Phobos ransomware is the dangerous cryptovirus that spreads around and regular users as often as bigger companies
Phobos ransomware is a file locker that first emerged in 2017. Nevertheless, malware came back a year later with two new variants.
Phobos ransomware is a file locker that first emerged in 2017. Nevertheless, malware came back a year later with two new variants.
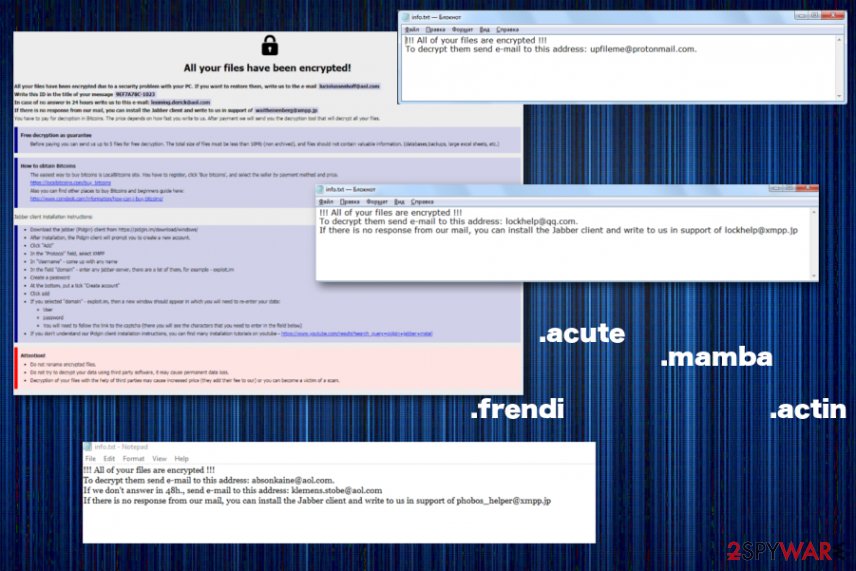
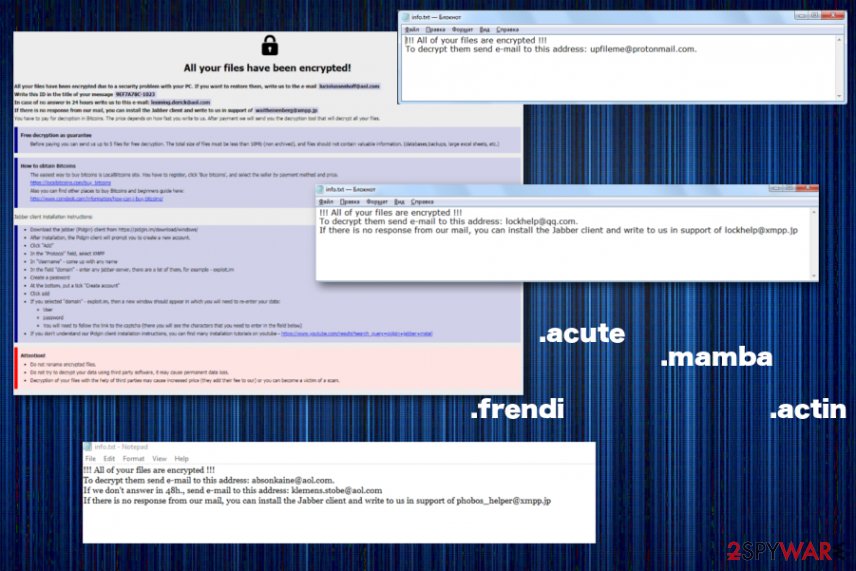
Phobos ransomware – malware that focuses on making money so virus encrypts files and asks for the payment transfer as soon as possible via text or hta files that get placed on the desktop or in some of the folders. This ransomware family has many versions, but there are not many different file extensions that get placed on encoded data. This is because creators tend to reuse the same extension, but change the email on the pattern or the contact information and spread a new wave of the threat. This is how cryptovirus manages to spread around widely and quickly. It can release a new variant each week. The year 2020 shows that the threat does exactly that.
Phobos is a cryptovirus that resembles a large Dharma family and was discovered by security researchers back in October 2017. Since its initial release, malware went under the radar for more than a year, until new variants started emerging at the end of 2018 and 2019. Initial infection used .[ID].[email].PHOBOS file extension and a Phobos.hta note asking victims to email virus developers via [email protected] to find out the amount of ransom that needs to be paid in order to retrieve access to locked data.
Later versions kept the extension .phobos, but used different contact addresses, along with the composite extension. The most recent contact emails changed to [email protected] and [email protected]. Currently, Phobos is actively attacking users all around the world, asking for as much as $5,000 ransom in return for the decryptor. It still remains active – the more recent and prominent versions throughout the last year are Actin ransomware and Mamba ransomware.
| Name | Phobos |
| Type | Ransomware |
| Known since | 2017 |
| Versions of extensions in the same family | .actin, .actor, .mamba, .phoenix, .acton, .frendi, .adage, .acute, .help, .com, .blend, .WALLET, .1500dollars, .adame, .banjo, .BORISHORSE, .Banta, .BANKS, .Adair, .zax, .HORSELIKER, .BANKS, .Barak, .Caley, .deal, .Cales, .calix, .Caleb, .elder, .octopus, .age, .deuce, .Angus, .Calum, .Dever, .Devon, .devil, .devos, .bablo, .dever, .dewar, .eight, .revon, .eject, .iso, etc. Most of them are repeated many times throughout the years of the virus activity |
| File extensions | [ID].[[email protected]].PHOBOS, [ID].[[email protected]].phobos, [ID].[[email protected]].phobos, [ID][[email protected]].phobos, [ID].[[email protected]].phobos, [ID].[[email protected]].phobos, .[ID].[[email protected]].phoenix, .[ID].[[email protected]].actor, .[ID].[[email protected]].mamba, .[ID].[[email protected]].actin, .[ID].[[email protected]].help, .[ID].[[email protected]].actin, .[ID].[[email protected]].actor, .[ID].[[email protected]].com, .[ID][email protected]].adage, .[ID].[[email protected]].blend, .[ID].[[email protected]].WALLET, .[ID].[[email protected]].acute, .[ID].[[email protected]].1500dollars, .[ID].[[email protected]].Acton, .[ID].[[email protected]].Acuna, .[ID].[[email protected]].banjo, .[ID].[[email protected]].BORISHORSE, .[ID].[[email protected]].Banta, .[ID].[[email protected]].Adair, .[ID].[[email protected]].zax, .[ID][email protected]].BANKS, .[ID].[[email protected]].barak, .[ID].[[email protected]].Caley, .[ID].[[email protected]].deal, .[ID][email protected]].Cales, .[ID].[[email protected]].calix, .[ID].[[email protected]].banjo, .[ID].[[email protected]].Devon, .[ID].[[email protected]].bablo, .[ID].[[email protected]].dewar, .[ID].[[email protected]].iso, etc. |
| Encryption algorithm | AES |
| Executable | processhacker-2.39-setup.exe |
| Ransom demand | Varies, can reach up to $5,000 or even $70 000 when the target is large business or company. The amount increases after 6 hours |
| Main dangers | Data loss, money loss, system compromise, malware infiltration |
| Distribution | Infected files as attachments on legitimate-looking emails, malicious files from hacked or malware-related websites |
| Elimination | Perform a scan with an anti-malware tool to remove Phobos ransomware |
| Repair | You need to double-check and scan the machine using something like Reimage Reimage Cleaner Intego or a system optimizer, so virus damage is deleted and alterations fixed or repaired automatically |
Phobos ransomware virus mostly spreads via malicious spam emails[1] or fake installers[2] (processhacker-2.39-setup.exe) for applications like Process Hacker 2. Once inside the computer, it starts scanning the system, targeting the predetermined file extensions.
The malware encrypts various pictures, multimedia, images, documents, and even databases or other data using AES cryptography.[3] Thus, files locked by Phobos ransomware cannot be opened without a specific decryption tool.
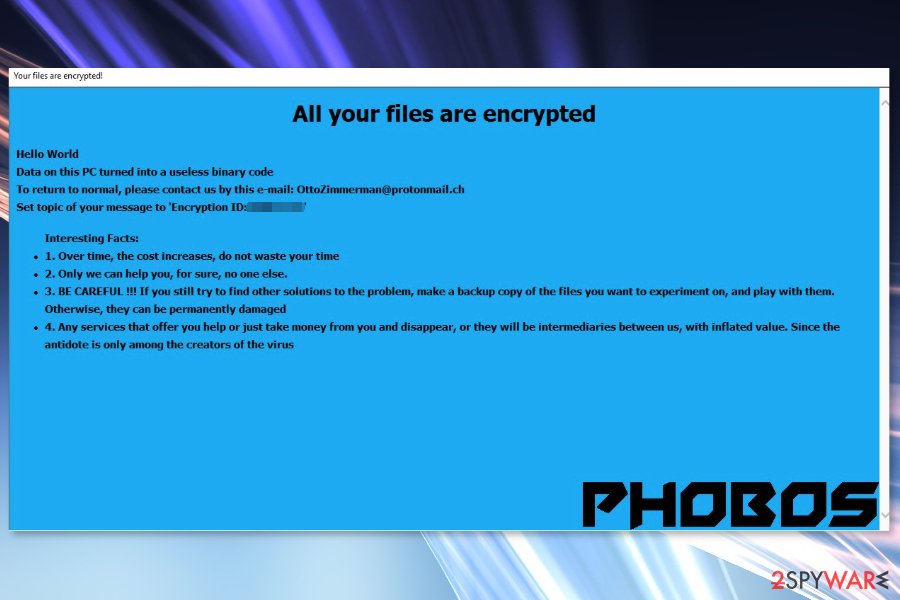
In the Phobos virus ransom note, criminals explain that the information stored on the affected computer was “turned into a useless binary code.” In order to make victims to follow the ransom payment instructions, crooks tell that other third-party data recovery services will not help them.
However, they might take the money and disappear. Though, this situation is most likely to happen if you contact and transfer the money to authors of the Phobos ransomware virus. Cybercriminals are not eager to help you because the only focus is getting money from the victims.
Over the course of December 2018 and February 2019, hackers released numerous new variants, which use different emails, including:
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
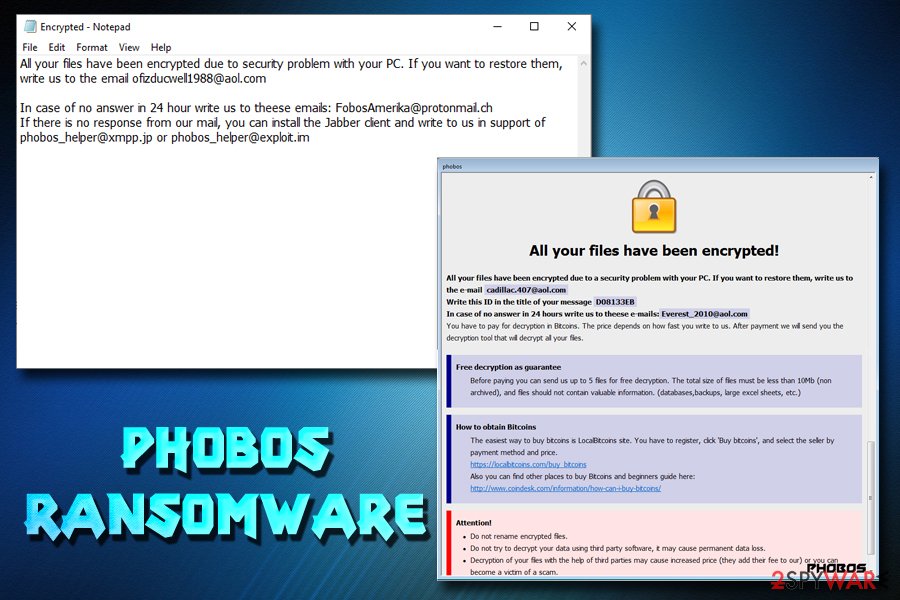
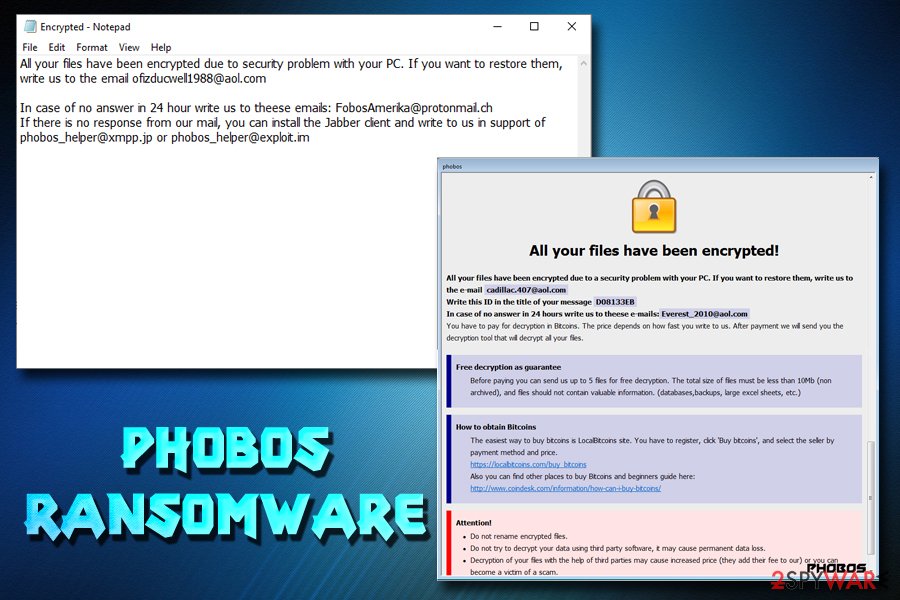
Once all files are encrypted, Phobos ransomware virus delivers a ransom-demanding message.
Once all files are encrypted, Phobos ransomware virus delivers a ransom-demanding message.
2019 came with even more news about Phobos virus because the ransomware started exploiting weak security to attack users all over the world.[4] It also targets businesses and large companies since these attacks ensure bigger profit from a single victim.[5] Badly secured RDP and other flaws used to enter the network and execute the malicious processes like file-locking and system changes.
Phobos ransomware developers varied their ransom notes, naming them Encrypted.txt and Data.hta. One of the latest messages states the following:
All your files have been encrypted due to security problem with your PC. If you want to restore them, write us to the email [email protected]
In case of no answer in 24 hour write us to theese emails: [email protected]
If there is no response from our mail, you can install the Jabber client and write to us in support of [email protected] or [email protected]
It seems like the virus is gaining success of receiving payments, as Phobos ransomware developers already received 3.5 BTC ($13,257 at the time of the writing) into their Bitcoin wallet.[6] It once again proves that the ransomware business model is extremely successful, and these type of infections will not go away anywhere. For that reason, using comprehensive security measures is a necessity.
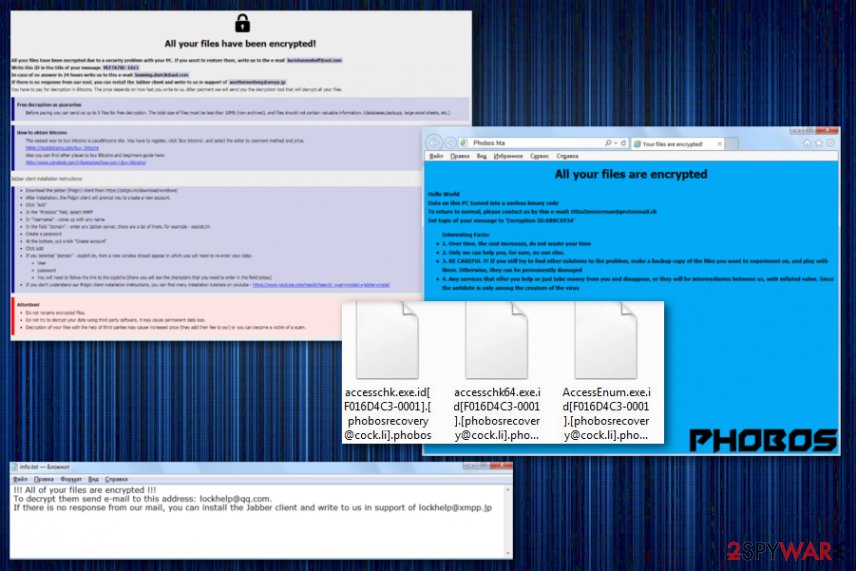
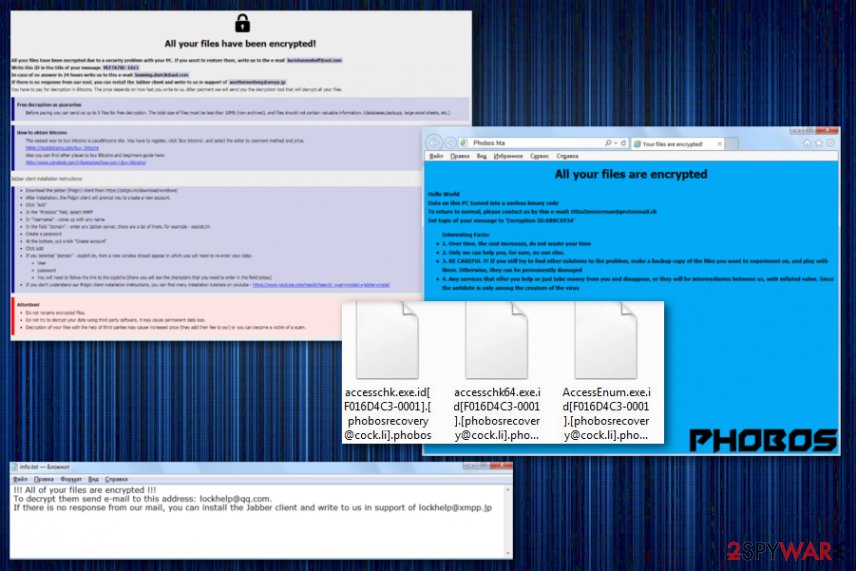
Phobos developers started actively releasing new variants in December 2018.
Phobos developers started actively releasing new variants in December 2018.
Hackers behind Phobos ransomware warn victims that, in case the ransom is not paid within a specific period, the size will increase significantly. However, cybersecurity specialists do not recommend contacting criminals and following their instructions because it might result in money loss.
If you got infected with the virus, do not panic, stay calm, and focus on Phobos ransomware removal. Trojans and ransomware often operate together to proliferate even more malware on the machine. Thus, ransomware infection might not only damage your files but corrupt the system as well. These threats often install programs, files or other malware to ensure the persistence.
However, you should not try to eliminate malware-related files manually. To remove Phobos ransomware safely and successfully, you have to obtain a reputable software and terminate the virus within several minutes. As soon as malware is eliminated, we suggest you scan the machine with Reimage Reimage Cleaner Intego as it can fix all the damage done by Phobos virus.
Phobos ransomware comes out with versions more dangerous than previous ones.
Phobos ransomware comes out with versions more dangerous than previous ones.
Phobos ransomware versions
The virus that came out first in 2017 is known for cybersecurity researchers for a while now, so data encryption and other extortion- based functionalities are analyzed. It is believed that the malware mainly is distributed from Ukraine and that the developers mimic dome features from other crypto-malware. Since October 2017, this family expanded, and even though the virus mainly uses .phobos extension to mark the files there are more versions that users tend to think.
Phobos ransomware
The first Phobos virus distribution month up until February 2019, delivered versions with the same .phobos file marker and only changed the contact information or names of the ransom notes. All the first variants looked similar to the Dharma ransomware because of the ransom message delivered as a hta program window and containing the thorough instructions about the payment. The full file marker added to encrypted files includes victims’ ID and a full email address besides the .phobos at the end.
These first versions had extensions with contact emails:
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
- [email protected]
The ransom note for these particular versions differs from Encrypted.tx, Data.hta and contained pretty much the same message. The only few differences were particular countries where the versions got released. January 2019 found versions were more spread in Brazil than other countries.
The later ransomware variants throughout these activity years, including this .phobos marker, also mixed up the ransom note file names between Info.txt, info.hta, and encrypted.txt.
Frendi ransomware
Frendi ransomware was the version that came out at the end of February 2019. This is the first version known to researchers that haven’t marked files with the initial .phobos appendix. The particular file extension that lands on encoded files include the .frendi appendix and [email protected] contact email. The same email address also included as the name of the main executable with ransomware payload.
Later on, a few more .phobos versions got delivered and after that at the start of April additional Frendi virus variants with [email protected] contact email emerged.
Phoenix ransomware
.phoenix is a file extension that also appeared in multiple versions of the virus throughout the years. Like other versions, not much changed from the initial cryptovirus, this threat included a few different contact emails in the ransom notes and file markers. [email protected] and [email protected], [email protected] are one of those. Ransom notes resembling Dharma family and marked with PHOBOS at the corner remained the same for years, while developers only changed the contact information and IDs per victim.
Actor ransomware
This .actor file appendix appeared once or twice in these Phobos virus campaigns, which is not common for the developers. One of these variants found in 2019, at the start of May, contained [email protected] on the file extension and delivered a text file name Encrypted.txt with a few sentences, as per usual. Although, the common HTA window was not delivered, according to some victims, this version was spotted at different times the same year with the same contact information.
Mamba ransomware
Mamba ransomware came out with a few distinct features and an alternate name of HDD Cryptor. This virus was more dangerous because at first, it started targeting large businesses and attacking victims to gain large amounts via ransoms up to 70 000$. This was one of the versions that exploit unprotected RDP to infect the machines. Contact emails for this particular version are known to be [email protected], [email protected].
Actin ransomware
The version that again targets more PC users and individual victims – Actin ransomware. This is one of many versions in this family, but the only one with the particular .actin file appendix. This threat also uses AES algorithm for the encryption process and demands victims to contact developers via [email protected] to get their files back allegedly. All those claims shouldn’t be trusted because these cybercriminals know what they are doing and they have no goal to help people. Actin virus also came out more than a few times and had different emails for each campaign, including [email protected], [email protected].
Acton ransomware
The slightly changed version from the previously described one, Acton ransomware was one of the less repeated variants int his Phobos ransomware family. Delivering the same info.hta program window with the payment instructions and contact information this time threat leaves out a ransom text file. Data encrypted by the virus get extensions including [email protected].
Adage ransomware
The more recent versions in Phobos ransomware started to get more unique names and file extensions. Virus developers occasionally release variants with the original .phobos, but June 2019, in particular, was the month of new ransomware releases. .adage virus file marker comes in the traditional pattern .id[XXXXXXXX -1096].[[email protected]].acute common for all the versions in Phobos family since 2017.
ISO ransomware
In the year 2020 Phobos creators delivered many versions reusing extensions like .jelp, .devos, and .dewarmany times. One of the more prominent and much more spreads around becomes this ISO ransomware version that carries a full pattern on extension .id[XXXXXXX-2589].[[email protected]].iso. It remains to place the hat window and text file on the system with random demands and instructions. Ransom note file info.txt and info.hta get placed on the desktop and in other folders. In those messages email and Telegram messaging app contact information get listed: [email protected], @iso_recovery.
Distribution methods of the file-encrypting virus
The crypto-malware can get inside the device when a user clicks on a malicious link, opens or downloads an infected file. The malware executable can be included in the email or presented as a useful program in various torrents or download sites. Thus, users have to be careful and avoid questionable content online.
- Never open spam emails and stay away from the attachments included into an email that is sent from unknown senders.
- Do not download illegal content.
- Stay away from pop-ups informing about available updates.
- Do not download software from untrusted or unauthorized sources.
- Install a reputable antivirus program.
- Keep all your programs updated.
Security experts from Norway[7] suggest creating backups and updating them regularly. Unfortunately, sometimes it’s impossible to decrypt files with third-party software. Therefore, having backups prevents data loss.
Phobos virus elimination guide
Trying to locate and wipe out malware-related files manually might end up with serious damage to the system. Therefore, we do not recommend risking to delete the wrong files. It’s better to dedicate Phobos ransomware removal for the professionals. We mean, you should obtain a reputable malware removal software, such as SpyHunter 5Combo Cleaner, or Malwarebytes, and get rid of the cyber infection automatically.
However, ransomware might be resistant and block security programs. For this reason, you should reboot the computer to the Safe Mode with Networking first in order to remove Phobos ransomware virus entirely. You can find the instructions below for this method and other tips that may help termination malware fully.
Also, for files that Phobos ransomware virus may damage and corrupt, try Reimage Reimage Cleaner Intego or a PC repair tool, system optimization application. Such software can easily indicate affected or damaged files, programs, system functions, and even fox such damage automatically without triggering additional changes or alterations.
This entry was posted on 2020-04-28 at 01:19 and is filed under Ransomware, Viruses.

