Cryakl ransomware does not give up: latest variant spotted on the wild in January 2020
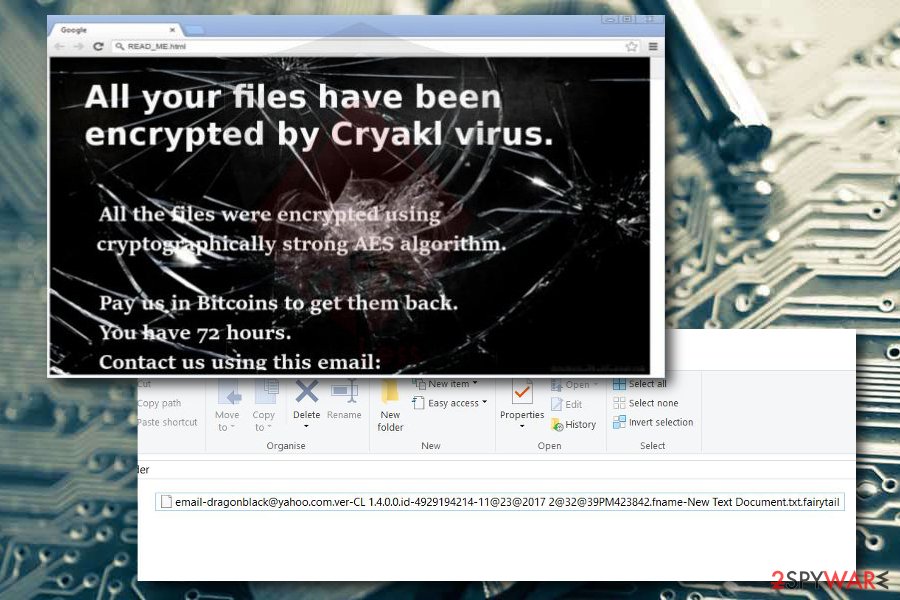
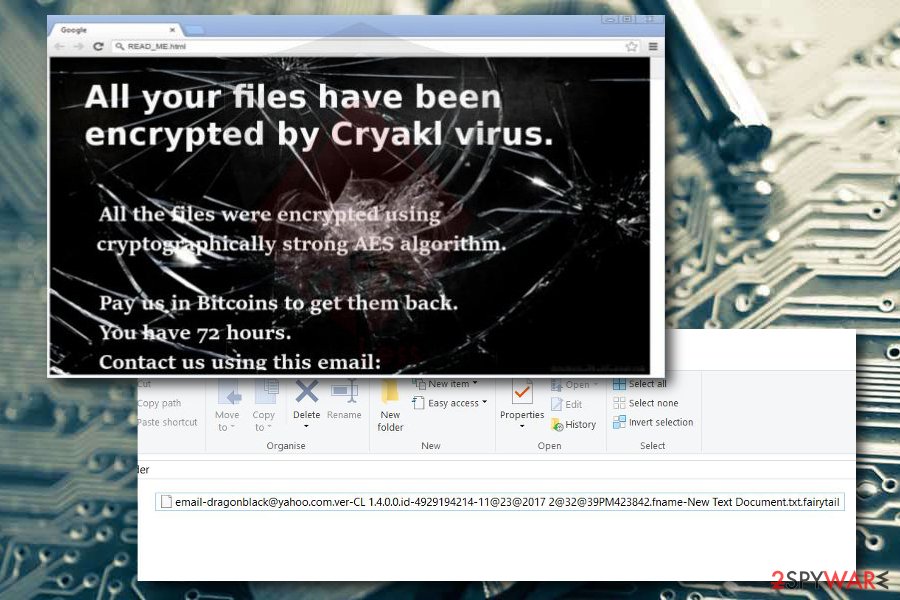
Cryakl ransomware is a term used to describe a crypto-ransomware virus[1], which seek to lock personal files on the infected machine and demand victims to pay a ransom. According to researchers, it uses a combination of AES and RSA encryption algorithms to lock files on a target system and appends .cryakl file extension to distinguish them from the others. Although it does not belong to the ransomware family, its developers attempt to mimic the infamous Locky ransomware.
Cryakl has been first detected in 2017. Soon after the first detection, its developers released a new variant of Cryakl ransomware, which is known as Fairy Tail ransomware manifested. In contrast to the predecessor, the latter switched to the .fairytail and the more complicated one “[email address].ver-[cl malware version].id-[victim’s id]-[month]@[day]@[year] [hour]@[minute]@[seconds] [am/pm].random name-[random file name].[random extension]” file extensions, while the rest of the traits were not changed.
| Name | Cryakl |
| Also know | Fantomas due to the background image used |
| Versions | Fairy tail, Cryak v1.5.1.0 |
| Extensions used |
|
| Common detection | Trojan-Ransom.Win32.Cryakl |
| Encryption used | A combination of AES and RSA |
| Distribution techniques | It is distributed through archived email attachments as a malicious Trojan-Ransom.Win32.Cryakl payload. The emails typically mimic various associations local to the targeted area |
| Symptoms | The ransomware initiates the system’s changes, modifies boot files, registry entries, and then unravels the encryption software. Consequently, all non-system files get unusual extensions. The desktop background is replaced, as well as text file is generated on the desktop |
| Decryption | People can decrypt files locked by the initial Cryakl, Fairy Tail, and Cryak v1.5.1.0 versions with a free Cryakl decryption software developed by Kaspersky. It is available for free on NoMoreRansom[2] website |
| Removal | Before removing the ransomware, make copies of the encrypted files to prevent permanent file loss. Then restart PC into Safe Mode and perform a full scan with a professional AV tool |
| Tip | Fix virus damage with Reimage Reimage Cleaner Intego repair tool. It will check registries, processes, and files for damage and will fix them for good |
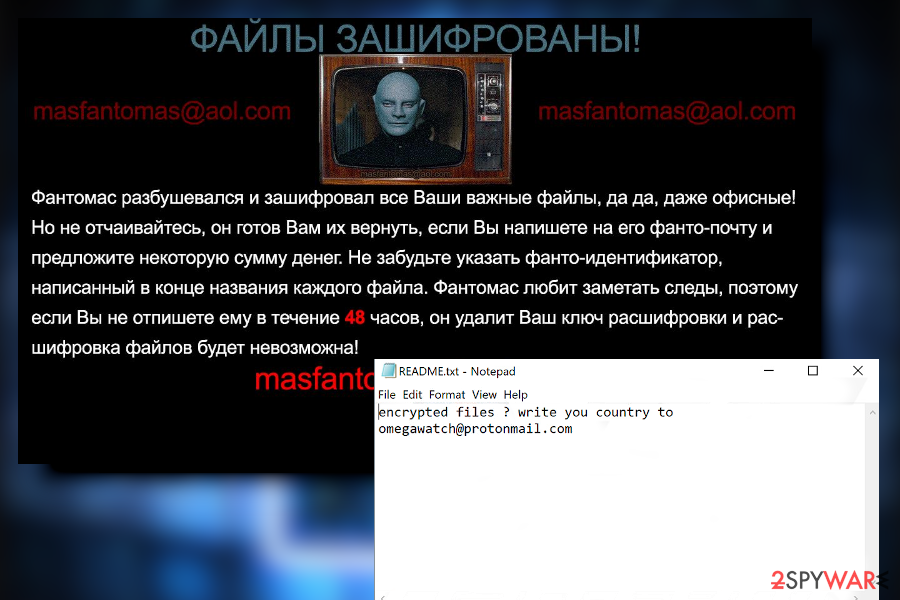
In January 2018, the Belgian Federal Police collaborating with Kaspersky Lab released a free Cryakl decryptor, which can also unlock files encrypted by .fairytail file extension virus. The release of free decryptor induced crooks to invent modified versions of this virus. The latest variant revealed at the beginning of March 2018 is known as Cryak v1.5.1.0. It encodes personal victim’s files with [email protected] http://1.5.1.0.id -1614714137-578233478334310455516964.fname-README.txt.doubleoffset file extension, which can hardly be unnoticed. It generates a README.txt ransom note, which provides a [email protected] email address to be contacted for more information.
As we have mentioned, to encode victim’s files, Cryakl virus, or its later versions, use AES and RSA algorithms. These mathematically complicated sets of codes are used to encrypt (public key) and decrypt (private key) the data on the infected computer. Unfortunately, the decryption key that belongs to developers of Cryakl ransomware is closely guarded on a secret remote server, so there is no way to get it without making a payment.
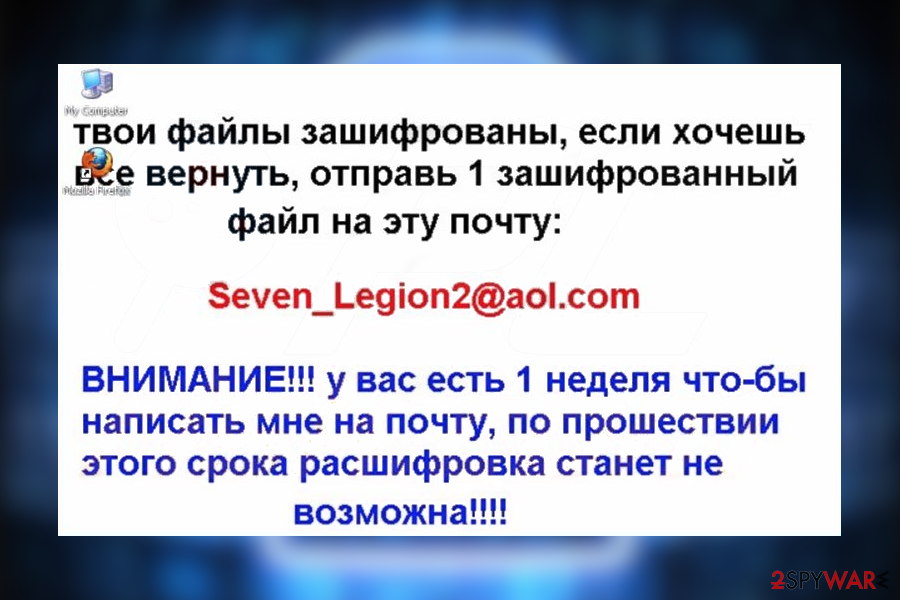
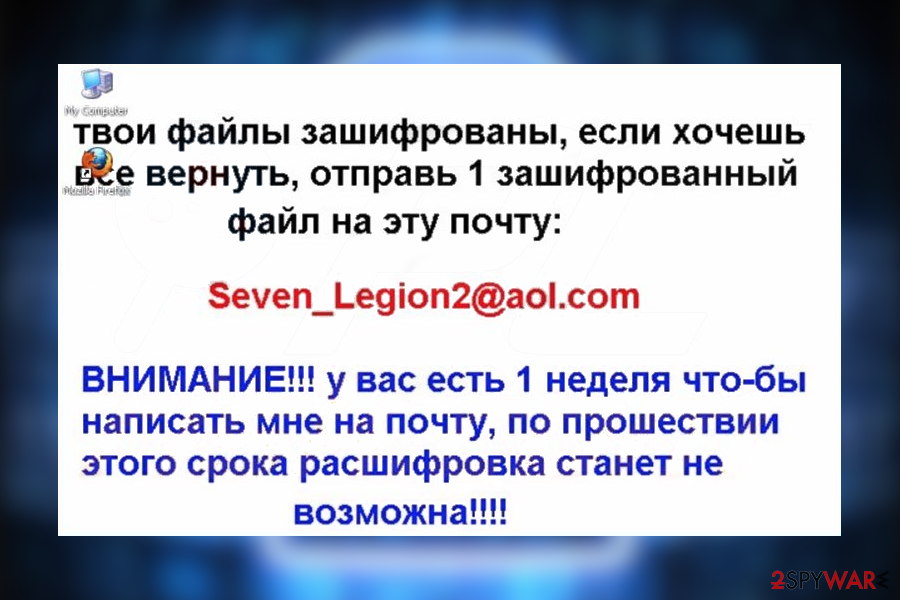
Once the virus finishes its first part of the operation, it drops readme.txt file on the computer’s desktop that provides a detailed ransomware note[3] explaining what should be done to unlock encrypted data. Typically, the victim has to write an email to virus developers and receive an address that should be used to transfer the ransom. Email addresses that have been given by Cryakl developers include:
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected],
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected],
- [email protected]
- [email protected]
If you have been considering making a payment, keep in mind that, even if the money is transferred, there is no guarantee that hackers will really give you a chance to access your files. According to PC experts, you should not even consider paying up. Instead, read on to find out how to remove Cryakl virus from your computer and what methods can you use for your files’ recovery. If you are in a hurry, run a full system scan with Reimage Reimage Cleaner Intego.
The first version of this malware emerged in the first weeks of April 2017. Since then, it has been believed that the virus is discontinued. However, recently, security researcher Michael Gillespie noticed a new version of this ransomware – Fairy tail ransomware.[4]
Cryakl virus developers release new variants since 2017
Cryakl virus developers release new variants since 2017
Just like previous versions, this Cryakl virus variant is quite discreet as it does not disclose much information about its intentions nor its requirements. The virus executes its malicious files, it might be either schvost.exe or another file which resembles an ordinary and a legitimate system file. Afterward, it starts searching for the files matching the extensions from the following list:
.dif, .dip, .djv, .djvu, .doc, .docb, .docm, .docx, .dot, .dotm, .dotx, .dtd, .dwg, .dxf, .eml, .eps, .fdb, .fla, .flv, .frm, .gadget, .gbk, .gbr, .ged, .gif, .gpg, .gpx, .gz, .h, .htm, .html, .hwp, .ibd, .ibooks, .iff, .indd, .jar, .java, .jks, .jpg, .js, .jsp, .key, .kml, .kmz, .lay, .lay6, .ldf, .lua, .m3u, .m4a, .m4v, .max, .mdb, .mdf, .mfd, .mid, .mkv, .mml.
The virus targets the most popular file formats to inflict as much damage as possible. It can attach .cryakl, .fairytail and other extensions to the corrupted files to mark them as corrupted ones. The unique code is subsequently sent to a command-and-control C&C server.
In most of the cases, the virus replaces the desktop background with brief information on the attack and contacts of the developers. Besides, it is sometimes dubbed as Fantomas, due to the picture of a French movie villain used on the background.
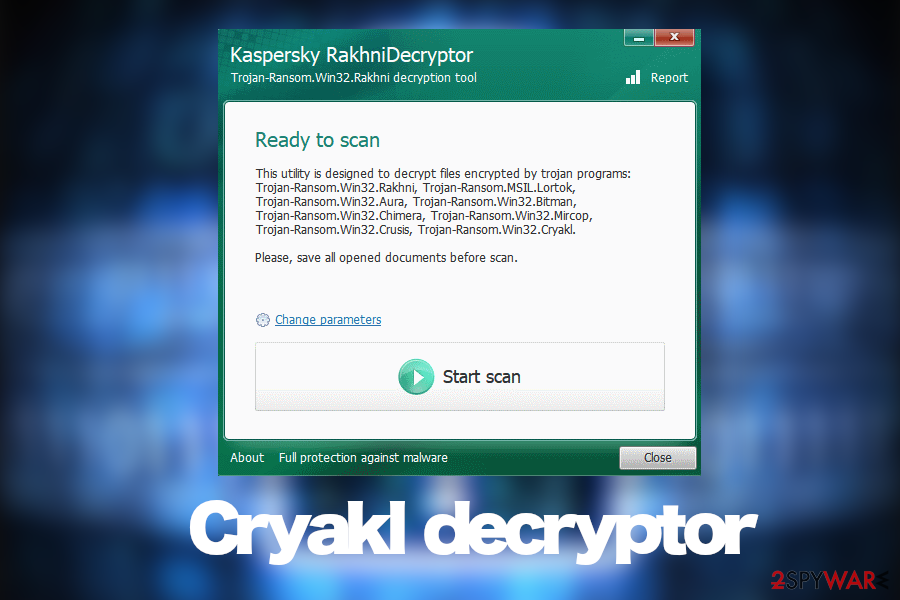
Since Cryakl ransomware employed a set of two related mathematical codes, it seems that there is no other way to recover the files except by paying the demanded ransom. Fortunately, you do not have to pay cybercriminals. Security experts at Kaspersky Lab have released a free Cryakl Decryptor which can be downloaded from Kaspersky’s official anti-ransomware project’s website.
In case the decryptor by Kaspersky Lab does not work, you can try a new version created by a malware researcher James Gourley. He claims that the decryptor works for both – .cryakl and .fairytail virus versions.[5] Since its release on the 30th of January 2018, multiple updates have been made; thus, increasing the chances of successful decryption.
Nevertheless, we cannot assure you that both decryptors will work with the latest versions of the virus. To see what can be done with your files, make sure you take care of the Cryakl removal first.

Cryakl ransomware virus uses AES and RSA encryption algorithms

Cryakl ransomware virus uses AES and RSA encryption algorithms
Cryakl ransomware keeps evolving: latest update found at the beginning of 2020
With the release of the Cryakl decryptor by Kasperky’s group, it has been widely discussed about the end of the ransomware. However, even though it’s not the most proliferate crypto-ransomware on the landscape, its developers are not going to give up easily.
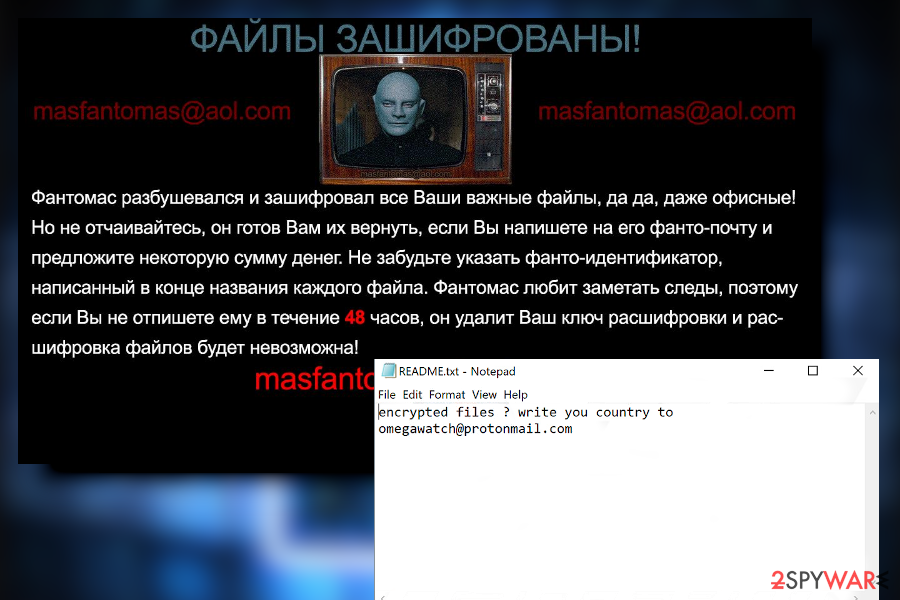
Cryakl uses an image of French villain, which is why it may be dubbed as Fantomas
Cryakl uses an image of French villain, which is why it may be dubbed as Fantomas
Cybersecurity researchers reported a new Cryakl version in the middle of January 2020. Although the latest version does not deviate much from its ancestors, its core has been modified in a way to prevent decryption. It uses RSA and AES mix cryptography and appends [[email protected]][victim’s_ID].[random_letters] extension to locked files. It also generates a README.txt text file on the desktop, which says:
encrypted files ? write you country to
[email protected]
The latest variant is targeting Russian PC users in particular, although it’s real proliferation is still under investigation. If you have been infected by this virus, we highly recommend you to make copies of the encrypted data on a USB flash or cloud and then remove Cryakl from the system.
Upon Cryakl removal, download the Kaspersky’s decryption software that was used to decrypt files locked by .cryakl and .fairytail extensions. There is a possibility that crooks did not do much and the algorithm can be deciphered.
Carefully opening emails can save you from ransomware attacks
It is a common strategy among the majority of hackers to spread their destructive malware through spam emails. Unfortunately, this technique still proves to be highly profitable. Cybercriminals have become so creative that they are now able to forge fake emails that look like to be sent from transportation companies, customs, or local institutions.
Users who haven’t encountered ransomware before and are unaware of ransomware distribution options should be very careful with emails from unknown senders. Make sure you double-check the attachment and, if you have even the smallest doubts, ignore the message.
FBI has already encouraged people to stay alerted and avoid peeking at similar spam emails. When in doubt, you should contact the company, institution directly to avoid further damage caused by the malware.
Cryakl ransowmare has been cracked by NoMoreRansom project. Free descriptor for older versions available
Cryakl ransowmare has been cracked by NoMoreRansom project. Free descriptor for older versions available
Cryakl removal should be performed before file recovery process
If this virus has already took control of your computer, we suggest you to shift to the automatic elimination immediately. For that, you have to install Cryakl removal utility, e.g., Reimage Reimage Cleaner Intego or Malwarebytes, and update it. Later on, start scanning the operating system and let your antivirus detect all the malicious files. After this process is complete, the program will automatically perform Cryakl removal on your computer. You may be required to restart your device after that.
Also, keep in mind that the anti-spyware application does not decode the files, it merely terminates the virus itself. For decoding your files, you may use two different decryptors provided below. Lastly, if you ran into some disturbances and cannot remove Cryakl because the security application simply won’t launch, check the access recovery guidelines provided below.
Remove Cryakl using Safe Mode with Networking
To remove Cryakl with Safe Mode with Networking, you need to use the following steps:
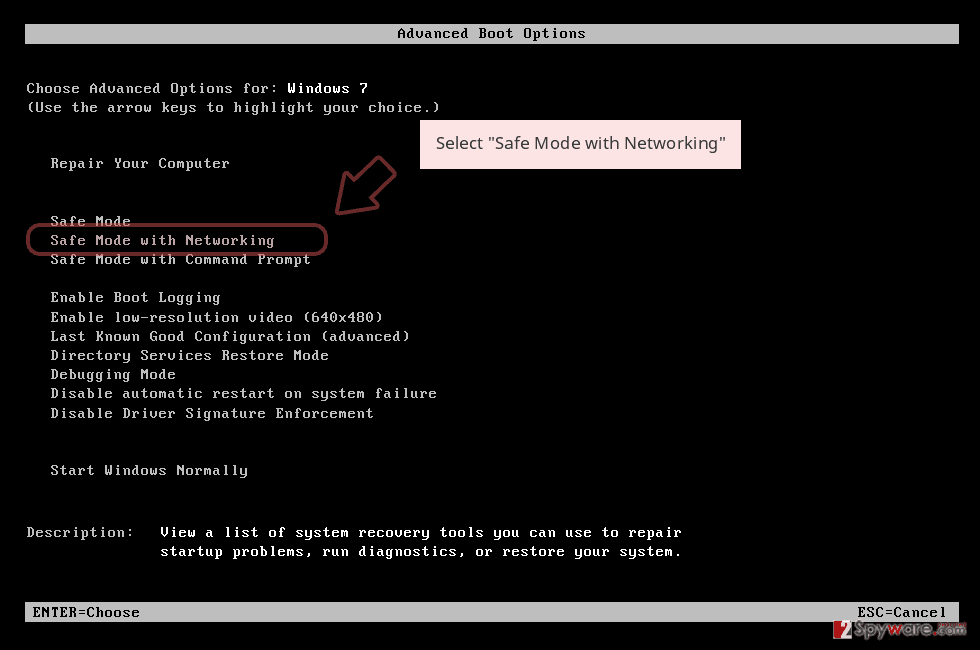
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
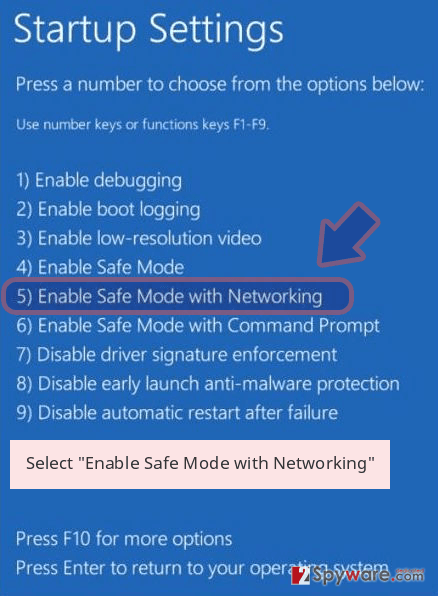
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Cryakl removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Cryakl using System Restore
To get rid of this virus completely, try System Restore method.
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Cryakl from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
We are accustomed to hearing about successful ransomware attack cases which end up with data and even financial loss. Luckily, it does not seem to be the case with Cryakl virus. This infection can be easily decrypted using the Cryakl decryption tool. However, if your computer is infected with some new generation Cryakl version and decryption does not work. We present several data recovery suggestions below.
If your files are encrypted by Cryakl, you can use several methods to restore them:
Using Data Recovery Pro to unlock blocked files
This automatic data recovery technique is especially suitable for those, who are less proficient with computers and wish for a quick and effortless recovery. Though there are no guarantees that the computer will be fully restored to its previous state, there is a chance that you will be able to get back at least some of the files that you’ve lost during the virus attack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Cryakl ransomware;
- Restore them.
File recovery using Windows Previous Versions feature
Before you head to the recovery instructions below, keep in mind that this method is useful when System Restore function was enabled pre-virus infiltration.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Data recovery option using ShadowExplorer
ShadowExplorer is a useful technique to use if you are infected with some less aggressive ransomware virus which does not delete Volume Shadow Copies of the files and ShadowExplorer can recover your data using them. Please follow the instructions below to try this method out.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Data recovery using Cryakl Decryptor
The fastest and most guaranteed way of data decryption is the application of Cryakl Decryptor tool. You can obtain this tool by clicking the previously indicated hyperlink or by visiting official Kaspersky’s website. However, we cannot guarantee that the program works with the latest virus versions.
Alternatively, you can try James Gourley’s Cryakl/FAIRYTAIL decryptor. As we already mentioned, this version has been updated several times, increasing the chances of successful decryption.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Cryakl and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-04-30 at 04:58 and is filed under Flooders, Viruses.

