Try2Cry – dangerous open-source ransomware with the USB worm traits
Try2Cry ransomware is a dangerous ransomware-type malware that uses the Rijndael symmetric key encryption algorithm[1] by calculating SHA512 hash for locking personal files on the host machine. Discovered by Karsten Hahn from the G DATA[2] team of cybersecurity experts, the ransomware has been attributed to the Stupid ransomware family.
The Try2Cry virus is an open-source malware, meaning that its code is accessible for hackers online and, most probably, less experienced criminals can customize it and use it for their needs in exchange for a commission fee. The virus is not capable of infecting all file types on the machine, though it is capable of locking the most popular data, such as pictures, PDF documents, Excel sheets, and other documents. Each of the locked entries gets the .try2cry file marker.
The main distinguishing feature of the Try2Cry ransomware virus is the way it spreads. In fact, it can be attributed to the USB worm[3] category as well, since it’s secondary task is to inject the malicious Update.exe file into all USB devices connected to the host machine. This file is a ransomware copy, so as soon as the infected USB flash drive is connected to another device, the payload gets activated.
| Name | Try2Cry |
| Classification | Ransomware |
| Geneology | Stupid ransomware |
| Encryption model | Rijndael algorithm SHA512 hash |
| File extension | .try2cry file extension |
| Files targeted | .doc, .ppt, .jpg, .xls, .pdf, .docx, .pptx, .xls, and .xlsx files |
| Contacts | [email protected] |
| Other traits | It’s open-source ransomware. Its source code is accessible for hackers on various background forums. |
| Distribution | This cryptovirus is being disseminated by various means, i.e. spam email attachments, cracks, keygens, fake software updates, etc. However, people can also get infected via USB Flash Drives as this virus can copy its Update.exe file to the external drive connected to the host machine |
| Decryption | The ransomware is decryptable. Users can use the Stupid decrypter for unlocking .try2cry files |
| Removal | Before launching the decryption software, it’s a must to remove the ransomware from the system using a professional anti-virus program. In addition to that, it’s advisable to scan all USB flash drives for infection if they have been connected to the infected machine |
| Fix ransomware damage | This particular virus can alter Temp folder and initiate various alterations within the Registry. To fix suchlike damage, run a scan with Reimage Reimage Cleaner Intego upon virus elimination |
Try2Cry virus has been found by a researcher from the G DATA team when the detection signature software designed for the detection of active USB worm components has been triggered by a malicious Update.exe file. After the sample analysis, the ransomware has been approved. It’s genealogy straining from the open-source ransomware family known as Stupid. According to its behavioral traits, the virus is similar to Spora, Thanos ransomware, and Andromeda trojan.
This misleading ransomware has been found spreading via infected USB Flash Drives and misusing LNK shortcuts to alter data stored on the infected drive. The files marked by LNK shortcuts serve as a ransomware payload, so once clicked, they open the original file and download the virus onto the machine. Consequently, Update.exe file runs the cipher and locks the .doc, .ppt, .jpg, .xls, .pdf, .docx, .pptx, .xls, and .xlsx files.
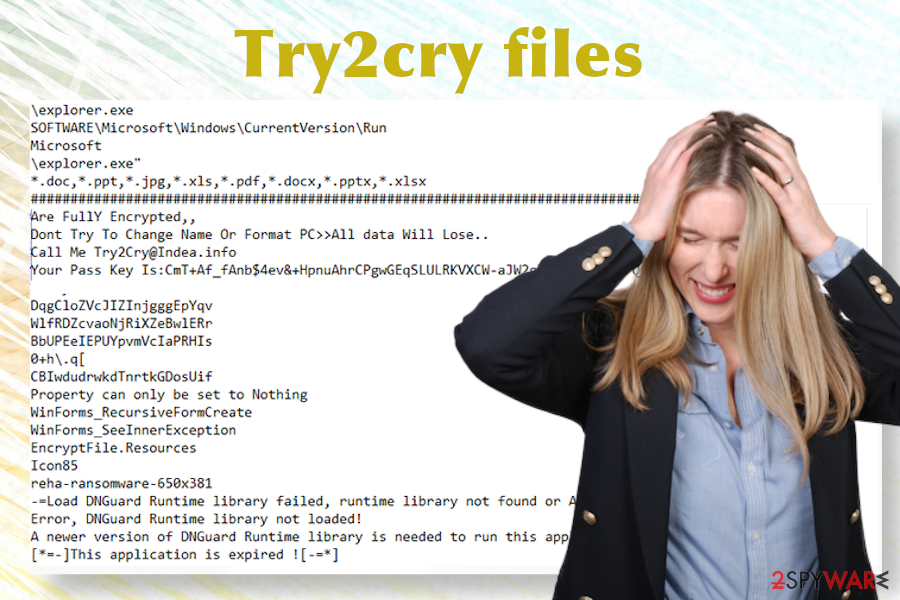
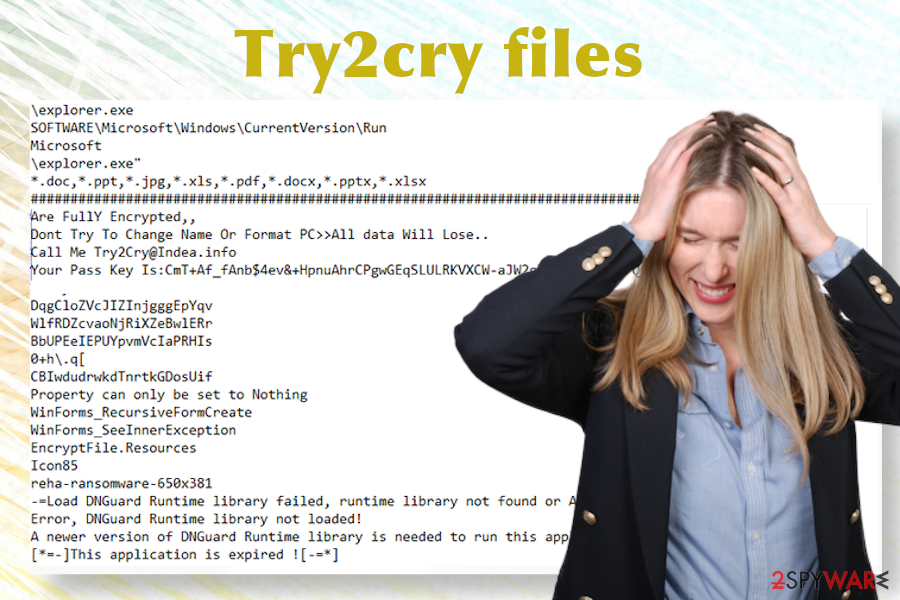
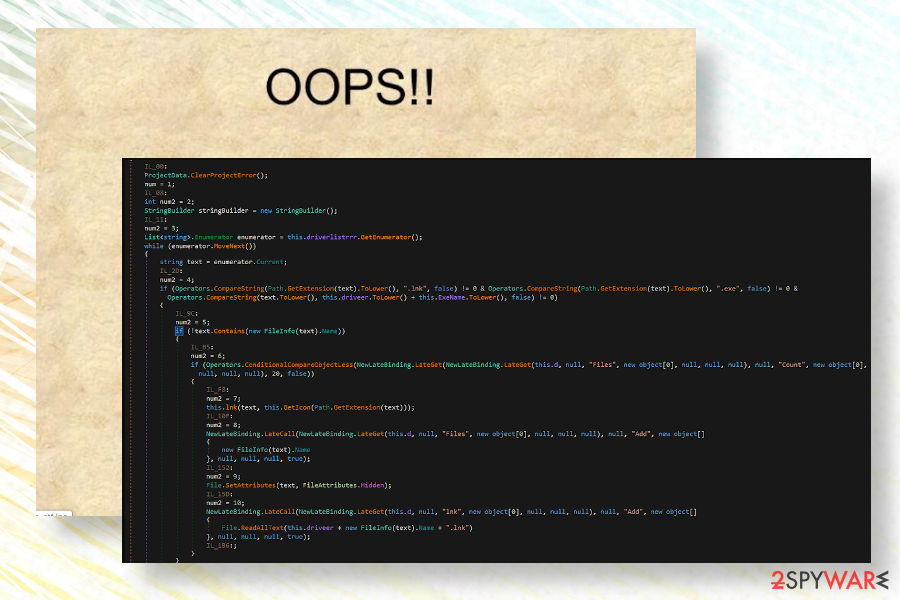
According to the researcher, the virus uses the Rijndael symmetric key encryption algorithm and SHA512 hash of the password to lock the data. Upon the encryption, the victim sees the data with the .try2cry file appendix. Besides, the victim may notice the \explorer.exe file, which once launched opens a ransom note saying:
You Are Fully Encrypted,
Don’t Try to Change Name Or Format PC>> All Data Will Lose
Call Me [email protected]
Your Pass Key Is:
The note does not specify criminals’ expectations about the size of the ransom or the time span the victim should react. The Try2Cry file virus note only contains the email address [email protected] and the unique key, which consists of lower and upper case letters, numbers, and symbols.
Windows machines that are already infected with any type of cyber infection are not likely to be infected by Try2Cry ransomware. The ransomware code has been designed to skip infected machines with the DESKTOP-PQ6NSM4 or IK-PC2 machine names. The researchers suppose that such behavior is based on the criminals’ will to test the ransomware with being interfered.
Try2cry initiates malicious processes to lock most popular file types and generates a rather non-informative ransom note
Try2cry initiates malicious processes to lock most popular file types and generates a rather non-informative ransom note
Anyway, if your machine got infected by this malicious virus, you should immediately scan the system with a professional anti-virus program to remove Try2Cry virus. There are plenty of reasons why you should do that. First of all, the longer the virus remains on the system, the more malicious system changes it can cause. Second of all, the Update.exe file copy can be disseminated to many USB devices, thus allowing the virus to reach other machines easily.
Last, but not least, before you decrypt try2cry files, it’s a must to perform a full Try2Cry removal. Otherwise, the virus may re-encrypt unlocked files or wipe them out completely. In order to perform a full virus elimination, you should restart the system into Safe Mode with Networking and launch the security software.
Right after the Try2Cry virus removal, run a scan with Reimage Reimage Cleaner Intego repair tool to recover the Windows machine. This application can help to restore deleted or altered registry keys, enable crucial processes that might have been disabled, and recover the Temp folder in a state it was before the ransomware attack.
Do not open suspicious files on the USB flash drives
The most interesting feature of this particular ransomware strain is its ability to infect USB drives connected to the infected machine. The malicious copy of the Update.exe is automatically transferred to the external drive, which shows up in the form of a new folder. In addition, the virus creates several folders that are named using Arabic names.
These folders are infected by malicious ransomware files. Therefore, if the user gets caught by the curiosity and others the Arabic-named files, the ransom file is opened and the ransomware payload is launched. However, NoVirus.uk[4] experts warn that the virus can also be disseminated by other means, including but not limited to spam email attachments, software cracks, and fake updates.
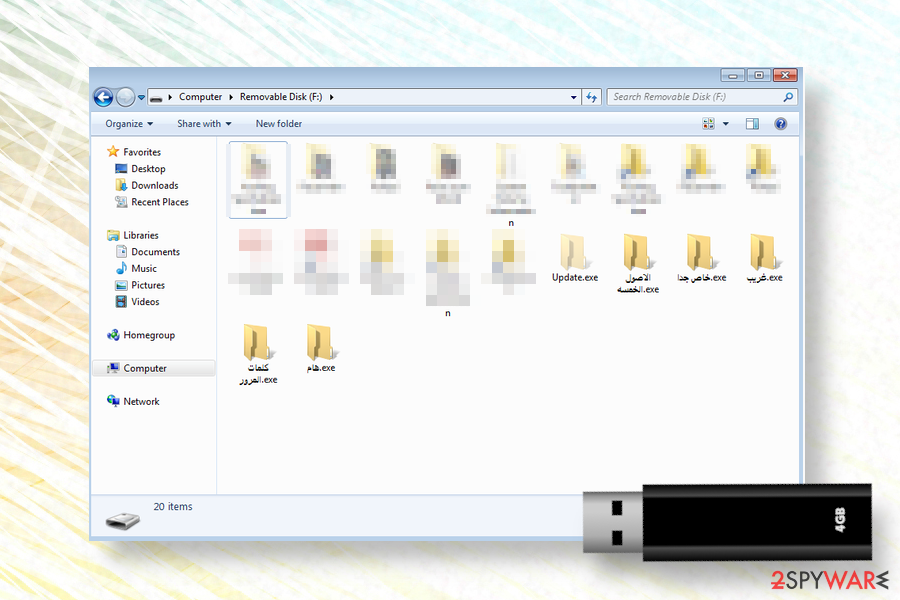
Try2cry ransomware is dubbed as a USB worm due to the capability of the copy itself onto the connected USBs
Try2cry ransomware is dubbed as a USB worm due to the capability of the copy itself onto the connected USBs
Therefore, a piece of advice would be to stop using torrenting sites for getting pirated software. Besides, we would strongly recommend staying away from cracks and keygens because instead of saving the money for some license key you may get infected with ransomware or another virus. Such experience may leave your pockets empty or cause complete loss of personal files.
Advanced guide on Try2Cry ransomware removal
When it comes to ransomware, it’s a must to act fast once you find at least a single file locked. There’s no reason to postpone the elimination process as delayed removal can lead to a higher number of encrypted files, more system modifications, and infiltration of other cyber infections.
Try2Cry removal is a process that can be handled by a professional anti-virus program only. There’s no way to eliminate the malicious bundle of ransomware files manually. Thus, we recommend using SpyHunter 5Combo Cleaner or Malwarebytes tools for cleaning your machine. Note that some of the malicious files may be blocking security tools, so you may need to restart the system into Safe Mode with Networking.
Once you remove Try2Cry ransomware, we strongly recommend you to scan the USB flash drive with security software or format it to prevent a relapsed attack. Besides, it’s advisable to ensure a full Windows optimization, which can be done by running a scan with Reimage Reimage Cleaner Intego utility.
Try2cry ransomware is capable of distorting Temp folder
Try2cry ransomware is capable of distorting Temp folder
After a full Try2Cry removal, try to decrypt your files using the Stupid decryption software or alternative data recovery methods that we have listed below.
Remove Try2Cry using Safe Mode with Networking
If ransomware blocks security software, you should restart the system into Safe Mode with Networking to launch it successfully. Here’s how you can do that:
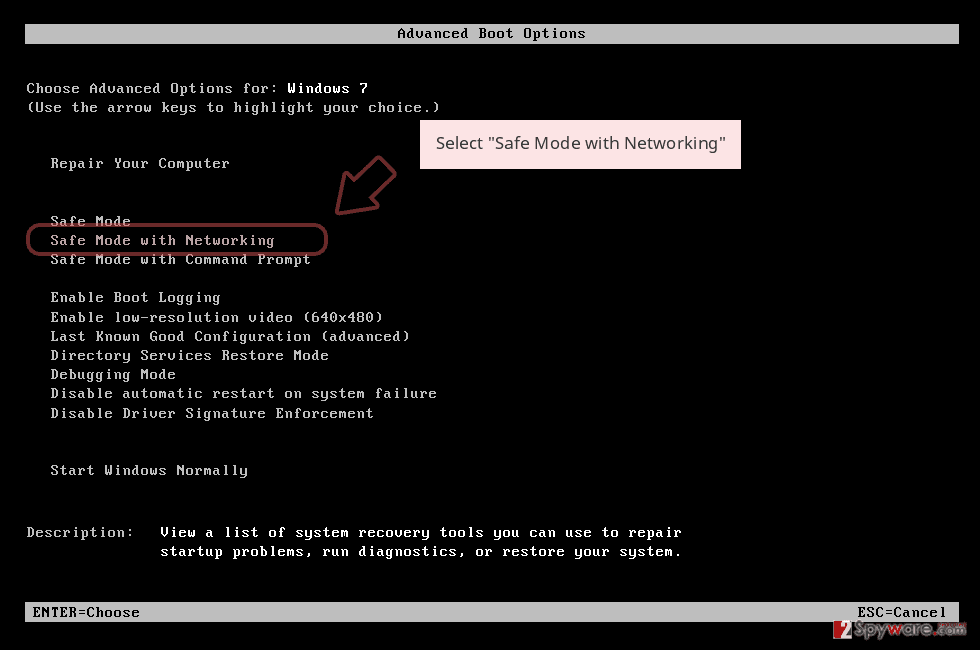
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
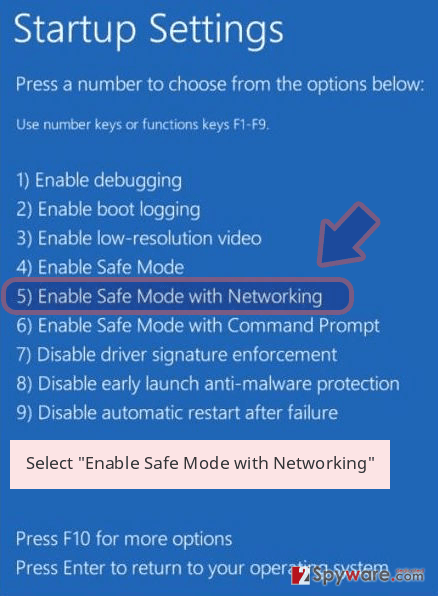
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Try2Cry removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Try2Cry using System Restore
If the previous method did not help to remove Try2Cry file virus, try to enable a System Restore Point this way:
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Try2Cry from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
Do not pay the ransom. That’s rule number one when we talk about the Try2Cry virus. This ransomware CAN be deciphered and we will provide all available options for that.
If your files are encrypted by Try2Cry, you can use several methods to restore them:
Take advantage of the Windows Previous Version feature
Windows has an in-built feature known as a Previous Version. This feature allows people to restore the data to the state it was before the ransomware attack. However, this option is available for those users who have had the System Restore function enabled before the infection.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Exploit Volume Shadow Copies
Shadow Explorer is a piece of software capable of retrieving lost data from Volume Shadow Copies. If the ransomware hasn’t been programmed to delete these copies, then you will be able to unlock try2cry files this way.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Use an official Stupid decryptor
A team of cybersecurity experts has introduced victims of Stupid ransomware with a fully functional decryption tool. The latest variant of this ransomware family, Try2Cry virus, can also be deciphered using this tool.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Try2Cry and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can’t grant a full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features.
Nevertheless, there’s a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
While much of the data can be accidentally deleted due to various circumstances, malware is also one of the main culprits that can cause loss of pictures, documents, videos, and other important files. Potentially unwanted programs may clear files that keep the application from running smoothly.
More serious malware infections lead to significant data loss when your documents, system files, or images get locked. Ransomware is the one that is focused on such functions, so your device gets useless without access to needed data. Even though there is little to no possibility to recover after file-locking threats, some applications have features for such recovery in the system.
In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
This entry was posted on 2020-07-08 at 02:30 and is filed under Ransomware, Viruses.

