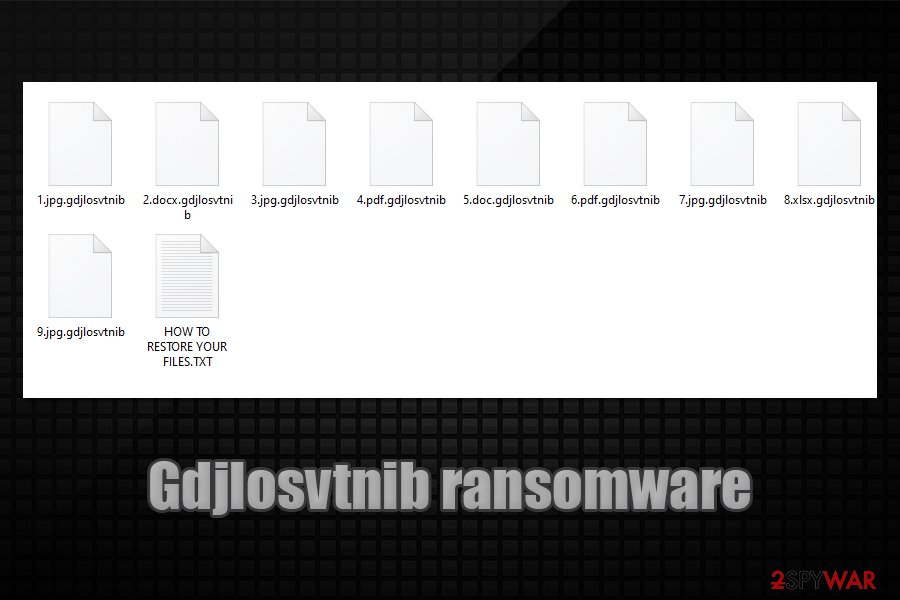
Gdjlosvtnib ransomware – extortion-based malware that might result in a full loss of pictures, music, documents, and other files
Gdjlosvtnib ransomware is a data locking computer infection that mainly targets businesses and organizations
Gdjlosvtnib ransomware is a data locking computer infection that mainly targets businesses and organizations
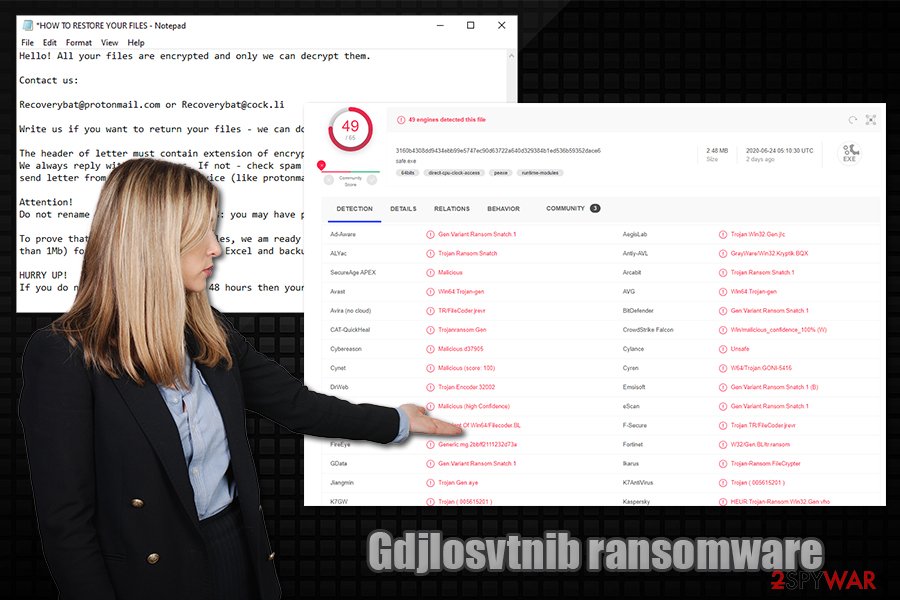
Gdjlosvtnib ransomware is data locking malware that stems from Snatch crypto-virus family, which mainly targets corporate networks, although it does not mean that it can not affect regular consumers as well. One of the first samples of this malware was discovered by security researcher GrujaRS on June 15, 2020.[1]
Once inside the system, Gdjlosvtnib ransomware performs all the necessary changes to the computer and then encrypts all the files located on the local and networked drives with the help of AES[2] cipher. During this time, the malware also allows the attackers to steal all the data from the infected network, which can later be published in case the firm or a person does not agree to pay ransom for Gdjlosvtnib file virus decryption tool.
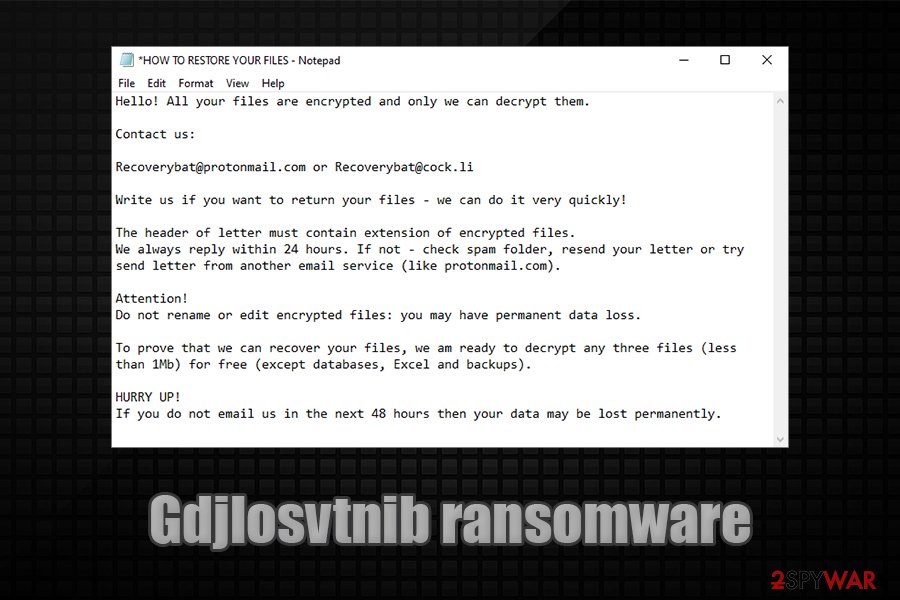
All files that have been affected by this sample will be appended with .gdjlosvtnib file extension, and will no longer be accessible. For communication purposes, malicious actors also leave contact emails [email protected] and [email protected] inside a ransom note HOW TO RESTORE YOUR FILES.txt.
| Name | Gdjlosvtnib ransomware |
| Type | File locking virus, crypto-extortionist |
| Family | Snatch ransomware |
| Distribution | The malware is usually distributed via targeted attacks that utilize weakly protected RDP connections or targeted phishing emails |
| File extension | Each of the files on the local and networked drives are appended with .gdjlosvtnib file marker and can no longer be opened |
| Ransom note | HOW TO RESTORE YOUR FILES.txt |
| Contact | Victims are asked to contact the attackers via [email protected] and [email protected] emails |
| Related files | safe.exe |
| Malware removal | Download and install powerful security software and then perform a full system scan. If security software is stopped by the infection, access Safe Mode with Networking. Note: the infected PC must be disconnected from the network |
| Data recovery | There are few recovery options if no backups were retained. We provide all the possible ones in the recovery section below |
| System fix | In case the machine is suffering from crashes, errors, BSODs, and similar issues, perform a full scan with a repair program such as Reimage Reimage Cleaner Intego |
Snatch ransomware, which Gdjlosvtnib file virus is a variant of, is a strain of malware that was first introduced in mid-2018, and since then several versions have been released, including:
Since December 2019, the malware steals sensitive information from the affected companies and businesses and then threatens to expose the sensitive data publicly, increasing the chances that the ransom is paid. While initial versions asked for 1-5 Bitcoin, newer variants, such as Gdjlosvtnib ransomware, can ask for much more.
Since Gdjlosvtnib ransomware mainly targets companies, it does not use the most prevalent distribution techniques such as spam emails or widely-applicable exploit kits to infect victims. Instead, the cybercriminal gang chooses its targets carefully and then hits them with targeted attacks, suchlike using weakly protected RDPs (Remote Desktop connections), or targeted phishing emails.
In most cases, the attackers spend a prolonged amount of time on the network in order to gain elevated permissions, harvest sensitive information, and only then deploy the encryption process. In some cases, the Gdjlosvtnib virus might also reboot Windows into Safe Mode and perform encryption through there,[3] as it allows it to avoid most of the security solutions installed on the network.
Gdjlosvtnib ransomware is cryptomalware that is designed to lock all personal files on local and networked drives and then demand large sums for their redemption
Gdjlosvtnib ransomware is cryptomalware that is designed to lock all personal files on local and networked drives and then demand large sums for their redemption
Gdjlosvtnib ransomware targets the most common files, such as PDF, MS Office, video, audio, archives, and much more. This is done to cause the maximum damage to the victims and increase the chances of them paying the ransom. After the locking process, which is performed with the help of a symmetric AES encryption algorithm, each of the files can no longer be opened and appears with the .gdjlosvtnib file extension. For example, an encrypted file would look like “document.doc.gdjlosvtnib.”
After that, the computer users are introduced with a ransom note that serves as a message from the attackers, which reads:
Hello! All your files are encrypted and only we can decrypt them.
Contact us:
[email protected] or [email protected]
Write us if you want to return your files – we can do it very quickly!
The header of letter must contain extension of encrypted files.
We always reply within 24 hours. If not – check spam folder, resend your letter or try send letter from another email service (like protonmail.com).Attention!
Do not rename or edit encrypted files: you may have permanent data loss.To prove that we can recover your files, we am ready to decrypt any three files (less than 1Mb) for free (except databases, Excel and backups).
HURRY UP!
If you do not email us in the next 48 hours then your data may be lost permanently.
As evident, victims of Gdjlosvtnib ransomware are urged to contact malware authors within 48 hours, or the data might be lost forever. Additionally, cybercriminals are offering test decryption of three files, which is meant to prove that the decryption tool indeed works. These tricks are very common and are engineered in a way so that the victims would be keener to pay.
However, paying is highly discouraged by security experts, as the attackers might send a non-working decryptor, or never contact victims at all. Instead, a full Gdjlosvtnib ransomware removal should be performed, and then alternative methods used for data recovery. Note that all the files on the network should be backed up before eliminating the malware. It is also important to mention that malware might eliminate itself as soon as the malicious actions are performed, although it is not uncommon for the attackers to leave modules, components, or other malware behind.
Therefore, you should remove Gdjlosvtnib file virus from your system by using powerful security software – we recommend SpyHunter 5Combo Cleaner or Malwarebytes. Additionally, after the elimination is complete, we recommend using Reimage Reimage Cleaner Intego repair tool to attempt to eliminate all the Windows system damage (in some cases, it could prevent a full Windows OS reinstallation).
As for .Gdjlosvtnib file recovery, there is no known method to recover files for free, unless backups are used. Nevertheless, some alternative approaches might be useful – we provided detailed instructions below.
Exposed RDP connections serve as main attack vectors to cybercriminals
Snatch ransomware developers are using the so-called “Big game hunting” technique – this method is used by cybercriminals that choose businesses and organizations in targeted attacks. Other ransomware gangs that rely on this method are Maze, Matrix, LockerGoga, REvil, and many others.
In targeted attacks, the malicious actors do not use the regular infection methods such as massively-distributed spam emails with malicious attachments or software vulnerabilities that thousands of users might be affected by. Instead, they rely on targeted phishing emails or Remote Desktop connections. Security experts from zondervirus.nl[4] provide the following tips to prevent such attacks from happening:
- Targeted phishing email. This method typically relies on upon already leaked or stolen information from data breaches. For example, the email address and the precise name of the targeted victim are extremely valuable to the attackers, as this information can make the email much more believable. Besides, cybercriminals also often employ email spoofing technique in order to make it seem like that “From” address looks legitimate.
In most cases, the attached files (MS Office documents, PDF, zip/rar files) cause the infection to spread as soon as the malicious macro is run on the host machine, although hyperlinks can also sometimes be used to download the payload which grants entry to the attackers. - Unprotected RDP connections. Remote Desktop is a feature that allows users from the same organization to reach another computer remotely. The RDP is often used in companies as the function is extremely useful and free. Unfortunately, this feature has many security flaws, as many companies do not ensure strong security when using it. Thus, it is important not to leave the RDP open to the internet, employ strong passwords, restrict access, and use a VPN.
Once Gdjlosvtnib file virus locks files, they can no longer be opened
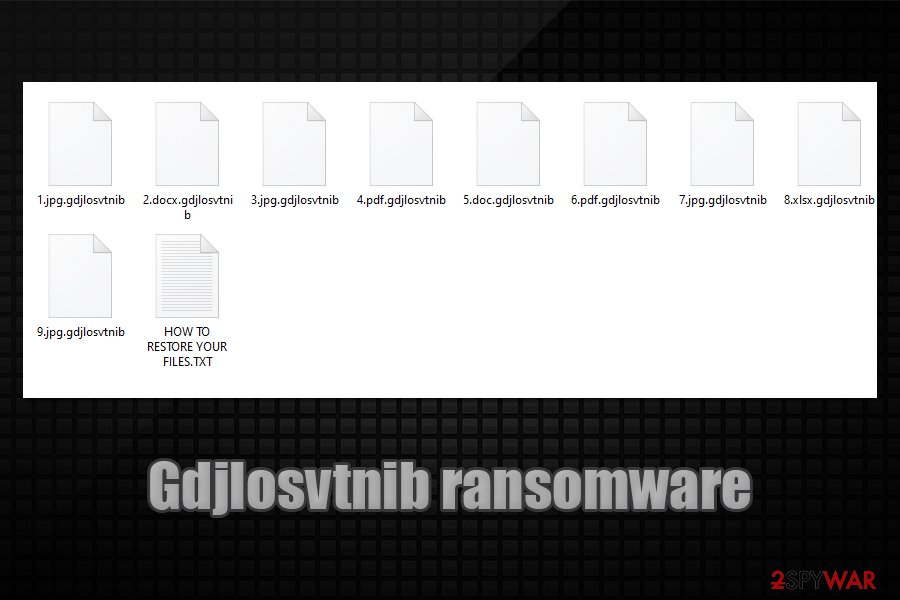
Once Gdjlosvtnib file virus locks files, they can no longer be opened
Gdjlosvtnib ransomware removal instructions
As previously mentioned, Gdjlosvtnib ransomware removal itself might not be needed, as many viruses of such kind simply eliminate themselves as soon as the encryption is performed. However, malicious actors can leave other malware behind, such as a backdoor, which can be used later to access the network once again. Therefore, after the infection has occurred, it is important to disconnect each of the infected machines from the network and only then remove Gdjlosvtnib ransomware from each of the workstations.
To get rid of the Gdjlosvtnib virus, you should employ the most up-to-date security software that is designed to find all the malicious components and other malware on the host system. In some cases, malware might interfere with the elimination process, so you should access Safe Mode with Networking in such a case – we explain how below.
Finally, files should be recovered from backups. If those were encrypted as well, data retrieval options are limited. Nonetheless, we provide all the possible choices in the recovery section at the bottom of this article.
The government has many issues in regards to tracking users’ data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Computer users can suffer various losses due to cyber infections or their own faulty doings. Software issues created by malware or direct data loss due to encryption can lead to problems with your device or permanent damage. When you have proper up-to-date backups, you can easily recover after such an incident and get back to work.
It is crucial to create updates to your backups after any changes on the device, so you can get back to the point you were working on when malware changes anything or issues with the device causes data or performance corruption. Rely on such behavior and make file backup your daily or weekly habit.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware occurs out of nowhere. Use Data Recovery Pro for the system restoring purpose.
This entry was posted on 2020-06-26 at 09:55 and is filed under Ransomware, Viruses.

