WannaRen ransomware is the cryptovirus that resembles WannaCry virus and encrypts almost all files found on the targeted Windows system
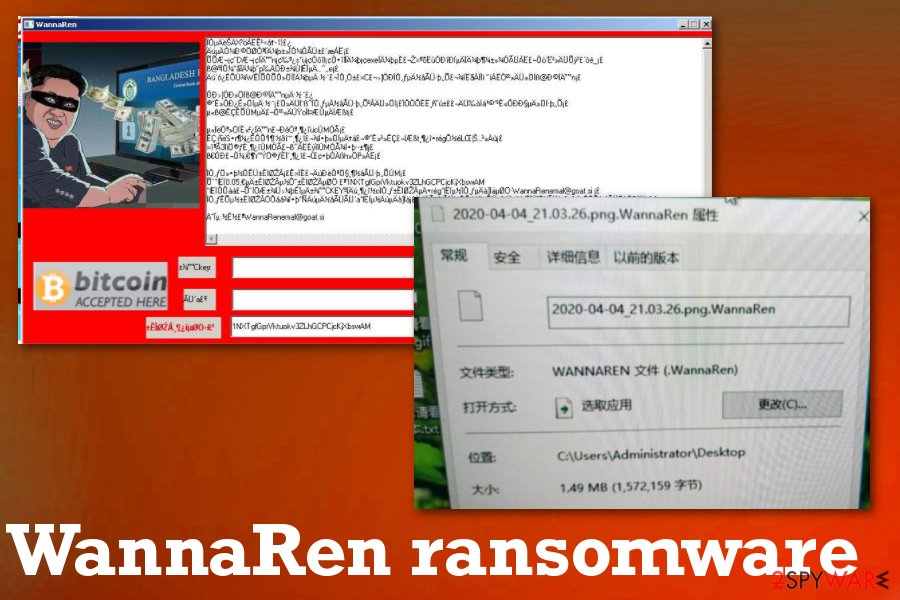
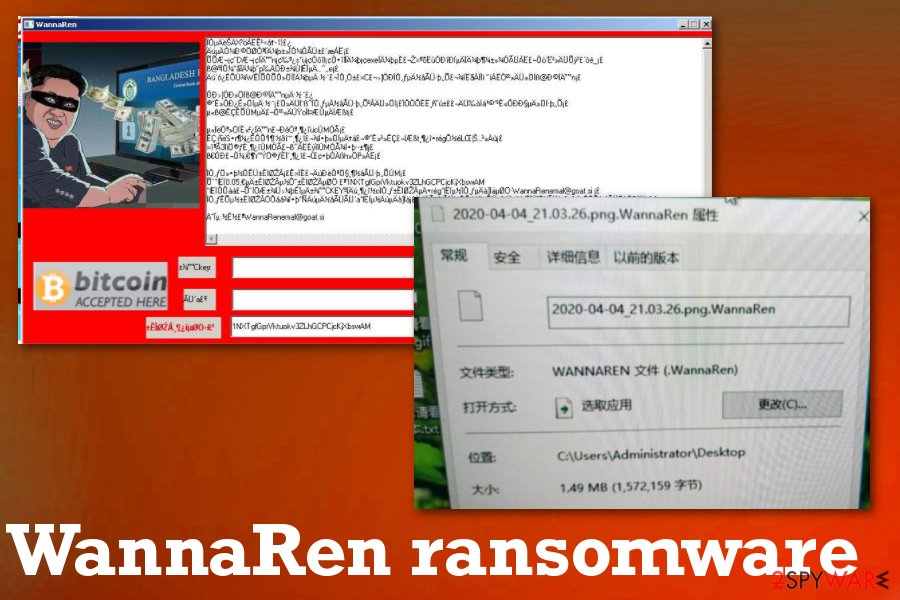
WannaRen ransomware is the product from hackers that mark encoded files using .WannaRen extension and demands at least 0.05 Bitcoin for the alleged decryption tool. There are two versions of this threat because one is sending the ransom note through a text file, and the other one uses pictures. Both of the versions are based on traditional Chinese language, Bitcoin addresses are the same, and there are no additional differences, so researchers state that the virus is developed and distributed by the same actors. Some researchers report that this threat is only encrypting files on Windows 10 an the other ones that malware doesn’t encrypt files at all. However, malware researchers often check samples on Virtual Machines, so ransomware may not act the same as on the Windows operating system. This is a serious infection that can damage the machine significantly and affect various parts of the system to ensure the persistence of the ransomware.
| Name | WannaRen ransomware |
|---|---|
| Target | The threat is displaying ransom message in traditional Chinese language, so the target is mots likely Chinese-speaking Windows users |
| File marker | .WannaRen is the extension that appears at the end of every encrypted file after the process of locking |
| Ransom note | The pop-up window named WannaRen appears on the screen with a ransom message and additional pictures, the form where you can buy Bitcoins and transfer them to an included wallet address |
| Two versions | There are two reported variants that only have one difference – the ransom note comes with text only or with additional pictures on the screen. Wallet address, extension, and other details are all the same |
| Ransom amount | 0.05 Bitcoin |
| Distribution | Victims report that infection appeared after installing Windows patch or other pirated cracks,[1] software. It may be the primary method of distribution, but ransomware also relies on the spam email method involving malicious files |
| Elimination | WannaRen ransomware removal requires attention from you and professional anti-malware tools that can detect[2] this malware and remove all the programs associated with the infection |
| Repair | You need to fully repair Windows system files and affected folders, settings. Get Reimage Reimage Cleaner Intego to do so and repair virus damage before you even consider data recovery options, so you can avoid losing those files |
There are many victims who ask for help and answers in online forums, so it is known that WannaRen ransomware virus has already affected devices and damaged computers. Some of the reports from victims also state that infection appeared after the installations of the Microsoft Eternal Blue patch. It may indicate that the main distribution technique is pirated software packages, malicious patch files, and other data that include malicious scripts.
WannaRen acts like WannaCry, but there are no other similarities or proven relations between two campaigns or malware creators. It may be the case because WannaCry was one of the most dangerous and active ransomware threats that managed to infect at least 150 countries in 2017 alone. It caused losses that, in total, go up to $8 billion. It is common to copy other threat actors, especially when it comes to cryptocurrency extortion-based malware.
This virus appears to be in development, and attacks are in early stages, so there might be some additional updates to the coding methods and other functionalities that make the malware more dangerous. This is also the reason why information about the WannaRen ransomware virus is limited and not detailed. However, we try to provide you will all the information, so you can know how to fight the infection.
It seems that Windows 7 users are not getting file encryption when WannaRen ransomware manages to get on the machine, but Windows 10 users complain about serious damage to the system, including the file encryption. This file-locking process is achieved by using army-grade encryption algorithms and changing the original coding of the file. In most cases, these threats target files like images, documents, video or audio files, and archives, databases.
You need to remove WannaRen ransomware as soon as possible because even though it mainly relies on common file types there is a huge possibility that other processes that get triggered in the background manage to affect system preferences and folders, functions of the OS.
Once WannaRen ransomware gets on the computer, these are changes that can get made by the virus itself to ensure the persistence of the infection:
- disabled AV tools and security functions;
- added programs and files;
- deleted applications;
- altered registry keys;
- speed and performance issues.
When you decide how to perform the WannaRen ransomware removal, it is crucial when you choose the anti-malware tool because there are separate databases for malware and not all AV detection engines use the same ones, so detection results may differ. Choose the official tool and make sure to use the full system scan option to check all places of the computer.
The anti-malware program offers what to do next when the malware is detected. Double-check after the termination to be sure that the system is virus-free. Then you can run Reimage Reimage Cleaner Intego and repair virus damage and recover files that WannaRen ransomware encrypted. The best method is data backups from cloud or external devices. If you do not have backups, try third-party tools. We have listed a few options below. 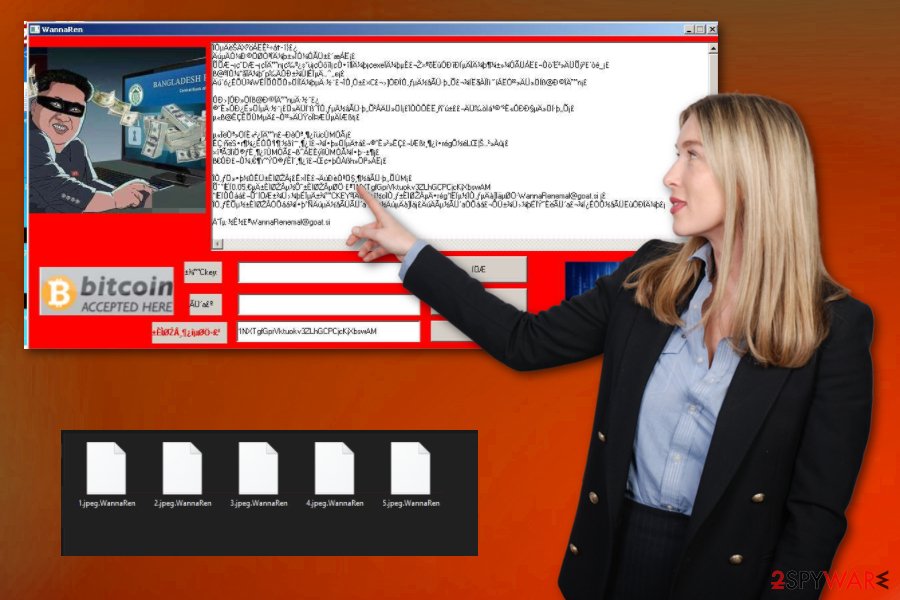
WannaRen ransomware is the cryptovirus that marks encrypted files with .WannaRen before asking for the payment.
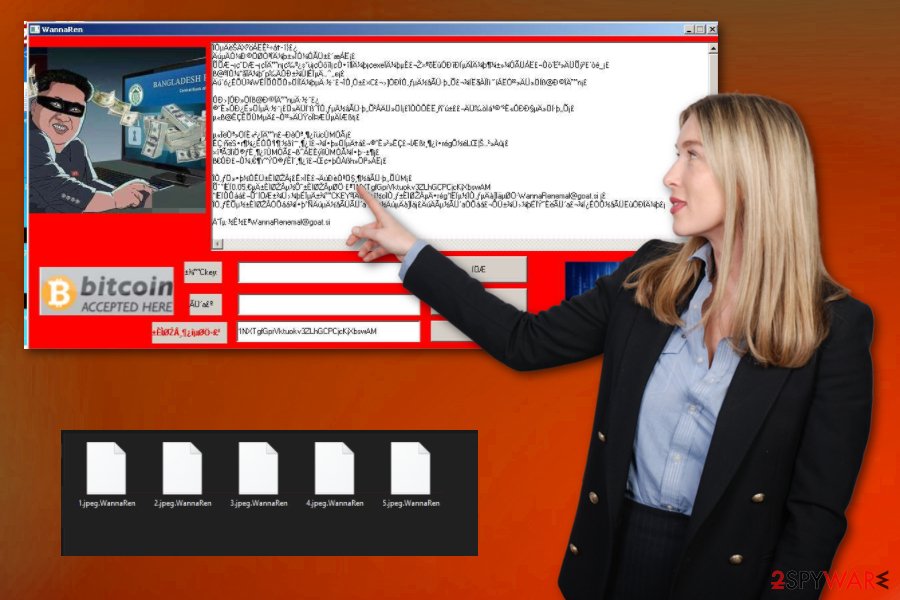
WannaRen ransomware is the cryptovirus that marks encrypted files with .WannaRen before asking for the payment.
Malicious files – in use for ransomware distribution
When malicious actors try to spread their products around as quickly and as wide as it is possible because ransomware creators care about profits and money that they can get from victims directly. Spam campaigns, when file attachments contain malware scripts, are one of the more used methods for such instances.
However, malicious files become more included in pirated software packages and gets installed when users download cracks, cheats, fake software, and license keys. There is no indication about the malicious file if you don’t check the install setup for the wanted program or game cheat. This is why the method works.
Victims reported that patches, software, and other pirated content were installed before the ransomware attack. It may be an indication of a particular relation, but you should pay attention to various details if you want to avoid anything like this. Delete any suspicious emails and do not download questionable files from notifications you were not expected to receive. Experts[3] always note that spam emails can include a handful of viruses, so make sure to check the file and sender before doing anything.
Clean traces of WannaRen malware from your Windows system
WannaRen ransomware virus might still be in development and get updates or changes in the coding or added other features, so there still can be some missing pieces or even vulnerabilities that allow this threat to get removed by using anti-malware tools. In some cases, such threats can disable AV tools and security programs.
Some users report that it is difficult to remove WannaRen ransomware due to the fact that their AV tools are disabled to cannot find the malware file. So reboot the machine in Safe Mode and then run the SpyHunter 5Combo Cleaner or Malwarebytes program to find and eliminate all traces of this ransomware. You can find some tips on this method below the article.
As for the WannaRen ransomware removal, you can then run steps suggested by the program you use and follow with a thorough system cleaning. Anti-malware tools should find all related programs, but these AV detection engines cannot recover encrypted files or fully clear virus damage. Reimage Reimage Cleaner Intego can at least check for affected files and repair any corrupted parts for you. Then you can go through data recovery options.
Remove WannaRen using Safe Mode with Networking
Reboot your device in Safe Mode with Networking before running the AV tool on the machine. This way you remove WannaRen ransomware
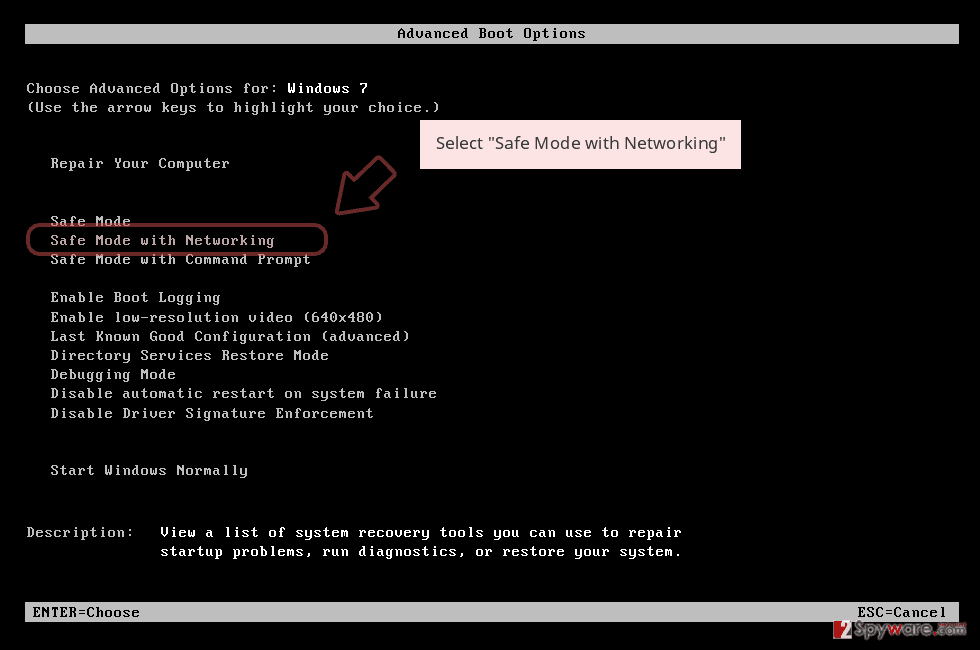
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
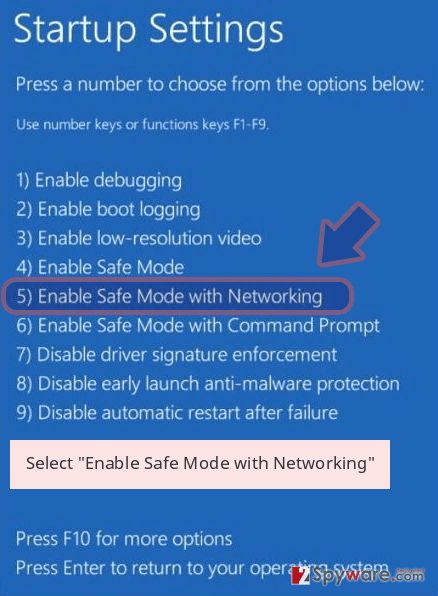
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete WannaRen removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove WannaRen using System Restore
System Restore feature gives the opportunity to recover a machine to a previous state when the virus was not active
Bonus: Recover your data
Guide which is presented above is supposed to help you remove WannaRen from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by WannaRen, you can use several methods to restore them:
Data Recovery Pro can gather all the encrypted files ad restore them for you
When WannaRen ransomware encrypts data, or you accidentally delete files, Data Recovery Pro can help with restoring them
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by WannaRen ransomware;
- Restore them.
Windows Previous Versions feature recovers individual data
System Restore should be enabled beforehand for Windows Previous Versions to work properly
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is the method for data recovery after WannaRen ransomware infection
When Shadow Volume Copies are untouched, this feature can be used for data restoring
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
WannaRen ransomware doesn’t have a decryption tool
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from WannaRen and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-04-08 at 06:34 and is filed under Ransomware, Viruses.

