Ursnif – dangerous Trojan used to steal sensitive data by recording users’ keystrokes
Ursnif virus is malware that specializes in banking credentials and other information-stealing by using a variety of methods. Released in 2006, malware has seen a fair share of updates and is constantly returning with new campaigns that typically utilize malvertising (fake Adobe Flash updates) and malspam (Word or Excel documents embedded in phishing emails) for the propagation of Ursnif Trojan.
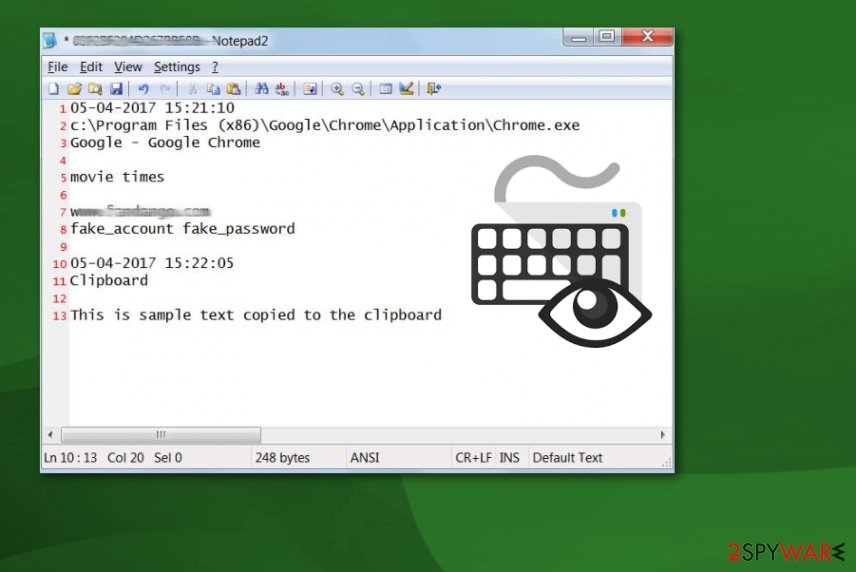
Once inside the system, the Ursnif virus[1] launches the malicious svchost.exe and explorer.exe processes, which are used to hide its presence on the host machine. Additionally, this modular malware starts numerous activities behind victims’ backs, including the distribution of other malware. However, the main virus activity is related to data tracking – it employs keylogging and other techniques in order to harvest information from browsers, email accounts, user configurations, as well as digital wallets. Ursnif later sends these details to the Command & Control that is accessible to the attackers only.
In 2015, the source-code of Ursnif was leaked online[2] and placed on the GitHub platform, which allowed several cybercriminal groups to modify malware in a way that would increase its capabilities. As a result, the Trojan is now widely used and is highly evasive, making it a prevalent choice within the illegal data-stealing business.
| Name | Ursnif |
|---|---|
| Type | Trojan, Data-stealer |
| Alternative names | Gozi ISFB, Dreambot |
| Associated process | Explorer.exe, iexplorer.exe, svhost.exe, click.exe |
| Symptoms | Information stealing malware rarely emits any symptoms, as it is designed to operate using stealth techniques. Nonetheless, some victims might notice suspicious computer behavior, such as inability to access particular sites via the web browser, system slowdowns, application/system crashes, errors, etc. |
| Danger level | High. Malware uses several evasion techniques, so it may remain on the system for months before it is detected, gathering sensitive information, such as financial details, account credentials, Social Security Numbers, and much more |
| Distribution | The main distribution method of Ursnif is spam emails boobytrapped with malicious attachments. In most cases, MS Office documents are used, although other file types were also spotted in the wild |
| Elimination | If your computer is connected to a network, disconnect it and then perform a full system scan with anti-malware software, such as SpyHunter 5Combo Cleaner or Malwarebytes |
| System fix | In some cases, malware can infect and damage Windows system files. As a result, users might experience stability issues, such as lag, crashes, BSODs, and errors. To fix these problems, you can use PC repair utility Reimage Reimage Cleaner Intego |
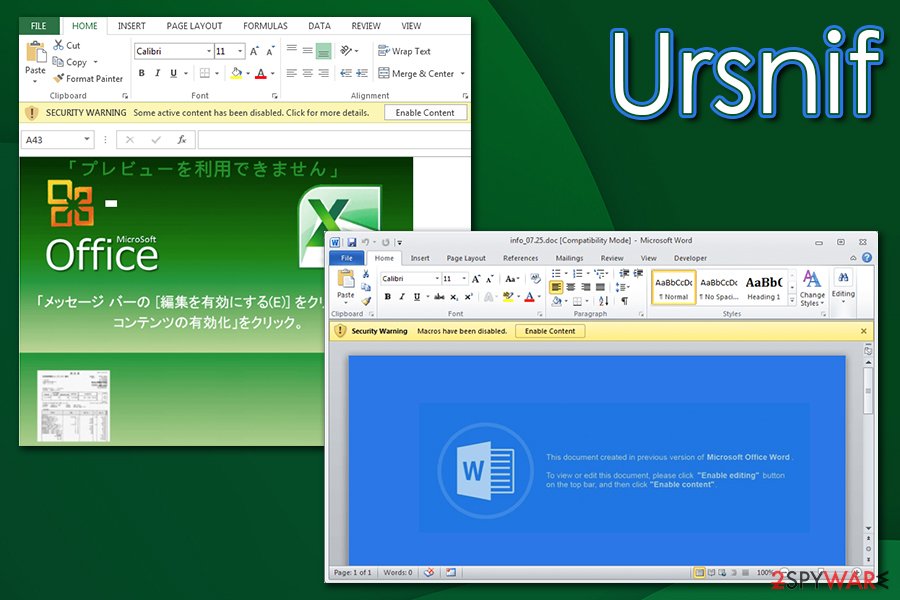
In one of the latest Ursnif campaigns, threat actors were spotted delivering the payload within MS Word documents, titled as “info_[date].doc,” that are embedded with malicious macros. As soon as users press “Enable Content,” a Visual Basic code is executed, beginning the infection routine. This variant of Ursnif was also using anti-detection techniques by injecting its Command & Control servers with a reference list of trusted companies, such as Microsoft:[3]
<…>you may notice the C&C host list includes “microsoft.com”, “update.microsoft.com”, “avast.com”, “cdevinoucathrine.info”, “zcei60houston.club” and “kenovella.club”. This seems odd. Why are the hosts of “microsoft” and “avast” listed here? In fact, this is a way to deceive researchers who capture and analyze the traffic.
In January 2020, security researchers from FireEye have discovered a new variant of Ursfnif, which was dubbed SaiGon.[4] While this version still focuses on data stealing, its capabilities include backdoor functionality (allows it to push other malware), process injection, and various evasion techniques.
Ursnif: functions and operation
This trojan is designed to record various sensitive information about the user, including banking data, logins or passwords, web browsing activity, information about the victim’s OS and device. All this recorded information is additionally shared with virus developers. Ursnif keylogger can also delete itself from the system once it receives such command.
Ursnif is constantly evolving, and several cybercriminal groups are working on its improvements. It started targeting various financial institutions from the beginning and recently expanded to more prominent organizations and changed distribution techniques and types of information to steal.

Ursnif virus is a keystroke-collecting malware that comes to your system via infected spam emails.

Ursnif virus is a keystroke-collecting malware that comes to your system via infected spam emails.
Ursnif virus is known to use different techniques as web injecting, man-in-the-browser, or keylogging functionality. The latest attacks were based on spear-phishing emails and the fact that malware deleted copies of itself after the initial process. These facts make this banking trojan more dangerous and difficult to detect or analyze.
This virus steals various data about the user personally, the device and other account information like:
- information from your email accounts;
- various information from your browsers;
- logins and passwords of your social media accounts;
- banking website logins and passwords.
Ursnif virus changes various registry keys to keep affecting the system. People behind this threat are focusing on getting revenue from various background activities on your system or even stealing your banking credentials so get your money directly out of your bank accounts.
While there is no way to spot the infiltration of this trojan, you should note that the main way used by this malware to get into the system is spam. Ursnif virushas been using intelligent tactics that rely on infected Word documents that are filled with malicious macros. If you have recently been asked to enable macros to check the content of email’s attachment, we highly recommend making sure that you are not infected. The easiest way to do that is to scan the system with updated anti-spyware.
If you have any doubts either you have this malware on the device or not, check your system with updated anti-spyware and perform Ursnif removal to save your personal information. To get rid of any viruses, use reputable anti-malware/anti-virus software. We do not recommend performing the removal manually as this is a dangerous cyber threat which can be related to numerous different components hidden on your computer. If you are blocked, reboot your PC to Safe Mode with networking first to disable the virus. Finally, we recommend a scan with Reimage Reimage Cleaner Intego to remediate Windows system and avoid stability issues post-infection.
In most of the cases, antivirus programs detect the Ursnif Trojan horse as:
- TR/Crypt.XPACK.Gen
- Virus/Win32.PolyRansom.c
- HEUR/Fakon.mwf
- Win32.Doboc.Gen.1
- Troj.Heur.LP.mE18
- etc.[5]
Virus activity may lead you to serious privacy issues or money loss, so you need to remove Ursnif virus as soon as possible. This type of cyber intruder can download and install other malware, including ransomware-type viruses, which could lead you to data loss. There is no need to keep yourself at such a risk. However, we should say one more time that you shouldn’t try to delete the trojan manually as you can lead your system to serious trouble by removing needed system components.
Spam email campaigns have been spreading this virus around as legitimate attachments asking to enable macros
Researchers[6] have always been warning people that they shouldn’t believe anything on the internet what looks too good to be true. That includes banner ads, in-text links, and spam emails as well.
Spam has also been a commonly used technique for trojan distribution. However, when discussing Ursnif trojan horse, note that it relies on a slightly different distribution method. The main way used by its developers to deliver this malicious threat relies on Word documents filled with malicious macros. Once downloaded, such attachment asks you to enable macros and launches the virus in this way.
Ursnif is typically delivered via malicious spam email attachments
Ursnif is typically delivered via malicious spam email attachments
Other unique features about the distribution technique used by this banking trojan:
- Compromised email accounts are used to reply to emails. The content of an email looks convincing;
- The malicious payload is released when the user downloads the macro-filled documents. However, the Trojan waits until the attachment is closed to launch the process;
- The safe-looking Word attachment also executes the PowerShell code. After this process, malware connects to URL and delivers the payload directly on the system;
- The whole campaign is based on the fact that emails are sent from familiar services what increases the chances of people opening the infected file;
- The most common pattern used to name these files is “the name of a local business or service_Statement”
You can avoid getting these intruders if you delete spam emails that are not from companies you know or services you do not use. Make sure to clean those suspicious emails from the email box more frequently and try to scan files before downloading them on the device. Pay more attention to these processes and do not open an email if you were not expecting that.
Best ways to remove Ursnif virus
When dealing with any silent intruder, anti-malware tools are the best option in virus elimination. However, trojans are one of the most dangerous cyber infections that can additionally install malware on the system. To remove Ursnif Trojan virus and all related programs from the system, run a full system scan with updated anti-spyware. If you are blocked, check two methods given below that are supposed to help you disable the virus before a scan.
We recommend SpyHunter 5Combo Cleaner or Malwarebytes for Ursnif virus removal, although you can also pick a security tool of your choice. Update these programs to their latest versions and run a full system scan to check your device thoroughly and get rid of any malware hiding on your system. You can also use the anti-virus software of your choice, just make sure that it is a reputable and well-known tool.
This entry was posted on 2020-05-05 at 07:47 and is filed under Trojans, Viruses.

