Ubisoft’s lawsuit attempts to punish providers of DDoS attacks launched at Rainbow Six: Siege servers in September
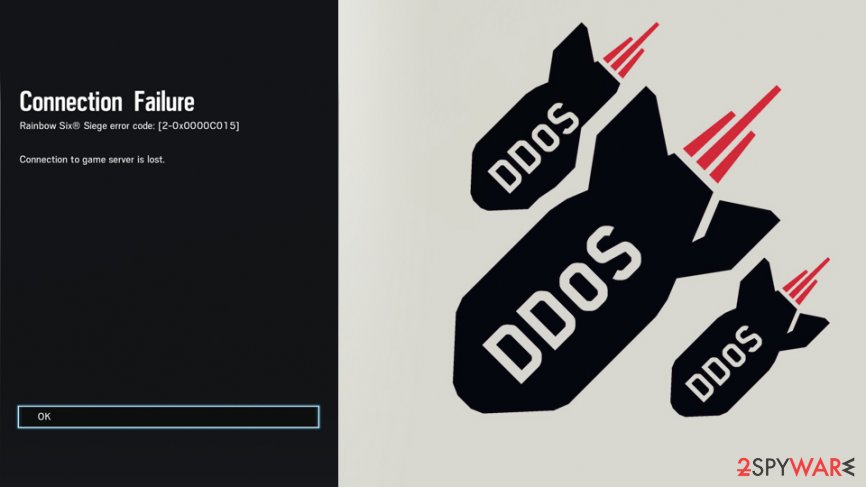
A major video game maker and publisher Ubisoft had filed a lawsuit against multiple websites that were allegedly used to launch DDoS attacks against Tom Clancy’s Rainbow Six: Siege multiplayer gaming servers in September last year. The attacks resulted in major disruptions for Ubisoft and the players of its most popular game, otherwise known as R6S.
The charged individuals are five people from Nigeria, Germany, and the Netherlands who run a website SNG.ONE, among other domain names, which is used to allegedly test servers against potential Denial of Service attacks. It offers a monthly plan for $30, as well as a lifetime subscription, which costs $299.85. However, the evidence was found that the owners list popular games like Fortnite, FIFA 20, Call of Duty: Modern Warfare 4, as potential targets on their support page.
While the defendants did not perform DDoS attacks against R6S servers (players who want to take unfair advantage of game crashes to climb in-game ranks did), Ubisoft argues that their malicious actions’ involvement was far greater than they themselves implicate and “are well aware of the harm.”
The lawsuit was also a result of one of the seemingly harmless tweet that was posted by one of the defendants and mocked the efforts of Ubisoft to mitigate the attacks back in September:[1]
Good job @ Ubisoft
Keep the work up.
Tom Clancy’s Rainbow Six: Siege video game players have been practicing a new way to climb up the ranks: launching DDoS attacks at game servers
The website owners are changed with violation of the computer fraud and abuse, California penal code, and other three counts of infractions in a lawsuit filed by Ubisoft in the US Court Central District of California late last week. The defendants are five individuals who were responsible for “weaponizing” DDoS attacks, named as following in the lawsuit documents:[2]
- Dennis Kruk
- Maximilian Kuehl
- Kelvin Uttih
- Another two individuals listed as B.R and [email protected].
Ubisoft claims that once DDoS are executed, they flood servers of the game with numerous requests – this creates major disruptions and overloads the network, resulting in users experiencing in-game lag, login issues, as well as disconnects, during which users are pulled out of the match without the possibility to finish it.
Ubisoft seeks to punish those responsible for the DDoS attacks in September: shut down the concerned sites, as well as gain financial compensation for the costs involved.
In order to maintain Ubisoft’s strong community of dedicated R6S players, Ubisoft has invested considerable time, money, and effort into ensuring that all of its players have a positive, fun, and rewarding experience each time they play R6S. By this lawsuit, Ubisoft seeks to stop an unscrupulous commercial group of hackers and profiteers dedicated to harming Ubisoft’s games and destroying the R6S player experience for their own personal financial benefit.
Ubisoft started banning cheating players
Ubisoft, along with other gaming companies like Blizzard,[3] have been battling DDoS attacks for a very long time. While domains get seized,[4] many responsible parties get caught by authorities and even serve jail time for the illicit activities, it does not compensate players who lose their matches, can’t access games, and suffer other losses. Gaming companies also suffer from major reputation hits, resulting in financial losses.
Since September, DDoS attacks against the R6S servers declined by 93%, since Ubisoft implemented multiple mitigation methods, such as banning of players involved in launching the DDoS, as well as reducing the involved servers’ workload.[5]
Most probably, the lawsuit could be avoided if not a few factors that led to it – there are hundreds of websites that offer similar services [sort of] legally. However, because service providers decided to mock Ubisoft’s attempts to stop the cyberattacks on Twitter, included multiple popular game names in their support panel, and also seemingly helped customers to set up the attacks, the outcome could be disastrous for the defendants.
