Eking ransomware – locks files and demands victims to pay a ransom within 24 hours
Eking ransomware is a malicious file-encrypting virus that has been discovered on the surface on May 17th, 2020. According to the researchers[1], the virus is being distributed via torrenting websites bundled with Adobe Acrobat crack. Once the malicious payload is launched, the Eking starts the first phase of the attack, i.e. injects malicious .exe processes and gains administrative privileges over the system. The second phase is related to file encryption. For locking up victim’s files, criminals behind this ransomware uses AES encryption and id.[[email protected]].eking appendix.
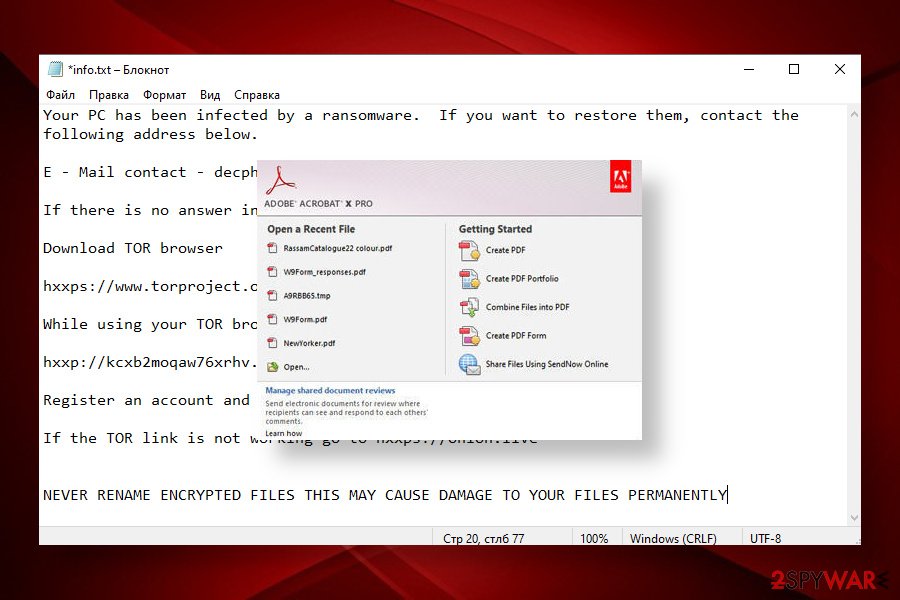
Eking ransomware virus genealogically stems from the infamous Phobos ransomware family, which has over 20 members, including Mamba, Phoenix, and ISO ransomware. Just like the predecessors, it mimics the notorious file-encrypting viruses from the Dharma family. It uses an identical style for a ransom note and provides word-to-word the same instructions on it. At the moment, the Eking virus creates a pop-up window info.hta or a text file info.txt in every folder that contains locked files. The file contains two emails for contacts: [email protected] and [email protected]. However, neither contacting criminals nor paying the ransom is recommended.
| Name | Eking |
| Geneology | The virus belongs to the Phobos ransomware family |
| Classification | Ransomware / File-encrypting virus |
| Encryption | Based on the Phobos family history, Eking is believed to be using AES cipher to encrypt files on an infected machine |
| File extension | The ransomware uses .eking extension to mark locked files. Typically the extension is preceded by a victim’s ID and [email protected] email in the square brackets |
| Ransom note | The ransom note looks identical to the one used by Dharma variants. It manifests in a form of a pop-up window named info.hta or a text file info.txt |
| Contact emails | [email protected] [email protected] |
| Distribution | At the moment, the virus is most actively distributed via torrent websites bundled with Adobe Acrobat crack. However, ransomware managers can also exploit open RDPs or spread the payload via malicious spam attachments |
| Elimination | The only possibility to remove the ransomware from the system is a thorough scan with a professional AV engine |
| File decryption | Unfortunately, there’s no official Eking decryptor. You can try alternative data recovery solutions that we have listed below this article or try to contact reputable ransomware researchers for help |
| Fix tool | The damage that the ransomware does to the system is huge and leading to Windows system errors. To fix such damage, use tools like Reimage Reimage Cleaner Intego repair software |
The .eking file extension virus has been detected as the latest Phobos variant. The user who is considered to be the first victim of this ransomware reported that he’s downloaded some software, a crack for Adobe Acrobat[2] specifically, and soon after that files, such as photos, videos, documents, etc. got locked with the id.[[email protected]].eking affix manifests on of their titles.
The Eking ransomware virus also displays a ransom note, which, as we have already pointed out able, is similar to the one displayed by Dharma. Victims may see a pop-up info.hta, which states the fact of an attack, provides contact information, ID number, and instructions on how to purchase Bitcoins. In addition, it may generate an info.txt file in every folder that contains encrypted data. The Eking ransom note contains the following information:
Your PC has been infected by a ransomware. If you want to restore them, contact the following address below.
E – Mail contact – [email protected] / [email protected]
If there is no answer in 24 hours. Try to contact us via Sonar.
Download TOR browser
hxxps://www.torproject.org/download/
While using your TOR browser copy and paste the URL below:
hxxp://kcxb2moqaw76xrhv.onion/
Register an account and message us in our ID : decphob
If the TOR link is not working go to hxxps://onion.live
NEVER RENAME ENCRYPTED FILES THIS MAY CAUSE DAMAGE TO YOUR FILES PERMANENTLY
The size of the redemption is not clear, though it may vary from $300 to $5000 in Bitcoins. However, paying the ransom is not recommended due to identity theft and other harm that hackers can cause. Instead, render the most powerful AV tool and remove Eking ransomware from your PC. Based on the VirusTotal[3] information, 47 AV engines out of 72 detect ransomware files a malicious. These are examples of AV detections:
- Trojan.GenericKD.33855769
- Malware@#jur7x0zvg9ce
- A Variant Of MSIL/Kryptik.VYW
- HEUR:Trojan-PSW.MSIL.Agensla.gen
- ML.Attribute.HighConfidence
- Win32:PWSX-gen [Trj]
- Gen:NN.ZemsilF.34110.vm0@aOGvnLi
- Trojan.GenericKD.33855769 (B), etc.
Eking ransomware is extremely dangerous not only because of the aggressive compromisation of personal files. Before running the cipher, the virus includes a malicious module into the Windows Task Manager and injects intrusive entries into the Windows Registry. Moreover, it alters the Windows boot sequence and provides itself administrative privileges. This way, criminals weaken the system’s security, diminishes its performance, and can misuse the breach as a backdoor for other malicious viruses (trojan, RAT, or spyware).
Moreover, the Eking virus might initiate alterations on the security system, thus preventing AV programs from detecting it. In this case, the removal of the virus requires rebooting the system into Safe Mode with Networking or enabling System Restore. While in Safe Mode, use reliable antivirus software, for instance, Malwarebytes or SpyHunter 5Combo Cleaner to scan the machine and delete all malicious entries.
Once you remove Eking ransomware from the system, investigate all the methods that could be applied for data encryption. If you have backups, then a ransomware attack is not a big deal for you. If unfortunately, there are no backups, you can try third-party data recovery software or contact the ransomware researchers and ask them for help because there’s no free Eking decryptor developed, at least not yet.

Eking ransomware is one of the Phobos family members that resurfaced in May 2020. Victims reported it hidden under software cracks shared on torrenting sites

Eking ransomware is one of the Phobos family members that resurfaced in May 2020. Victims reported it hidden under software cracks shared on torrenting sites
Finally, do not leave the system vulnerable after the Eking ransomware removal. As we have pointed before, the virus initiates a multitude of malicious activities on the system, which can lead to BSODs, errors, slowdowns, or infiltration of other malware. Optimize the system with Reimage Reimage Cleaner Intego to restore its stability.
Tricky methods are used to disseminate ransomware viruses across the globe
Cybersecurity experts from Dieviren.de[4] claim that the bulk of ransomware infections steam from phishing emails and their malicious attachments (macros). These attachments are usually non-suspicious looking PDF files, Microsoft Office documents, and similar. The content of the message may mimic reputable banking, shipping, or healthcare companies. However, each time when the inbox gets a new message with an attachment, it’s advisable to do the following:
- look for mistakes (grammar, typo, logic, etc.)
- double-check the sender
- scan the attachment with an anti-virus program
However, phishing emails are not the only way to transmit malware. In many cases, computers get infected after downloaded software from peer-to-peer networks. This applies to software, such as cracks, keygens, and similar illicit content. Therefore, it’s important to very cautiously when using third-party torrenting services, such as The Pirate Bay. Also, do not forget to protect RDP configuration if you are using such service because remote desktop apps are also frequently exploited by criminals. Make sure to password protect the RDP and use as strong password as you can come up with.
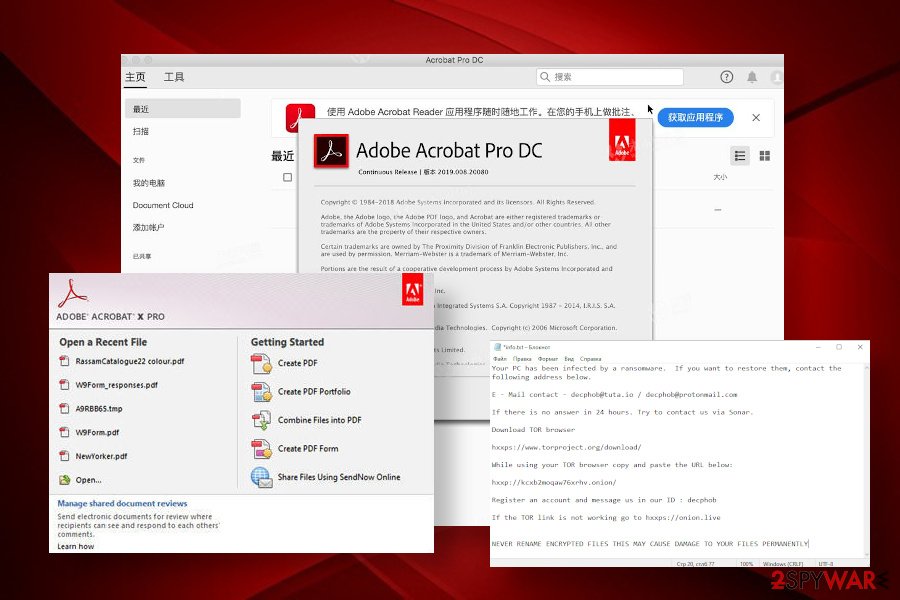
Eking ransomware virus is currently distributed via infected Adobe acrobat crack, which is shared by unknown people on torrenting websites
Eking ransomware virus is currently distributed via infected Adobe acrobat crack, which is shared by unknown people on torrenting websites
Eking ransomware removal methods
Eking ransomware should be removed from the system as soon as you notice suchlike extension appended to your files. Don’t forget that ransomware viruses are often supplemented with multiple payloads, so the longer it stays on the system, the more risk arises to get a trojan or spyware infection in the background.
Besides, it’s important to remove Eking virus before any attempts to recover locked files. Otherwise, the ransomware may strike again and re-encrypt the data. Elimination of this virus requires purchasing a full package of a really professional anti-virus program. We recommend using these tools: SpyHunter 5Combo Cleaner or Malwarebytes.
Also, upon Eking removal scan the system with Reimage Reimage Cleaner Intego to restore its technical side to the state prior to the attack. Only after that take action to retrieve data that the virus encrypted. For that, you can use a decryption tutorial submitted by our security experts.
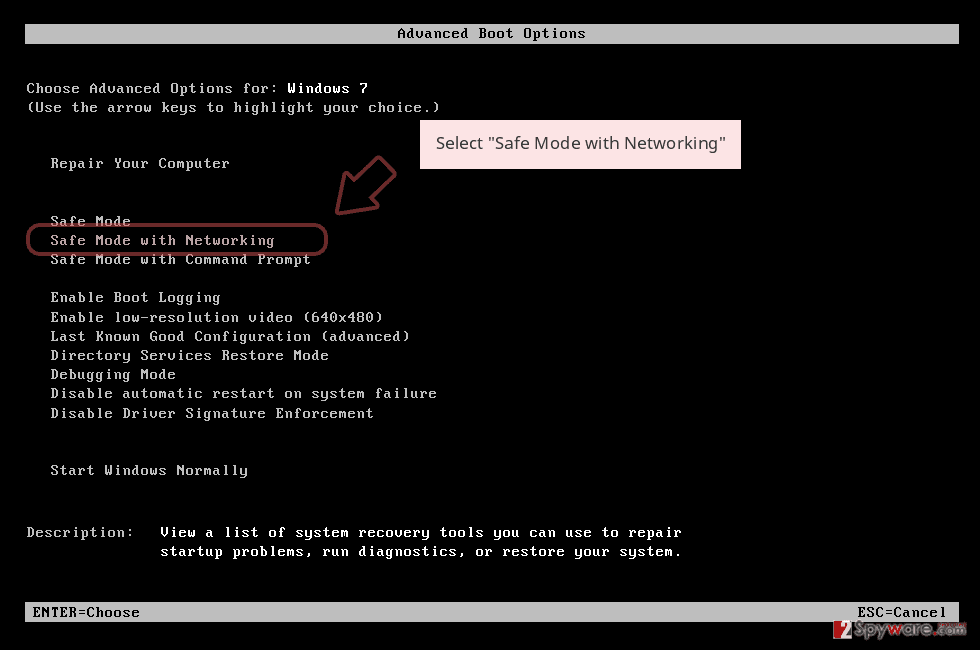
Remove Eking using Safe Mode with Networking
The ransomware may run specific processes within Task Manager that interfere with AV processes and prevent it from launching. In this case, restart the system into Safe Mode to launch the scanner.
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
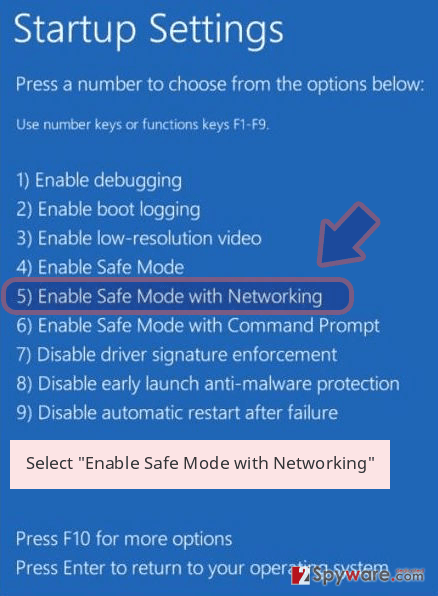
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Eking removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Eking using System Restore
To remove all malicious settings on your machine and return it back to its previous state, you should activate the System Restore feature as explained below.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Eking from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your data got encrypted by Eking ransomware, do not fall for paying the ransom since no one can guarantee that paying will be the end of the problem. Instead, you should remove the virus and try alternative data decryption methods.
If your files are encrypted by Eking, you can use several methods to restore them:
Data Recovery Pro may help to retrieve many of the encrypted files
Although Data Recovery Pro software has been developed for data recovery after the Windows crash, it has been tested with ransomware viruses and showed capabilities to unlock parts of data.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Eking ransomware;
- Restore them.
Take advantage of the in-built Previous Versions feature for data recovery
Previous Version feature allows Windows users to restore the settings of the system to a particular date. However, this feature won’t work if you didn’t have it enabled before.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Shadow Explorer software can very helpful when trying to restore files after ransomware attacks.
Eking ransomware might run specific PowerShell commands that delete the Shadow Volume Copies of the files. Nevertheless, it’s not yet clear whether it enables these commands or not, so at least try to recover some files using Shadow Explorer.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Unfortunately, there’s no way to decrypt files encrypted by Eking ransomware virus for free.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Eking and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-05-20 at 06:05 and is filed under Ransomware, Viruses.

