AnteFrigus ransomware – the cryptovirus that targets only drives associated with removable devices that might be a bug in functionality
AnteFrigus ransomware is the cryptovirus that targets D:, E:, F:, G:, H:, and I: drives, and does not encrypt any files in the C: that is mainly targeted by other ransomware. AnteFrigus ransomware is the virus that gets distributed via a malvertising campaign that redirects users to the RIG exploit kit. This strange ransomware has some unique and uncommon features in comparison with other ransom-based malware strains. However, some researchers speculate that malware is still in development, and different functionalities may only be a flaw in coding, not made un purpose. This virus does not target the C: drive that is commonly affected by the file-locking malware, it only focuses on D:, E:, F:, G:, H:, and I: drives commonly associated with removable devices or network drives.
Since AnteFrigus ransomware doesn’t look sophisticated and fully running, it might be released at a later date with more proper coding and encryption functionalities. At the time, what we know is the distribution technique that involves malvertising, RIG EK that tries to take advantage of Internet Explorer vulnerabilities, and install the payload. When this is successful, the malware encrypts data and marks those files using random appendix, which is also included in the name of the ransom note that delivers instructions for the cryptovirus victim.
Tor payment site link is displayed in the note, so victims can know the price of the alleged decryption key and send the Bitcoin payment to criminals’ addresses. However, that is not recommended because paying doesn’t guarantee the file recovery. The best and the safest option is to terminate AnteFrigus ransomware, stay away from contacting the developers, and rely on your data backups to restore files on the already safe machine.
| Name | AnteFrigus ransomware |
|---|---|
| Unique feature | Ransomware encrypts files in D, E, F, G, H, and I drives, when common cryptovirus targets only C drive. This intruder affects data connected to network storage, removable devices |
| File marker | Encrypted files get the random extension that is also included in the names of other files |
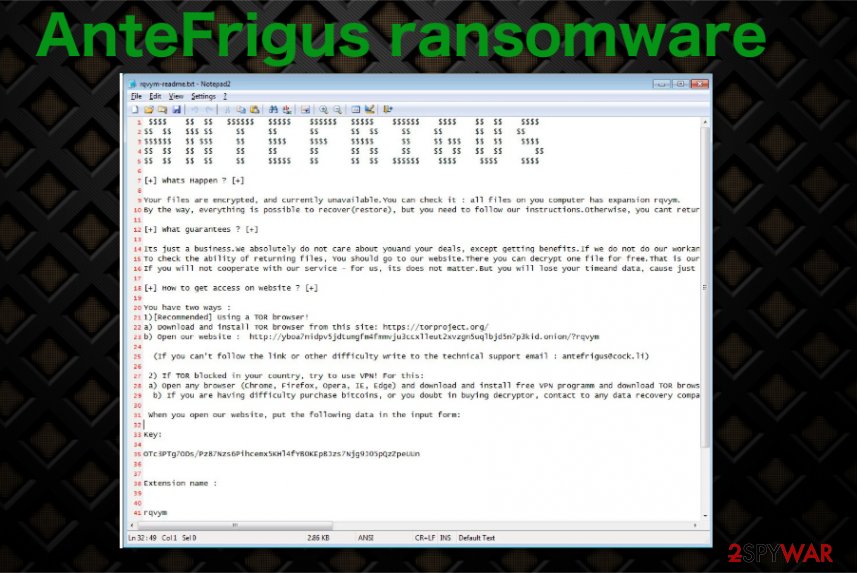
| Ransom note | The text file that includes a demanding message gets placed in various folders like C:\Instraction folder, and on the desktop gets named in a pattern: file appendix-readme.txt |
| Ransom amount | The amount demanded from researchers during the sample tests started at $1,995 and in a few days, got up to $3,990 in Bitcoin. This particular amount of ransom can differ from victim to victim |
| Distribution | HookAds[1] malvertising redirects users to RIG exploit kit that uses malicious scripts hosted on compromised sites and tries to exploit Internet Explorer vulnerabilities. If that happens, ransomware payload can be added on the machine without users’ knowledge |
| Contact email | [email protected] |
| Possible damage | Encrypted files cannot be opened without paying the ransom, other files loaded on the system and processes running in the background affects the data recovery and virus termination functions. The exploited vulnerability can lead to the installation of other threats like trojans or info-stealing malware |
| Elimination | The best tool that you can use for AnteFrigus ransomware removal is the anti-malware tools because such software is capable of detecting[2] malicious activity |
| System cleaning | Since the virus runs through various drives on the machine, it loads files and programs on the device to affect the performance significantly. You should try to fix virus alterations using repair tools like Reimage Reimage Cleaner that might fix corrupted registry entries and restore files in the system folders that get damaged |
AnteFrigus ransomware is the encryption malware, but it acts apart with its unique features. The threat is not encrypting C: drive and focusing on files with the following strings:
dll, adv, ani, big, bat, bin, cab, cmd, com, cpl, cur, deskthemepack, diagcab, diagcfg, diagpkg, drv, exe, hlp, icl, icns, ico, ics, idx, ldf, lnk, mod, mpa, msc, msp, msstyles, msu, nls, nomedia, ocx, prf, rom, rtp, scr, shs, spl, sys, theme, themepack, wpx, lock, key, hta, msi, pck.
There are many speculations why these files are the focus of the encryptionAnteFrigus ransomware. Some users from the business environment save their data in such network shares, so this is possibly the thought-out method of affecting devices. However, samples found in the wild got analyzed and reveled other flaws that indicate this ransomware is still in the test mode, and the strange encryption is not sophisticated enough so it can be called a bug.
When AnteFrigus ransomware gets on the system, it starts encrypting files and marks then using a randomized extension that also appears on the ransom note file name that gets placed in the C:\Instraction folder and on the desktop. C:\qweasd\test.txt file also gets created, which may be used as either debug or lock file.
This AnteFrigus ransomware virus is developed by cybercriminals, so when you have some knowledge about such malware, you should know that there is no reason to trust financially motivated people with your files. In most cases, people who pay the ransom don’t get their files back. You shouldn’t risk getting your files and money permanently lost by paying or contacting the hackers. 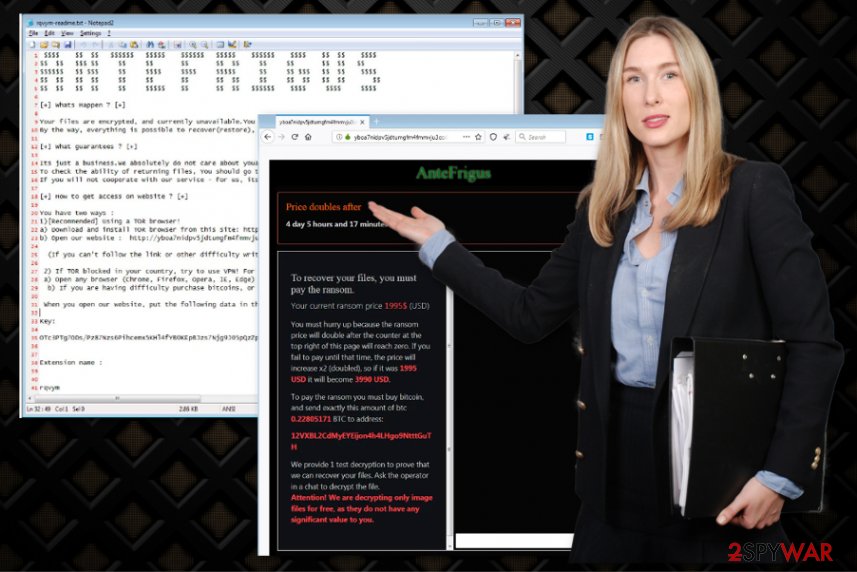
AnteFrigus is the ransomware that doesn’t look fully developed yet, so it is possible that all the strange features may be a bug, not the intended behavior. AnteFrigus ransomware shows a long ransom-demanding message in the file placed on the desktop and in other folders that gets named after the particular file extension. Although the note seems convincing enough, all the claims about the test decryption and cooperation are there to trick people into believing there is a possible way to get your files back after the encryption.
The ransom note displays:
[+] Whats Happen ? [+]
Your files are encrypted, and currently unavailable.You can check it : all files on you computer has expansion mewqsm.
By the way, everything is possible to recover(restore), but you need to follow our instructions.Otherwise, you cant return your data(NEVER).[+] What guarantees ? [+]
Its just a business.We absolutely do not care about youand your deals, except getting benefits.If we do not do our workand liabilities – nobody will not cooperate with us.Its not in our interests.
To check the ability of returning files, You should go to our website.There you can decrypt one file for free.That is our guarantee.
If you will not cooperate with our service – for us, its does not matter.But you will lose your timeand data, cause just we have the private key.In practise – time is much more valuable than money.[+] How to get access on website ? [+]
You have two ways :
1)[Recommended] Using a TOR browser!
a) Download and install TOR browser from this site: hxxps://torproject.org/
b) Open our website : hxxp://yboa7nidpv5jdtumgfm4fmmvju3ccxlleut2xvzgn5uqlbjd5n7p3kid.onion/?mewqsm(If you canít follow the link or other difficulty write to the technical support email : [email protected])
2) If TOR blocked in your country, try to use VPN! For this:
a) Open any browser (Chrome, Firefox, Opera, IE, Edge) and download and install free VPN programm and download TOR browser from this site hxxps://torproject.org/
b) If you are having difficulty purchase bitcoins, or you doubt in buying decryptor, contact to any data recovery company in your country, they will give you more guarantees and take purchase and decryption procedure on themselves. Almost all such companies heared about us and know that our decryption program work, so they can help you.When you open our website, put the following data in the input form:
Key:
Extension name :——— –
!!!DANGER !!!
DONT try to change files by yourself, DONT use any third party software for restoring your data or antivirus solutions – its may entail damge of the private keyand, as result, The Loss all data.
!!!!!!!!!
ONE MORE TIME : Its in your interests to get your files back.From our side, we(the best specialists) make everything for restoring, but please should not interfere.
!!!!!!!!!
You can also encounter additional content appearing on the screen when the computer gets affected. AnteFrigus ransomware delivers a warning pop-up with the statement that your machine got encrypted. The virus can also cause freezes or crashes on the device because during the encryption, many processes get launched in the background. You cannot notice the infiltration itself, but ransomware becomes noticeable when the system gets altered and interfered with.
Then you need to focus on AnteFrigus ransomware removal and do that as soon as possible because once the virus is done encrypting data it starts deleting them from places like Windows registry, system folders or disables security functions, programs needed for file restoring purposes.
When you remove AnteFrigus ransomware, you should also focus on that additional damage and repair affected files. Interfering with system files, directories manually can be dangerous, so we recommend getting a system optimization program or a tool like Reimage Reimage Cleaner that may find and fix the damage for you. Once registry entries get repaired and Windows files replaced with safe ones, you can recover that data encrypted by the malware using file backups or third-party software. 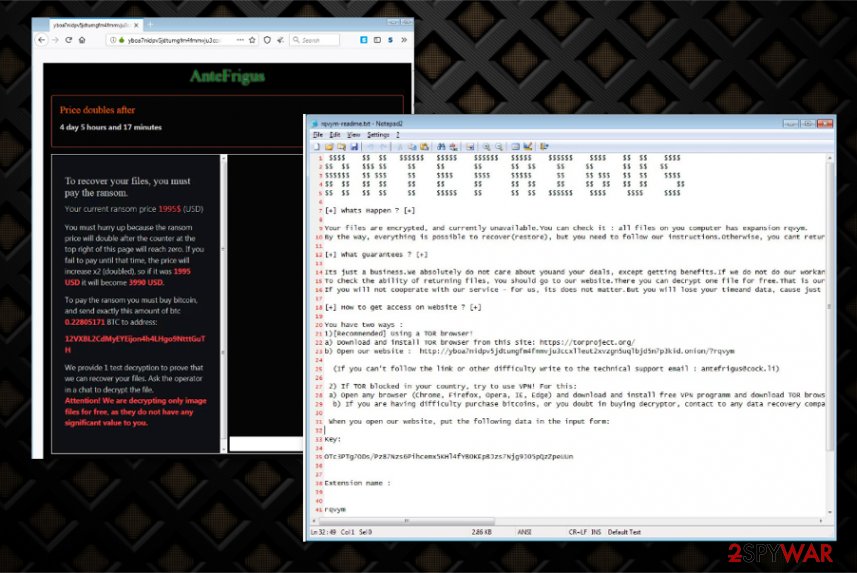
Exploit kits and other deceptive technique
Exploit kit activity linked with the ransomware distribution gets detected less often, but this particular RIG exploit kit is known for delivering trojans, ransomware, and other malware for a while. It works via infected sites when the user is browsing compromised pages that causes redirects or malvertising campaigns. Once the redirect is shown RIG landing page triggers the exploitation of some flaws and the direct malware payload download.
Other vectors used by ransomware developers can include malicious files injected on emails as attachments, hiding behind pirated software packages, and so on. Experts[3] always note about malware delivering methods that lure on deceptive sites, misleading emails, and services like torrents, but people remain to pay less attention than needed to these details.
Terminate AnteFrigus ransomware virus by employing anti-malware tools
The process of AnteFrigus ransomware removal requires your attention and additional help from professional anti-malware tools. Since this threat is distributed involving exploit kits and deceptive online content, you should take the possibility of additional threats already installed on the machine into consideration.
To remove AnteFrigus ransomware alongside all the trojans, malware, and virus-related files, you should employ an anti-malware tool that can run a full system check and detect all the malicious files. If you leave any core files belonging to the virus, your machine can get more affected.
Remember that the AnteFrigus ransomware virus is a serious threat, so you should think about the damage, additional files, and programs added on the machine. Cleaning the system is not only focusing on terminating the threat. Scan the machine using Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner, or Malwarebytes and try to clean the computer as much as possible before you recover your files.
This entry was posted on 2019-11-15 at 04:09 and is filed under Ransomware, Viruses.

