Trojan.Downloader is the general term used to describe trojans designed to download other malware on the machine
Trojan.Downloader is the type of trojan horse that installs files, malware, and malicious applications. It may look like a legitimate program or file, but it is malicious in nature. In most cases, these threats get downloaded without users’ knowledge or consent, so this virus has the main purpose of creating damage, stealing, and disrupting data. The intruder gets downloaded on the computer, so it can run in the background freely. Trojan can even download and install new versions of itself, drop the payload of ransomware-type threats,[1] and trigger other more noticeable symptoms.
However, the purpose of Trojan.Downloader virus is to remain undetected until the confidential, personal, sensitive information is stolen, obtained, or the machine gets compromised. It is focusing on secret downloads and operations involving remote server that helps with malicious executions and file downloads. It may only work when there is an internet connection, so it can connect to a remote server, but once malware gets injected, the system gets affected regardless of the internet. There are many similar threats that fall under this term like JSDownloader or Ymacco Trojan.
| Name | Trojan.Downloader |
|---|---|
| Type | Trojan horse[2] |
| Purpose | Malware is created to spread other threats, inject payload files, drop malicious data, applications, and launch other operations that a malicious actor wants to trigger |
| Distribution | The particular malware spreads using malicious files, phishing links. Trojan can infiltrate the machine silently and undetected, so the infiltration is not noticed |
| Elimination | You need to remove Trojan.Downloader as soon as you encounter any suspicious symptoms, so you can clear any associated malware at the same time |
| Danger | Trojans can infect machines with other threats and steal data directly from the system using other tools. There are many layers this malware might have to achieve creators’ goals |
| Repair | Since the trojan is running in the background for a while possibly, your device can get damaged. Find corrupted or affected parts with the help of Reimage Reimage Cleaner Intego |
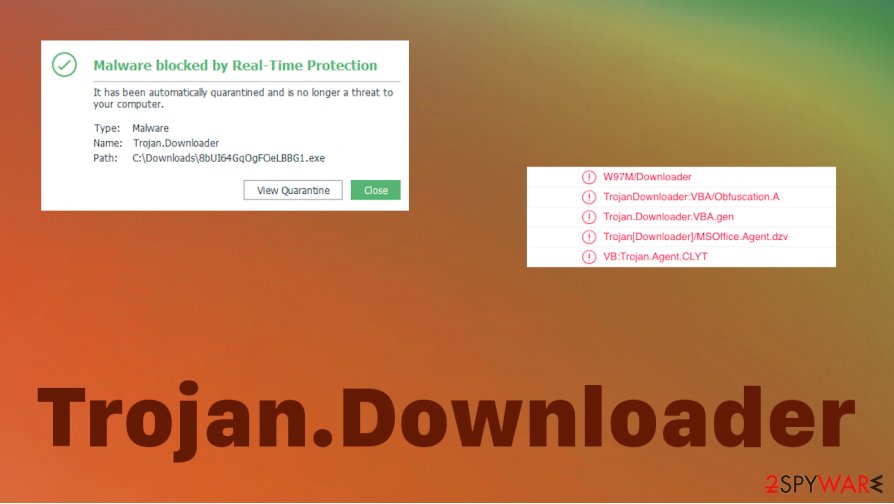
Generally, Trojan.Downloader is the detection[3] that appears on the AV program windows after a system check. A trojan horse can be distributed when it is downloaded from the email as an attachment or delivered from a malicious link. Exploit kits and malicious sites can often be used in such campaigns.
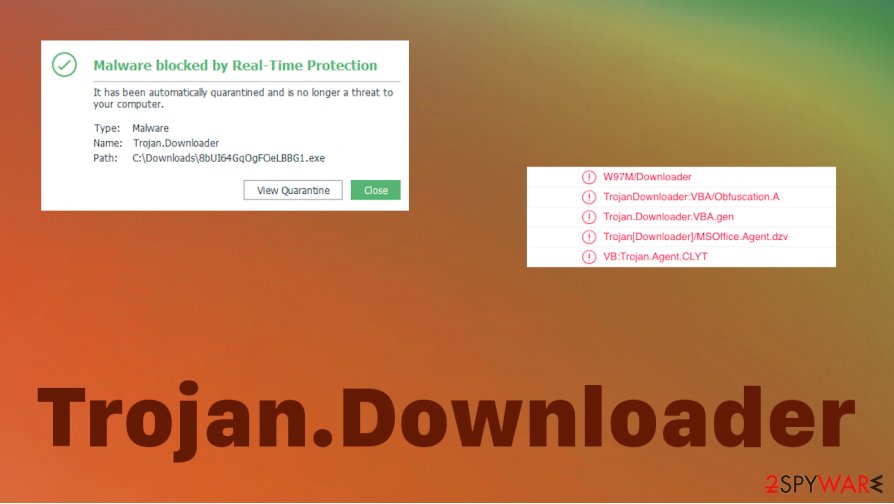
No matter what method is used to spread the particular version of Trojan.Downloader. Since this is the more general term, you may have a particular infection on the machine. There are tons of them, and researchers have described many of them. Unfortunately, there are ransomware and cryptojacking threats that get detected with this result.
Try to remove Trojan.Downloader once the AV engine shows you the detection name on the screen. Do not wait for long since there are dangerous trojans and other types of malware associated with such detection result:
- Trojan-Downloader:FraudLoad
- Trojan-Downloader:W32/JQCN
- Trojan-Downloader:OSX/Jahlev.A
- Trojan-Downloader:W32/Bredolab
- Trojan-Downloader.JPUY
Trojan.Downloader cannot cipher information on the machine, nor trigger particular issues on the targeted computer. You cannot tell when the initial infiltration happened, so you need to react as soon as anything suspicious occurs on the device. The best way to tackle such infection is the proper anti-malware tool selection that can find and delete traces of the virus properly.

Trojan.Downloader – general term for the virus payload dropper.

Trojan.Downloader – general term for the virus payload dropper.
You should pay attention to the fact that there are many threats like this Trojan.Downloader virus, so you can encounter the threat one way or another. It many spread ransomware, so when you try to remove any cryptovirus, and you see the result with this detection it is pretty much known how the extortion-based virus cam to your PC.
Trojan.Downloader removal is a very important process because when the malware is added on the system it starts to run in the background to achieve the needed goals. It can:
- install and run programs;
- steal data from the machine;
- inject direct malware payload;
- open backdoors for remote hackers;
- record direct keystrokes.
False alerts and phishing emails can trigger the spread of trojans
There are tons of email campaigns that can spread this or any other malware around. Those emails mainly include file attachments, links in the notification itself, and redirects to more malicious sites, hacked copies of legitimate platforms. You may encounter some fake alerts with notices about software licenses and declarations about illegal activities.
If you click on any malicious content or allow processes to run, you may trigger the infiltration of malware like this or even other programs that cause further damage. Phishing email campaigns can be noticed, if you find suspicious material and delete the notification, avoid clicking on anything. You need to pay attention to various materials, especially the ones that you encounter online.
Avoid pirating and torrent sites, rely on proper software sources, do not get scared by scammy messages, read into everything, so you cannot become a victim of an online scam. Run the AV tool more often, so malicious content gets blocked before trojan infiltration happens.
Perform the full virus elimination process, so you get rid of the Trojan.Downloader virus
You may encounter issues with the system when a threat like Trojan.Downloader virus is installed, but you cannot know what causes these problems with the machine. This is why we always recommend having a powerful anti-malware tool on hand that can check the system for various threats and intruders.
You should remove Trojan.Downloader as soon as your AV engine indicates the threat. Or you can check the system with SpyHunter 5Combo Cleaner or Malwarebytes if you find anything suspicious with the device and performance of the computer. Try to use at least a few tools if you cannot find anything malicious. There are many databases that AV tools can rely on.
When you successfully achieve the wanted results of Trojan.Downloader removal, you should also think about the things that Trojan may have done to your device. There are features that get disabled and various functions that trojan triggers to run or stops operating. Try to check for affected files using Reimage Reimage Cleaner Intego and repair those issues.
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. It is a hassle when your website is protected from suspicious connections and unauthorized IP addresses.
The best solution for creating a tighter network could be a dedicated/fixed IP address. If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for server or network manager that need to monitor connections and activities. This is how you bypass some of the authentications factors and can remotely use your banking accounts without triggering suspicious with each login.
VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world. It is better to clock the access to your website from different IP addresses. So you can keep the project safe and secure when you have the dedicated IP address VPN and protected access to the content management system.
While much of the data can be accidentally deleted due to various circumstances, malware is also one of the main culprits that can cause loss of pictures, documents, videos, and other important files. Potentially unwanted programs may clear files that keep the application from running smoothly.
More serious malware infections lead to significant data loss when your documents, system files, or images get locked. In particular, ransomware is is a type of malware that focuses on such functions, so your files become useless without an ability to access them. Even though there is little to no possibility to recover after file-locking threats, some applications have features for data recovery in the system.
In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
This entry was posted on 2020-07-23 at 06:24 and is filed under Trojans, Viruses.

