Rooe ransomware – file locking malware that deletes Shadow Volume Copies to prevent easy recovery
Rooe ransomware is a file locking virus that modifies Windows hosts file in order to prevent users from seeking help
Rooe ransomware is a file locking virus that modifies Windows hosts file in order to prevent users from seeking help
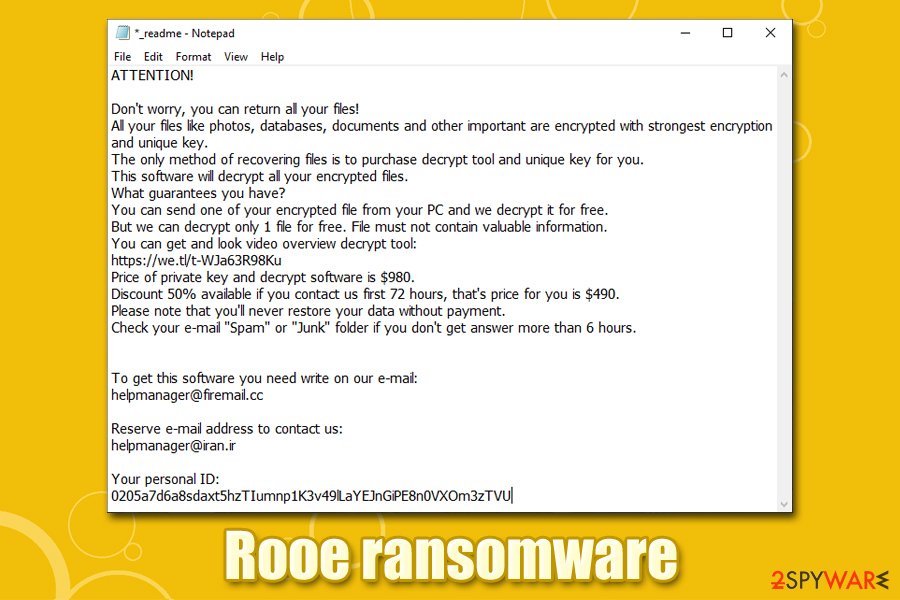
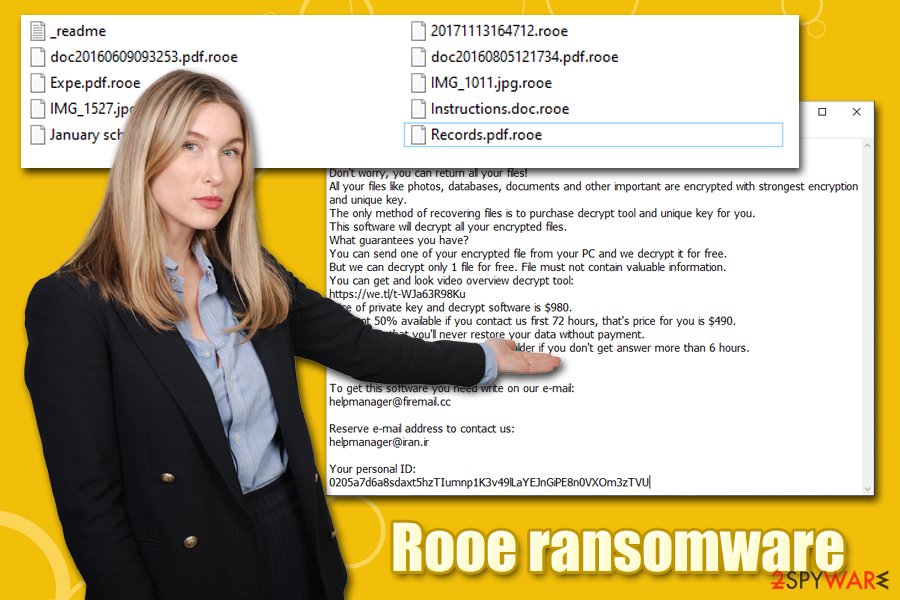
Rooe ransomware is a new Djvu/STOP virus variant that was first spotted in mid-February 2020. Just as its predecessors, the malware uses software cracks to penetrate the machines of random users and then encrypts all pictures, music, videos, documents, databases, PDF, and other files with the help of a secure RSA encryption algorithm.[1] As a result, users cannot access their files, each of which is a marker with .rooe extension; although hackers offer a deal – pay $490 within the first 72 hours of infection, and you will get the Rooe ransomware decryptor. After that, the requirement doubles, and victims are asked to pay $980 in Bitcoin.
Rooe virus also drops a ransom note _readme.txt, which also includes contact details of the attackers – [email protected] and [email protected]. However, if you fell a victim of ransomware, you should not hurry and pay the ransom – there are several other methods that might be able to save your data, e.g., Emsisoft’s decryptor for STOP Djvu. However, before performing Rooe ransomware removal, you should backup all the encrypted files
| Name | Rooe ransomware |
| Type | Cryptomalware, file locking virus |
| Family | The malware stems from the prominent Djvu/STOP virus family |
| Distribution | Most of the infections occur when users download and run pirated program or software crack installers |
| File extension | All personal files are appended with .rooe extension (malware skips most executable and all system files) |
| Ransom note | _readme.txt note is dropped into each of the folders that hold encrypted files |
| Contact | For communication purposes, malicious actors ask victims to write an email to [email protected] or [email protected] |
| Ransom size | Among all versions of the virus, hackers’ demands are consistent: they ask for $490 in BTC within first 72 hours of infection, which later increases to $980 |
| Data recovery | In case the Rooe virus used an offline ID to encrypt data, Emsisoft’s decryptor might be helpful. In other cases, third-party recovery software can be used, although chances of it being successful are low. Paying criminals, while not recommended, might be the only chance of regaining data |
| Malware removal | Download and install reputable security software, bring it up to date, and perform a full system scan (in Safe Mode if required) |
| System fix | Ransomware performs multiple system changes that can render Windows unstable after its termination; to fix virus damage, we recommend using Reimage Reimage Cleaner |
Rooe ransomware and its forerunners have deep roots within cybercrime scene: the initial release of malware was observed in December 2017; since then, it became one of the most prolific ransomware families that target regular users. Previous versions of the family include .bboo, .alka, .repp, .btos, and many others (the total number of variants, each using a different extension, exceeds 200).
To battle this extensive malware, security researchers developed tools like STOPDecrypter that has helped thousands of victims to recover files for free, although it only worked for users whose data was encrypted with an offline ID. Luckily, security experts at Emsisoft delivered a decryptor which works for all variants released prior to August 2019; another decryption tool works only with offline IDs as well. While not immediately, users can expect the decryptor to work in some cases, even with the Rooe ransomware encrypted files.
Rooe ransomware distribution is simple yet effective – illegal installers
One of the main reasons why this ransomware family is so successful is its simple yet efficient distribution tactics. Malicious actors operate on various shady software crack and pirated software websites, where they upload booby-trapped installers. Users who are willing to install software and bypass the licensing process, often resort to torrent and similar websites. Unfortunately, it is a hub for malware, and Rooe ransomware is just one of many infections that victims could catch there.
It is important to notice that crack tools will most certainly be marked as malicious by almost all security vendors – this happens because of the core principle of the operation, as cracks are designed to break a code within other applications. Therefore, there is no way to verify whether the installer actually holds the malware inside, or it would simply crack the software. Without a doubt, you should stay away from malicious installers that might result in permanent loss of personal data help on a computer.
Nevertheless, maliciosu actors always seek to expand their campaigns, and other distribution methods may be employed at any time. Therefore, stay safe by following these precautionary measures:
- Backup all your files regularly – this would potentially save you from all negative ransomware effects;
- Employ comprehensive anti-malware software with web protection enabled;
- Make sure you update Windows OS along with all the installed programs on the patch day;
- Use strong passwords for all your accounts (and never reuse them);
- Do not use the default Remote Desktop Protocol port and protect it with a password consisting of alphanumeric characters, i.e., not easily predictable one;
- When dealing with unsolicited emails, watch out for malicious attachments or hyperlinks (documents that ask you to run macro function are especially dangerous);
- Enable firewall, use VPN with RDP, and protect your browsers with ad-blockers.
Rooe ransomware might install data stealing modules and modify Windows hosts file
Rooe virus targets all the latest versions of Windows machines (Windows 7, Windows 8, and Windows 10) that use either 64 or 32-bit architecture. One the malicious executable, which is usually named randomly, is launched, the malware creates an entry inside %AppData% and %User% folder and then begins the infection routine. There are several changes that Rooe ransomware needs to perform within the system in order to run a successful encryption process.
Rooe ransomware is a Djvu virus variant that holds all personal files hostage until ransom of $490/980 in BTC is paid
Rooe ransomware is a Djvu virus variant that holds all personal files hostage until ransom of $490/980 in BTC is paid
For example, Rooe ransomware is programmed to disable Windows Startup function and delete Shadow Volume Copies to prevent quick recovery. For persistence, it also modifies the Windows registry[2] database, which allows it to run each time the computer is booted.
There are few distinctive characteristics that relate to Rooe ransomware, as well as other Djvu variants, which include:
- Ransomware may place a data-stealing module into web browsers, which would allow hackers to collect sensitive information that is entered by victims; this information can later be used for money theft or can be sold on the dark web’s underground forums;
- During the infection routine, the virus modifies Windows hosts file in the background by including all the security-focused website addresses. As a result, victims are unable to connect to these sites that would help them to remove Rooe ransomware from their systems and possibly recover files using alternative methods;
- Djvu ransomware was observed incorporating additional malware payloads during its infections process – one of such examples includes the notorious AZORult banking Trojan.[3]
Once the necessary preparations are done, Rooe will proceed with file encryption. At this time, users may see a Windows update window – this is done deliberately in order to prevent victims from interrupting the process. A ransom _readme.txt will be presented right after that, it reads:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https://we.tl/t-Oc0xgfzC7q
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]Your personal ID:
As previously mentioned, paying cybercriminals behind the Rooe ransomware virus is definitely not an optimal solution, as you may end up losing your money along with your already compromised files. Remember that you are dealing with criminals, and these people cannot be trusted. If you decide to pay the ransom, do it at your own risk.
As an alternative method, you can employ the decryption tool from Emsisoft, or use third-party solutions – we provide the detailed guide below. Important note: you should backup all the encrypted data before you perform any changes to it, as you may damage it permanently, and then even hackers won’t be able to decrypt it. Keep in mind that removing Rooe ransomware will not recover your files, as these two processes are not related.
Regardless if your files can be saved or not, you should also take care of the infected system. If, after Rooe virus removal, your system is unstable, use Reimage Reimage Cleaner to fix the broken registries and other system files.
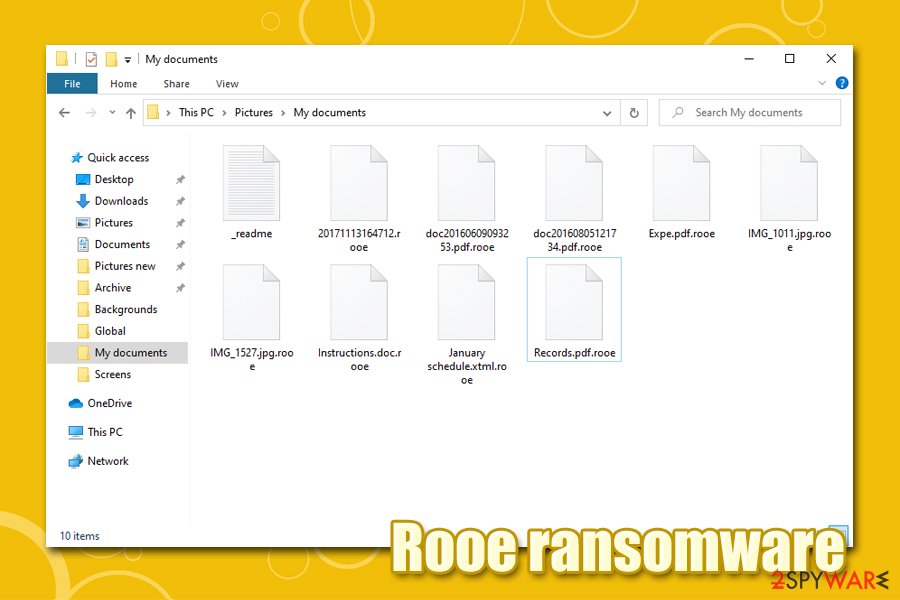
Rooe ransomware uses sophisticated RSA algorithm to lock data on targeted device
Rooe ransomware uses sophisticated RSA algorithm to lock data on targeted device
Rooe ransomware: a correct removal process
In many cases, Rooe virus infection comes as a surprise to users, as most never had to deal with ransomware before. While it is true that file locking malware can be exceptionally devastating not only for corporations but also for regular users, it is important not to panic and perform Rooe ransomware removal steps correctly.
In case you have backups available (which is usually not the case), you scan your computer with anti-malware software without having to worry about anything. Employ SpyHunter 5Combo Cleaner, Malwarebytes, or other reputable software for the purpose. However, if you do not possess backups, you need to make a copy of your locked files first and only then remove Rooe ransomware from the system. Depending on your personal situation, you may recover all, some, or none of your data using alternative methods listed below.
After you complete Rooe ransomware termination, you should go to the following location on your machine and delete the hosts file in order to be able to access security-related websites once again:
C:\Windows\System32\drivers\etc\
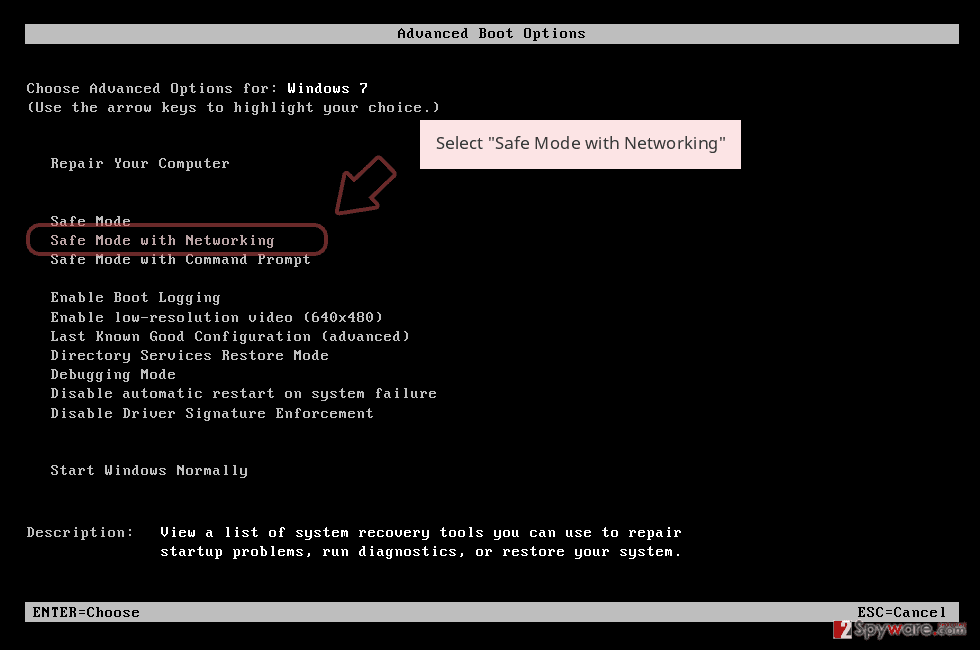
Remove Rooe using Safe Mode with Networking
In case Rooe ransomware is tampering with your security software, access Safe Mode with Networking:
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
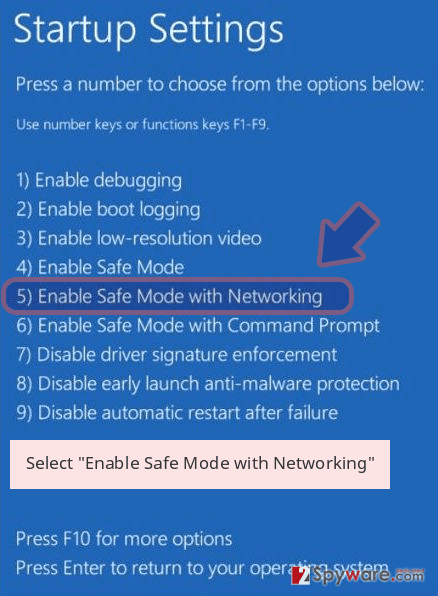
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Rooe removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Rooe using System Restore
You may also try to get rid of the malware by using System Restore:
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Rooe from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by Rooe, you can use several methods to restore them:
Data Recovery Pro solution
Data Recovery Pro is one of the best tools when it comes to recovery of accidentally deleted or otherwise lost files. While it is not designed to decipher ransomware-encrypted data, it may help you retrieve at least some of the copies from within your hard drive.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Rooe ransomware;
- Restore them.
Make use of Windows Previous Versions feature:
If you had System Restore function enabled before the malware attack, you could try this method.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer may be able to recover all files under some circumstances
Try ShadowExplorer – it may be capable of recovering all files in case certain bugs occurring during the encryption process by the Rooe virus.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Try Emsisoft’s decryptor
While there are few methods to check whether ransomware used an online or offline ID for your files, you should simply not bother and try the decryptor instead. You can download Emsisoft’s decryptor here. Additionally, you may also ask Dr.Web to assist you, although the help is not free.
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Rooe and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-02-14 at 08:08 and is filed under Ransomware, Viruses.

