Ymacco Trojan is a dangerous malware that can open backdoors on the infected machine and expose users to malicious websites
Ymacco Trojan is a highly dangerous cyber infection that aims at injecting malicious scripts on the infected machines, downloading other dangerous programs, manipulating system’s performance, rerouting users’ traffic to compromised websites, and more. In short, it can initiate various risk-posing performances on the host machine, so an ASAP removal is recommended.
This trojan[1] has been designed in a sophisticated manner, which is why it is capable of infecting machines stealthily via spam emails, pirated software, cracks, and similar content. Upon installation, it starts running malicious processes, one of the most prominent of which is Uwgcset.exe. Usually, this process is highly obfuscated to prevent detection. Nevertheless, a full scan with a professional AV tool usually ends up warning users about the Trojan:Win32/Ymacco.AAC9, Win32/TrojanDownloader.Delf.CYB, Trojan.GenericKD.43360621, and similar detection.
Unfortunately, the Ymacco virus is extremely deceptive as it does not give its presence straightforwardly. It can hide in the system for quite a while unnoticed until the user noticed high CPU usage by suspicious files, unfamiliar files within random folders, web-browser redirects to sites like z.whorecord.xyz, a.tomx.xyz, pushwelcome.com, pushtoday.icu, and others. Malware like can cause serious issues, such as spyware or ransomware infiltration, so make sure to remove the Ymacco Trojan without a delay.
| Name | Ymacco Trojan |
| Type | Trojan |
| Danger | This trojan poses a risk to the users of infected machine by initiating regular redirects to infected web domains, running malicious processes in the background, and downloading other malware to the system |
| Detection | Trojan:Win32/Ymacco.AAC9 (Windows Defender) Win32:PWSX-gen [Trj] (AVG) Win32/TrojanDownloader.Delf.CYB (ESET-NOD32) HEUR:Trojan-Spy.Win32.Noon.gen (Kaspersky) Trojan.Win32.WACATAC.THFAHBO (TrendMicro) Trojan.GenericKD.43360621 (BitDefender) Trojan.GenericKD.43360621 (B) (Emsisoft) PossibleThreat.ARN.M (Fortinet) Trojan.Downloader (Malwarebytes) ML.Attribute.HighConfidence (Symantec), etc.[2] |
| Symptoms | The Trojan does not manifest itself in a straightway. It runs malicious processes in the background and triggers high CPU consumption. Besides, it may hijack web browsers and redirect the traffic to sites infected by malicious scripts |
| Removal | The trojan cannot be detected manually. It runs malicious files in various system locations and often disguised under legitimate Windows files/processes. Therefore, a full system scan with a professional AV tool is required |
| Fixing the damage | Upon Ymacco removal, a scan with Reimage Reimage Cleaner Intego tool is recommended. Since it has a capability to distort the system’s settings, files, and processes, full optimization is required to prevent issues in the future |
This trojan is often dubbed as Trojan:Win32/Ymacco.AAC9 on the bases of the AV detection brought by Windows Defender. Nevertheless, it’s internationally known as the Ymacco backdoor or trojan virus due to the traits that it has.
- The malicious trojan loader Uwgcset.exe infiltrates machines without being noticed as a component of a malicious spam email attachment or pirated software like cracks or keygens;
- Upon infiltration, it extracts the trojan package and starts running various malicious entries on the Startup and Task Manager;
- It misuses CPU, which is why the system’s performance decreases significantly;
- It aims at weakening the system’s performance to open the backdoor and enable access to other malicious software.
- It creates persistence to avoid detection and removal. Often the processes of AV programs are disabled.
- The Ymacco Trojan virus can inject malicious scripts within web browsers to open malicious websites;
Experts from Virusai.lt[3] claim that a regular system scan with a reputable AV engine is a must to ensure that the system is virus-free. Keep in mind that Trojans like Trojan:Win32/Ymacco.AAC9 virus is difficult to detect because they do not manifest themselves easily, so no scanning the machine on regular bases can mean a long persistence to the virus.
At the moment, a successful Ymacco removal can be initiated with 52 most reputable AV tools as they have crucial updates required for the detection of this pest. Note that the detection may differ regarding the application that you are using, so if you want to be clear if this particular trojan is hiding on your machine, you can check the VirusTotal provided detection names for it.
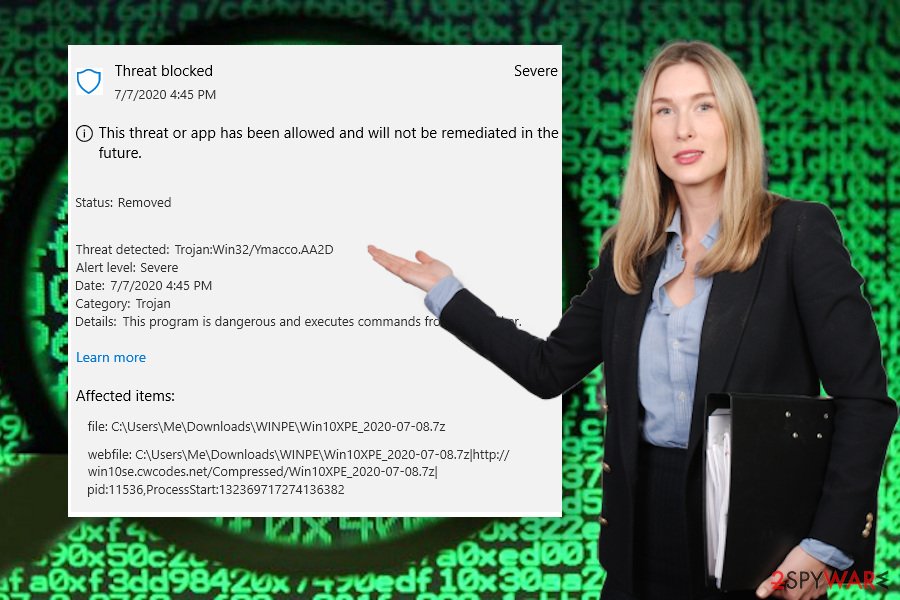
The trojan is often detected as Trojan:Win32/Ymacco.AAC9 and the detection should not be ignored as it signals a dangerous virus to be running on the machine
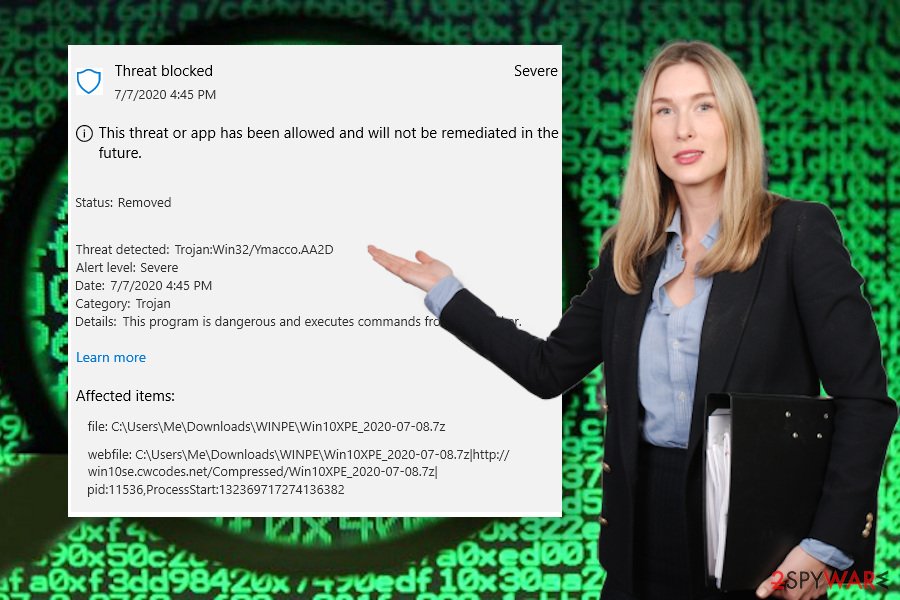
The trojan is often detected as Trojan:Win32/Ymacco.AAC9 and the detection should not be ignored as it signals a dangerous virus to be running on the machine
The good news is that the Ymacco virus is not a spyware or banking trojan. It means that it does not seek to steal your passwords or other credentials. It’s primary task – weaken PC’s security and increase vulnerability. After that, it exposes the user of an infected machine to the malicious domains, thus posing a high-risk of malware downloads.
The bad news is that Ymacco trojan redirects can expose you to sites like z.whorecord.xyz, a.tomx.xyz, and others that are infamous for click-to-download malware distribution, infected software updates, click-bait ads, and other social engineering strategies.
Therefore, make sure to remove Ymacco Trojan as soon as possible. For this purpose, take advantage of a powerful anti-virus program and run its scan after restarting Windows into Safe Mode with Networking.
As we’ve already pointed out, a scan with an AV engine will not repair damaged system files. Thus, tight after the Ymacco removal, download Reimage Reimage Cleaner Intego or similar repair tool and set it to fix all detected system issues.
Malicious code disguised under file attachments can deliver trojans
The source of trojans cannot be specified because there are many. Criminals are using various techniques to make people slip on downloading malicious entries to their machines, so the only precautionary measure is to be careful when browsing online and keeping the machine fully protected by AV programs.
Nevertheless, there are several methods that are known to be the primary trojan download sources. First of all, malicious codes are frequently hidden in spam email attachments. People may get fake email messages that supposedly contain financial information, receipts, invoices, order confirmations, and so on. Such emails may be professionally crafted, though usually, they contain grammar, typo, and logic mistakes.
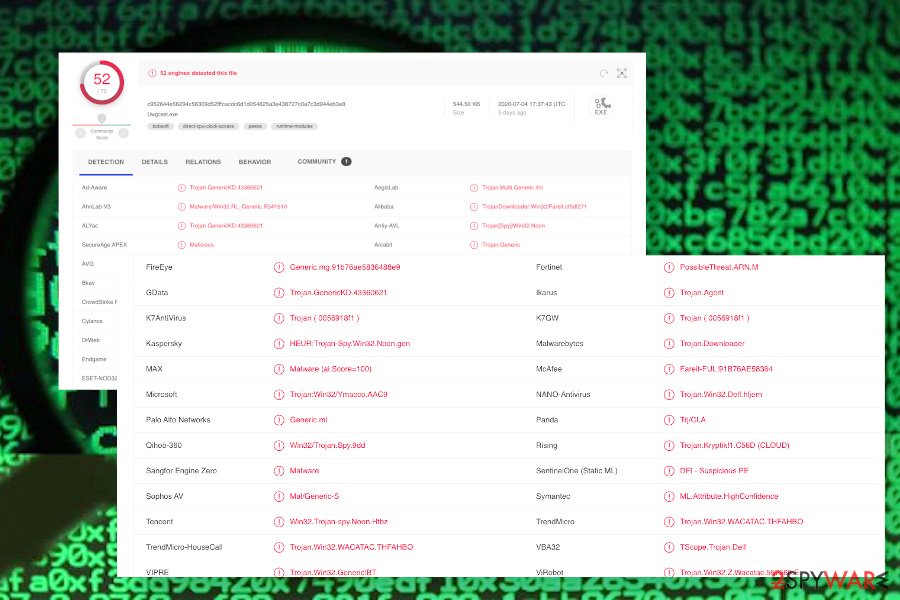
Ymacco trojan is recognized by most of the reputable AV engines, except different detection names are used
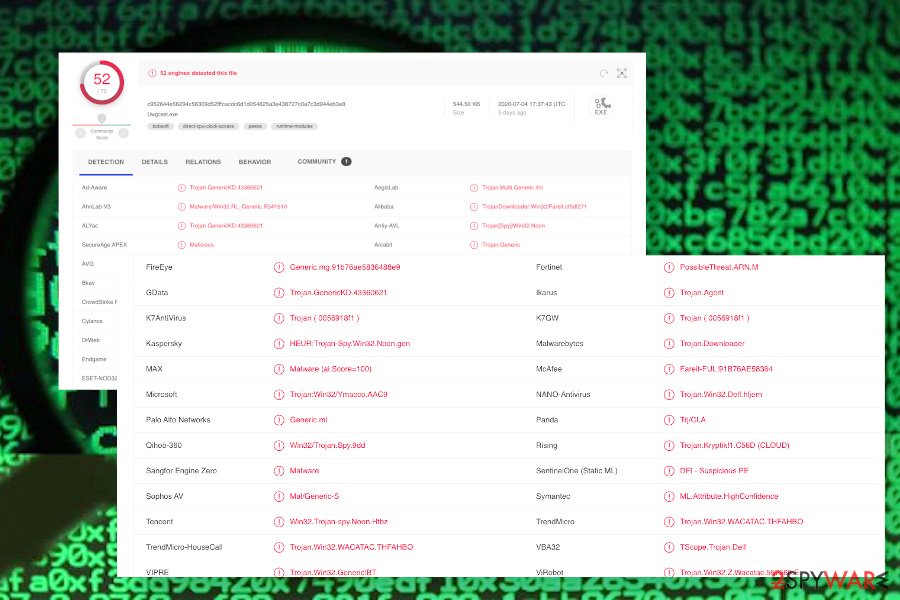
Ymacco trojan is recognized by most of the reputable AV engines, except different detection names are used
Apart from spam, people may be tricked into downloading trojans by downloading illegal content from P2P networks, torrenting sites, or other pirating sources. Hackers can easily inject malicious scripts into various cracks, keygens, third-party games, etc.
Trojans are also often distributed via infected links that people receive on social media. For instance, the well-known Facebook virus has been, and probably still is, the most successful malware distribution campaign. Therefore, do not trust suspicious content even if it comes from a trusted source.
Remove Trojan:Win32/Ymacco.AAC9 detection to protect the system from malware
There is a sole technique that is fully functional in dealing with viruses like Ymacco trojan. That’s a thorough system scan with a robust anti-malware tool. Since this virus is highly dangerous in its nature as it poses a risk to the user’s privacy and the system’s security, it has to be fully eliminated.
Employing a professional anti-malware for Ymacco trojan removal gives the advantage of cleaning other cyber infections at the same time. If you are not sure when the machine has been infected, there’s a risk that it has been running for a long time already and might have downloaded a bunch of malicious files.
Employ SpyHunter 5Combo Cleaner or Malwarebytes tools for checking the system and performing a full Ymacco removal. If you cannot launch the security tool, try to restart Windows into Safe Mode with Networking (a guide provided below). Finally, do not underestimate the need for the system’s optimization. Download Reimage Reimage Cleaner Intego and scan the machine to restore all files that the trojan might have damaged or removed.
The government has many issues in regards to tracking users’ data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Computer users can suffer various losses due to cyber infections or their own faulty doings. Software issues created by malware or direct data loss due to encryption can lead to problems with your device or permanent damage. When you have proper up-to-date backups, you can easily recover after such an incident and get back to work.
It is crucial to create updates to your backups after any changes on the device, so you can get back to the point you were working on when malware changes anything or issues with the device causes data or performance corruption. Rely on such behavior and make file backup your daily or weekly habit.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware occurs out of nowhere. Use Data Recovery Pro for the system restoring purpose.
This entry was posted on 2020-07-10 at 02:42 and is filed under Trojans, Viruses.

