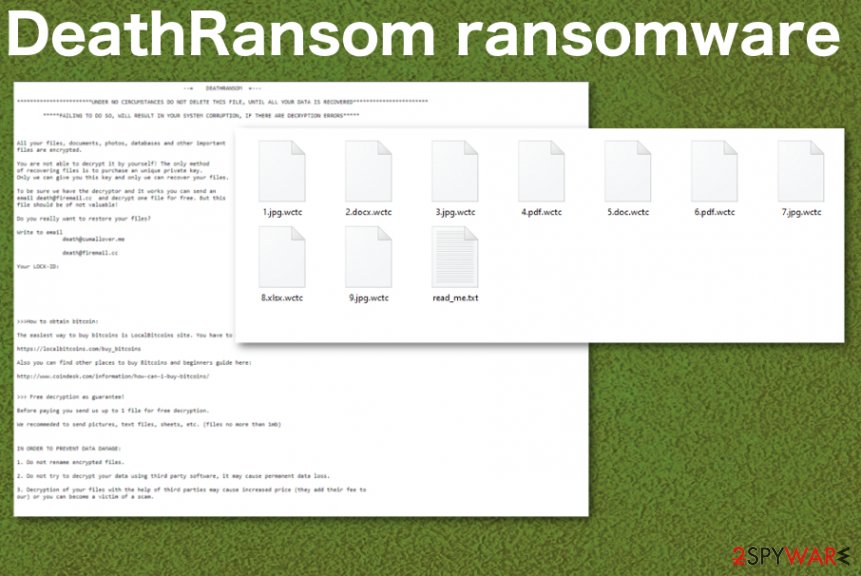
DeathRansom ransomware is the program that requires a ransom in Bitcoin once personal files get encrypted and marked using .wctc appendix
 DeathRansom ransomware is the cryptovirus that names itself in the ransom note read_me.txt and also is called Wacatac due to the file marker .wctc. The threat is classified as ransomware because it focuses on infecting the system and demanding the payment for alleged file recovery. Developers claim to have a decryption tool that is the only solution for your files, and this is why you need to pay. However, not many incidents when people paid ended up positively,[1] so we don’t recommend even considering the option. The best solution is to remove the threat and then recover files using data backups or third-party software.
DeathRansom ransomware is the cryptovirus that names itself in the ransom note read_me.txt and also is called Wacatac due to the file marker .wctc. The threat is classified as ransomware because it focuses on infecting the system and demanding the payment for alleged file recovery. Developers claim to have a decryption tool that is the only solution for your files, and this is why you need to pay. However, not many incidents when people paid ended up positively,[1] so we don’t recommend even considering the option. The best solution is to remove the threat and then recover files using data backups or third-party software.
Even though DeathRansom ransomware virus developers claim that your machine gets damaged if you don’t pay, you need to remove the malware as soon as possible and avoid further system corruption. In time cryptovirus can infiltrate the system and make changes in system folders, settings, and files, so the threat keeps running in the background even when encryption is done.
| Name | DeathRansom ransomware |
|---|---|
| Danger | Cryptovirus is the threat that focuses on getting money from victims, so your belongings are not important for the cybercriminals. File-locking is only a reason for the crypto-extortion, so contacting malicious actors can only lead to more issues, permanently lost files and money instead of restored data |
| File appendix | .wctc marks all the files after the encryption |
| Ransom note | read_me.txt appears on the desktop and in folders with encoded files. This file is created to inform people about encryption and provide the information needed for the payment |
| Contact emails | [email protected] and [email protected] |
| Distribution | Typical ransomware spreading techniques include spam email campaigns with infected file attachments and malicious files packed with pirated software. Each vector involves shady techniques allowing to spread widely at once and only requires downloading or opening the file on the targeted machine. Encryption starts immediately after[2] |
| Elimination | For DeathRansom ransomware removal process, you should employ an anti-malware tool because AV tools are based on malware database and detection[3] that indicates various malicious processes and programs affecting the machine. Once the system scan is done, you can use the antivirus application and delete the virus completely |
| System file repair | Antivirus tools cannot repair virus damage, so you should use Reimage Reimage Cleaner that may indicate system file corruption and possibly fix the damage |
DeathRansom ransomware is the threat that, in general, is not affecting system files because it focuses on common personal files like photos, videos, documents, audio files, and databases or archives. The infiltration starts with file encryption, and malware firstly makes you worried about the data and payment options, so other processes can be launched in the background of your device.
In various cases of other ransomware, the malicious payload dropper also infiltrates the data-stealing trojan or other malware that can run behind the victims’ back and affect the performance significantly besides DeathRansom ransomware encryption. This is one of many reasons why the cryptovirus category is considered one of the most dangerous in the cybersecurity world.
DeathRansom ransomware infiltrates the system quickly when the infected file gets launched on the system or loaded on the machine. Immediately after that, ransomware is executed and triggered, the encryption process starts. At first, files in various formats get located, and then their original code altered using the AES encryption algorithm.
When files get .wctc marker on each document or photograph, you can be sure that the Wacatac ransomware virus is done with encryption. The ransom note read_me.txt also appears around the same time and delivers the following:
–= DEATHRANSOM =—
*******UNDER NO CIRCUMSTANCES DO NOT DELETE THIS FILE, UNTIL ALL YOUR DATA IS RECOVERED*******
*****FAILING TO DO SO, WILL RESULT IN YOUR SYSTEM CORRUPTION, IF THERE ARE DECRYPTION ERRORS*****
All your files, documents, photos, databases and other important
files are encrypted.You are not able to decrypt it by yourself! The only method
of recovering files is to purchase an unique private key.
Only we can give you this key and only we can recover your files.To be sure we have the decryptor and it works you can send an
email [email protected] and decrypt one file for free. But this
file should be of not valuable!Do you really want to restore your files?
Write to email
[email protected]Your LOCK-ID: –
>>>How to obtain bitcoin:
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click ‘Buy bitcoins’, and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
>>> Free decryption as guarantee!
Before paying you send us up to 1 file for free decryption.
We recommeded to send pictures, text files, sheets, etc. (files no more than 1mb)
IN ORDER TO PREVENT DATA DAMAGE:
1. Do not rename encrypted files.
2. Do not try to decrypt your data using third party software, it may cause permanent data loss.
3. Decryption of your files with the help of third parties may cause increased price (they add their fee to
our) or you can become a victim of a scam.
Some researchers state that DeathRansom ransomware is not encrypting files actually because some analysis of obtained samples revealed that files got marked with the extension but not really encoded. The pretend encryption still works for many victims that pay for the decryption possibilities. Also, this feature can depend on the version or indicate that the virus is still in development. 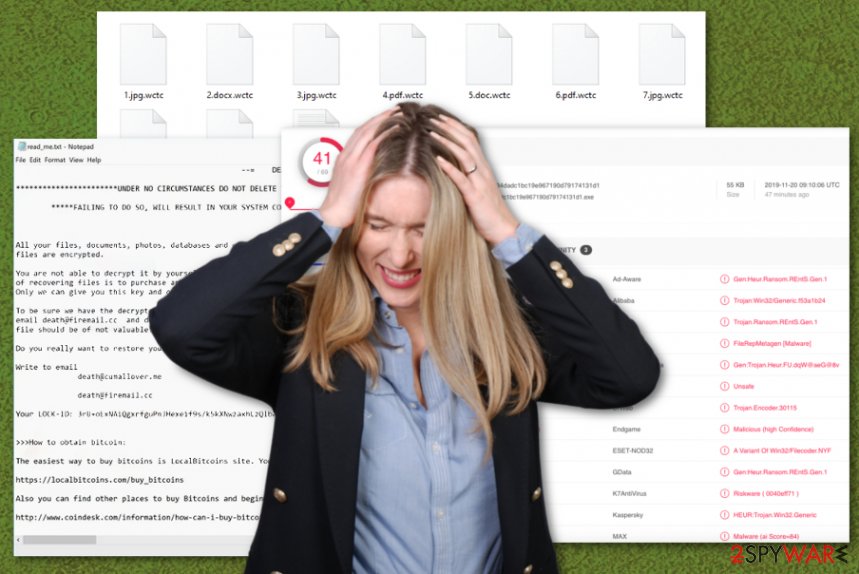
DeathRansom ransomware is the threat that can be indicated by AV tools and removed from the machine during a system scan. DeathRansom ransomware developers encourage people to contact them and pay for the service that they possibly offer – file recovery but that is not the best option, and many experts recommend behaving the opposite. You should clean the system, delete the virus as soon as possible, and repair the damage that can be done already.
By contacting the team of criminals behind the threat, you risk getting malicious files via email instead, and this makes DeathRansom ransomware removal even more difficult. Cryptovirus elimination, in general, is not that easy because you need to find all the files, programs, and associated malware to clean the machine fully.
Fortunately, anti-malware programs are tools based on malware detection that can help you to remove DeathRansom ransomware. Although this is not the easiest process, the automatic method is giving you the advantage to terminate all intruders with one system scan.
A full check on the machine can indicate malware, PUPs, malicious files, harmless background processes, and the DeathRansom ransomware. Detection names depend on each database, but when AV tool says that you need to remove something due to malicious behavior, you should follow the recommended steps.
As for file recovery, we recommend relying on file backups from external devices or cloud databases. Experts[4] note that threats like DeathRansom ransomware can run the encryption on newly added files and damage your data permanently, so make sure that the machine is virus-free before you do anything like that.
An additional tip when you fight DeathRansom ransomware might be the system repair tool and a scan indicating corrupted, damaged, or missing files. Reimage Reimage Cleaner may indicate damaged, affected, or simply outdated files that can further affect the performance and keep the cryptovirus more persistent. After all these system repair steps, you can be sure that recovered files are not going to be affected by the virus. 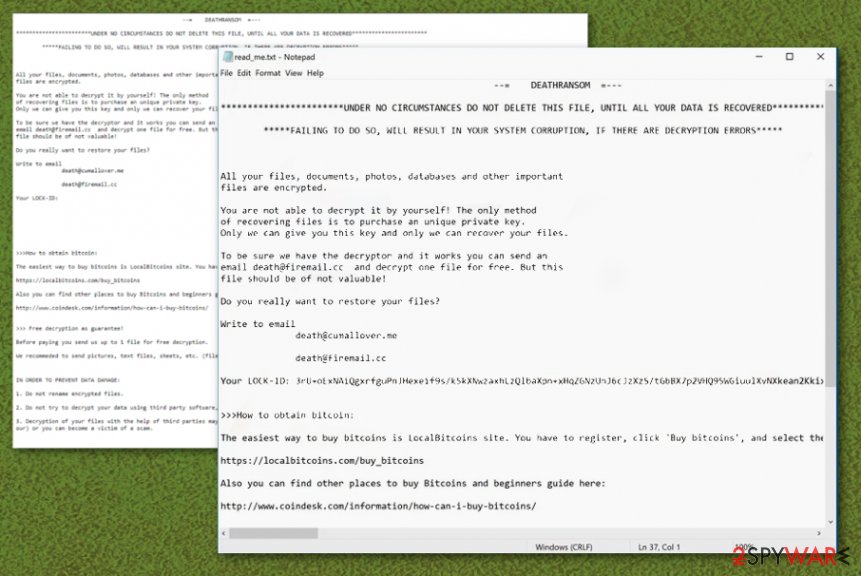
DeathRansom ransomware is the malware that delivers instructions for each victim in read_me.txt ransom note.
Macro viruses find the way on the system to drop the malicious payload
The most common technique used to spread crypto-malware involves infected files as attachments on spam emails. Trojans, other malicious programs can also be delivered and further infect the machine with ransomware this way. The technique involves phishing emails that use names of known companies, services like DHL, FedEx, eBay, and so on.
This method helps to spread around the world because these companies and emails stating about financial details, order information, or shipping updates are commonly received every day. People tend to not pay attention to the sender and all the details that may be red flags and opens emails without thinking twice.
However, once the email is opened, and the file attachment downloaded, launched on the machine, malicious macro viruses get triggered and launch the installation of ransomware payload. You can avoid this infiltration if you pay attention to every received email and delete suspicious ones more quickly.
Terminate the infection and end all the processes related to DeathRansom/Wacatac ransomware
DeathRansom ransomware virus has a few names based on the ransom note contents and on the file appendix that appears on encrypted data. Also, different detection results can frustrate people about the name of this malware. However, the name of the virus is not the important thing.
The most important thing that you need to think about is DeathRansom ransomware removal process because when it comes to cryptovirus, time is not on your side. Encryption is a quick process that affects your personal files, but during the time on your machine, the virus can interfere with system settings and data.
This is why you need to delete the virus damage when you remove DeathRansom ransomware. Corrupted files, affected system functions, deleted or installed programs cannot be fixed that easily. Anti-malware tools work perfectly for the initial ransomware termination, but file recovery and system damage repair requires more help. Rely on Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner, or Malwarebytes for virus damage check and follow the guide below for data recovery options.
This entry was posted on 2019-11-20 at 07:42 and is filed under Ransomware, Viruses.

