Kasiski ransomware is the cryptovirus that uses unusual prefix for renaming encrypted files
Kasiski ransomware is the virus that gets photos, documents, archives, video files, and other commonly used data encrypted to have the opportunity for a ransom demand. This ransomware spreads around the world and frustrates users with the money demanding message that appears on the desktop as a wallpaper and a text file. Criminals claim to offer the decryption tool, but that is all for faking legitimacy and trust. Cryptovirus creators only care for your money, so don’t even consider paying them.
Kasiski virus is created by criminals who speak Spanish and want $500 from each victim. The threat is targetting Hispanic users, so it can be distributed around the world easily. Also, it is possible that some versions of the particular threat can aim to English-speaking users and lock files, demand ransoms.
Kasiski virus appears to be a new type of ransomware[1], which, surprisingly, is created for an x64[2] version of Windows. It seems that the threat cannot even work on 32-bit devices. The name of this ransomware is derived from the appendix that the original names of corrupted files get. The virus renames files during the encryption process. Unlike other ransomware, it doesn’t add extensions but appends [KASISKI] prefix to the file names.
| Name | Kasiski ransomware |
|---|---|
| File marker | [KASISKI] prefix comes at the start of every encoded file and shows which data got locked by the threat |
| Targets | Hispanic users all over the world |
| Ransom note | INSTRUCCIONES.txt – a file that delivers the message from criminals and displays all the needed information for the victim about encrypted files and possible recovery options. |
| Ransom amount | The text file with instructions also offers to decrypt files with a decryptor for $500 |
| Distribution | Spam email attachments with malicious macros get delivered to hundreds of users, so when the file is opened, and macros enabled, ransomware can drop straight on the system and start the encryption |
| Distinct feature | The virus is developed for 64-bit systems, so it is not working on 32-bit devices |
| Elimination | Kasiski ransomware removal should be performed with proper anti-malware tools, so all the malicious files get removed and virus terminated |
| Repair | A full system scan with tools like Reimage Reimage Cleaner can significantly improve the state of security because such utilities can repair system files and corrupted registries or functions |
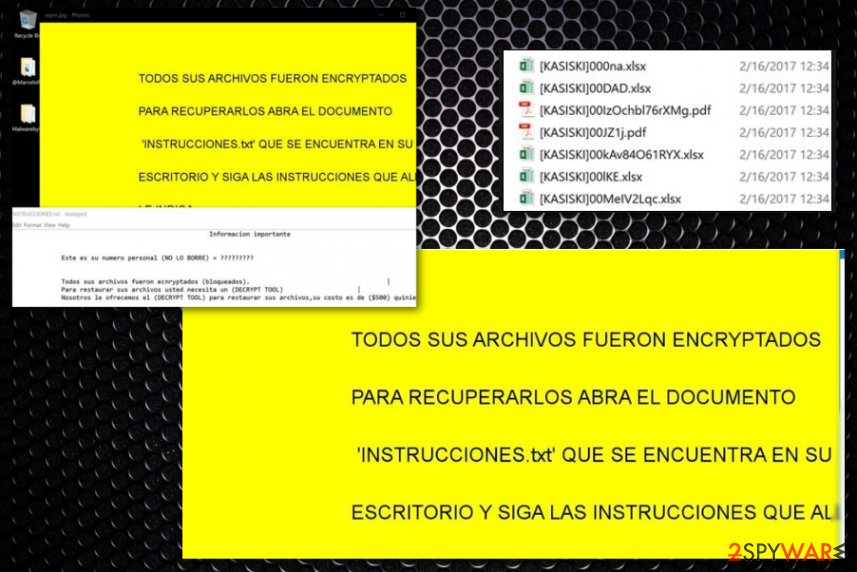
The virus can be installed by the user himself, without knowing what kind of file/program it is. As we have already mentioned, Kasiski malware encrypts[3] almost all files with a strong cipher and then changes desktop background with a basic yellow picture with some text written on it.
Then the virus drops a file called INSTRUCCIONES.txt (on the desktop) which is known to be a ransom note – a message from malicious actors. Cybercriminals typically create such files on the system after corrupting victim’s data. They aim to inform the victim of how the corrupted data can be recovered, and usually, they demand money immediately.
In this ransom note, authors of Kasiski ransomware ask the victim to pay a ransom in Bitcoins. They promise to provide a “DECRYPT TOOL” for $500. Here’s how the beginning of the ransom note looks:
Informacion importante
Este es su numero personal (NO LO BORRE) =
Todos sus archivos fueron encryptados (bloqueados)/
Para restaurar sus archivos usted necesita un (DECRYPT TOOL)
Nosotros le ofrecemos el (DECRYPT TOOL) para restaurar sus archivos, su costo es de ($500) quinie
However, we never advise victims to pay the ransom because obviously, cybercriminals are not the people you can count on. Therefore, we usually advise victims to remove Kasiski ransomware from the system using anti-malware tools because such software can easily find and remove the malware from the affected device.
Unfortunately, for affected system files, you should install a program designed for system repair such as Reimage Reimage Cleaner that can help with Kasiski virus damage. Then find a backup, which is needed for data recovery. If you do not have a needed backup[4], you can try data recovery methods provided below the article.
However, the virus is under analysis at the moment, researchers might come up with Kasiski decryption tool after a while. Until then, take care of the machine, clean virus traces, try to secure your PC from possible additional malware attacks, and try to restore all the encoded data with files stored on external devices. Make sure to double-check before adding any data on the machine, because you may lose your files if any leftover ransomware files trigger the secondary encryption round. 
Kasiski ransomware is the cryptovirus that shows the ransom demanding message on the wallpaper.

Kasiski ransomware is the cryptovirus that shows the ransom demanding message on the wallpaper.
Traditional ransomware distribution techniques
How ransomware crooks distribute their malicious programs depends on their programming skills. More advanced ones employ hacking skills to spread malicious files via ad networks, others use exploit kits[5], and finally, some scammers use Trojans to infect devices with ransomware.
However, the most efficient technique that is the most used by such criminals so far is also a very basic one. Malware authors only need to compose convincing email letters and send them out to hundreds or even thousands of victims. The message typically says that the user needs to view “attached contents.” In most cases, attachments state about some kind of financial data like order information or invoices.
However, we advise users to think whether a) they know the sender personally or not; b) were they expecting to receive such an email or not. If the answer to these questions is no, better stay away from such letters and delete them ASAP. Always do so with emails you were not expecting to get or notifications that contain red flags like typos, grammar mistakes, or shortened hyperlinks. Those can also send you to macro-laced[6] sites or trigger direct downloads of malicious files, malware.
Kasiski ransomware virus termination procedures include AV tools
If your computer was compromised, remove Kasiski ransomware immediately using proper anti-malware tools. Ransomware-type programs often come with various additional features such as an ability to install new malware, transmit personal information, and even more.
To make your PC safe again, it is recommended to use powerful anti-malware software such as SpyHunter 5Combo Cleaner or Malwarebytes. Full Kasiski ransomware removal guidelines are given down below – follow them carefully, do not rush! Using those methods may help you with the proper AV scan too.
You do not want to miss infectious components because if you do so, they might weaken your PC’s security, which would allow other viruses to infiltrate the system easier. When you are done with the proper elimination of all Kasiski virus components, you can go for the data recovery solutions that are also listed below. Make sure to repair system files using Reimage Reimage Cleaner before though.
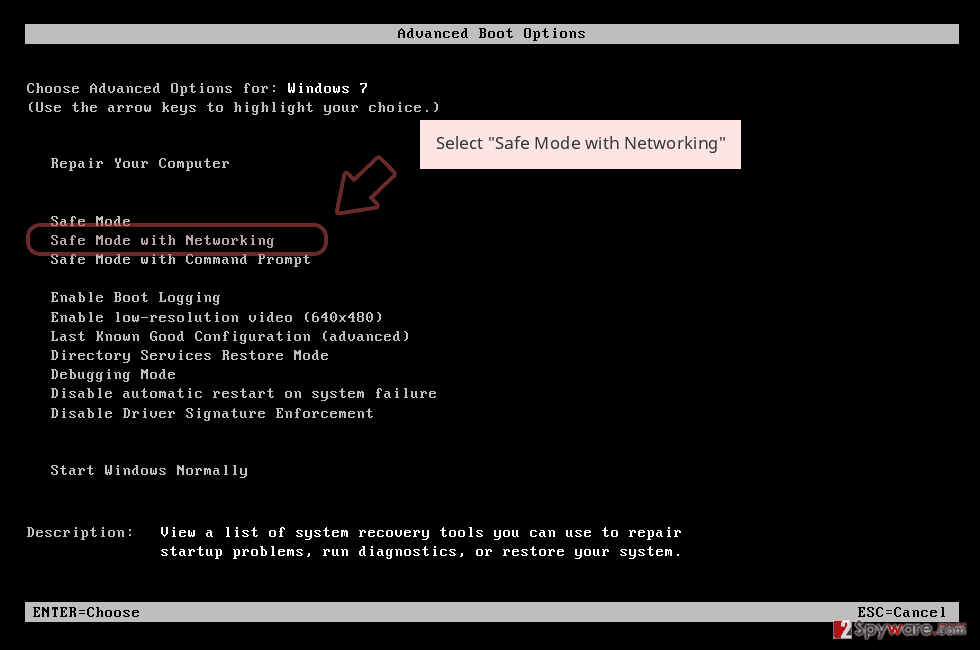
Remove Kasiski using Safe Mode with Networking
Reboot the system in the Safe Mode with Networking and run the AV tool then
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
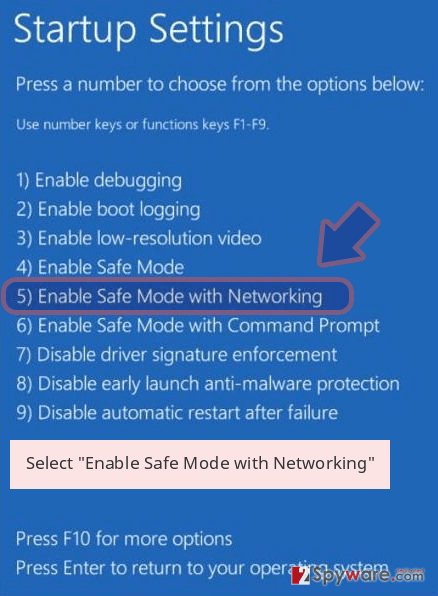
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Kasiski removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Kasiski using System Restore
Make the system virus free by enabling System Restore feature
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Kasiski from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by Kasiski, you can use several methods to restore them:
Data Recovery Pro is the program that can restore your files after encryption and other incidents
You can use Data Recovery pro for encrypted files or for accidentally deleted data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Kasiski ransomware;
- Restore them.
Windows Previous Versions is the feature that can help with affected files
When System Restore gets enabled, you can rely on Windows Previous Versions feature and recover data individualy
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer restores files affected by Kasiski ransomware
The option can work when Shadow Volume Copies are left untouched
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Kasiski ransomware has no decryption tool
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Kasiski and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-03-05 at 02:48 and is filed under Ransomware, Viruses.

