RagnarLocker is the self-named cryptovirus that targets enterprises and software companies and claims to share sensitive information
RagnarLocker ransomware is the threat that runs pre-deployment tasks and steals victims’ files before encrypting data on the system, so private information can be uploaded publicly when the ransom is not paid. These attackers behind the threat are aiming to get as much money as possible, so once those files get encrypted, the ransom is demanded. The amount is asked in Bitcoin and can differ from 20 to 60BTC, hence huge companies as their targets.
The recent target of the RagnarLocker virus – VGCARGO got demanded to pay 25 Bitcoins in exchange to get their files restored.[1] Highly-targeted attacks use RSA-2048 encryption and change the original code of various files found on the network. Once that is done custom note gets developed which includes the name of the affected company and specific ransom amount set for the particular victim.
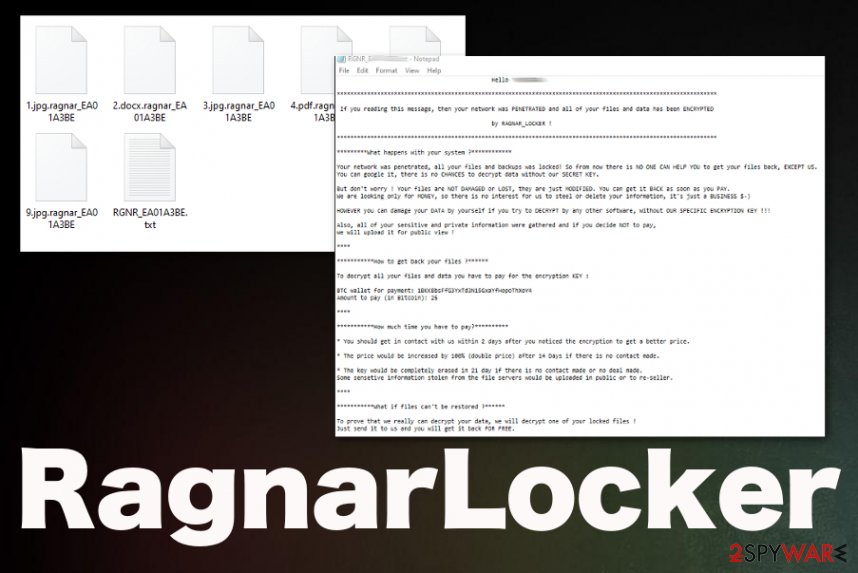
RagnarLocker ransomware virus developers generate the name of this text file according to the extension that is unique for each target and includes .rangnar and file marker. Ransomware terminates and disables various processes, especially security software and functions used for file backups. This particular locker targets remote management software used by managed service providers. Such applications provide remote support for people, so virus terminates any functions to avoid detection and termination of the attack.
| Name | RagnarLocker ransomware |
|---|---|
| Target | Large businesses, enterprises, and software companies |
| File marker | .ragnar_*** or .ragnar_<ID***. Every file extension gets customized and includes particular Id generated for specific target |
| Encryption method | Relies on RSA2048, but also uses the combined AES+RSA algorithm for encryption processes |
| Contact email | [email protected] |
| Ransom note | The note including contact information and further instructions contains the personalized message and gets named in the same pattern as the file marker RGNR_***.txt or RGNR_ .txt |
| Ransom amount | Differs from 20 to 60 Bitcoin |
| Distribution | Spam email campaigns include malicious files that trigger the drop of a ransomware executable that launches the encryption immediately. Legitimate looking emails state about financial data or notifications from known companies or services |
| Unique functions | Attackers claim to steal data before encrypting files, so they can additionally blackmail people into paying the ransom. It is not known if that really happens, but such a feature becomes common for enterprise-targeting ransomware threats |
| Elimination | You need to get a proper anti-malware tool for RagnarLocker ransomware removal, so all the related files and malicious applications can be deleted completely from the machine |
| Repair | Malware like this can make big changes and damage crucial places of the OS, so you should repair these issues with the help of a proper system tool or cleaner like Reimage Reimage Cleaner |
There are no sources that completely confirm the relation between RagnarLocker ransomware and Ragnarok ransomware, but the name, tactics, and similarities are there. Both threats target companies, use similar patterns of extensions and ransom notes. The Locker may be a new and improved version of the first version that targeted Citrix and got discovered at the end of 2019.
RagnarLocker ransomware developers claim that they have some pre-deployment tasks that get executed before encrypting files found on the system. One of the processes involves stealing personal data and storing particular files on their servers, so when the victim is refusing to pay the demanded amount, all those details get released publicly, exposing valuable and sensitive data.
When criminals are ready, the main function of RagnarLocker ransomware is started – file encryption. In most cases, RSA-2048 is the method used for the file-locking. Before encrypting virus checks the location of the affected devices, so people from Russia, Azerbaijan, Armenia, Georgia, Kazakhstan, Kyrgyzstan, Moldova, Tajikistan, Turkmenistan, Uzbekistan, and Ukraine can be excluded.
RagnarLocker ransomware also checks Windows services running on the machine, so processes with certain strings can be stopped. This is the common method used by threats like this because it is the method that helps to avoid virus detection and termination. These strings include:
- vss
- sql
- memtas
- mepocs
- sophos
- veeam
- backup
- pulseway
- logme
- logmein
- connectwise
- splashtop
- kaseya.
These activities and additional features that malware has, affect the persistence and processes like RagnarLocker ransomware removal significantly. Also, since recovery options, software, and features get disabled, it becomes more difficult to recover after the attack. Unfortunately, the malware runs WMIC.exe shadowcopy delete command and removes Shadow Volume Copies that can be useful for file restoring. 
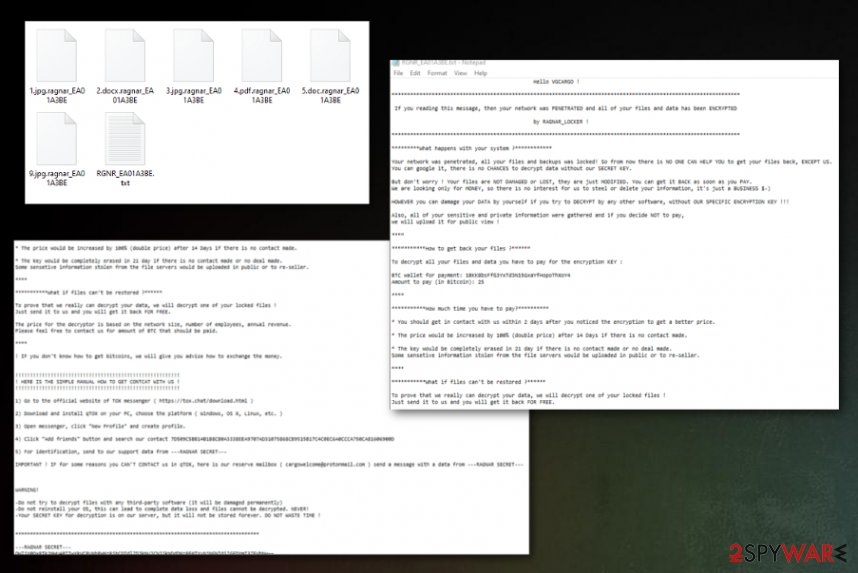
RagnarLocker ransomware – a virus that shows the personalized ransom note on the screen after the encryption process.
RagnarLocker ransomware – a virus that shows the personalized ransom note on the screen after the encryption process.
Unfortunately, RagnarLocker ransomware is one of the most dangerous threats that can be found on the internet because these attacks involve money extortion.[2] Since money is the main goal of such threats, large targets are more attractive. There are no vulnerabilities in the coding and encryption methods, so this threat cannot be decrypted.
You need a proper anti-malware tool that could detect and terminate the virus for you. When it comes to enterprises, professional security experts need to remove RagnarLocker ransomware completely off of the network since any connected device can get affected by the virus or even damaged.
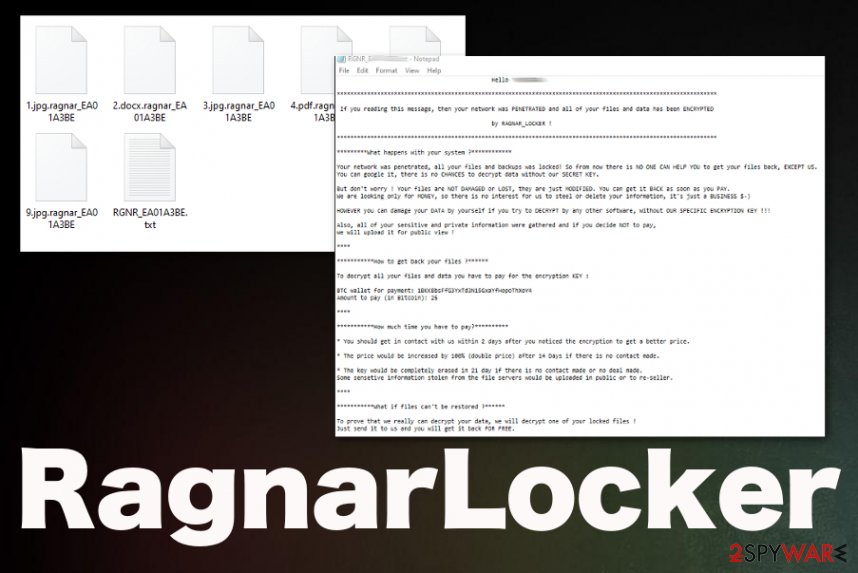
When the encryption is successfully done, RagnarLocker ransomware creates a unique ransom note and releases the personalized message for the people from the affected company. The message states about encryption, cryptocurrency addresses, contact information. Also, developers provide TOX chad ID that should help to communicate with them and the email address, but the first one is not working.
RagnarLocker virus ransom note:
Hello * !
********************
If you reading this message, then your network was PENETRATED and all of your files and data has been ENCRYPTED
by RAGNAR_LOCKER !********************
*********What happens with your system ?************
Your network was penetrated, all your files and backups was locked! So from now there is NO ONE CAN HELP YOU to get your files back, EXCEPT US.
You can google it, there is no CHANCES to decrypt data without our SECRET KEY.But don’t worry ! Your files are NOT DAMAGED or LOST, they are just MODIFIED. You can get it BACK as soon as you PAY.
We are looking only for MONEY, so there is no interest for us to steel or delete your information, it’s just a BUSINESS $-)HOWEVER you can damage your DATA by yourself if you try to DECRYPT by any other software, without OUR SPECIFIC ENCRYPTION KEY !!!
Also, all of your sensitive and private information were gathered and if you decide NOT to pay,
we will upload it for public view !****
***********How to get back your files ?******
To decrypt all your files and data you have to pay for the encryption KEY :
BTC wallet for payment: *
Amount to pay (in Bitcoin): 25****
***********How much time you have to pay?**********
* You should get in contact with us within 2 days after you noticed the encryption to get a better price.
* The price would be increased by 100% (double price) after 14 Days if there is no contact made.
* The key would be completely erased in 21 day if there is no contact made or no deal made.
Some sensetive information stolen from the file servers would be uploaded in public or to re-seller.****
***********What if files can’t be restored ?******
To prove that we really can decrypt your data, we will decrypt one of your locked files !
Just send it to us and you will get it back FOR FREE.The price for the decryptor is based on the network size, number of employees, annual revenue.
Please feel free to contact us for amount of BTC that should be paid.****
! IF you don’t know how to get bitcoins, we will give you advise how to exchange the money.
!!!!!!!!!!!!!
! HERE IS THE SIMPLE MANUAL HOW TO GET CONTCAT WITH US !
!!!!!!!!!!!!!1) Go to the official website of TOX messenger ( hxxps://tox.chat/download.html )
2) Download and install qTOX on your PC, choose the platform ( Windows, OS X, Linux, etc. )
3) Open messenger, click “New Profile” and create profile.
4) Click “Add friends” button and search our contact *
5) For identification, send to our support data from —RAGNAR SECRET—
IMPORTANT ! IF for some reasons you CAN’T CONTACT us in qTOX, here is our reserve mailbox ( * ) send a message with a data from —RAGNAR SECRET—
WARNING!
-Do not try to decrypt files with any third-party software (it will be damaged permanently)
-Do not reinstall your OS, this can lead to complete data loss and files cannot be decrypted. NEVER!
-Your SECRET KEY for decryption is on our server, but it will not be stored forever. DO NOT WASTE TIME !********************
—RAGNAR SECRET—
*
—RAGNAR SECRET—********************
Paying the ransom is never the best answer, experts[3] always note that there is no need to even consider paying the amount that RagnarLocker ransomware or any other cryptovirus creators ask of you. You can get additional malware sent to you via the email or asked to pay more after one transfer.
Even though RagnarLocker ransomware mainly targets large companies and is focused on English-speaking people it can freely get on everyday user devices in any country all over the world, so you should be extremely cautious and pay attention to all the listed features and tips that we gathered. Rely on the anti-malware tool and scan the machine if you noticed any similar symptoms. If needed, get a PC repair program like Reimage Reimage Cleaner and get rid of the virus damage. 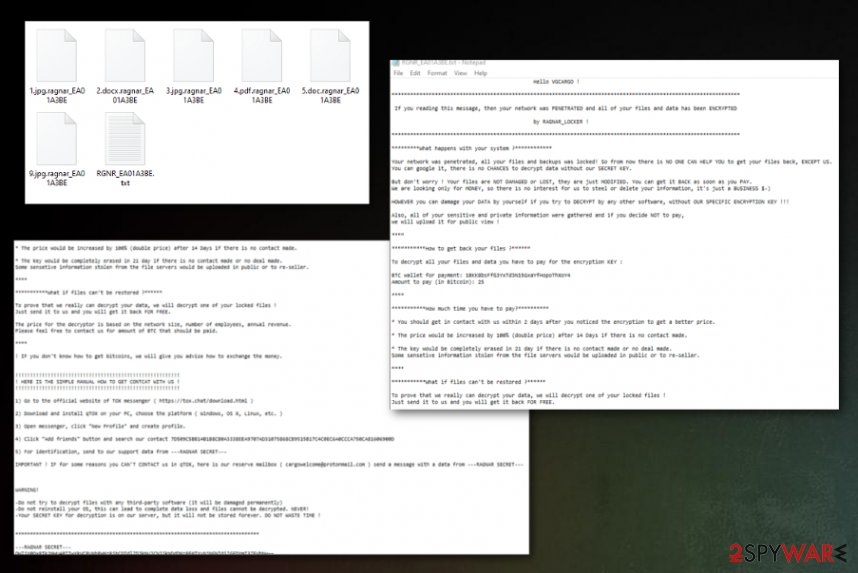
RagnarLocker ransomware is the cryptovirus that configures a particular extension for encoded data that includes .ragnar and unique code. After this, the same pattern with victims’ ID is used to name the ransom note file.
RagnarLocker ransomware is the cryptovirus that configures a particular extension for encoded data that includes .ragnar and unique code. After this, the same pattern with victims’ ID is used to name the ransom note file.
Stay away from emails with attached files
Email campaigns spread a handful of different threats and can lead to various malware infections when you don’t pay enough attention to the content and sources of the notifications. In most cases, those emails may seem legitimate and safe when the sender is a particular service or company that you know and trust. Don’t fall for such tricks.
Pay attention to the particular sender and the type of files attached. Financial information, order details, receipts, and other sensitive data shouldn’t end up on your email box when you don’t use the service. So keep suspicions and avoid opening emails that are not expected.
Malicious macros can get loaded on these MS files and similar data that gets attached to safe-looking emails. Once the file is downloaded and opened on the machine, the suggestion to enable additional content shows up on the screen. After that, the malicious script gets loaded on the computer, and encryption starts. Delete emails without clicking on any links or attachments.
You need a clean system before you can do anything related to RagnarLocker virus encrypted files
You need to note that RagnarLocker ransomware virus is not only affecting large companies but also can get on devices of users all over the globe without any effort. This is more dangerous because of the advanced methods and techniques used by the threat actors.
The most important thing is the fact that malware gets persistent due to all the additional changes in system folders, settings and added programs, entries on the registry, and so on. For that reason, you not only need to remove RagnarLocker ransomware, but you should also repair those issues and get rid of the virus damage.
Get SpyHunter 5Combo Cleaner, or Malwarebytes for the proper RagnarLocker ransomware removal and then run Reimage Reimage Cleaner as a PC repair application and clean any traces or fix affected parts of the malware. Make sure to pay attention to the AV tool delivered results and detection rates, follow the suggested steps and clean possible intruders. You need to get back to a properly cleaned machine before you even consider file restoring.
This entry was posted on 2020-02-19 at 07:03 and is filed under Ransomware, Viruses.

