Luckybeginning.com is a browser hijacker that aims to earn revenue by leading users to affiliated websites
Luckybeginning.com is a browser hijacker that, upon infiltration, changes the settings of the installed browser without permission
Luckybeginning.com is a search engine that has been developed by a company MobiTech Inc – the developers state that “LuckyBeginning is here to make your web experience faster, easier, and more organized.” However, this application is also considered a browser hijacker[1] and is a minor security threat, as its affiliates might bring users to misleading websites. Additionally, the site is marked as “Not secure” by Google Chrome, Opera, MS Edge, and other reputable web browsers.
In most cases, users will find Luckybeginning.com set as their homepage, new tab URL, and the search engine after the installation of freeware or shareware. This is due to a technique called software bundling – a deceptive marketing practice that results in infection of browser hijackers, adware, and even malware.
While Luckybeginning.com redirects all the searches to Google.com, its search engine cannot be trusted, as sponsored links are often presented at the top, leading to [sometimes unsafe] websites that might be misleading and result in the installation of other potentially unwanted programs. Besides, MobiTech also expresses that both anonymous and personal information might be gathered when users interact with the Luckybeginning.com site.
| Name | Luckybeginning.com |
| Type | Browser hijacker, potentially unwanted program |
| Infiltration | The unwanted application is usually installed along other software or downloaded from third-party hosting sites |
| Potential risks | Users who are infected are at the higher risks of being convinced to pay for useless software, install other potentially unwanted programs and disclose their information to unsafe third-parties |
| Symptoms | Homepage, new tab URL and the search engine altered; sponsored links appear at the top of search results; the overall amounts of ads increased |
| Termination | To get rid of browser hijackers and other PUPs, you can scan your machine with anti-malware or follow our manual removal guide at the bottom section |
| Recovery | To ensure a successful recovery and optimization, scan your computer with Reimage |
In general, browser hijackers are not considered to be high threats to user safety, as they do not compromise the machine’s vital functions like startup repair. Additionally, they usually do not engage in illegal harvesting of keystrokes or credit card details. Nevertheless, be aware that Luckybeginning.com does indeed uses tracking technologies like cookies in order to gather valuable information about users’ web browsing habits. The data includes:
- Time and date of sites’ visits
- IP address
- Computer configuration settings
- Search terms
- Links clicked, etc.
Be aware that search queries and IP addresses might disclose your identity, and, depending on the location you live in, it is considered to be personally-identifiable data. Also, Luckybeginning.com Privacy Policy discloses that some PII might also be collected:
We may receive personal information about you from a broad range of activities on luckybegining.com,including surveys,contests,program registrations,tell-a-friend services and general correspondence. Also,we may receive personal information about you from certain third party distribution partners or service providers as part of providing our search services to such third parties. Depending on the service used,the personal information we collect may include contact information (such as first and last name,mailing address,email address and telephone number),demographic information (such as age,gender,occupation and household income) and location and billing information (shipping and billing address,credit card information).
While the site claims that it uses appropriate measures to retain the gathered info security, there are no guarantees that this data will not be leaked by unwanted parties or even cybercriminals. Note that the search engine does not use an encrypted connection[2] to the site, hence it makes it easier for the attackers to steal it. We believe that this is one of the main reasons for Luckybeginning.com removal.

Luckybeginning.com is a potentially unwanted program that usually gets installed with other software from third-party websites
Additionally, those infected with the so-called Luckybeginning.com virus will also experience an increased amount of ads on all sites that they visit. While most of the content is safe, those who interact with suspicious ads might be linked to sites that deceptively prompt users to download scareware[3] apps or promise free/extremely cheap gifts like “The new iPhone X for $1.”
Please do not fall for these scams, as you might end up infecting your device with other PUPs or even malware, or spend money on software that is useless. Instead, remove Luckybeginning.com from your machine by following our detailed instructions below. Additionally, due to changes to web browser settings, we also highly advise you to reset Google Chrome, MS Edge, Safari, or any other installed browser. Finally, we also suggest you use Reimage to fix the inconsistencies left after the Luckybeginning.com hijack.
Browser hijackers might slip into computers unnoticed
Browser hijackers can be downloaded and installed via two main methods. The first one might be treated as direct – when you visit the official website of the app and install it right there. In most of the cases, users install various PUPs intentionally when looking for certain functionality, such as video converting, video display, system optimization, or other.
Another, and probably the most likely way to get infected with a browser hijacker is during the installation of free applications obtained from third-party sites. Such and similar software packages are widely spread on the Internet, especially on such popular download websites as download.com, soft32.com, softonic.com, cnet.com, and so on.
Fortunately, it is possible to opt-out of optional components easily. For that, you have to pick Advanced/Custom settings, watch out of deceptive button placements and pre-ticked boxes, and decline all the offers on the way. The unintentional installation of PUPs usually happens due to users’ inability to check each installation step carefully – so keep that in mind when you decide to download a new app.
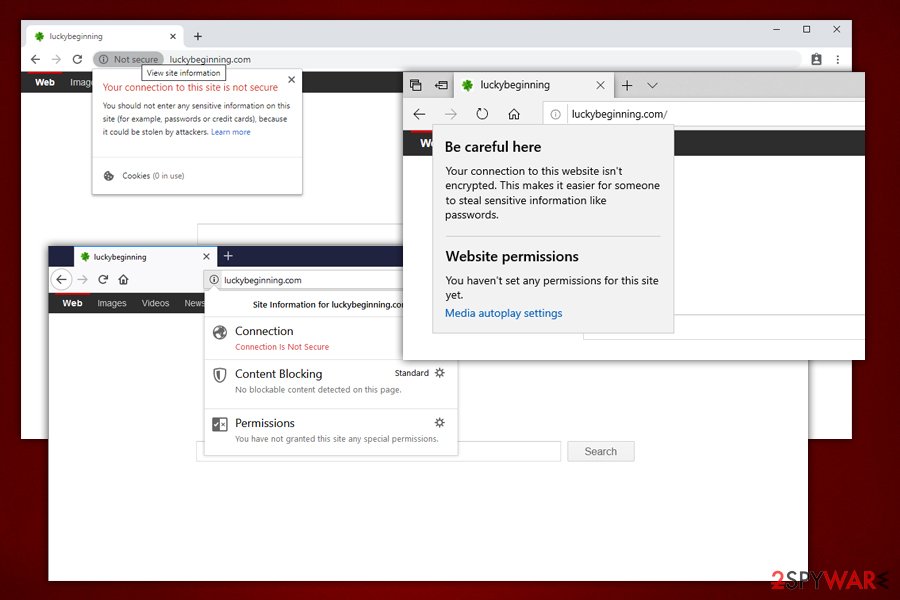
Luckybeginning.com is not using adequate protection to prevent attackers from stealing information entered on the site
Get rid of Luckybeginning.com hijacker
If you want to start Luckybeginning.com removal, you should first remind yourself the last time you installed new software on your computer. Since the homepage and new tab changes can be assigned by different PUPs, it might sometimes be difficult to determine which apps are related. This is especially true if you like to install new programs frequently or accept all the offers after landing on a deceptive site.
Therefore, soft the installed programs based on the date and check for any suspicious entries. To finalize Luckybeginning.com removal, you should also reset all the installed browsers. If you are struggling to find which app is responsible for the hijack, you might want to try to scan your machine with anti-malware software that recognizes PUPs.
You may remove virus damage with a help of Reimage. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.

