Koti is the 226th Djvu ransomware family member that emerged in the middle of May 2020
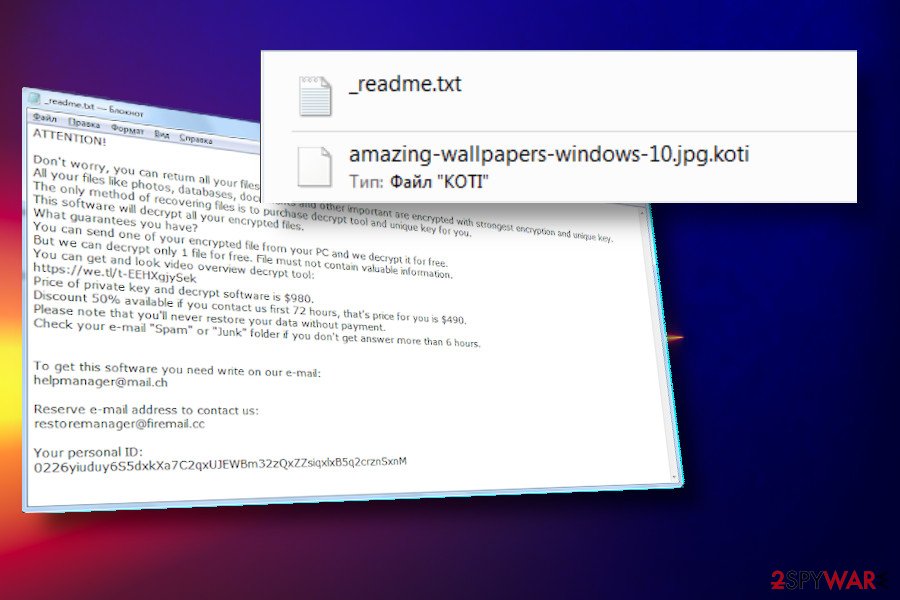
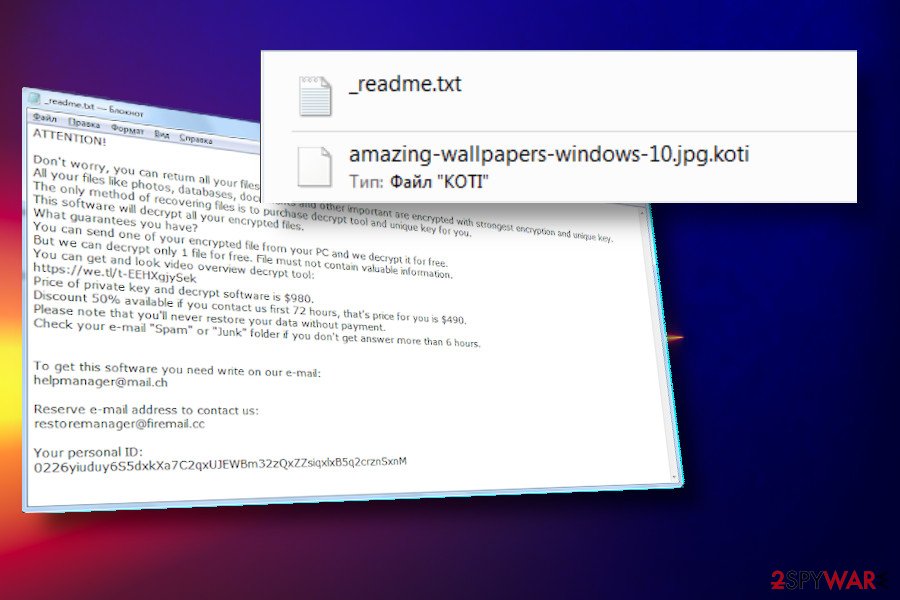
Koti ransomware is the latest version of the infamous Djvu family of crypto-malware. Resurfaced in the middle of May 2020, it takes the 226th position in the list of STOP/Djvu variants and stands in line with .mpal, .sqpc, and .mzlq entries. Alike its predecessors, Koti ransomware uses RSA encryption model to lock non-system files and uses a standard _readme.txt ransom note. Besides, it is using the .koti file extension to separate encrypted documents, pictures, videos, photos, databases, archives, and other data from the others.
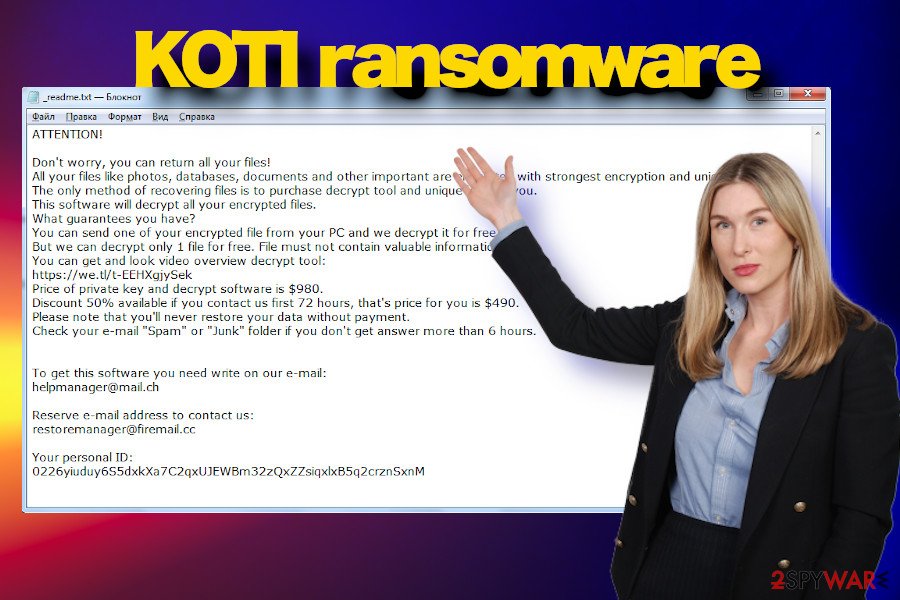
The criminals behind Koti ransomware are using the [email protected] and [email protected] emails for contacts. Apparently, they are using the same extortion scheme as the victims are demanded to pay the $980 in Bitcoins as a ransom for a decryptor, though promise to double down the price if the payment comes within 72 hours.
| Name | Koti |
| Family | The infamous group of STOP / Djvu ransomware |
| Detection | May 2020. The first ransomware sample has been uploaded into the official Emsisoft’s support[1] site |
| Classification | The Koti virus falls for the ransomware or file-encrypting malware group |
| Version number | This ransomware is currently the latest djvu version, which stands 226th in the list |
| File marker | The viruses uses .koti file extension to mark locked files |
| Encryption model | RSA |
| Distribution | This extortionist is typically distributed via malicious e-mail message attachments, unprotected RDP ports, P2P networks, or pirated software |
| Other traits | One the payload is launched, the ransomware locks files and drops a ransom note _readme.txt, which contains a detailed guide on how to pay the ransom |
| Payment conditions | Criminals urge victims to pay $490 if the payment is transferred within 72 hours. If the victim delays the payment, the price is doubled and reaches $980. The only currency accepted – Bitcoin. |
| Detection | It is not possible to detect malicious ransomware files manually. The detection and removal of the intruder is possible with a professional AV engine. |
| Damage | The ransomware removal does not ensure full recovery of the affected system files. To fix Windows registry entries, boot files, and other core components, use Reimage Reimage Cleaner Intego utility. |
Koti ransomware has been expected to manifest in May, since Djvu ransomware is infamous for its regular release of renewed versions. The first sample of this virus has been uploaded into Emsisoft’s support forum where the victim presented the _readme.txt file accompanied by a file locked by .koti file extension.
A close investigation proved the evidence of Koti to be rooted from Djvu ransomware family. It uses a similar base for the distribution, infiltration, encryption, and extortion. According to researchers, its payload is typically distributed via obfuscated spam email attachments or pirated software. Besides, it may also be used for spreading the infamous AZORult trojan as a secondary payload.
Upon successful infiltration, the ransomware begins the first phase of the deployment. The malware settles down multiple boot processes, launches PowerShell to delete Shadow Volume Copies, and disables the AV engine to evade immediate removal. Koti ransomware may also corrupt Windows host files and establish firewall access to security-related forums and websites containing guidelines on how to remove the ransomware and recover damaged files.
This cyber infection is not a threat to mess with as it may cost you a permanent file loss. The best solution for its victims is a full Koti ransomware removal using a program like SpyHunter 5Combo Cleaner, Malwarebytes, or another professional antivirus tool. This file-encrypting virus can not only encrypt the data on the host machine, but also plant multiple malicious files, compromise the system severely, and download the Azorult trojan as a secondary payload. Consequently, criminals may get access to your personally identifiable information (PII)[2], including saved passwords, banking information, login details, etc.
The changes that the Koti ransowmare initiates can hardly be overlooked. Initially, it starts running malicious processes within Task Manager, which is why CPU usage may increase significantly. The most obvious sign indicating ransomware infection is the .koti file extension appended to the pictures, archives, Microsoft Office documents, videos, and other non-system files.
Koti ransomware is a dangerous file-locking virus that appends .koti file extension to encrypted files and demands victims to pay the ransom
Koti ransomware is a dangerous file-locking virus that appends .koti file extension to encrypted files and demands victims to pay the ransom
As a final point, the virus creates a _readme.txt ransom note on the random system’s folders and the desktop. The note contains the detailed instructions on how to contact ransomware developers and how to transfer the ransom. In short, the victims are expected to contact the crooks via the [email protected] and [email protected] emails and transmit a ransom, which varies from $480 to $980 in Bitcoins.
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-EEHXgjySek
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]Your personal ID:
Indeed, criminals who promote this ransomware virus expects to extort as much money as possible. However, our biggest piece of advice is to remove Koti ransomware in the first place and then try to recover files using third-party software. Do not get scared by claims that you will lose the files permanently by running an AV scan. Criminals use such and similar scare tactics to catch victims on the hook.
After full Koti ransomware removal, you can start thinking about a recovery of the encrypted data. Since Djvu is one of the largest ransomware families on the surface, cybersecurity experts have invested much time to develop a free decryption software. At the moment, the Dr. Web Rescue Pack is probably the most reliable tool for retrieving files. However, not all Djvu variants can successfully be crashed by this tool. In case of a failure, try alternative data recovery methods listed at the end of this article.
Methods that criminals engage for ransomware distribution
Experts from LosVirus.es[3] provided us with their findings on the methods that cybercriminals are typically using to spread ransomware infections. According to them, the most popular medium to spread malicious payloads is spam. Hackers craft reliable-looking email messages mimicking the style of various companies (DHL, FedEx, White House, Red Cross, etc.) and disguise ransomware under infected “order confirmations” or similar attachments.
Nevertheless, spam email attachments are not the only ransomware transmitters. Crooks often exploit vulnerable Remote Desktop Protocol (RDP) network connections and use brute-force attacks to infect target systems. The TCP port 3389 is one of the most frequently exploited vulnerabilities allowing criminals to easily attack potential victims. P2P networks, illegal or hacked websites, software cracks, keygens, and other online content that can easily be exploited by hackers.
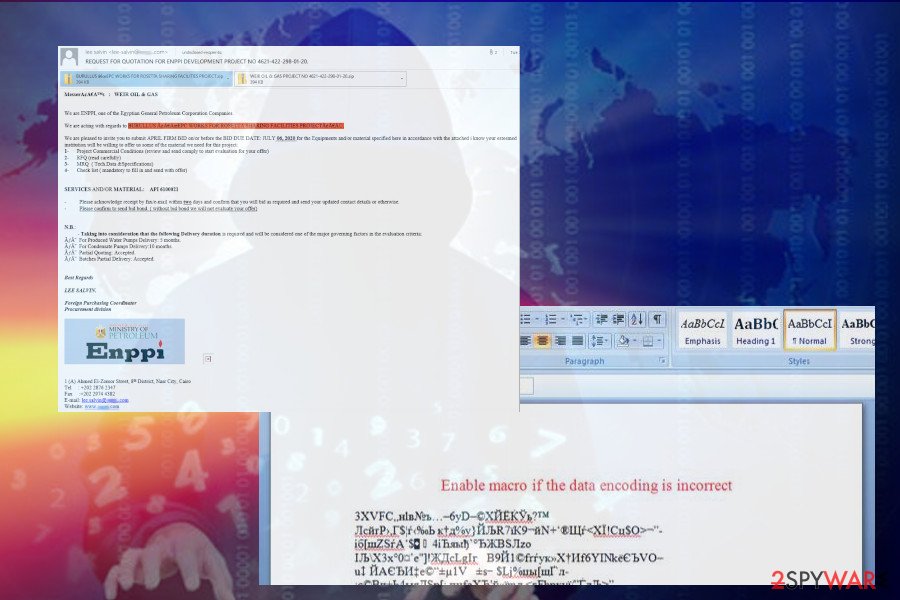
Koti ransomware is typically distributed via malicious spam email attachments
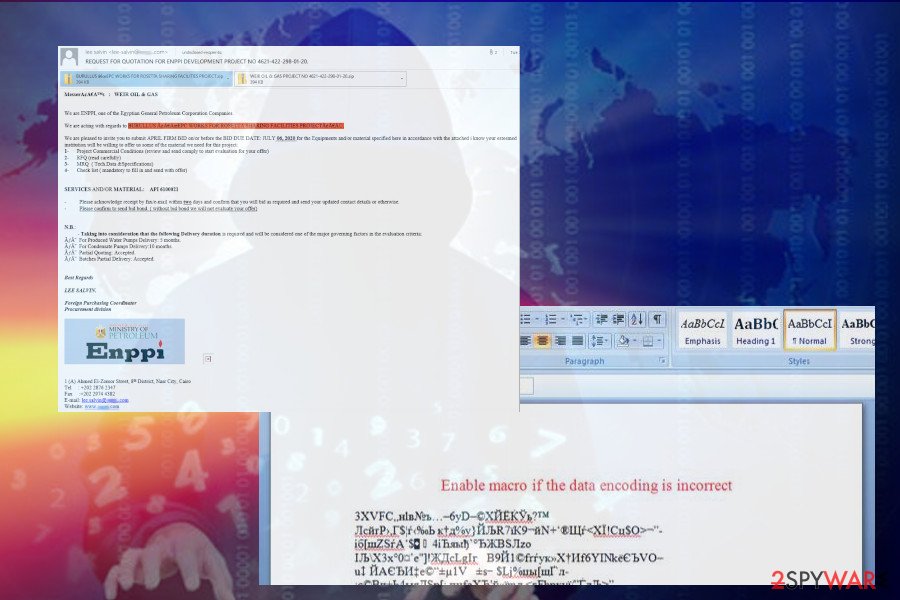
Koti ransomware is typically distributed via malicious spam email attachments
Thus, having an anti-virus program installed is not sufficient to protect the system from malware. A user’s consciousness is equally important. First of all, people should start taking care of the backups, at least backup the most important data, such as documents or family photos. Second of all, think twice before downloading illicit software or visiting potentially dangerous domain.
Use a professional AV engine to remove Koti ransomware
Koti ransomware removal requires the usage of a powerful antivirus program. If you’ve ever dealt with a ransomware-type virus, you should know that manual removal is not possible under any circumstances. File-encrypting viruses are built in a very comprehensive manner as they infiltrate tens of malicious files in diverse system’s places to make Windows conform to malicious commands.
Before any attempts to remove Koti ransomware, we recommend copying encrypted files to alternative storage, bet it USB flash drive or cloud. That’s a necessary precautionary measure to prevent permanent loss of files encrypted by .koti file extension.
For a full Koti removal use SpyHunter 5Combo Cleaner, Malwarebytes or an alternative AV engine of your preferences. After that, try to recover the data using the recovery solutions provided below.
Remove Koti using Safe Mode with Networking
Since the malicious files run by Koti ransomware can block antivirus programs, you may need to reboot the system into Safe Mode to enable the security program.
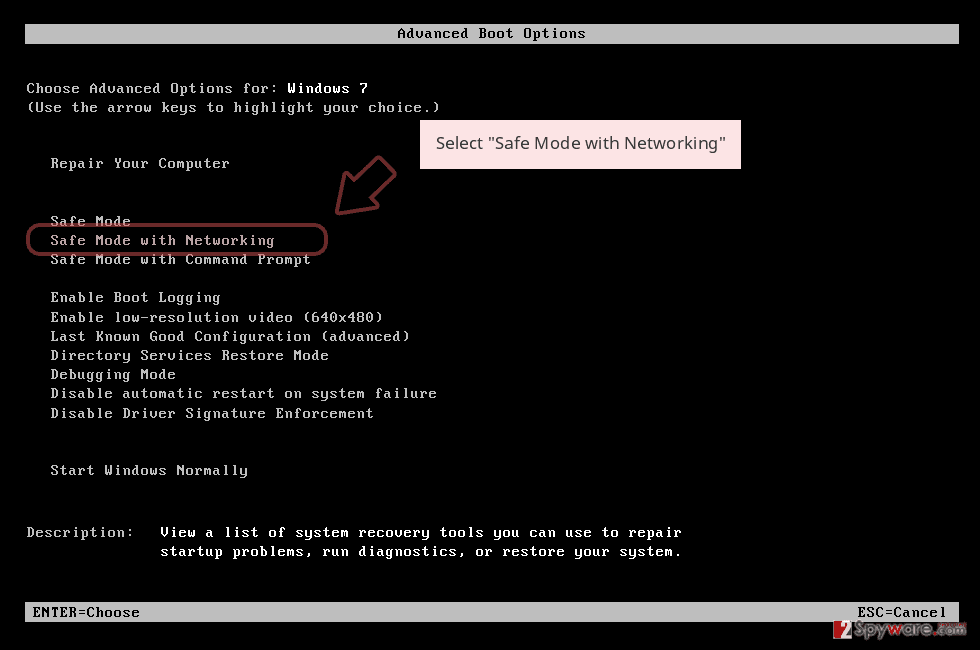
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
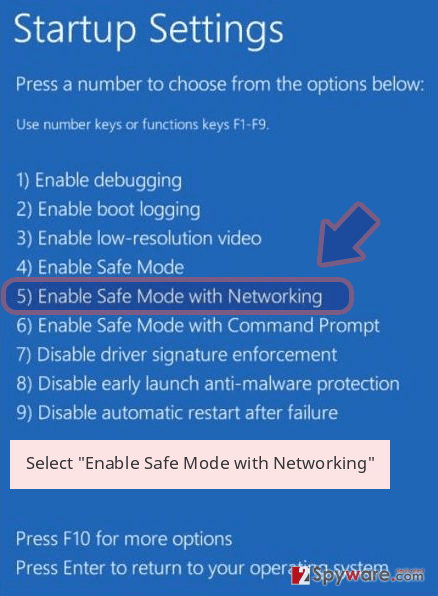
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Koti removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Koti using System Restore
Use these steps to activate System Restore and prevent all malicious activities from continuation
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Koti from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
Unfortunately, the official Koti decryptor hasn’t yet been developed. Nevertheless, there’s a handful of options that you can try to recover data compromised by this malicious virus.
If your files are encrypted by Koti, you can use several methods to restore them:
Run a scan with a Data Recovery Pro
Data Recovery Pro is a program that may help to retrieve at least a part of the documents damaged by ransomware. Nevertheless, before launching it, make sure that you have initiated a successful Koti removal.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Koti ransomware;
- Restore them.
Try Windows Previous Version feature
If you have had enabled the Windows Previous Version feature on your PC, then try getting your files back using this software.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Recover files from Volume Shadow Copies
It is known that most of Djvu ransomware variants are programmed to remove Volume Shadow Copies. Nevertheless, it’s not clear if Koti ransomware virus deletes these copies, so if none of the previous recovery options helped, give Volume Shadow Copies a try.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No official Koti decrypted available
Since Koti is a fresh cyber infection, researchers did not manage to create a decryption software for it. Nevertheless, it’s advisable to try a DrWeb Rescue Pack.
Moreover, a member of the ransomware hunters team called DemonSlay355 launched a free STOPdecryptor, which can help people decrypt some of the Djvu variants that have a personal ID number 6se9RaIxXF9m70zWmx7nL3bVRp691w4SNY8UCir0. If such a number has been generated for you by Koti ransomware, you can download a decryptor from here.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Koti and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-05-18 at 05:09 and is filed under Ransomware, Viruses.

