DCRTR ransomware – a file locker that can make important files inaccessible as long as victims won’t pay the ransom
DCRTR ransomware is a dangerous computer virus which appears in the computer system after opening a rogue email message or its attachment.
DCRTR ransomware is a dangerous computer virus which appears in the computer system after opening a rogue email message or its attachment.
DCRTR ransomware is a file-encrypting virus that uses a strong encryption[1] algorithm and appends .dcrtr file extension. When all targeted files are encrypted, malware downloads a ransom note called ReadMe_Decryptor.txt where criminals tell to contact them via [email protected] email address. DCRTR virus typically spreads as an obfuscated email attachment.[2] Once a victim opens it, the malicious payload is dropped to the system. Malware immediately alters Windows Registry, downloads malicious files, and might affect legit system processes. As soon as it makes a presence on the affected machine, the ransomware virus runs a data encryption procedure. Crypto-malware targets the most popular types of files, such as Microsoft Office documents, images, audio, video files, databases, or archives.
According to researchers, the .dcrtr extension is not the only one that DCRTR ransomware is using. Since 2018 it has been updated several times and currently has WDM-DCRTR, DCRTR-Crypt, Cryptes, Parrot, and Rhino versions behind its back. The latter variant emerged in May 2020 and can be distinguished from the .rhino appendix and double ransom files info.hta and ReadMe_Decryptor.txt.
| Name | DCRTR |
|---|---|
| Type | Ransomware |
| New version | WDM-DCRTR, Parrot, and Rhino |
| Extensions added | [[email protected]].dcrtr, .crypt, [[email protected]].parrot, [[email protected]].rhin, .CRYZP, .COPAN, .COLORIT, .GOLD, .SOS, .STAFS, .LOCK, .cryptes, .java |
| Ransom message | ReadMe_Decryptor.txt, HOW TO DECRYPT FILES.txt, info.hta |
| Email address | [email protected], [email protected], [email protected], [email protected], [email protected], [email protected], [email protected] [email protected], [email protected]@protonmail.com, [email protected], [email protected], [email protected], [email protected], [email protected] |
| Encryption ciphers | A combination of AES, SHA, and RSA algorithms is used |
| Target | The most popular types of files that are locked by the ransomware – images, audios, videos, text files, databases |
| Main distribution source | Spam messages and their rogue attachments |
| Removal process | Perform the elimination as soon as you spot the first symptoms. You can use SpyHunter 5Combo Cleaner to detect all possibly damaged objects in the system |
| vIRUS DAMAGE | Experts recommend fixing virus damage with a repair tool Reimage Reimage Cleaner Intego. Otherwise, registry entries, Windows files, and processes that the ransomware might have corrupted may be left malfunctioning |
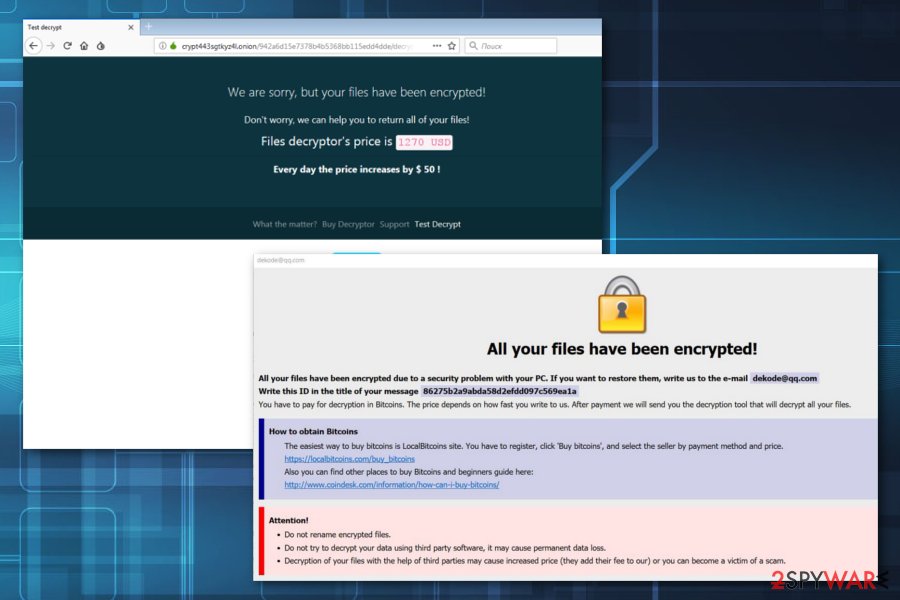
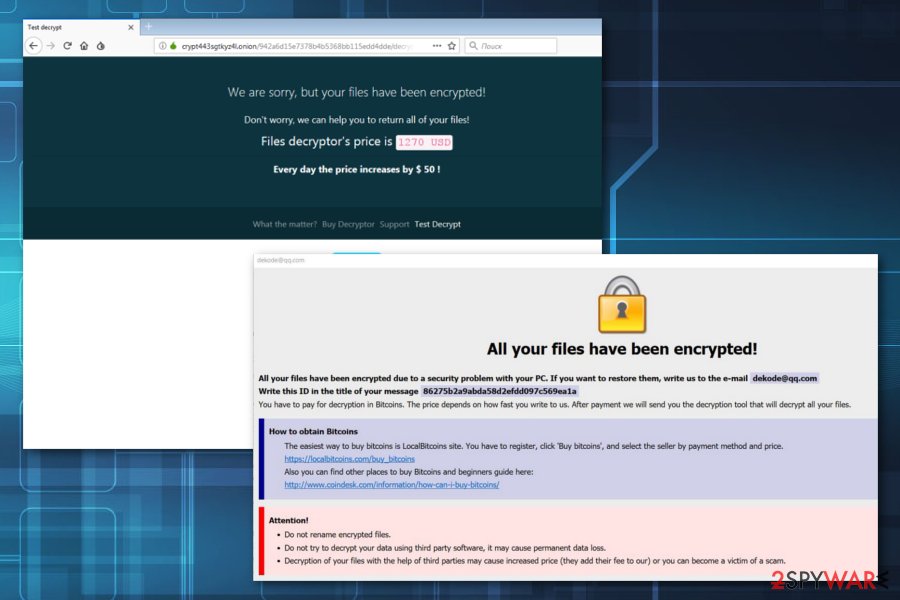
Malware uses a combination of AES, SHA and RSA ciphers to make files on the device inaccessible. The significant feature of the DCRTR is the appended file extension. Typically, it adds [[email protected]].dcrtr suffix to targeted data. Following the successful encryption, the malware provides a ransom-demanding message to the victims. In the text file, authors of DCRTR malware asks to send an email to [email protected]. Victims are urged to do it immediately because the size of the ransom depends on the writing speed.
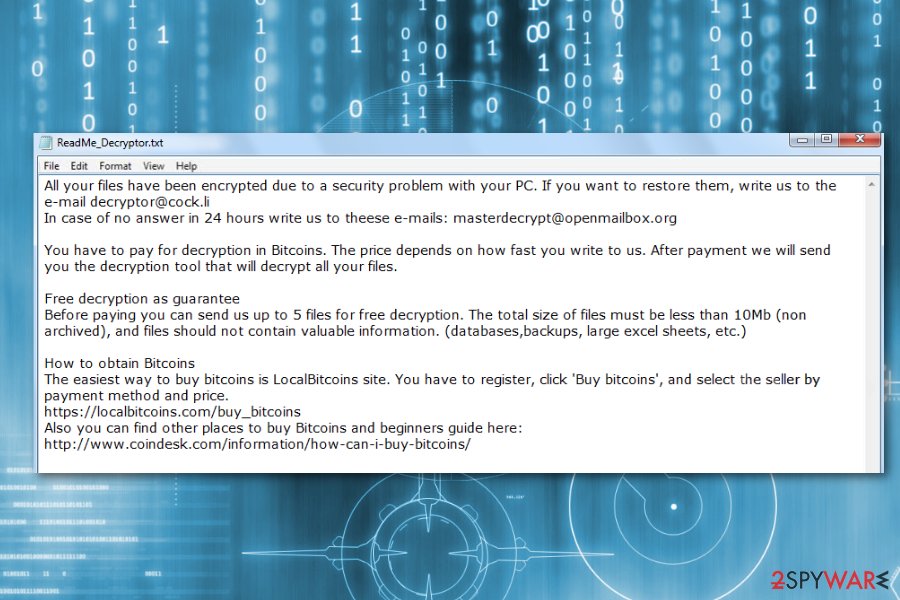
The DCRTR ransom message looks like this:
All your files have been encrypted due to a security problem with your PC. If you want to restore them, write us to the e-mail [email protected]
In case of no answer in 24 hours write us to theese e-mails: [email protected]You have to pay for decryption in Bitcoins. The price depends on how fast you write to us. After payment we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 5 files for free decryption. The total size of files must be less than 10Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)How to obtain Bitcoins
The easiest way to buy bitcoins is LocalBitcoins site. You have to register, click ‘Buy bitcoins’, and select the seller by payment method and price.
hxxps://localbitcoins.com/buy_bitcoins
Also you can find other places to buy Bitcoins and beginners guide here:
hxxp://www.coindesk.com/information/how-can-i-buy-bitcoins/
Crooks also offer to add 5 files for free decryption in order to prove they actually have the DCRTR decryptor. According to the ransom note, victims should receive a response with the number of Bitcoins they have to pay in order to use the criminal’s decryptor. However, if they do not receive a letter in 24 hours, they should send an email again to [email protected].
However, paying the ransom is not recommended[3] because crooks might disappear once they receive your transaction. What is worse, they might ask you to pay more money by threatening that your files will be leaked or deleted. We guess that you definitely do not want to face money losses, especially useless ones. You should not get tricked by these threats and remove DCRTR virus from the device.
Unfortunately, DCRTR removal won’t recover your files. However, virus elimination is needed to clean and fix your computer in order to use it safely again. For that, we highly recommend using SpyHunter 5Combo Cleaner or Malwarebytes tols. Once your device is virus-free, you can use data backups or try alternative recovery methods. Find third-party software below this article and choose the most attractive tool for you. Perform each step as shown in the guidelines and you might be able to restore some of your files successfully.
DCRTR ransomware – a file locking cyber threat which performs the encryption and urges BTC in exchange for the decryption tool.
DCRTR ransomware – a file locking cyber threat which performs the encryption and urges BTC in exchange for the decryption tool.
DCRTR ransomware versions
WDM-DCRTR ransomware
At the beginning of November this year, a new version of DCRTR ransomware was released. This file-locking cyber threat is called very similarly – WDM-DCRTR ransomware. The virus operates in the same way as its old variant. Once installed, it uses unique encryption ciphers to lock important documents on the infected computer. Files appear with the .crypt extension and cannot be loaded successfully until they are blocked by the ransomware virus.
You can recognize WDM-DCRTR virus from this file: FileCryptor.pdb. This sneaky cryptovirus can display various ransom notes. The ransom message can appear as HOW TO DECRYPT FILES.txt. What is even more interesting, WDM-DCRTR ransomware imitates other ransomware viruses. The payment page is designed in the same way as GandCrab-ransomware’s, a ransom note’s text related to the Rapid ransomware. The content of this message says:
the Hello, dear friend E!
Have your files is the All Been The ENCRYPTED
the Do you really want to the restore your files is?
Our email to the Write – [email protected]
and tell’s us your unique ID – ID-XXXXXXXXXXXXXXXXXXXXXXXXXXXXXXXX
Nevertheless, WDM-DCRTR uses the Dharma-related Info.hta files to launch one of the ransom notes. So, as we can see, this cryptolocker tries to imitate other viruses by using similar content. This cyber threat also reaches the system via dubious email messages and their attachments. However, you can get easily messed up which ransomware[4] has infected your PC once you see the note.
Parrot ransomware
It seems that DCRTR ransomware is still in an active development phase since its family keeps growing in 2020. Ransomware researchers detected a Parrot ransomware strain in February after people started reporting files encrypted by [[email protected]].parrot.
Likewise its predecessor, Parrot ransomware takes advantage of the mixed AES and RSA cryptography model, which allows criminals to affect all non-system files and render them useless without a unique decryption key. Victims are demanded to write an email to [email protected] and append one locked file, which is less than 500kb for test decryption.
A quick description of the ransowmare fact is outlined in the ReadMe_Decryptor.txt file positioned on the desktop, which stands for a ransom note. The size of the redemption is not specified, although it’s stated that the payment is expected in Bitcoin cryptocurrency.
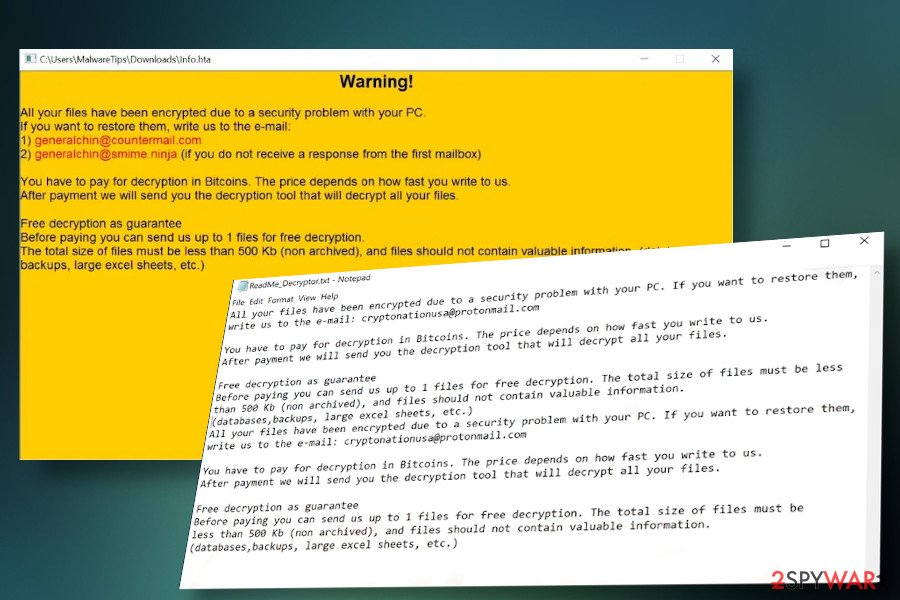
Rhino ransomware
Rhino is yet another DCRTR ransomware family member. Revealed in the middle of April 2020, it is circulating on the internet as a malicious payload attached to email messages. Experts warn that Coronavirus-themed campaigns may be currently used to drive this malware.
DCRTR virus has evolved and released the renewed Rhino ransomware
DCRTR virus has evolved and released the renewed Rhino ransomware
In fact, it’s homogenous with the previous Parrot and WDM-DCRTR variants, except that it uses a distinctive file extension, which is [[email protected]].rhino. Besides, it shows an unusual trait to drop two ransom notes, one on the desktop and the other in the %APPDATA% directory. Victims can find info.hta and ReadMe_Decryptor.txt ransom notes, which contain the following instructions:
Warning!
All your files have been encrypted due to a security problem with your PC.
If you want to restore them, write us to the e-mail:
1) [email protected]
2) [email protected] (if you do not receive a response from the first mailbox)
You have to pay for decryption in Bitcoins . The price depends on how fast you write to us.
After payment we will send you the decryption tool that will decrypt all your files.
Free decryption as guarantee
Before paying you can send us up to 1 files for free decryption.
The total size of files must be less than 500 Kb (non archived), and files should not contain valuable information. (databases, backups, large excel sheets, etc.)
Unfortunately, none of the DCRTR ransomware versions, including Rhino, can be decrypted for free. The victims are expected to pay a ransom ranging from $500 to $1500 in Bitcoins to get a personal decryption software. However, financial support for criminals is not a good idea, especially having in mind that it may lead to identity theft. Instead of paying, remove Rhino with a tool like SpyHunter 5Combo Cleaner and try to retrieve locked files with a reputable security tool.
Methods used for spreading file-encrypting viruses
The virus might be attached to any spam email that appears in your inbox. Malicious spam emails are the primary ransomware distribution methods. Thus, be careful when opening emails from unknown senders and do not rush opening attached files even though they look safe and legit. If you are not expecting to receive anything important lately, better delete all unrecognizable messages that you receive.
Furthermore, ransomware executable might hide under ads on various websites, presented as a software update or any illegal software that you can download from file-sharing websites. Keep in mind that security programs do not always protect from malware if you download malicious files yourself. Additionally, be careful once browsing on pages that you have never seen before as their links might also have malware-laden content injected.
Security experts from LesVirus.fr[5] also remind to create copies of the most important files and save them in the external storage devices. They will be very helpful if ransomware hits your PC. However, if you decide to purchase a USB flash drive, make sure that you keep it unplugged when it is out of usage.
Get rid of DCRTR virus
DCRTR removal is too complicated to perform manually. Therefore, you should not try to locate and delete any malware-related files. This may lead to irreparable damage to the system. For this reason, you should choose reliable software that will take care of your PC. We recommend using Reimage Reimage Cleaner Intego or Malwarebytes to get rid of the cyber threat from your machine. These programs are strong enough to clean your PC from malicious components.
However, after you remove DCRTR virus, you should also reboot the system to Safe Mode with Networking to disable the virus first. In this way, crypto-virus won’t be able to disturb its elimination. After you perform these steps, you can start thinking about the data recovery process. We have provided some methods below this article which we advise trying.
This entry was posted on 2020-05-07 at 04:36 and is filed under Ransomware, Viruses.

