PRT ransomware is the threat that demands money in the form of Bitcoin from victims after the file encryption made their data useless
 PRT ransomware – a cryptovirus that gives each victim a uniques victims’ ID that indicates a particular device for the malicious actors. This is needed for the decryption and file recovery, but it is not recommended to contact virus creators since this is a version of powerful Paradise ransomware. There are no options for the decryption, or information that developers can restore your files after the payment, so do not consider paying the demanded amount. This is not a very much changed version in the family, so based, on previous variants this is not the time to trust malicious actors. R00t ransomware is one of the more recent versions released before the PRT virus.
PRT ransomware – a cryptovirus that gives each victim a uniques victims’ ID that indicates a particular device for the malicious actors. This is needed for the decryption and file recovery, but it is not recommended to contact virus creators since this is a version of powerful Paradise ransomware. There are no options for the decryption, or information that developers can restore your files after the payment, so do not consider paying the demanded amount. This is not a very much changed version in the family, so based, on previous variants this is not the time to trust malicious actors. R00t ransomware is one of the more recent versions released before the PRT virus.
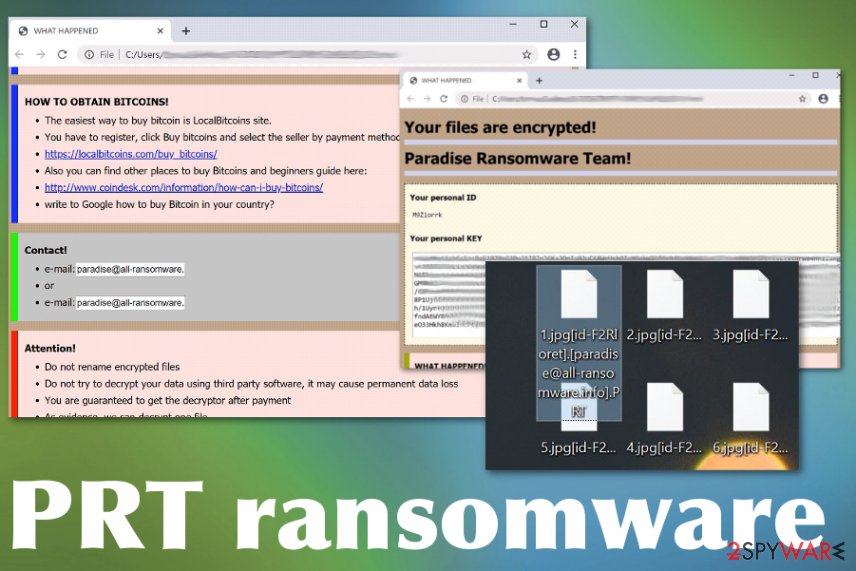
PRT ransomware virus gets this specific name from the pattern of a file marker that is placed on encoded data after the process of encryption. When RSA 2048 encryption is employed for the file locking, affected files get .[id-victims’ID-][[email protected]].PRT after the original file type extension, so the victim can see which files got affected. Unfortunately, photos, videos, documents, archives, and even databases all get locked at once. Even though ransomware is not encrypting system files, the virus can easily affect those files directly by accessing system folders, settings, and manipulating files, functions, or applications.
| Name | PRT ransomware |
|---|---|
| Family | Paradise ransomware |
| File marker | .[id-victims’ID-][[email protected]].PRT |
| Encryption method | RSA 2048[1] |
| Ransom note | #DECRYPT MY FILES#.html – the pop-up window that is displaying the victims key, additional details and methods to pay, places where Bitcoins can be bought, contact emails of criminals and suggestions to send files for test decryption |
| Contact emails | [email protected] and [email protected] |
| Distribution | The threat is known to use typical malware spreading methods that include web modules and infected files attached to email notifications posing as financial messages from legitimate companies or services. Torrent or pirated services also deliver infected files during installations, so payload of the cryptovirus can enter the system |
| Damage | When the payload of the malware gets on the system is possible that trojans or info-stealers[2] also end up installed behind your back. However, the biggest issue regarding such infection is the blackmailing feature and money involvement Users can lose their data and money when they pay for the attackers and end up not getting the decryption tool |
| Elimination | The proper PRT ransomware removal can be performed with anti-malware tools. The virus tends to install additional files or disable particular functions, applications, so the persistence of the cryptovirus is higher and you cannot easily remove it or recover encoded files |
| Optimization | You should note that file recovery on the system that is still affected by the malware can lead to permanent damage and system corruption. Get a system repair tool or a program like Reimage Reimage Cleaner , so you can check for affected files and fix any virus damage if needed |
PRT ransomware targets various devices but focuses on the Windows operating system, where it can be easily executed and launched. Threat lands on the machine and begins to search for files suitable for encryption. It runs through driver letters on the computer and identifies the ones with .doc, .docx, .xls, .pdf, and other types of commonly used files.
When data gets detected, PRT ransomware infection starts with the encoding procedure, which ends with the file marking. All affected files receive the long extension, including their victims’ ID and a contact email used for reaching malicious actors. Then the pop-up window appears with the following message-instructions:
Your file are encrypted!
Paradise Ransomware Team!Your personal ID
Your personal KEY
WHAT HAPPENED!
* Your important files produced on this computer have been encrypted due a security problem.
* If you want to restore them, write to us by email.
* You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
* After payment we will send you the decryption tool that will decrypt all your files.
WHAT HAPPENED!
* Your important files produced on this computer have been encrypted due a security problem.
* If you want to restore them, write to us by email.
* You have to pay for decryption in Bitcoins. The price depends on how fast you write to us.
+ After payment we will send you the decryption tool that will decrypt all your files.
FREE DECRYPTION AS GUARANTEE!
* Before payment you can send us 1-3 files for free decryption.
* Please note that files must NOT contain valuable information.
* The file size should not exceed 1MB.
* As evidence, we can decrypt one file
HOW TO OBTAIN BITCOINS!
* The easiest way to buy bitcoin is LocalBitcoins site.
* You have to register, click Buy bitcoins and select the seller by payment method and price
* https://localbitcoins.com/buy_bitcoins!
* Also you can find other places to buy Bitcoins and beginners guide here:
* http:/weew.coindesk.cominformation/how-can-i-buy-bitcoins!
* vérite to Google how to buy Bitcoin in your country?
Contact!
* e-mail: paradise@all–ansomware
* or
* e-mail: paradise@all–ansomware
Attention!
* Do not rename encrypted files
* Do not try to decrypt your data using third party software, it may cause permanent data loss
* You are guaranteed to get the decryptor after payment
* As evidence, we can decrypt one file
* Do not attempt to use the antivirus or uninstall the program
Since PRT ransomware is a version of the previously developed threat, so these instructions containing paying steps and the information about the encryption are not much changed. Even though the initial name of the program window gets changed according to the version on randomly, this is the version of Paradise virus, even the detection names from AV tools determine that.[3]
However, even though we note that you need to use an anti-malware program for the PRT ransomware removal, detection names do not indicate any important things besides the family and heuristic names change depending on the particular AV tool database. So focus on the detection results in general, not the particular name and base your selection of the AV software on the rate of detections, so you can get the best results. 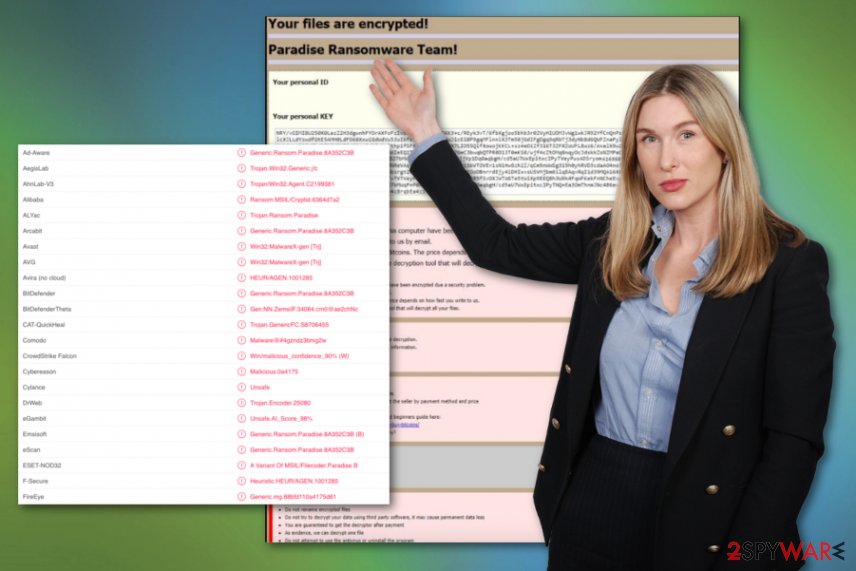
PRT ransomware is a version of another cryptovirus that demands payment for possible file recovery. Before you remove PRT ransomware from the machine, consider to save some of the encrypted files and data associated with the threat on the external device, in case an official decryption tool will be released in the near future. That is not expected since these criminals use powerful and sophisticated algorithms and delete their previous databases.
When it comes to files affected by the virus, when there is no particular tool designed to decrypt them, and paying PRT ransomware creators is not an option, you need to have files backed up on an external device or a cloud service and use them. Not everyone has those options, so third-party programs can be employed, and we have a few options down below for you.
Then you need to consider the damage that PRT ransomware virus leaves in other places and system files that get damaged due to the infection. Manual interference with Windows registry entries, system settings, and folders is not that safe when you are not an experienced computer user, so automatic tools for system repair are more dependable.
You can install a utility like Reimage Reimage Cleaner or another PC optimizer and run the system check, so any parts that get affected by the PRT ransomware virus damage get indicated for you and you can fix system issues without causing additional problems. Then you can focus on data recovery and getting the computer back in the shape that allows processes to run smoothly.
people behind the PRT malware are extortionists and they can promise restoration and recovery of the files, but the aim of the criminals is to keep the virus persistent until they get your money. You may even find additional viruses designed to steal data, damage other parts of the machine, so it is best to react and clean the system with AV tools immediately when you receive the encryption notice. 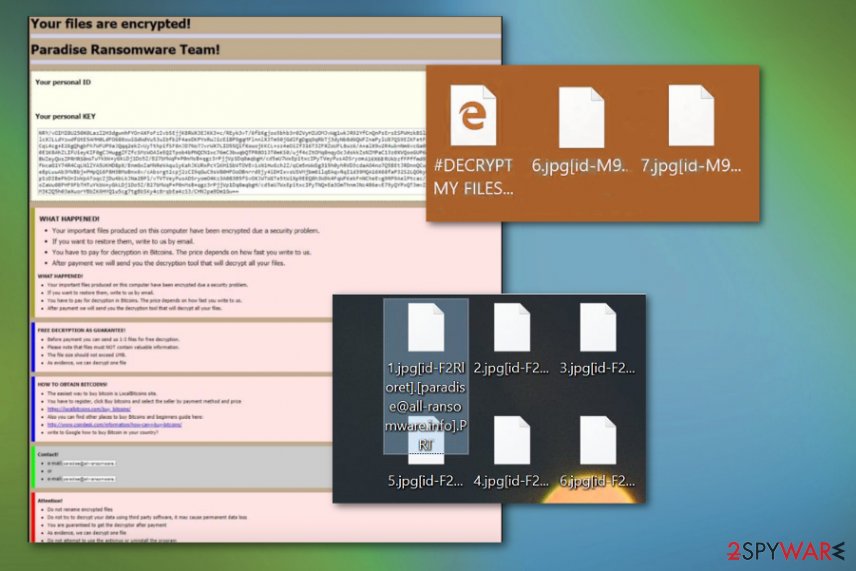
PRT ransomware is the malware that got its name from the file extension including PRT at the end of a filename.
The issue with ransomware infections starts from malicious content
Malicious code can get injected on various types of files, including documents, executables, and system data. Criminals can also create websites with triggers that launch malicious infections and installs ransomware or other threats directly on the machine. You cannot even notice these processes since they all happen in the background.
However, there is a way that can help you avoid infiltration in advance. The best tip is to keep security tools on the machine and running from time to time, so dangerous material gets blocked before accessing the important parts. Paying close attention to received emails and visited content also can help you stay away from dangerous material.
Malicious files come attached to spam emails that pose as legitimate notifications from companies or services that are popular all over the world, so the received email is not raising many questions. However, when you extract the file from such an email or visit the site linked on the notification, malicious macros get triggered and ransomware code loaded directly on the machine. Pay attention to every detail and avoid loading suspicious files on the machine.
Delete PRT file-locking virus with malicious behavior detection-based software
When your data gets locked by the PRT ransomware virus, you need to react immediately. There is a small window when the encryption is still ongoing, and not many other processes can run in the background. If you delete the virus as soon as possible, you can avoid further damage to your machine and system settings.
So try to remove PRT ransomware completely once the ransom message appears. Your anti-malware tool might be the only thing you need. However, if you don’t have such a security tool in the first place, you need to install one right away. Then, the anti-malware tool like SpyHunter 5Combo Cleaner or Malwarebytes can check the system and eliminate all ransomware traces.
However, you may still need to check for any left issues regarding the virus damage after this automatic PRT ransomware removal. So rely on system tools like Reimage Reimage Cleaner and tackle those affected files or altered settings. Then you are free to worry about encrypted files and search for repair solutions.
This entry was posted on 2020-01-22 at 04:18 and is filed under Ransomware, Viruses.

