BitPyLock ransomware is the threat demanding thousands of dollars from victims and promising to recover the encrypted files after
 BitPyLock ransomware – cryptovirus that encoded data and makes files useless, so there is a reason behind ransom demand. The particular encryption algorithms allow changing the original code of photos, videos, documents, audio files, and archives, so when people notice data marked with .bitpy appendix, they can now why the ransom demanding message got placed on the Desktop. Malicious actors deliver the blackmail message on the program window named # HELP_TO_DECRYPT_YOUR_FILES #.html and expect to get 0.8 Bitcoin payment by ensuring that victims will get their files back after the money transfer.
BitPyLock ransomware – cryptovirus that encoded data and makes files useless, so there is a reason behind ransom demand. The particular encryption algorithms allow changing the original code of photos, videos, documents, audio files, and archives, so when people notice data marked with .bitpy appendix, they can now why the ransom demanding message got placed on the Desktop. Malicious actors deliver the blackmail message on the program window named # HELP_TO_DECRYPT_YOUR_FILES #.html and expect to get 0.8 Bitcoin payment by ensuring that victims will get their files back after the money transfer.
Unfortunately, such promises rarely become a reality, so trusting BitPyLock ransomware virus developers is not advised by any experts.[1] Especially when encryption relies on two powerful algorithms, it is not believed that criminals care about your belongings or the state of files.[2] Decryption is not possible for this strain, so you can only rely on file backups or third-party software designed to decrypt or at least recover files. It may be the case, that virus is in development, and researchers will offer the program for such affected files in the future. So you can store virus-related files on an external device, get rid of the ransomware traces left on the machine with proper AV tools, and wait for the possibilities while using the safe machine.
| Name | BitPyLock ransomware |
|---|---|
| File marker | .bitpy – the appendix that appears at the end of every affected file after the original file extension. This is the sign that file is unreadable because of file-locking |
| Encryption algorithms | AES-256 and RSA-2048[3] |
| Ransom note | # HELP_TO_DECRYPT_YOUR_FILES #.html – program window showing all the needed instructions and informing the victim about all the possibilities. This is the file that determines contact information, a particular amount of money that the user needs to pay and provides the cryptocurrency wallet address |
| Ransom amount | 0.8 Bitcoin |
| Contact emails | [email protected] |
| Distribution | Files with malicious code get attached as invoices, receipts, and other information on emails posing as notifications from legitimate services and companies. Other malware, trojans or worms can deliver this virus directly on the machine |
| Elimination | To remove BitPyLock ransomware once and for all, you need to get a proper AV tool that can detect[4] virus traces and malicious behavior-based programs |
| Repair | When ransomware gets on the machine, it alters settings and preferences to keep the malware running longer, so you should go through those changes and reverse them. Reimage Reimage Cleaner or a similar PC tool might do that for you automatically |
BitPyLock ransomware is the new strain of malware that focuses on file-locking and blackmailing. This is the virus that focuses on a common type of data like documents, photos, videos, databases, archives, or audio files. All potential files get encoded immediately after infiltration, so the ransom-demanding message can be quickly delivered.
Once that is done, and BitPyLock ransomware developers have already asked for money, additional system settings get changed and even disabled. Various functions of the computer can get disabled or corrupted, so security tools are not interfering with ransomware processes.
However, this also means that the virus can install other programs to ensure that malicious processes can run. With these changes in particular settings, BitPyLock ransomware removal becomes more difficult. Even though it is not the easiest, to begin with.
Various files related to BitPyLock ransomware get placed in system folders, in the Windows Registry and startup preferences. But these places are not visited often, so you need to scan the machine fully to find these things and get rid of them. On the other hand, the ransom note is placed on the Desktop, in some folders where encoded data is located, so you quickly found the message.
Since the payment gets demanded in the program window, it often is opened on the screen directly after the encryption with the following text:
All your files are encrypted!
All your files, including, but not limited to:
Photos, videos, databases and office projects have been encrypted
– using strong military grade encryption algorithms AES-256 and RSA-2048.Recovery tools and other software will not help you!
Don’t find your backups? because they have been successfully encrypted too or securly wiped!The only way to recover your files, are to meet our demands.
1. Create a Bitcoin wallet (we recommend you to create on Blockchain.com)
2. Register on LocalBitcoins.com (or any other Bitcoin exchange), then buy 0.8 Bitcoin (BTC).
3. Send Bitcoins to our wallet below (in case sensitive. Make sure you copy past it):
1NAaH4rWww9yBUndSggQpQBLte5w927Jaj
4. Send Bitcoin Transaction ID to our e-mail address along with your “Private ID” below of this page:
[email protected]
5. You will receive the tools needed to decrypt all of your files immediately!Note: Before payment you can contact with us for 1 free small file as decryption test!
Be warned, we won’t be able to recover your files if you start fiddling with them!
You have 72 hours (3 days) from this moment to send us payment, or you files will be lost in eternity!
Private ID: –
When this message is appearing, victims believe that paying is the only solution for this infection. However, you should remove BitPyLock ransomware instead of even considering the payment option. Cybercriminals that spread less harmful threats are dangerous and untrustworthy. These people are focusing on getting your money and making a profit from the loss of your data. Even contacting them can lead to unfixable PC issues or permanently lost/ damaged files. 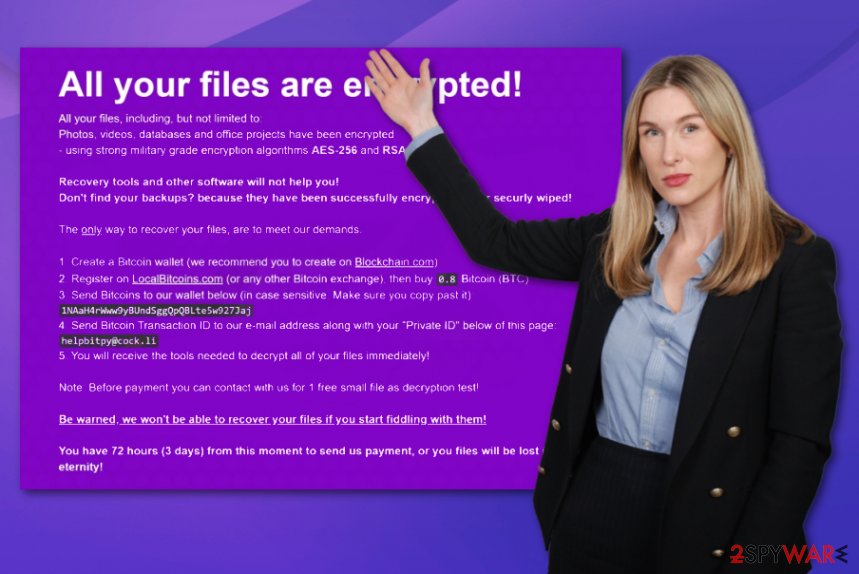
BitPyLock is the ransom-demanding virus that asks for thousands of dollars for the alleged file recovery. Regardless of the quantity of the encrypted files, BitPyLock ransomware developers going to ask for the payment transfer in chosen cryptocurrency. It mainly differs from variant to variant, so this time it is set to 0.8 Bitcoin that equivalents to at least 5 or 6 thousand US dollars. It can be increased when you contact criminals and go up to tens of thousands, so there is no need to write them.
Cryptocurrency wallets are not that easily traceable, so virus developers can remain anonymous for a long time. In most cases, ransomware developers are not caught by the police and continue to blackmail people all over the world. Since the official decryption tool is not released, you can only recover BitPyLock ransomware encrypted files with a particular software or by replacing them with backups.
The only way BitPyLock ransomware could get decrypted is when law enforcement gets access to the database where particular victim identification keys are stored. Such IDs are needed for decryption since each victim gets the unique code after the file-locking process.
However, restoring files while BitPyLock ransomware is still running on the machine is not a good idea. You need to get an anti-malware tool, run that program on the system, so all parts of the machine get checked and all traces of the cryptovirus eliminated. You can get your files encrypted again if you forget to do this step.
Then you should repair virus damage using PC repair utility or a system optimization program, so all alterations that BitPyLock cryptovirus have made get recovered. Reimage Reimage Cleaner may do that and indicate system files requiring the repair. Then, go through options below the article that provide solutions for encrypted data recovery.
Malicious macros trigger payload droppers
Direct spamming and other scam campaigns are commonly used to spread multiple types of cyber threats, including ransom-demanding malware. Deceptive techniques help to trick people into believing anything they see on the screen. Emails stating about financial information, containing order or payment confirmation documents as attachments, can be convincing enough and not creating any suspicions.
However, emails posing as notifications from legitimate companies or services can deliver malware directly from the email itself via a malicious link or trigger the drop of the infected file when you enable macros on the Microsoft document attached as an important file. One-click on the button “Enable” can allow the direct payload to launch the virus or the process of dropping the code.
Keep away from the content you are not familiar with and make sure to delete emails you were not expected to get. This is the only way to avoid cyber infections – keep yourself from questionable content online. 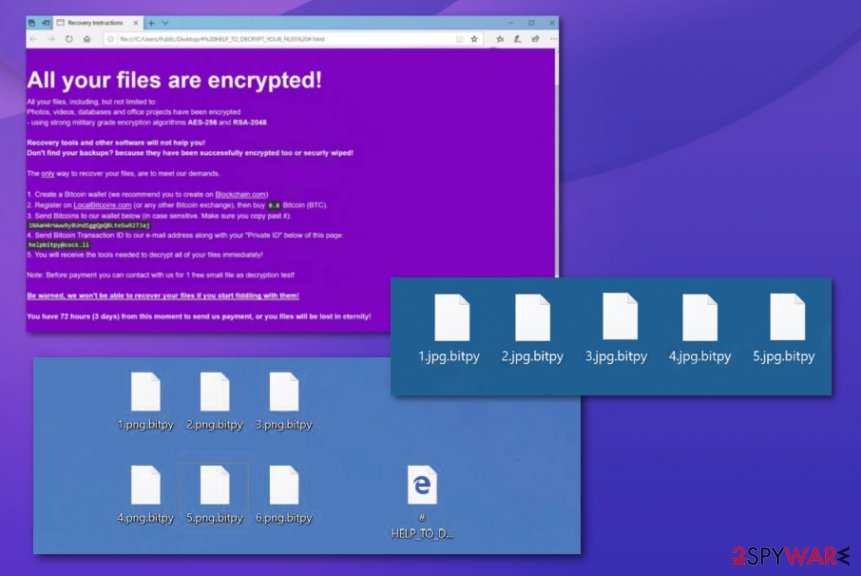
BitPyLock ransomware – threat that encrypts data and marks all files using .bitpy extension.
BitPyLock ransomware termination should happen as soon as possible
Don’t forget that this virus is one of the most dangerous cyber threats that can run in the background and make alterations to settings of the machine without requiring additional permissions. These alterations extremely affect the results of BitPyLock ransomware removal and the process itself.
You cannot remove BitPyLock ransomware when there are many changes made to security functions or registry and startup. So run the PC in Safe Mode and then launch Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner, or Malwarebytes to clean the damage, additionally check for traces left behind. Only then you can go through affected files and try to restore them,
Interfering with BitPyLock ransomware virus affected files before deleting the malware can result in lost files and damaged machines. These are instructions for additional features and programs helpful when dealing with such infection.
Remove BitPyLock using Safe Mode with Networking
Reboot the machine in Safe Mode with Networking and make the machine free of BitPyLock ransomware
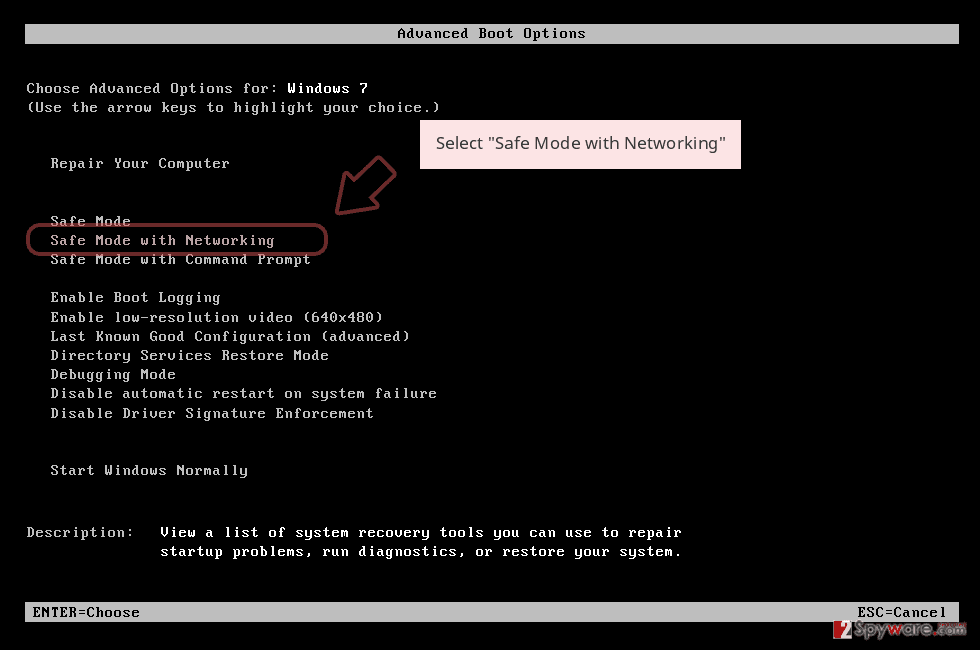
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
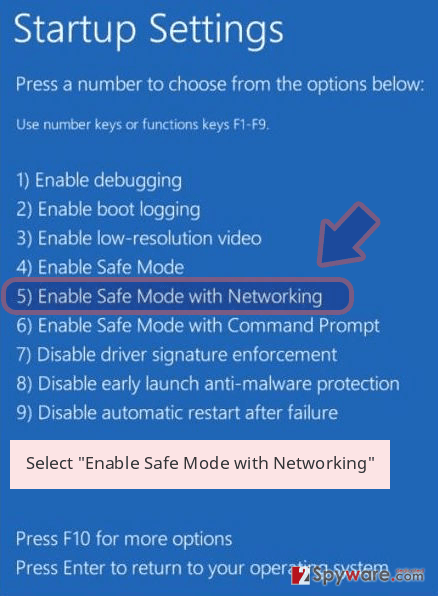
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete BitPyLock removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove BitPyLock using System Restore
System Restore feature is the function that allows users to recover the machine in a previous state when the virus was not active
Bonus: Recover your data
Guide which is presented above is supposed to help you remove BitPyLock from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by BitPyLock, you can use several methods to restore them:
Data Recovery Pro – the program designed to restore files affected by malware
This is the solution forBitPyLock ransomware virus victims when they don’t have particular file backups needed to restore encrypted data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by BitPyLock ransomware;
- Restore them.
Windows Previous Versions feature for the data rescue
When System Restore is enabled, files affected by BitPyLock ransomware can be restored using Windows Previous Versions
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer – a method for the data recovery
If you are sure that BitPyLock ransomware virus is not affecting Shadow Volume Copies, you can rely on this function
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption is not possible for BitPyLock ransomware
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from BitPyLock and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-01-13 at 08:00 and is filed under Ransomware, Viruses.

