[email protected] ransomware – data locking virus that might make you lose your files forever
[email protected] ransomware is a powerful malware that renders personal files useless until ransom is paid
TorS@Tuta.Io ransomware is a powerful malware that renders personal files useless until ransom is paid
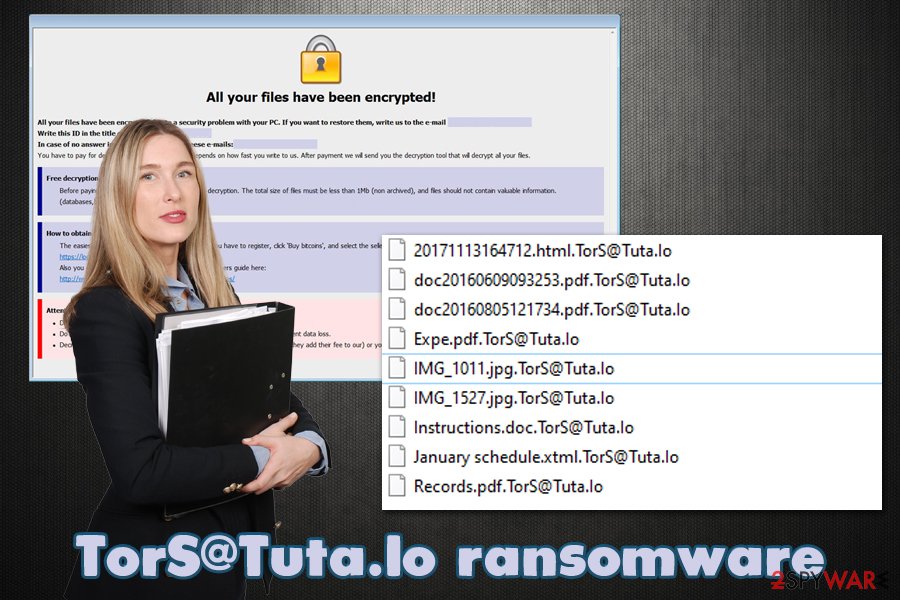
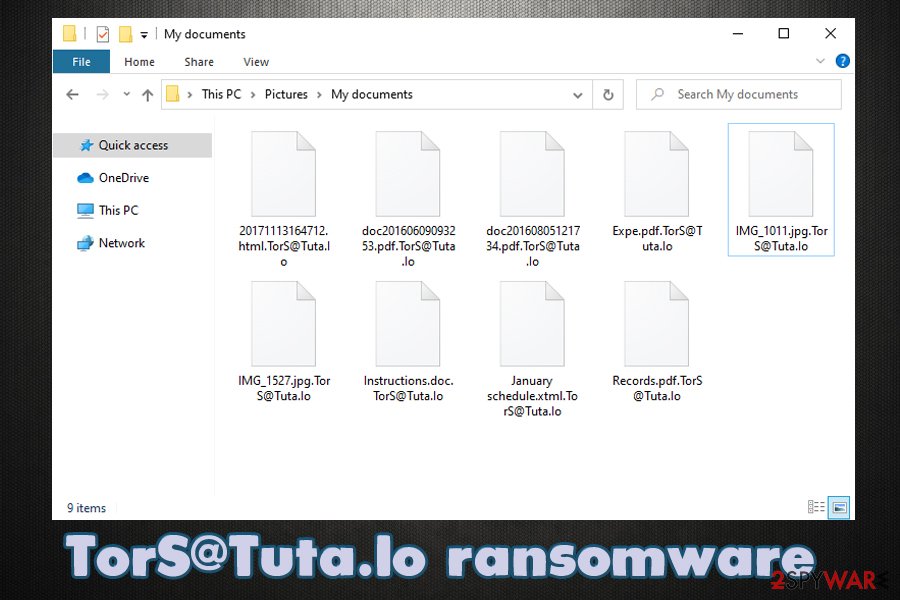
[email protected] ransomware is a type of malware that specializes in money extortion. Mainly distributed via spam email attachments, such as Zip files, this virus’s main goal is to encrypt all personal files on the infected machine with the help of a powerful encryption algorithm.[1] Suchlike modified data becomes inaccessible for the victims, and each of the affected files is marked with [email protected] appendix.
Once pictures, music, documents, databases, videos, as well as other files, are locked, [email protected] virus delivers a ransom note which is titled “Help decrypt.hta.” This file serves as a notice from malware authors, who claim that the only way to recover files is by transferring Bitcoin to a particular digital wallet. However, we do not recommend doing so, as you might end up losing your money in addition to personal data.
| Name | [email protected] ransomware |
| Type | File locking virus, crypto-malware |
| Malware family | GlobeImposter ransomware |
| Distribution | Spam emails, exploits, fake updates, insecure RDP connections, software cracks, etc. |
| File extension | Each of the affected files is appended with [email protected] extension. Example of an encrypted file: “[email protected]” |
| Ransom note | Help decrypt.hta pop-up window, which is shown as soon as malware completes the file locking process |
| Data recovery options | Without backups, there are little chances of recovering all the encrypted files. However, there might be a few methods that could help you retrieve at least some portion of the encrypted data – check the second section of this article for more details |
| Malware removal | Ransomware can be eliminated by scanning a computer with powerful anti-malware software – we recommend using SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | Malware infections can render any Windows system less effective, sluggish or even result in system crashes. Thus, if you experience such issues once you get rid of the infections, you can attempt to repair virus damage with tools like Reimage Reimage Cleaner Intego |
First spotted by security researcher Ravi[2] in mid-July 2020, this malware belongs to an established ransomware family – GlobeImposter 2.0 (also called Fake Globe). However, the ransom note closely resembles one that is used by Dharma ransomware authors, hence, experts believe that the distributor is related to both strains.
While [email protected] file virus is mostly distributed via spam email campaigns, malicious actors might use other methods to ensure a bigger victim count. Other delivery tactics might include:
- Malicious links/ads embedded on various websites;
- Exploit kits and software vulnerabilities;[3]
- Software cracks or pirated program installers;
- Unprotected Remote Desktop connections, etc.
Once inside a Windows environment, [email protected] ransomware would perform several system changes, which include registry database modification, Shadow Volume Copy elimination, process termination, malicious file injection, etc. The malware performs these changes in order to prepare the system for the file encryption process. We suggest using repair tools like Reimage Reimage Cleaner Intego to attempt to fix virus damage after [email protected] ransomware removal is performed.
A full system scan is performed in order to find predetermined types of files, which include PDF, MS Office documents, Zip, JPG, and many other most commonly used files. The extortionists program malware to look for these files to cause the maximum amount of damage to victims, hence increasing chances of ransom payments.
[email protected] ransomware is a file locking virus that stems from GlobeImposter malware family
TorS@Tuta.Io ransomware is a file locking virus that stems from GlobeImposter malware family
As soon as file encryption is initiated, victims then soon notice that they are unable to open and use them. This unfortunate consequence is that it makes ransomware like [email protected] virus so devastating. Users might never get their files back, so it is important to employ powerful security software that would prevent such outcomes from happening in the future.
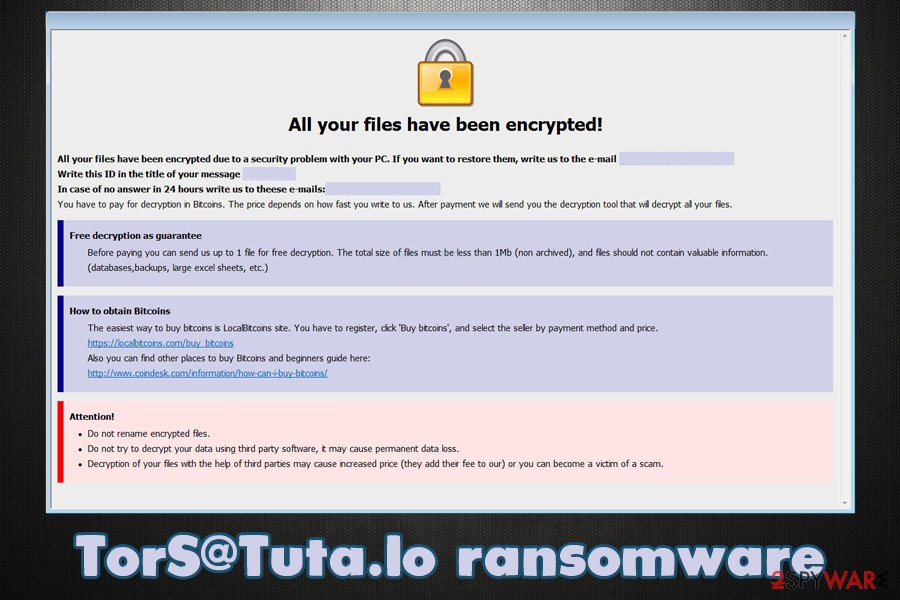
To inform users, hackers behind [email protected] ransomware deliver a pop-up window, which reads:
All your files have been encrypted!
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail: [email protected]
Write this ID in the title of your message:In case of no answer in 24 hours write us to theese e-mails:[email protected]
You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 1-3 file for free decryption. The total size of files must be less than 5Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click ‘Buy bitcoins’, and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Attention!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
However, paying the ransom is not recommended by most security experts, as the attackers might simply take the money and never provide the [email protected] ransomware decryption tool that is needed for data recovery.
Instead, we suggest you remove [email protected] ransomware virus from your computer with a powerful anti-malware software and then use alternative methods for data recovery. You will find a full guide below.
[email protected] file recovery options
Once you get infected with ransomware, an automated process is initiated, which is embedded within malware’s functionality – it uses a powerful encryption algorithm to lock all personal files on the system. Unfortunately, this process is not reversible with [email protected] file virus elimination.
Anti-malware software can be used to get rid of the infection itself so that no incoming files would be encrypted anymore. However, all the data which was present on the computer when the infection occurred will be inaccessible even after malware removal. Most users have a huge misconception about this process and believe that security software can help them open [email protected] files.
So the question remains: how to recover [email protected] files? The answer is, unfortunately, not a positive one, as the only secure method to retrieve data is by copying it over from backups that should have been prepared before ransomware struck.
There is also an option to pay cybercriminals so that they provide the decryption tool. However, there have been numerous cases when victims did not receive what they were promised – keep in mind that these people are cybercriminals.
If you had no backups, here are your remaining options of restoring [email protected] files:
- Using third-party data recovery tools that might be able to retrieve at least some portion of the lost files;
- Attempting to use built-in recovery features, such as Windows Previous Versions Feature or System Restore;
- Waiting till security researchers find a weakness in malware’s code and develop a working ransomware decryptor.
For more details on how to perform these steps, check our recovery section at the bottom of this article.
There are very few options of recovering [email protected] virus files if no backups are available
There are very few options of recovering TorS@Tuta.Io virus files if no backups are available
A correct way to eliminate [email protected] ransomware and deal with its consequences
As mentioned above, [email protected] ransomware removal is not the same as file recovery, and these two processes should be treated as two different things. However, since most of the victims of ransomware typically never encountered such an infection before, they do not know how to handle the [email protected] virus file situation.
If you had no backups of your files and they are important to you, you should first back them all up on an external device, such as a USB flash or cloud storage. Keep in mind that encrypted files do not hold malicious code inside them, so they are safe to use in all cases. As soon as backups are ready, you can remove [email protected] ransomware from your machine. For that, you should download powerful anti-malware software and perform a full system scan. Note that members of this malware family might attempt to disable your antivirus, so you can access Safe Mode with Networking as explained below to bypass this feature.
Once you get rid of the [email protected] file virus infection, you can attempt to recover your data as per the instructions provided below.
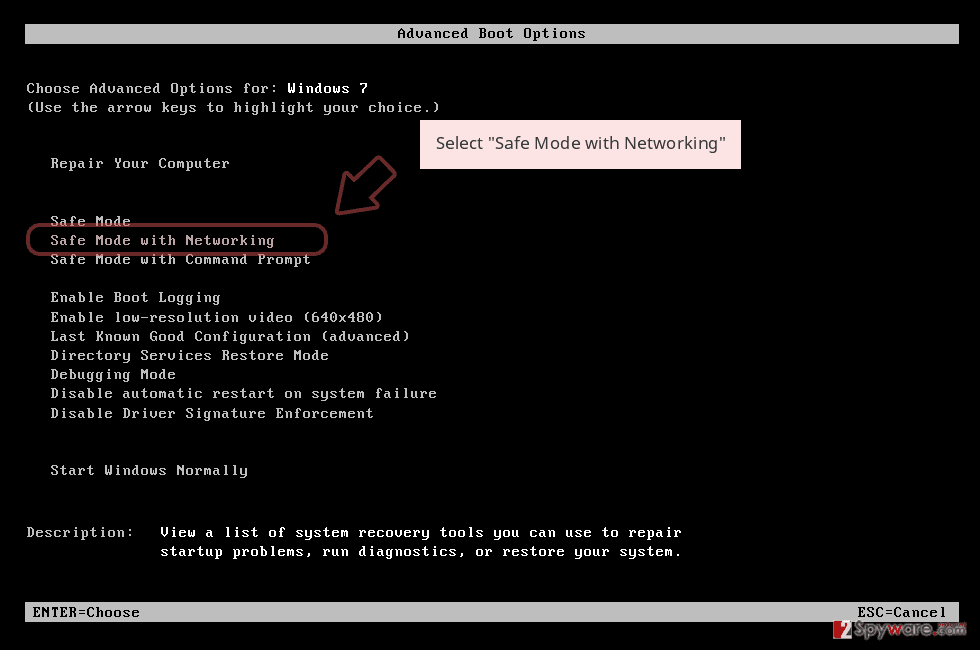
Remove [email protected] using Safe Mode with Networking
In case of malware is tampering with your security software, you can access Safe Mode with Networking:
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
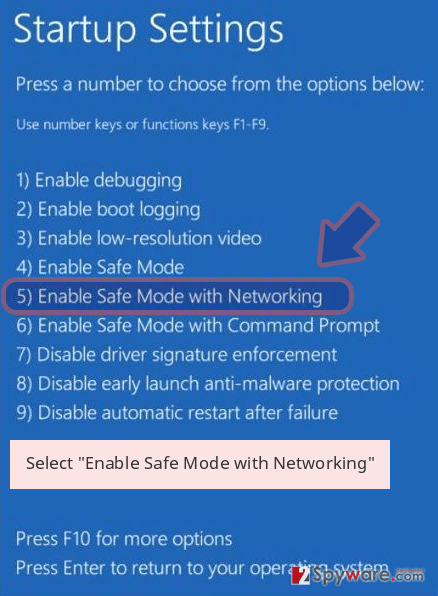
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete [email protected] removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove [email protected] using System Restore
System Restore is one of the methods that can be used in order to recover your computer to the previous state (this might not be successful is the virus eliminated files needed for this feature to be useful):
Bonus: Recover your data
Guide which is presented above is supposed to help you remove [email protected] from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by [email protected], you can use several methods to restore them:
make use of Data Recovery Pro
Data Recovery Pro is one of the most popular recovery applications that is mostly used for lost or accidentally deleted files. In some cases, it can also retrieve working copies of ransomware-encrypted files, although the success rate depends on many factors, including how much you used your computer after getting infected with [email protected] ransomware.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by [email protected] ransomware;
- Restore them.
Try the built-in Windows Previous Versions
This feature can only work if the virus failed to delete Shadow Volume Copies.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer might be able to restore all the encrypted data
In those rare cases, when ransomware fails to delete Shadow Volume Copies, ShadowExplorer is the best tool to use for file recovery.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryption tool has yet been created
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from [email protected] and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can’t grant a full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features.
Nevertheless, there’s a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
While much of the data can be accidentally deleted due to various circumstances, malware is also one of the main culprits that can cause loss of pictures, documents, videos, and other important files. Potentially unwanted programs may clear files that keep the application from running smoothly.
More serious malware infections lead to significant data loss when your documents, system files, or images get locked. Ransomware is the one that is focused on such functions, so your device gets useless without access to needed data. Even though there is little to no possibility to recover after file-locking threats, some applications have features for such recovery in the system.
In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
This entry was posted on 2020-07-17 at 09:49 and is filed under Ransomware, Viruses.

