Pywdu is a newly released member of the gradually expanding Snatch ransomware family
Pywdu ransomware is malware, which manifested at the end of June 2020. According to cybersecurity researchers, it belongs to the Snatch ransomware family, which has initially emerged back in 2018 and reproduced several deadly dangerous versions, including .FileSlack, .jupstb, .EGMWV, and others.
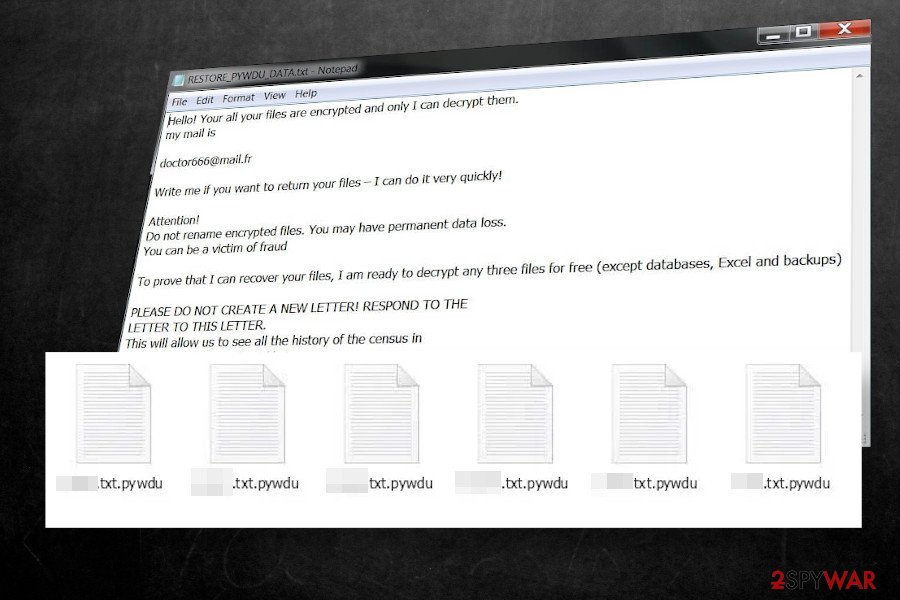
The Pywdu ransomware uses targeted spam email campaigns with an intention to attack corporations in particular, though it can end up on home users’ PCs as well. Upon infiltration, it uses the AES encryption[1] algorithm to lock data on the targeted PC, which subsequently gets the .pywdu file extension (e.g. mydocument.docs.pywdu).
The attackers drop a ransom note RESTORE_PYWDU_DATA.txt on the desktop and demand victims to contact them via [email protected] for further instructions. To prove gain victim’s trust, crooks claim to restore three files for free, while the rest of the data will be recovered after paying the ransom. Unfortunately, the size of the redemption is not specified, though experts presume that the Pywdu virus developers set up the price depending on how many files have been locked.
| Name | Pywdu |
| Class | Ransomware / file-locking virus |
| Family | Snatch ransomware |
| File extension | The virus locks files by appending the .pywdu extension |
| Ransom note | RESTORE_PYWDU_DATA.txt |
| Encryption model | Based on its ancestors, the ransomware is likely to render AES-256 encryption algorithm |
| Contacts | [email protected] |
| Distribution | The main dissemination technique – targeted spam email messages. However, it can also be distributed via software cracks, keygens, and unprotected RPDs |
| Decryption | Experts haven’t yet developed a functional Pywdu decryptor. Therefore, you should either pay the ransom (not recommended), use backups or try alternative data recovery methods, such as Volume Shadow Copies |
| Ransomware removal | The only way to eliminate the package of the malicious files that comprise the Pywdu file virus is to use a professional anti-virus |
| This ransomware is capable of stopping important Windows processes, altering boot sequence, and creating malicious Windows registries. These changes are not restored during the virus removal. Thus, try to repait system damage with Reimage Reimage Cleaner Intego tool | |
There’s no precise information on how Pywdu ransomware spreads. However, based on the previous variants of this ransomware and ransomware practice, in general, the following means are most likely to be used:
- Targeted spam emails (contain malicious attachment or hyperlink);
- Exploits;
- Pirated software, keygens, cracks;
- Fake software updates (mimicking Windows software updates, Flash Player updates, etc.);
- Backdoors (can be downloaded as a secondary payload via Trojans), etc.
Upon the installation, the Pywdu virus stops several Windows processes, injects malicious files in the list of startup programs, and starts running malicious entries, the most active of which is dttcodexgigas.029ff83e481b8c870b58b1e4d9c52cb8ba60954e[2]. This particular processes initiates the following commands via an elevated PowerShell:
- vssadmin delete shadows /all /quiet
- sc queryex type= service
It means that the .pywdu file virus disabled Volume Shadow Copies, thus preventing the user from retrieving the locked files without paying the ransom (unless the victim has backups). After all malicious commands are executed, the virus runs a cipher to locked all personal data obtained on the infected machine. According to experts, the ransomware can encrypt the following file types:
.7z, .rar, .m4a, .wma, .avi, .wmv, .csv, .d3dbsp, .sc2save, .sie, .sum, .ibank, .t13, .t12, .qdf, .gdb, .tax, .pkpass, .bc6, .bc7, .bkp, .qic, .bkf, .sidn, .sidd, .mddata, .itl, .itdb, .icxs, .hvpl, .hplg, .hkdb, .mdbackup, .syncdb, .gho, .cas, .svg, .map, .wmo, .itm, .sb, .fos, .mcgame, .vdf, .ztmp, .sis, .sid, .ncf, .menu, .layout, .dmp, .blob, .esm,. 001, .vtf, .dazip, .fpk, .mlx, .kf, .iwd, .vpk, .tor, .psk, .rim, .w3x, .fsh, .ntl, .arch00, .lvl, .snx, .cfr, .ff, .vpp_pc, .lrf, .m2, .mcmeta, .vfs0, .mpqge, .kdb, .db0, .DayZProfile, .rofl, .hkx, .bar, .upk, .das, .iwi, .litemod, .asset, .forge, .ltx, .bsa, .apk, .re4, .sav, .lbf, .slm, .bik, .epk, .rgss3a, .pak, .big, .unity3d, .wotreplay, .xxx, .desc, .py, .m3u, .flv, .js, .css, .rb, .png, .jpeg, .txt, .p7c;
.p7b, .p12, .pfx, .pem, .crt, .cer, .der, .x3f, .srw, .pef, .ptx, .r3d, .rw2, .rwl, .raw, .raf, .orf, .nrw, .mrwref, .mef, .erf, .kdc, .dcr, .cr2, .crw, .bay, .sr2, .srf, .arw, .3fr, .dng, .jpe, .jpg, .cdr, .indd, .ai, .eps, .pdf, .pdd;
.psd, .dbfv, .mdf, .wb2, .rtf, .wpd, .dxg, .xf, .dwg, .pst, .accdb, .mdb, .pptm, .pptx, .ppt, .xlk, .xlsb, .xlsm;
.xlsx, .xls, .wps, .docm, .docx, .doc, .odb, .odc, .odm, .odp, .ods, .odt; (the list is not finite)
Upon file encryption, the victim can no longer access personal files and is blackmailed to purchase a decryption key to unlock .pywdu files. To inform the victim about the attack and awaited response, criminals leave a ransom note RESTORE_PYWDU_DATA.txt on the desktop, which shortly explains what has happened and demands to email them via [email protected].
Hello! Your all your files are encrypted and only I can decrypt them.
my mail is
[email protected]
Write me if you want to return your files – I can do it very quickly!Attention!
Do not rename encrypted files. You may have permanent data loss.
You can be a victim of fraudTo prove that I can recover your files, I am ready to decrypt any three files for free (except databases, Excel and backups)
PLEASE DO NOT CREATE A NEW LETTER! RESPOND TO THE
LETTER TO THIS LETTER.
This will allow us to see all the history of the census in
one place and respond quickly to you.hurry up!
Those who have received the above-shown ransom note are strongly recommended not to lose once’s minds. The ransomware is dangerous and can cost permanent file loss. However, we strongly recommend weighing all pros and cons before paying. Think twice whether the data that has been locked is worth hundreds of dollars and an affair with cybercriminals.
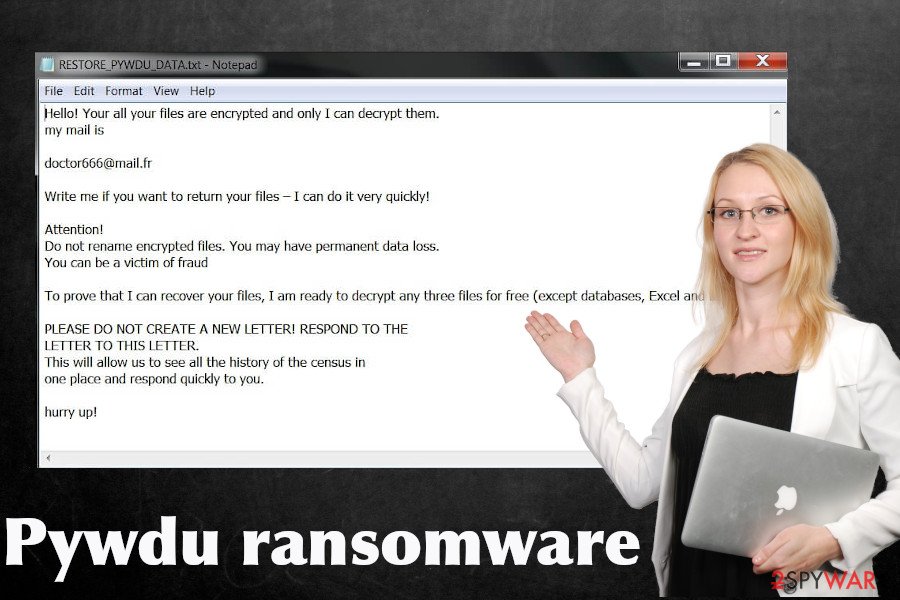
Pywdu ransomware is a dangerous cyber infection that encrypts files and demands its victims to make the payment for a decryption software
Pywdu ransomware is a dangerous cyber infection that encrypts files and demands its victims to make the payment for a decryption software
At best, you should immediately copy the encrypted files into an alternative data storage and remove Pywdu ransomware virus from the machine. For this purpose, you should restart the system into Safe Mode (the virus may block the processes of anti-virus programs) and run a robust anti-virus program.
Pywdu virus removal will not recover the encrypted data, as well as not recover the settings of the Windows OS. Therefore, you should try alternative data recovery methods (listed at the end of this article) and optimize the system with Reimage Reimage Cleaner Intego repair tool.
Ransomware is usually distributed via spam emails and pirated software
Ransomware is a type of virus that tops the charts of the most dangerous cyber infections. If it gets installed, the victim is endangered to lose personal files, money, or both. Therefore, experts keep warning Internet users about the most common ransomware distribution techniques to help people stay safe.
Unfortunately, criminals are too inventive and sophisticated to find out various means tricking people into accidentally running malicious files that carry ransomware. The prevailing technique, and still most successful, is malicious attachments appended to spam email messages.
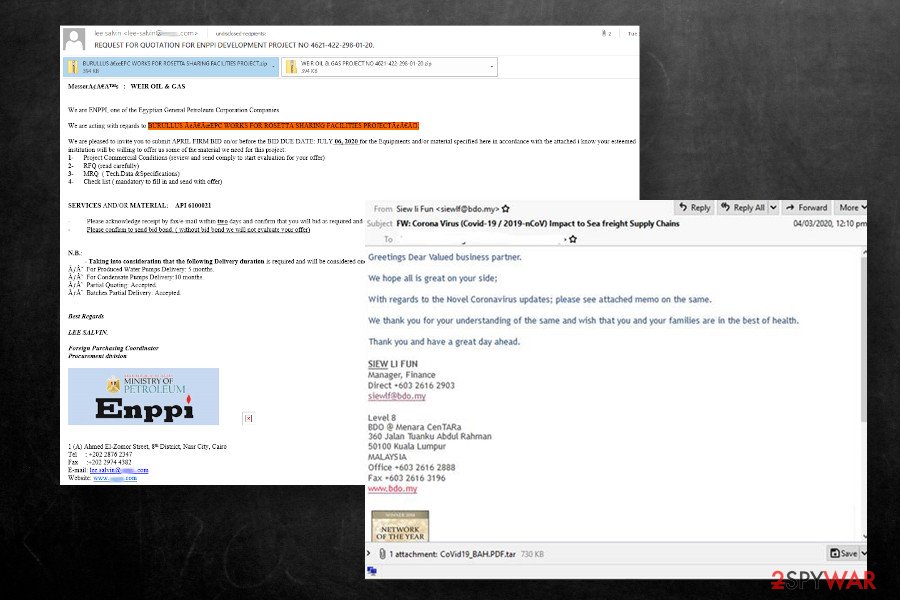
Pywdu virus is usually spread via malicious spam email attachments
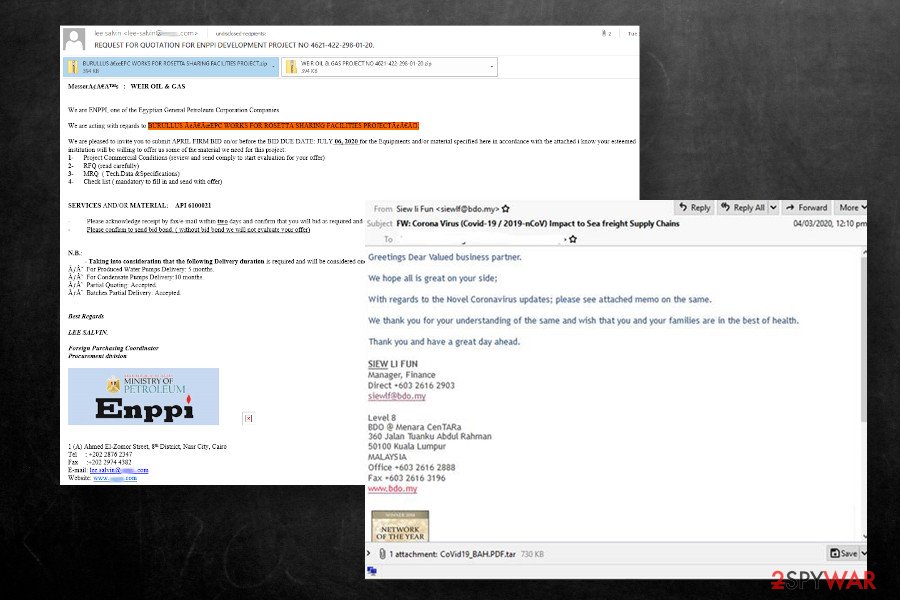
Pywdu virus is usually spread via malicious spam email attachments
Apart from malspam, ransomware can be activated via software cracks, keygens, and other pirated content. Therefore, it’s crucial to take precautionary measures to stay away from dangerous content. Dieviren.de[3] experts have excluded the basic precautionary measures that each user should mind:
- Download and use a robust anti-virus solution. At best, use the whole package of security software to ensure the highest protection level;
- Regularly install software updates, OS updates, and patch vulnerabilities
- Investigate every email before opening its attachments. Even if you received a message asking to confirm the order or check something, it doesn’t mean that you can open the .doc, .pdf, .htm, or another type of attachment. Double-check the sender, look for grammar/type mistakes, and other hooks showing the email to be spam. You can also scan the attachment with an anti-virus tool if it has scan to e-mail function
- Use a strong password and VPN when using Remote Desktop Protocol;
- Stay away from dangerous websites (porn, gambling, P2P, torrent, etc.)
Delete Pywdu ransomware before trying to recover locked data
Indeed, finding all files encrypted by the .pywdu file virus is shocking and most of the users consider paying the ransom. Probably, paying the ransom seems to be the sole solution for those who keep important work files and archives on the system, family photos, and other documents and do not regularly make backups.
If you have backups on external hard drive or cloud, you have nothing to worry about. Remove Pywdu virus immediately using SpyHunter 5Combo Cleaner, Malwarebytes or alternative security tool, recovery the system with Reimage Reimage Cleaner Intego, and then recover .pywdu files from backups. If, however, you have no backups, we do not recommend paying criminals for their delinquent activities. Instead, eliminate the ransomware and try to recover data using alternative methods.
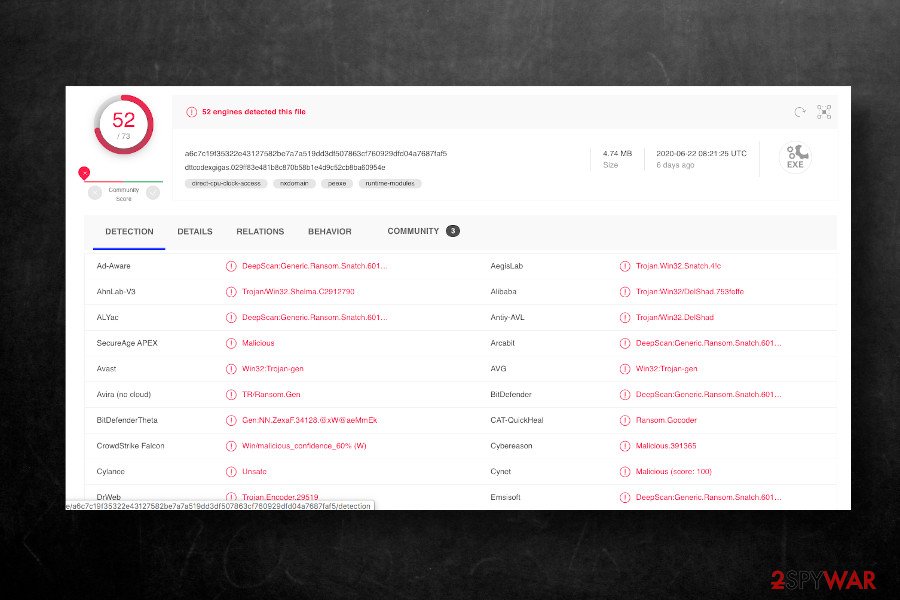
Pywdu ransomware can be quarantined and removed by most of the professional AV programs
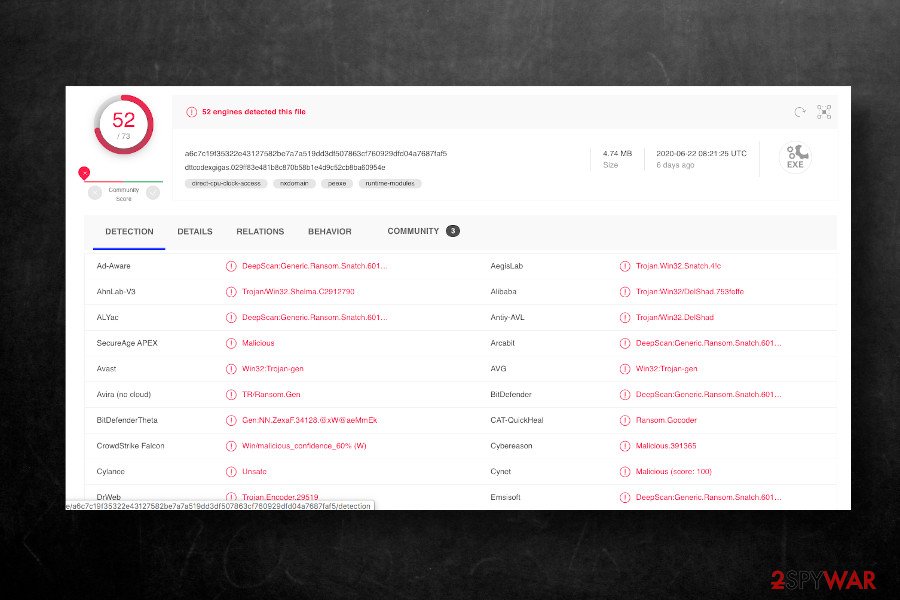
Pywdu ransomware can be quarantined and removed by most of the professional AV programs
Unfortunately, Pywdu removal won’t recover encrypted files. However, it is expected that experts will soon find a flaw in the ransomware file encryption model and generate a fully functional decryption tool. Therefore, we recommend copying locked files into the external storage, giving a try for third-party data recovery tools, and, in case of no luck, wait for a decryptor to be launched.
Online spying has got momentum in recent years and people are getting more and more interested in how to protect their privacy online. One of the basic means to add a layer of security – choose the most private and secure web browser. Although web browsers can’t grant a full privacy protection and security, some of them are much better at sandboxing, HTTPS upgrading, active content blocking, tracking blocking, phishing protection, and similar privacy-oriented features.
Nevertheless, there’s a way to add an extra layer of protection and create a completely anonymous web browsing practice with the help of Private Internet Access VPN. This software reroutes traffic through different servers, thus leaving your IP address and geolocation in disguise. Besides, it is based on a strict no-log policy, meaning that no data will be recorded, leaked, and available for both first and third parties. The combination of a secure web browser and Private Internet Access VPN will let you browse the Internet without a feeling of being spied or targeted by criminals.
While much of the data can be accidentally deleted due to various circumstances, malware is also one of the main culprits that can cause loss of pictures, documents, videos, and other important files. Potentially unwanted programs may clear files that keep the application from running smoothly.
More serious malware infections lead to significant data loss when your documents, system files, or images get locked. Ransomware is the one that is focused on such functions, so your device gets useless without access to needed data. Even though there is little to no possibility to recover after file-locking threats, some applications have features for such recovery in the system.
In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.
This entry was posted on 2020-06-29 at 03:46 and is filed under Ransomware, Viruses.

