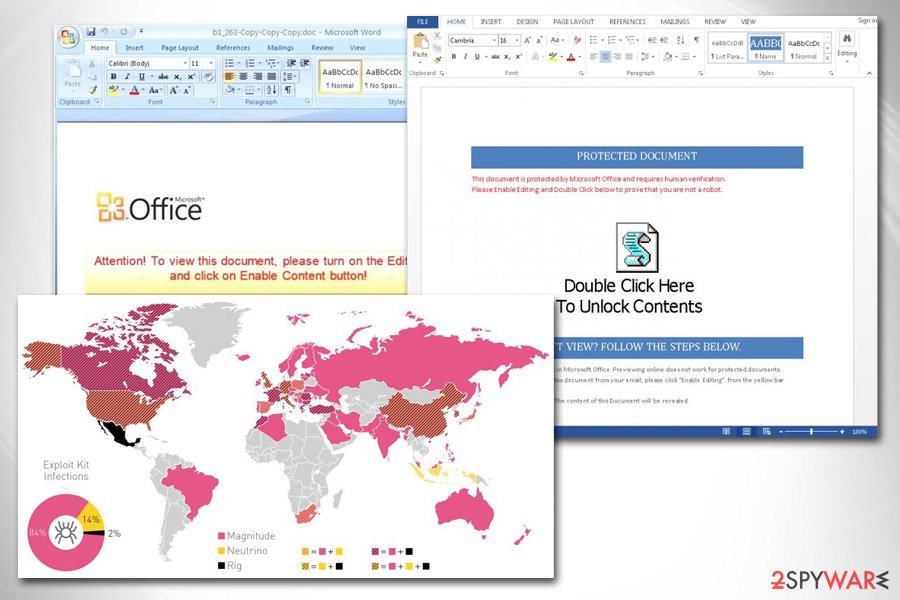
During years of its operation, Cerber ransomware was split into five major variants, although sub-variants are being released on a regular basis, and mostly spread via malicious Word documents sent out to thousands of users via spam emails, although other methods, like Rig and Magnitude, exploit kits were also used. Once inside, the malware applies AES-256[2] or RC4 encryption algorithm to lock up all personal data and mark it with .cerber, .cerber2, .cerber3, .af47, .a48f, .[random characters] or another extension, and changes the desktop wallpaper, which notifies victims about the Cerber virus intrusion. Additionally, hackers also drop a ransom note which comes in various formats (.txt, .vbs, and .html) and asks users to pay a ransom of 1.24 BTC or more, depending on the malware version.
| SUMMARY | |
| Name | Cerber Ransomware |
| Type | Cryptomalware, file locking virus |
| Operated scheme | The malware uses RaaS (ransomware-as-a-service) scheme – the developers of malware keep 40% and the distributing parties retain 60% of the profits earned from ransom payments |
| Encryption algorithm | Cerber ransomware will encrypt all personal files using AES-256 or RC4, and render the computer system unstable |
| Size of ransom | The ransom size varies greatly and can reach 1.24 BTC |
| Extension | cerber, .cerber2, .cerber3, .af47, .a48f, .[random characters], .ba99, .beef |
| Variants | |
| Ransom notes | # DECRYPT MY FILES #.txt, # DECRYPT MY FILES #.html, # HELP DECRYPT#.html, _READ_THIS_FILE.hta, *HELP_HELP_HELP[random characters]*.hta, _R_E_A_D___T_H_I_S___[random]_.txt or _R_E_A_D___T_H_I_S___[random]_.hta, README.hta |
| Assocaited files | Acotyledon.exe, Straightness.exe, Parameter.exe, Giobertite.exe |
| Distribution | Exploit kits (Rig, Neutrino, Magnitude), spam emails, malicious sites |
| Decryptable? | There are limited options when it comes to data decryption, although some variants can be decrypted with the help of Trend Micro decryption tool |
| Elimination | In some cases, Cerber may disable the installed anti-virus software in order to operate without interruptions. To bypass this feature, you should access Safe Mode with Networking and perform a scan with reliable security software, such as SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | Cerber ransomware often renders system unstable as it also affects some system files. To avoid reinstallation of Windows operating system, you can apply its fix using Reimage Reimage Cleaner repair software |
Cerber ransomware virus has been changing the name of its ransom note repeatedly. So far, the crypto-malware versions use the following names for ransom notes: # DECRYPT MY FILES #.txt, # DECRYPT MY FILES #.html, # HELP DECRYPT#.html, _READ_THIS_FILE.hta, *HELP_HELP_HELP[random characters]*.hta, _R_E_A_D___T_H_I_S___[random]_.txt or _R_E_A_D___T_H_I_S___[random]_.hta, README.hta.
Like any other file-encrypting virus, the virus can infiltrate the system via malicious spam emails carrying deceptive .ZIP, .DOCM, .PDF, or .JS file attachments. An interesting detail about Cerber ransomware is that it will not attack your computer if you live in one of these countries:
- Azerbaijan;
- Armenia;
- Georgia;
- Belarus;
- Kyrgyzstan;
- Kazakhstan;
- Moldova;
- Turkmenistan;
- Tajikistan;
- Russia;
- Uzbekistan;
- Ukraine.
Unfortunately, if none of these is your country of current residence, this virus may potentially hit your computer.
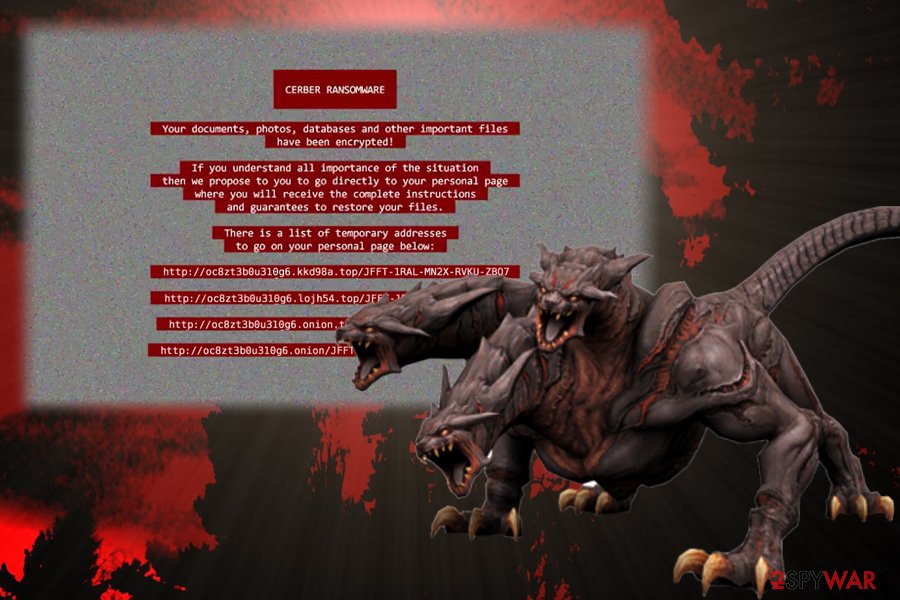
Cerber ransomware sets itself to run automatically on the next computer startup. Once the computer becomes active, ransomware starts sending random error messages and then reboots your computer into Safe Mode with Networking. Unfortunately, the virus then restarts your computer again, this time in a normal regime, and starts the encryption process. The latest version has received a huge update – now it uses red color for the ransom note used to warn the victim about the encrypted data.
Once the encryption process is finished, Cerber ransomware drops ransom notes in each folder that stores infected files. These notes are named as DECRYPT MY FILES. The file extension may vary, it can be a .html, .txt, or .vbs file. The .vbs file will also play a sound message, which says:
Hi, I’am CERBER RANSOMWARE 😉
—–
Y0UR D0CUMENTS, PHOTOS, DATABASES AND OTHER IMPORTANT FILES HAVE BEEN ENCRYPTED!
—–
The only way to decrypt your files is to receive the private key and decryption program.
To receive the private key and decryption program go to any decrypted folder,
inside there is the special file (*_R_E_A_D___T_H_I_S_*) with complete instructions
how to decrypt your files.
If you cannot find any (*_R_E_A_D___T_H_I_S_*) file at your PC, follow the instructions below:
—–
1. Download “Tor Browser” from [link] and install it.
2. In the “Tor Browser” open your personal page here:
[link]
Note! This page is available via “Tor Browser” only.
—–
Also you can use temporary addresses on your personal page without using “Tor Browser”.—–
1. [link]
—–
Note! These are temporary addresses! They will be available for a limited amount of time!
—–
The ransom note explains what happened to your computer and provides instructions on how to retrieve your files. Shortly said, virus developers, ask you to download Tor browser[3] to access the website where you can pay the ransom anonymously. It demands the victim to pay 1.25 BitCoins, which is approximately $512 USD.
It also threatens that the ransom will be doubled if the victim does not pay within seven days. If the ransom is paid, this ransomware should supposedly provide a unique download link to get a Cerber ransomware virus decryption tool. Otherwise, there is no way to decrypt files for free. Please, do NOT fall for these lies and get rid of ransomware to stop the encryption of another portion of your files.
Every unprotected computer can be infected with Cerber ransomware. Removal is not easy
Next to money extortion, Cerber ransomware is capable of stealing crypto wallet data
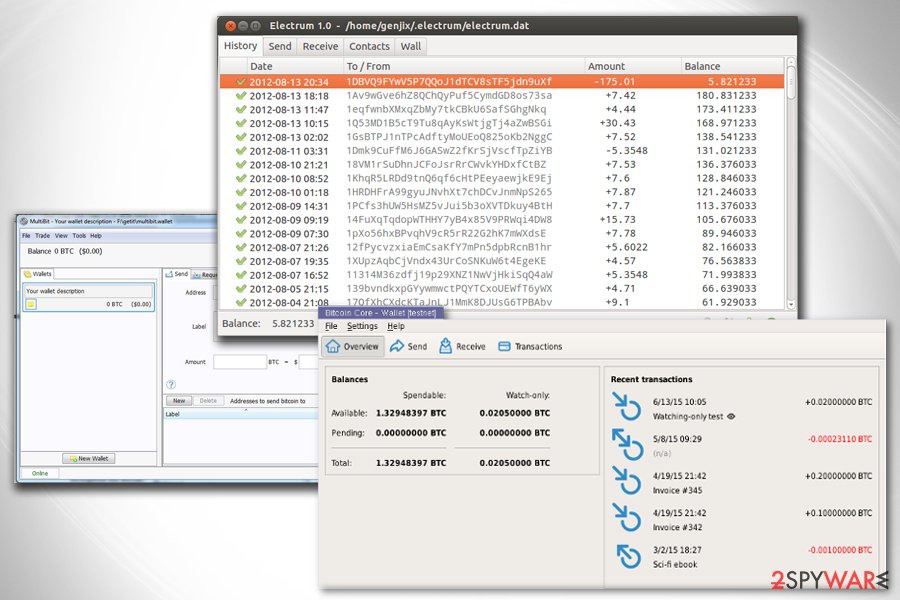
In order to boost their income, developers of the Cerber ransomware have recently launched a new variant that is capable of stealing Bitcoin wallet data.[4] After the infiltration, it steals passwords stored in the Internet Explorer, Google Chrome, and Mozilla Firefox web browsers. Once it’s done, it becomes easier to obtain information from Bitcoin wallets.
The virus looks up for free files that belong to the different Bitcoin wallet apps:
- wallet.dat used by Bitcoin Core wallet;
- *.wallet used by Multibit wallet app;
- electrum.dat used by Electrum wallet app.
Another proof that Cerber ransomware virus continues growing and expanding is a recent collaboration with developers of Kovter Trojan. This cyber infection is known since 2013 as click-fraud malware. Both malicious programs were noticed spreading with spam emails that delivered fake notifications from parcel delivery services, such as FedEx, USPS, and UPS.[5]
Therefore, once victims are tricked into opening an obfuscated file, they download two viruses instead of one cyber infection. As a result, victims can not only get their files encrypted but also lose personal information, such as login details. To make sure you are not infected, double check your system with Reimage Reimage Cleaner . It will also help you remove Cerber ransomware with each of its files and will also fix damaged files and similar components on your computer.
Good news: some Cerber ransomware versions fail to remove Shadow Volume Copies
New year have already brought us new changes in Cerber ransomware. After making the latest researches on this malware, experts discovered that it turned red. In fact, red color has shown up in the ransom note of this ransomware that warns its victims about the encryption of their files and a need to pay the ransom in exchange for the malicious decryptor. Besides, this crypto-virus tends to use .ba99 file extension which is appended to every victim’s file. Four random characters can also be appended.
Fortunately, this malware fails to remove Shadow Volume Copies of these files that it encrypts, what should help users recover their data with the help of Shadow Explorer and similar tools. This version has already been named as Red Cerber. Of course, after discovering such concerning news, we predict that this virus will stay at its peak this year just like it did the last year.
What is more, cyber criminals have just started with new distribution tricks. Although they are still delivering massive loads of the virus’ examples via email, now they appear to be using IP addresses that belong to Amazon Web Services, or shortly Amazonaws.
These malicious emails reportedly contain no subject line and no message, simply an attachment. The attachment is a ZIP file with a Word document in it, which contains a Macros script that downloads the ransomware as soon as the victim enables Macros function in Word. Zip archives, as well as Word documents, are named with a random set of digits. Here are some of the malicious email addresses that criminals are using to deliver Cerber ransomware to target systems:
- vroak[@]otmail.it;
- clayton.lively[@]cogentpowerinc.com;
- kasserer[@]villingevand.dk;
- rbrown[@]rsu13.org.
Cerber ransomware versions. 2020 guide
Cerber Decryptor
Cerber Decryptor tool has been offered by Cerber ransomware virus authors since its appearance. They have been advertising it as a program that is supposedly the only one capable of recovering encrypted data for the victim. This might not be true because you can never rely on cybercriminals. This piece of malware can be bought in Bitcoins, but there is no information whether it decrypts files or not.
Even if it does, remember that criminals can send it to you in a bundle with malicious files or Trojans, which can cause further security problems to you. Malware researchers have always been suggesting not to rely on cyber criminals and decryption services that they offer. Besides, paying the ransom would fund their further projects, so you may want to think twice before you reach out for your credit card. The wisest solution is to initiate Cerber ransomware removal right after it shows up on the system. This procedure can save some part of your files from encryption.
Cerber2 Ransomware
Cerber2 ransomware is the second version of Cyber virus. It was released in August 2016, and it seems to be distributed via drive-by downloads, malvertising, and malicious email campaigns. This virus locks the data using a nearly unbreakable encryption algorithm and adds .cerber2 file extension to them.
Once encrypted, files cannot be accessed in any way without having the decryption key. Of course, you can get the decryption key, but crooks ask to pay money for it, in other words, you need to pay a ransom to get your files back. It is strongly recommended not to pay the ransom as Cerber2 decryption tool might have flaws and not decrypt the data entirely. Just like other ransomware decryptors offered by authors, this one can be supplemented with harmful additional files as well. Security experts recommend removing v2 as soon as the victim notices that the computer has been compromised by it and retrieve lost data from backups.
Cerber3 ransomware
Cerber3 is yet another version of crypto-virus that has clear improvements in its code. This new version of Cerber ransomware has also been considered to be more malicious and destructive as the hackers had plenty of time to fix the bugs found in the previous two versions. The second version of this ransomware was found by security researchers in the middle of September 2017. After appending .cerber3 file extension to the encrypted data, it drops the ransom note called # HELP DECRYPT #.html.
The virus was actively spread via Ammyy Admin web page[6] which was infected with the malicious file for several days, approximately from the 13th to 15th of September. The binary, which was entitled as an encrypted.exe, was placed in AA_v3.exe. Previously, this domain was assaulted by other highly damaging malware in the future. At the moment, the website is fully restored and safe for public use.
Cerber 4.0
Cerber 4.0 is yet another vicious version of ransomware. This virus does not use previously-used extensions anymore. It has improved its encryption algorithm and now displays extensions consisting of a jumble of different numbers instead. Besides, according to the virus creators, this new version of the virus is much more resistant to antivirus detection and manages to disguise its activity on the computer until all of the files are encrypted.
Talking about files, it has been found that Cerber v4.0 is now capable of encrypting even more file types which only proves that ransomware developers are not hanging around and are ready to exploit as many users as possible. For this purpose, they have also released the RaaS version of Cerber which can be obtained on the dark web. Currently, experts count three main distributors of this malware, but it is very likely that more cyber crime enthusiasts will join in.
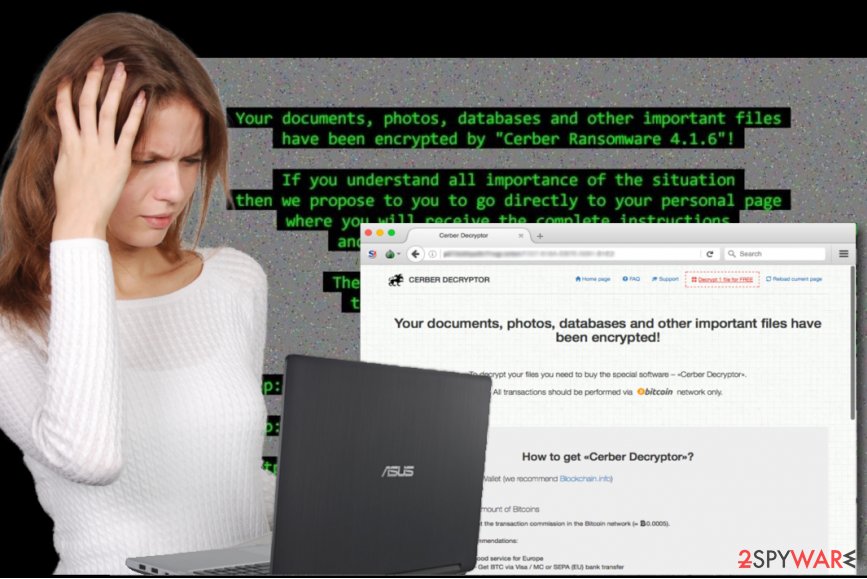
Cerber 4.1.0 ransomware
Cerber 4.1.0 ransomware differs from the previous versions mainly due to appended extension. While previously, .cerber2 and .cerber3 extensions were the trademark signs of the versions, now the virus leaves 4-digit extension or adds no extension at all.
Another major improvement lies in the distribution. PseudoDarkleech Rig exploit kit helps transfer the malware. On the other hand, such discovery will help the virus researchers to publish the decryption key and issue prevention measures sooner. The improved version also sends the request of a specific HTTP. It results in retrieving JSON file which contains payment instructions. It links to 17gd1msp5FnMcEMF1MitTNSsYs7w7AQyCt bitcoin address. Though there are more technical details revealed, it still makes Cerber ransomware virus a terrifying cyber infection.
Cerber 4.1.1 version
Cerber 4.1.1 version comes in the “bonus” package along with 4.1.0 version. Since it is little known about the exceptional features of this edition, there are many speculations about its capabilities. It is likely to spread via the same exploit kit as 4.1.0 version. Virus researchers have noticed that Cerber ransomware has changed its IP address again. Such strategic move makes the tracking of the infection source more complex.
In order to generate 4-digit code, the ransomware employs a complicated registry segment called “MachineGun”. It is an integral part of the entire HKLM\Software\Microsoft\Cryptography key. Taking into account, these peculiarities complicate the elimination of the threat. That is why a proper security application is a necessity. Similar infections await for victims in file-sharing networks or other questionable domains. It is unwise to consider remitting the payment as several versions of the malware have already gained millions of dollar profit and the developers are unlikely to send the decrypter.
An example of Cerber 2 encrypted files
Cerber 4.1.4 virus
Cerber 4.1.4 virus showed up right after the appearance of 4.1.1 version, and these viruses are very similar. They both encrypt files using the same methods, corrupt the original filename and append a customized four-character extension instead of the original one. Ransomware roots deeply into the system, adds registry keys, alters values, drops its components to the %TEMP% folder and other locations across the entire computer system to make it harder to remove.
Each component is extremely dangerous, and it is a must to remove them all at once to ensure a successful Cerber 4.1.4 removal. This virus strongly encrypts personal data without any shame and demands a ransom in exchange for Decryptor. No matter how hard malware analysts try, they cannot break this virus’ obfuscation layers and find out what algorithm is used to generate unique encryption/decryption keys for the victim. Sadly, files encrypted by this version cannot be recovered with any decryption tools.
Cerber 4.1.5 ransomware
Cerber 4.1.5 ransomware appeared at the beginning of November 2016, and successfully infected hundreds of computers already. This version copies techniques used in the past and hardly differs from previous versions. Encrypted files become unrecognizable because virus scrambles their filenames; however, the virus creates a unique file extension for each victim and appends it to encrypted records. It leaves a ransom-demanding message in README.hta file, which points to personal payment websites.
The victim is asked to pay 0.6967 BTC, which equals to $500, or more if he/she fails to pay up in the given term. Cerber 4.1.5 reportedly spreads with the help of notorious Neutrino and RIG exploit kits, malvertising, and of course malware-laden emails. You can protect your PC from this ransomware by stockpiling data backups and installing a trustworthy anti-malware software.
Cerber 4.1.6 ransomware
Cerber 4.1.6 ransomware emerged at the end of November 2016, more or less after a month after the appearance of the 5th edition of the fourth ransomware version. This modification of the virus has no outstanding improvements and functions just like its former versions do. The virus merges RSA and RC4 encryption algorithms to create an uncrackable cipher that renders personal files, documents, databases and other important files useless.
The ransom price is 501$, and criminals command the victim to transmit this sum of money via Bitcoin system within five days; otherwise, they increase the ransom price. This sequel to the infamous project is just as dangerous as its predecessors, and it also connects every compromised PC into a botnet to carry out DDoS attacks. Victims of the 4.1.6 version should remove the virus as soon as possible and perform several system scans to thoroughly analyze the computer and remove all malicious files and ransomware remains.
Cerber 5.0 ransomware
First spotted in late December 2016 to March 2017, Cerber 5.0 ransomware, was another version released by developers in the hopes of snatching more money from virus victims. This variant of the Cerber family was spread with the help of malicious executables falsely signed by legitimate companies that provide certifications.
Once inside the system, Cerber 5.0 virus will check if there is one of the following anti-virus installed on the system: ArcaBit, ArcaVir, Avast, Bitdefender, Bullguard, CA, Emsisoft, ESET, eScan, eTrust, F-Secure, G Data, Kaspersky, Lavasoft, or TrustPort. If one of these apps is present, the ransomware will not initiate the infection procedure.
In case the opposite is true, Cerber 5.0 ransomware will disable Windows startup repair function, delete Shadow Volume Copies, and terminate the following processes:
- excel.exe;
- infopath.exe;
- msaccess.exe;
- mspub.exe;
- onenote.exe;
- outlook.exe;
- steam.exe, and a few others.
After that, Cerber 5.0 ransomware will encrypt all personal files located on the computer, although it will skip most of the viral system files, such as boot.ini, .desktop.ini, .iconcache.db, .ntuser.dat, etc. Just as its predecessors, this variant will drop a ransom note (although named differently – README.hta), where crooks will ask users to click on a provided link that would direct them to a personal payment/contact page. As usual, users should not give in to crooks’ demands, as they might lose the money, along with encrypted files.
Cerber 5.0.1 ransomware
Cerber 5.0.1 ransomware was quickly launched to back up the previous infections. It keeps encrypting files with RSA-2048 and AES-256 algorithms. That is why users, entrapped by Cerber ransomware, might comply with the hackers’ demands to retrieve the files. Needless to say, it is not recommended to transmit the money as there are few guarantees of getting it back. This version has been spreading as a fake email warning with huge billing sums.
The virus urges a victim to open the attachment which would activate a VBA script. Afterward, it will execute the .exe file which downloads the main file of the infection. It also disguises its processes in Task Manager to lower the risk for users to spot ominous command. Do not waste and eliminate the threat before it causes more severe outcomes.
Red Cerber ransomware
Red Cerber ransomware. This version has been detected on the eve of 2017. In comparison to previous variations, the gearheads introduce several changes in the overall design and operation peculiarities. One of the key modifications was the disabled command to delete shadow volume copies. Likewise, it gives hope for its victims to recover the encrypted files.
What is more, it employs additional tools for delivering a blow to a virtual community. Along with spam emails, RIG and Nemucod exploit kit are also employed to increase the number of victimized systems. Compromised and corrupted domains also serve for spreading this virus. Keep in mind that the corrupted version of Adobe Flash Player also might disguise Red Cerber malware. There are also a few modifications concerning encryptable file formats. Its developers add 50 file extensions which the virus aims to encode. However, a few, mainly system executable files, such as .exe and .bat, were excluded from the list.
Help_help_help ransomware virus
Help_help_help ransomware virus. After taking a short break during the holidays, the cyber villains introduced the modified version of Red Cerber. The key changes include the introduction of the demands in the *help_help_help[random characters]*.hta file. The version which is found by TrendMicro as RANSOM_CERBER.F117AK[7] avoids firewalls, antivirus software or antispyware products.
The penetrators also added improved Nemucod exploit kit. Needless to say that such improvements only elaborated the infection even more. The key astonishing feature of the malware lies in the execution process. Nemucod exploit kit delivers cer.jpg file into your system. After its sets foot on the operating system, it performs a metamorphosis: the file changes into .exe file.
Consequently, it becomes only a matter of seconds when help_help_help virus completes its hijack. After encrypting target files, the virud drops a ransom note called _R_E_A_D___T_H_I_S___[random]_.txt or _R_E_A_D___T_H_I_S___[random]_.hta. The ransom note starts with a different line than the rest of Cerber ransomware virus ransom notes – it says “Hi, I’am CERBER RANSOMWARE 😉.” The virus asks for half a Bitcoin (around $1195) and increases this price to 1 BTC in 5 days.
Cerber 6 ransomware virus
Cerber 6 ransomware virus. While a while has passed since the last version of Cerber, the developers used this time to improve and craft this crypto-malware to a new level. The latest version, 6th installment, presents improved anti-sandboxing and anti-VM features. In other words, it is able to avoid detection in virtual machines which complicates the developing counterattack strategies. It is also known to use SFX files, i.e. self-extracting files.
In response to wider public awareness about the distribution of this malware, the felons look for ways how to execute the malware with minimal users’ interference. The use of multiple and diverse hacking techniques explains why Cerber ransomware remains the biggest cyber issue. Besides disguising in spam emails, it also employs exploit kits, trojans, and bugs in well-known program utilities to multiple its damage on the virtual community. At the moment, there is no decryption software released for this version. However, some of our recommended options at the end of the article might be effective.
Magniber ransomware virus
Magniber ransomware virus. This version of crypto-ransomware has been spotted by Michael Gillespie on October 14, 2017. It can be recognized from .ihsdj or kgpvwnr extensions which it adds to encrypted records. The virus was initially called My Decryptor ransomware. Later on, a group of security researchers spotted a massive malvertising attack closely related to Magnitude exploit kit which filters victims based on their geolocation and language used in the computer. The exploit kit targets CVE-2016-0189 vulnerability in Internet Explorer and if the target meets the requirements, infects the system with Magniber virus.
The name of the ransomware derives from Magnitude + Cerber. The malicious virus is surprisingly similar to the latest Cerber malware variants. However, technical similarities are not the only thing that makes security researchers wonder about the origins of Magniber. It appears that Cerber ransomware activity has slowed down during October, which gives the base for thinking that cybercriminals were creating a new and possibly more dangerous ransomware variant.
The malicious software appears to be targeting people from South Korea only. Of course, this location-based ransomware variant can turn to other world countries at any time, so we strongly advise you to protect your computer and create a data backup. This ransomware encrypts files only to demand a ransom via My Decryptor page (accessible via Tor browser) and demands 0.2 Bitcoin ($1100). If the victim decides not to pay, the ransom price increases to 0.4 Bitcoin after 5 days.

Never pay ransom to cybercrooks as you can lose all your money
Close look at Cerber ransomware distribution
Reportedly, malware is currently trying to involve other cybercriminals to join its affiliate network and allows them to distribute this virus however they want. The original developers of Cerber ransomware virus take part of the profit and allow the affiliates to keep the rest of it. Be aware that cybercriminals mostly distribute this virus via spam emails, so make sure you do not open any suspicious emails[8] that come from unknown senders. Even most of such malicious correspondence[9] goes to “Spam” catalog, there is no guarantee that a virus-carrying email will not slip to your regular Inbox as well.
So, you should be particularly careful about opening any attachments that come from unknown sources and are accompanied by suspicious emails. Often the cybercriminals will pose as representatives of governmental or law enforcement institutions, so it is recommended that you always check the legitimacy of such emails if you receive any. Cerber ransomware virus can also enter your computer with the help of Trojans[10].
Therefore, you should avoid untrustworthy download websites because you might download an infected file that has this malicious virus carrier attached to it. Needless to mention, you should avoid visiting high-risk web pages and interacting with the pop-ups and other notifications you may encounter there. The latest ransomware distribution campaign targets vulnerabilities in legitimate software and uses them to push the ransomware into target computers. The only way to protect your PC from being infected is to keep an anti-malware software running at all times.
According to PC experts, misleading emails pushing users to pay the ransoms to prevent the infiltration of Cerber have also been detected. Stay away from such email messages and do NOT even think about making these fines! You need to take care of your company’s safety instead. Make sure you let your employers know about such attacks and install reliable security software.
Ransomware uses Magnitude and other exploit kits to increase its distribution rate
No need to say that, during all these years of distribution, Cerber ransomware has been expanding and looking for new monetization methods. During a massive attack in South Korea[11] and other Asian countries, cyber criminals who are hiding behind this ransomware used Magnitude exploit kit.
When a user visits a malicious website, the malware checks a few details about the virus in order to decide whether it is worth launching the attack or not. These “gates” are known as “Magnigate”[12] and are used to check the user’s IP address, ISP, and the information about the operating system or web browser. In this way, the virus can launch targeted attacks and avoid infiltrating random computers.
As a result, this crypto-virus has been actively attacking companies and their computer networks. Interestingly enough, in addition to Cerber encryption, people hiding behind this virus threaten their victims to launch malicious DDoS attacks[13] that will supposedly disturb the company’s network and its overall operation. Hackers start with the threat email which warns about the upcoming attack and demands to pay a set amount of ransom. After that, the amount of money is said to increase.
Cerber virus is also capable of stealing Bitcoin wallet data
Donoff Trojan downloader is used to extract malicious Cerber’s code
The virus is still actively distributed in December 2016. According to a report from Microsoft, Cerber ransomware is rapidly proliferating with the help of an email spam campaign, which delivers password-protected .zip archives. Typical email subject lines contain words like “Howdy,” “Hi” or “Hello,” and a very short message asking to view contents of the attached file, and providing a password to the attachment. Once extracted, files inside this archive activate malicious macro scripts that download Donoff Trojan downloader, which downloads the ransomware to the computer system.
In addition, it is still actively distributed via RIG exploit kit. The victim only needs to enter a site that hosts an exploit kit to allow it to exploit security vulnerabilities in the system and download the ransomware without the user’s consent. The virus has also been noticed proliferating its copies via compromised websites that host the Nemucod virus. These sites can easily redirect the victim to Pseudo Darkleech, which strongly obfuscates the infection when Nemucod drops Cerber ransomware virus on the victim’s computer system.
Speaking of the virus’ code, we must point out that the virus has changed the font background color from bright green to red. On top of that, the latest version of the virus doesn’t touch Volume Shadow copies[14], which basically are a door to data recovery. With tools like ShadowExplorer, you can restore at least part of the data encrypted by this ransomware virus!
Ransom.Cerber can also abuse Apache Struts 2 vulnerabilities
In April 2017, researchers identified new mutations in the distribution of this virus. This time, people behind Cerber project targeted vulnerabilities in Apache Struts 2 on Windows servers. To begin with, Apache Struts is a free and open-source framework for creating Java web applications. It turns out that malware distributors have been attacking systems running programs created with Apache Struts and setting up backdoors, enrolling devices into DDoS bot network, placing cryptocurrency miners and of course, malicious viruses like ransomware on compromised machines.
The vulnerability in Apache Struts software allowed criminals to target servers instead of individual computers, providing them with chances to reach potential victims that surely have money and most likely are willing to pay up just to get the control of the data back.
The attackers used an exploit code that allowed them to run shell commands and launch BITSAdmin utility, and finally download Cerber ransomware from a remote server. Now, researchers have discovered that this particular piece of ransomware modifies Windows Firewall rules and prevents communication from installed antivirus to the world, making it impossible to install antivirus updates or sending reports to the developer. According to researchers, the Bitcoin wallet address used by this version of the infamous ransomware remains the same.
While the discussion about Cerber ransomware has tied down, users might have let their guard down convinced that the malware has faded into oblivion. Such thinking might be perilous, as the hackers are yet to strike again. Recently specialists have detected this menace hidden in Dropbox files. While in the case of ordinary spam messages, a user still needs to extract the attachment in order to activate the infection.
The developers found a workaround to this feature and spread this crypto-malware via self-extracting Dropbox files. Luckily, they still need to be “clicked” in order to inflict damage. There is another wave of this malware coming: TrendMicro virus report reveals multiple new versions of the threat: Ransom_Cerber.R000C0DD517, Ransom_Zerber.R08NH0CD317, etc. The report also reveals that the latest version is also able to avoid machine learning detection by security applications[15]. Continuous re-loading of the executable files prevents detection. However, specialists reassure that multilayer security software is still a proper solution when dealing with Cerber ransomware virus.
Cerber uses RaaS scheme, meaning that distributors apply different techniques to deliver ransomware; for example, spam email attachments, exploit kits, etc.
Recovering locked data: free Cerber decryptor can help users infected with .cerber and .cerber2 versions
In August 2016, malware researchers managed to find some flaws in the ransomware project and launched a site that allowed victims to decrypt .cerber and .cerber2 files for free. Although authors of this site do not provide any information on how did they manage to defeat the ransomware, some security experts had guessed that they have managed to find out what the Master Decryption Key is. It appears that this was not true, and most likely they have found a flaw in the virus C&C server. Reportedly, hundreds of victims who followed news about the virus managed to decrypt their precious files for free.
Sadly, organized criminals quickly found the flaw and patched it, so as a result, it is no longer possible to decrypt files using this decryption service anymore. What is more, Cerber’s payment site has been improved by adding a Captcha system, which helps to avoid automated attempts to access the site. It seems that this gang is well-organized and determined to keep this virus undefeatable, which is a horrifying fact. Therefore, computer users are advised to take precautions, create data backups and protect computers with proper anti-virus solution to prevent a ransomware attack, because, at the moment, there is no way to recover encrypted data using decryption tools.
No ways to recover other files locked by the infamous virus
Unfortunately, it is impossible to decrypt the files locked by Cerber ransomware without paying the ransom. However, it is not recommended to pay up[16] because:
- It only encourages cybercriminals to continue their fraudulent activities and create more computer viruses;
- Plus, bear in mind that there is NO guarantee cyber criminals are actually going to help you to recover your files;
- You may not receive the decryptor at all, even if you pay up.
- Also, this tool may be corrupted, bring other malware on your computer and this way, damage it even more.
Therefore, you should not collaborate with the cybercriminals on any level, because their main intention is to make money, and they will do their best to make their efforts to pay off.
Deleting the virus from your computer will not help to eliminate the cipher from the files. Trying to recover your files using the hacker-suggested Cyber decryptor tool is not safe either. The best decision is to turn to some more reliable ways to recover your data. The quickest and safest way to achieve that is by importing your data from a backup device.
We strongly recommend you NOT to keep the copies of your data on online storage clouds, because some viruses can access them via your Internet connection and corrupt them, too. It is best to keep your files stored on some external drive and update it regularly[17]. But there are risks here too.
If the external drive is plugged into the computer at the time of the virus infiltration, the files in the storage will most likely be encrypted too. So, make sure that you unplug the external storage device from your computer every time you backup some files. If you do not have a backup, you might want to try these decryption tools – Photorec, Kaspersky virus-fighting utilities or R-Studio.
Keep in mind that you must eliminate the Cerber virus from your device completely before you attempt to recover your files in either of the ways mentioned above. You can do that using anti-malware software like Reimage Reimage Cleaner .
Cerber ransomware removal guide
There is no doubt that Cerber ransomware is one of the most dangerous computer viruses of today. Computer experts are still working to create a decryption tool to help its victims decrypt their files, but, at the time of writing, there is only one legitimate decrypter that should be tried to recover the encrypted files without paying the ransom. It is provided in the “Recover your data” section. Besides, if you are infected and cannot open your files, we suggest you follow optional recovery solutions created by our tech experts to finish Cerber removal from the system.
However, before you try them, make sure you remove Cerber ransomware as soon as possible. Don’t forget that it is a dangerous and well-structured computer threat, so you should opt for a professional malware removal tool to eliminate the ransomware from a victimized computer fully. If the removal procedure did not go as smooth as you expected, you can try the instructions provided below. Once you unblock your virus remover, try scanning your computer again.
This entry was posted on 2020-02-03 at 06:35 and is filed under Ransomware, Viruses.

