MarraCrypt ransomware is a file locking malware that spreads like a worm
MarraCrypt ransomware is a type of malware that locks all personal data on the infected computer and then asks for a ransom for its redemption
MarraCrypt ransomware is a type of malware that locks all personal data on the infected computer and then asks for a ransom for its redemption
MarraCrypt ransomware is crypto-malware that was developed in order to make users pay ransom after locking personal files on the host computer. First spotted by dnwls0719 cybersecurity researcher in late February 2020,[1] this virus seems to be a variant of Hermes and HildaCrypt families. Unlike many other crypto-lockers, however, MarraCrypt virus spreads like a worm[2] via flash drives, logical drives, and other external devices.
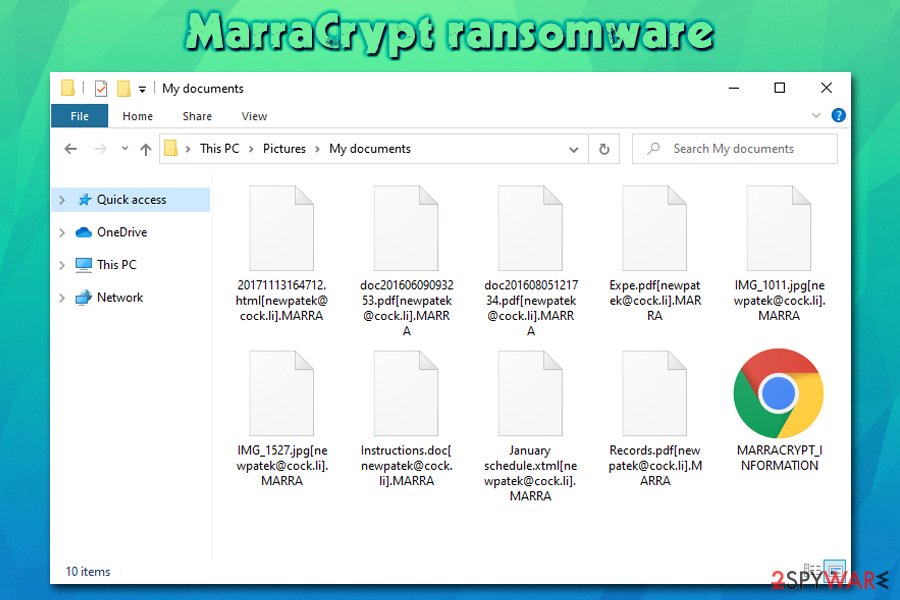
Once inside the system, the MarraCrypt virus uses AES + RSA cipher to encrypt personal files and appends .MARRA extension to each. The malware also drops a ransom note MARRACRYPT_INFORMATION.HTML in which victims are prompted to contact the attackers via [email protected] or [email protected] emails and pay the ransom for MarraCrypt ransomware decryptor using Bitcoin or another cryptocurrency.
| Name | MarraCrypt ransomware |
| Type | File locking virus, crypto-malware |
| Related files | svchosta.exe (not signed), sys.bat |
| Distribution | While this ransomware was spotted being distributed via contaminated external drives or malware droppers, malicious actors may also employ spam emails, drive-by downloads, software cracks, and other methods to deliver malware to victims |
| Malware family | Hermes and HildaCrypt ransomware |
| File extension | Most of the files on the host systems are appended with .MARRA file extension, although an email is also added before the file marker. For example, a “picture.jpg” is transformed into “picture.jpg[[email protected]].MARRA |
| Ransom note | MARRACRYPT_INFORMATION.HTML ransom note is placed on the desktop and all folders where encrypted files are located |
| Contact information | Cybercriminals provide two contact emails ([email protected] or [email protected]) for the negotiation purposes |
| Damage |
|
| File recovery | Without paying the ransom or backups, recovering the encrypted files is difficult, although you could try alternative methods listen in the recovery section below |
| Malware removal | Download and install reputable security software (such as SpyHunter 5Combo Cleaner or Malwarebytes) and perform a full system scan |
| System fix | In case your operating system starts malfunctioning after you get rid of the infection, repair the damage done to it with Reimage Reimage Cleaner to regain normal Windows functions |
While MarraCrypt ransomware authors propagate malware as a worm via infected external drives or malware that is already present on the system, that does not mean that you can not get infected with it in other ways. Hackers often change their distribution tactics in order to infect as many victims around the world as possible. Some of the most popular distribution methods include:
- Spam email attachments and embedded hyperlinks
- Exploit kits in conjunction with software vulnerabilities[3]
- Software cracks/keygens/loaders and repacked or pirated application installers
- Poorly protected Remote Desktop (RDP) connections
- Fake updates or other scams found on malicious sites, etc.
Regardless of how MarraCrypt virus gains access, however, the result is always the same – all the pictures, videos, music, databases, MS Office documents, and other files get encrypted so that the attackers would have the reason to ask for money. This illegal business has become extremely lucrative, and security researchers are observing more new ransomware variants (Rezm, Tsar), as well as new families (PwndLocker, SepSys) – just like MarraCrypt ransomware is.
However, before scanning the machine for files to encrypt, MarraCrypt ransomware first performs multiple preparations within Windows system. For example, it deletes Shadow Volume Copies to prevent an easy recovery, modifies Windows registry key HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\ Windows\ CurrentVersion\Run\ to retain persistence, etc.
In some cases, these changes can hinder MarraCrypt ransomware removal or even corrupt vital Windows system files. To bypass this, you can access Safe Mode with Networking and fix virus damage with tools like Reimage Reimage Cleaner .

MarraCrypt ransomware is a file locking virus that mainly spreads as a worm via external drives

MarraCrypt ransomware is a file locking virus that mainly spreads as a worm via external drives
Once the computer is modified and vital recovery systems disabled – this is typical ransomware behavior – MarraCrypt ransomware begins to look for data to encrypt. Typically, the most commonly-used file types are targeted, such as .doc, .zip, .mp4, .jpg, .pdf, and others. After this process, users can see each of the files marked with [[email protected]].MARRA appendix.
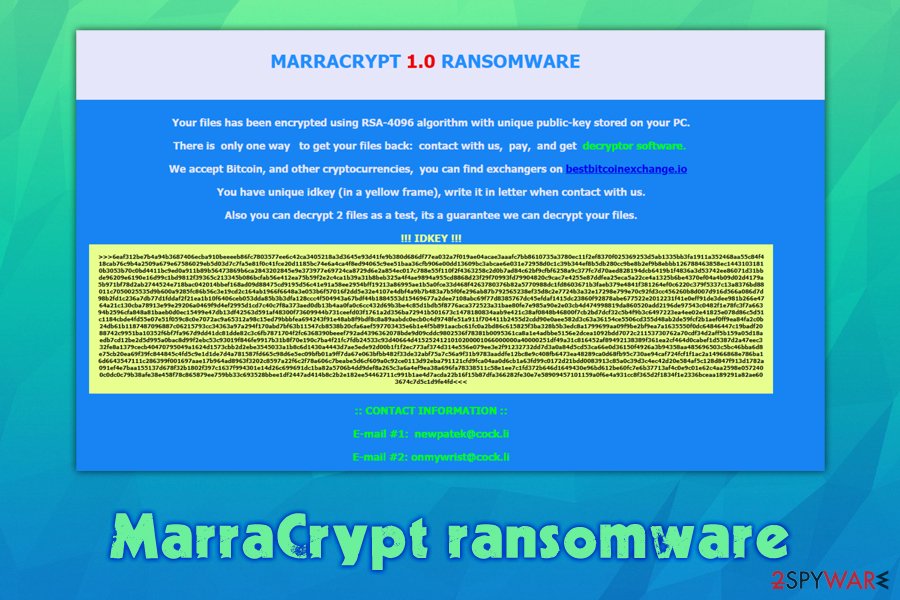
MarraCrypt ransomware then presents a message from the attackers in the HTML format – it can be opened via any browser. It reads:
MARRACRYPT 1.0 RANSOMWARE
Your files has been encrypted using RSA-4096 algorithm with unique public-key stored on your PC.
There is only one way to get your files back: contact with us, pay, and get decryptor software.
We accept Bitcoin, and other cryptocurrencies, you can find exchangers on bestbitcoinexchange.io
You have unique idkey (in a yellow frame), write it in letter when contact with us.
Also you can decrypt 2 files as a test, its a guarantee we can decrypt your files.!!! IDKEY !!!
:: CONTACT INFORMATION ::E-mail #1: [email protected]
E-mail #2: [email protected]
While the attackers do not mention what the size of the ransom is, paying them is highly discouraged by security researchers, as MarraCrypt virus authors can simply ignore you after. Besides, this action will only fuel criminals to infect more victims and develop new versions of malware. Despite this, it is understandable that some users might not have another choice and risk their money to retrieve the MarraCrypt ransomware decryption tool.
However, before you take on such dangerous tasks, we suggest you try alternative methods first. Before that, you have to remove MarraCrypt ransomware infection from your system, as, if you succeed in file recovery, all of the data will be encrypted once again. It is also important to note that you should make a copy of the encrypted data before you try recovery software listed below, as such tries might permanently corrupt your files otherwise.
Best ransomware recovery method – avoiding the infection
There are many things that impact how the situation will turn out in your particular case when it comes to ransomware infection. For example, malware might fail to encrypt all files, or bug out when trying to delete Shadow Volume Copies, making a recovery so much easier. Additionally, you can almost completely negate the negative effects of ransomware infection by holding backups of your most important files.
However, keep in mind that, even if you do have backups, the threat might also use additional modules that steal sensitive information or proliferate other malware. Personal information that you might input via your keyboard on online banking or other websites might be harvested and sold on the dark web, increasing profits for the attackers.
Currently, there is no decryption tool for MarraCrypt ransomware-encrypted files available
Currently, there is no decryption tool for MarraCrypt ransomware-encrypted files available
Therefore, the best defense against ransomware is the prevention of its infiltration in the first place, and there are many things you can do to reduce the risk. While comprehensive security software is a good start, it is definitely not enough to prevent malicious files from accessing your system.
For example, you should always make sure that your Windows/installed programs are running the latest versions, never download software cracks/pirated installers, enable ad-block and Firewall, never reuse passwords, disallow email attachments to run macros, etc. In other words, be more careful when browsing the web, accessing your emails, or doing practically anything on your computer.
MarraCrypt ransomware removal steps
Many ransomware victims mistakenly believe that they can regain access to their files as soon as MarraCrypt ransomware removal is executed. Unfortunately, this is not the case, as there are multiple anti-malware programs that can successfully detect and get rid of the infection. For example, MarraCrypt virus executable is detected by 55 different AV applications under the following names:[4]
- Trojan.GenericKD.33362147
- Generic.ml
- Trojan:Win32/Occamy.C
- Trojan.Win32.MALREP.THBBDBO
- Heuristic
- Trojan.MSIL.DOTHETUK.wds, etc.
Along with the main executable, anti-malware tools can ensure that all the malicious files and other infections are eliminated from your system – so install one of the tools and perform a full system scan (in Safe Mode if required). As mentioned, this will remove MarraCrypt ransomware but will not restore the encrypted data.
If you had no backups, you could rely on, make a copy of all the encrypted files and then apply the methods we provide below. Keep in mind that they have a low success rate, and paying the attackers might be your only choice at saving your data.
Remove MarraCrypt using Safe Mode with Networking
If MarraCrypt file virus has disabled your anti-virus, access Safe Mode with Networking:
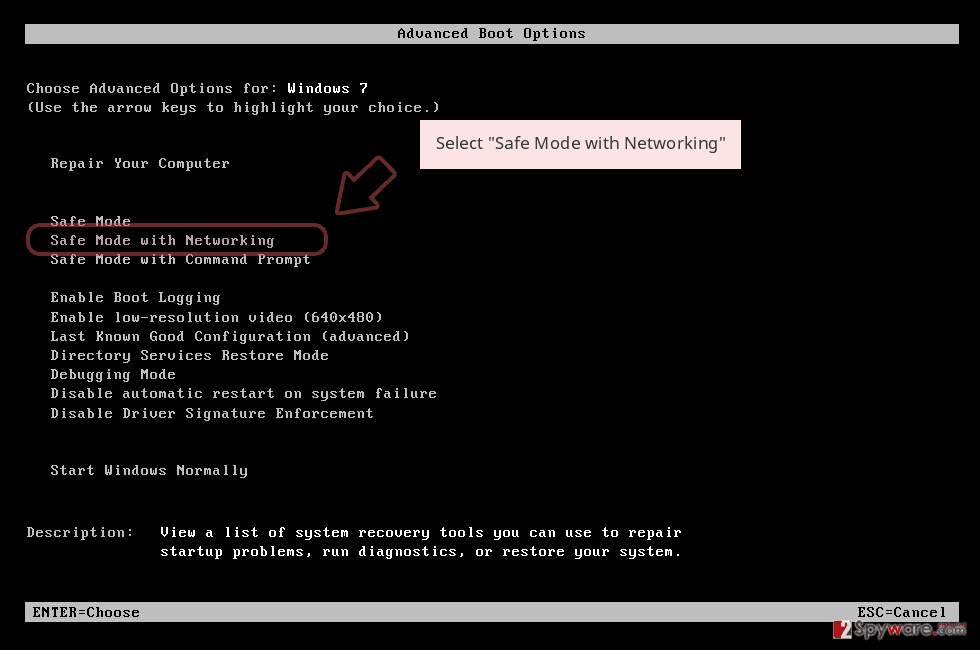
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
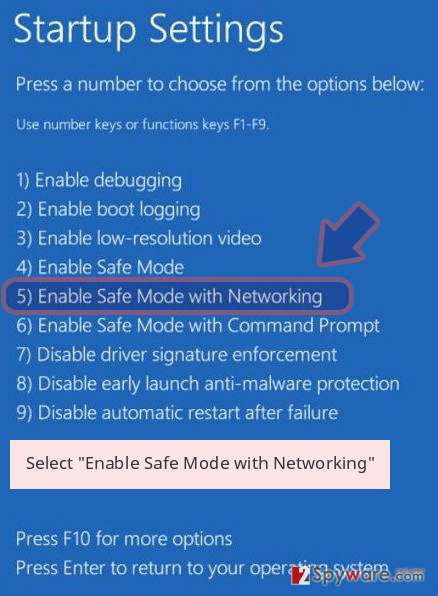
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete MarraCrypt removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove MarraCrypt using System Restore
In some cases, you can eliminate malware by employing System Restore:
Bonus: Recover your data
Guide which is presented above is supposed to help you remove MarraCrypt from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by MarraCrypt, you can use several methods to restore them:
When trying to recover .MARRA files, try using Data Recovery Pro
Data recovery software may be successful in retrieving working copies of files from the hard drive. However, the more you use your computer after the infection, the more chances of success diminish.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by MarraCrypt ransomware;
- Restore them.
Windows Previous Versions feature might be useful for separate files
If you had System Restore function enable prior to ransomware attack, Windows Previous Versions Feature might help you to recover files one-by-one.
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Make use of ShadowExplorer
This software works based on Shadow Volume Copies located on Windows. If these backups were not deleted by the MarraCrypt virus, you might be able to recover all your data.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No decryptor is currently available
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from MarraCrypt and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-03-04 at 07:14 and is filed under Ransomware, Viruses.

