Lalo ransomware – a dangerous virus that renders all personal files on a host machine useless
Lalo ransomware is a file-encrypting cyber infection that launches the AES-256 encryption algorithm and encrypts most of the non-system files on the compromised PC. It has been detected in the middle of April 2020 by a well-known malware researcher Michael Gillespie who shared his findings on Twitter. The researcher revealed that the Lalo virus is a new strain of an infamous DJVU ransomware, which is already known as s sub-variant of STOP ransomware. It is built on the same malicious code as its ancestors, renders AES-256 cipher to lock files, and demands $980 ransom payment. The symptom of a Lalo ransomware attack is a .lalo file extension attached to locked files. Besides, a victim is also supplied with a ransom note called _readme.txt.
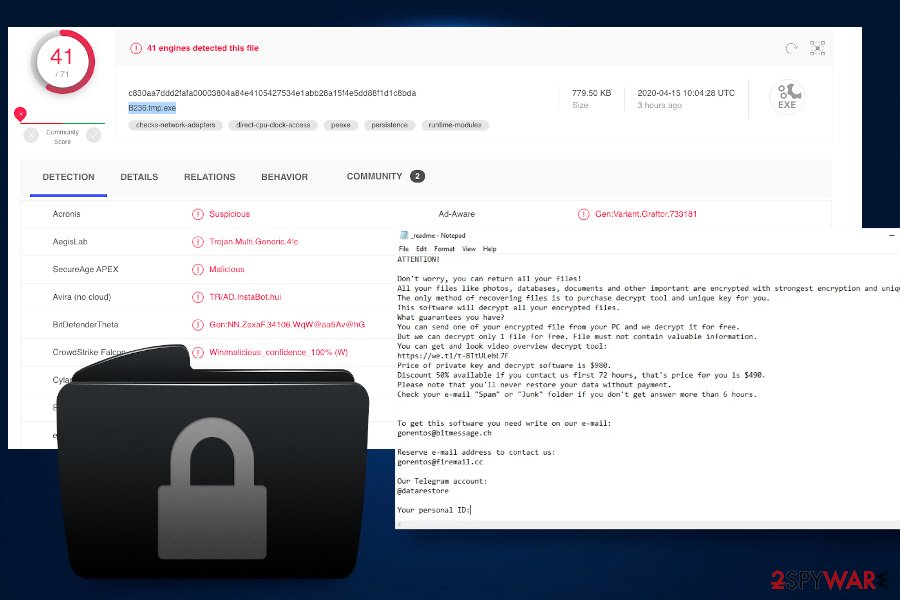
Criminals are initiating spam attacks to spread a malicious B236.tmp.exe file, which is one of the main malicious executables that the virus is based on. In addition to malicious spam attachments, bad actors may also exploit vulnerable RDPs[1] to forcibly inject a malicious payload via a remote server. In any case, if the payload is launched, Lalo ransomware roots deeply into the OS and runs multiple malicious processes in the background and alters Windows registry entries. Besides, it blocks AV software, removes Windows Volume Shadow copies, and builds a firewall to terminate third-party data recovery tools.
| Name | Lalo |
| Lineage | DJVU, STOP ransomware |
| Distinctive features | .lalo file extent attached to non-system files, _readme.txt file in every folder |
| Related files | B236.tmp.exe |
| Encryption technology | AES-256 |
| Infiltration techniques | Infected email attachments, software cracks, keygens, Trojans. In most of the cases, ransomware viruses spread via malicious .zip and .exe attachments that require enabling Macros. Besides, rogue software cracks distributed on the torrent websites are very likely to carry this infection. |
| Decryption methods | Currently, there is no Lalo decryption software available. However, some of its ancestors have already been cracked, therefore, the decryption software for current ransomware is very likely to show soon. |
| Removal possibilities | There is no other way to remove Lalo except to run a full system scan with a professional antivirus. According to VirusTotal[2], most of the famous AV engines are capable of detecting it, but virus definition should have the latest updates. Our recommended tools for ransomware removal are SpyHunter 5Combo Cleaner or Malwarebytes. |
| Tip | To fix the system’s vulnerabilities and bugs that ransomware virus have caused, launch Reimage Reimage Cleaner Intego tool to initiate a full repair. |
Upon all background activities are done, Lalo virus launches a scanner for non-system files (more than 100 extensions), including photos, videos, music, documents, database sheets, and similar. The ransomware encryption process is initiated using the AES-256 encryption algorithm, which applies a difficult mathematical structure to encode the files and generate diverse IDs and decryption keys for each victim.
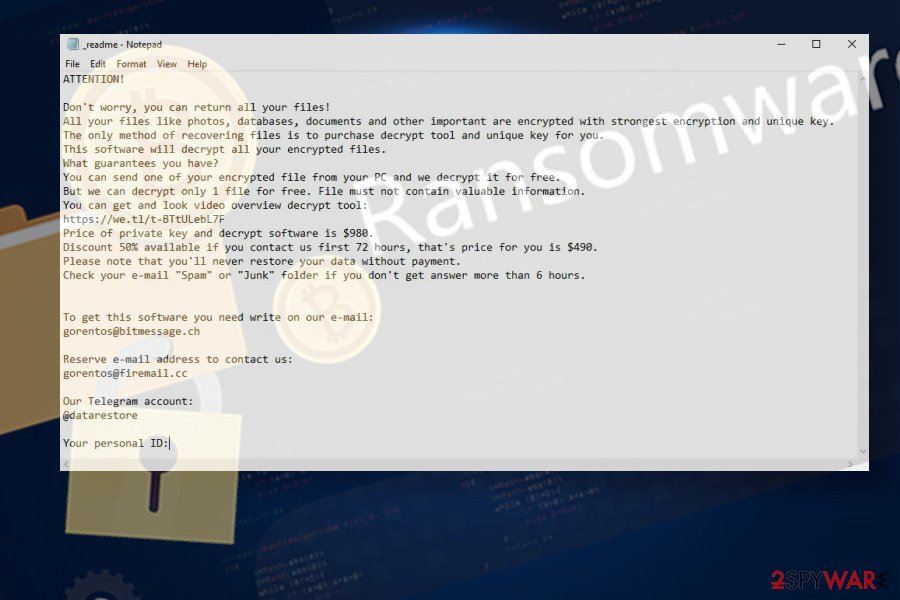
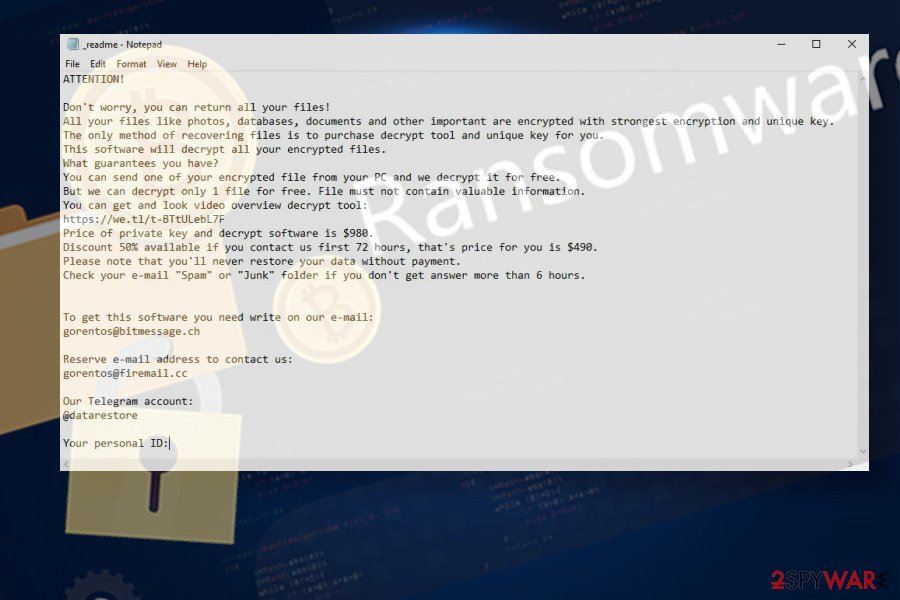
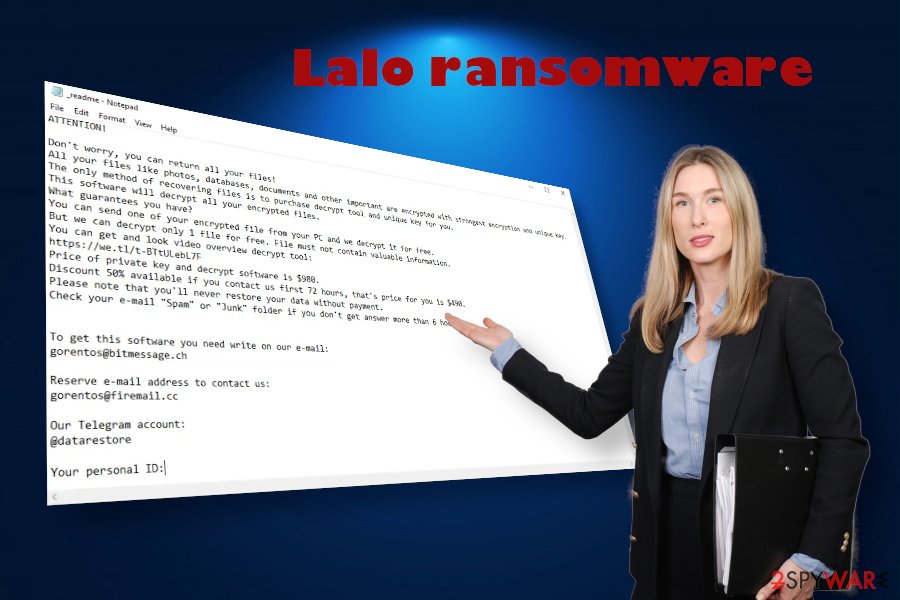
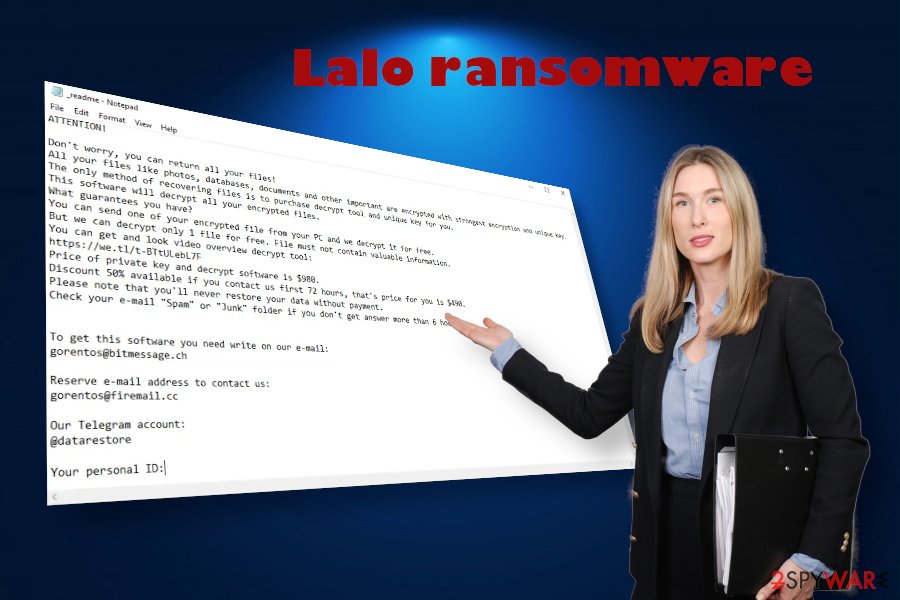
As soon as the encryption process is finished, victims are introduced with a ransom note, which is, as usual for many ransomware, named _readme.txt. That’s a really unpleasant message from hackers behind the Lalo virus, which states the fact that the computer is hacked, all personal files encrypted, and the ransom payment is expected.
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
hxxps://we.tl/t-oDZg08Mf5e
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]Your personal ID:
xxxxxxxxx
At this time, if the victim hasn’t yet noticed the malicious changes executed on the system, most probably will get a shock seeing all files with .lalo file extension. Unfortunately, it’s not possible to remove the extension in any way manually. One of the options to get files back is to contact bad actors standing behind Lalo ransomware via [email protected] or [email protected] within 72 hours and pay $490 for a personal Lalo decryption software.
The other method is to boot your PC into Safe Mode immediately and run a full system scan with it to remove Lalo ransomware package. No, the data will not be decrypted this way. However, having in mind that Djvu ransomware has been cracked by a DemonSlay355 virus researcher who shared a STOPdecryptor software, there are many chances that Lalo will be defeated as well. Keep in mind that tens of professional IT-savvy virus experts are continuously analyzing this virus and can release a free decryption key at any time. Therefore, we do not recommend rushing to pay the ransom, especially having in mind that contact with criminals may lead to scam or a second ransomware attack. Although the ransom note does not specify how the payment has to be done, based on the practice with previous Lalo ransomware variants, it’s very likely that crooks will require the payment in Bitcoins. That’s the safest way for criminals to remain untrackable.
Files with .lalo appendix indicate ransomware infection
Files with .lalo appendix indicate ransomware infection
Instead of having any contact with criminals, initiate a full Lalo removal and make a copy of files with .lalo extension. Upon virus removal, you will be able to try to recover them using third-party data recovery tools or wait a while for decryption software. As for the future, we strongly recommend you not to keep valuable information without backups. It’s always advisable to have copies of files on the cloud storage, remote server or a USB hard drive, which is accessible for you only.
Criminals exploit users’ inexperience and systems’ vulnerabilities to spread ransomware widely
While Lalo ransomware is still under investigation, we can only generalize the ways that it can infect computers. However, it’s more than clear that the most vulnerable devices that it enters are lacking system updates, are poorly protected, and already infected with malware.
In many cases, criminals managed to inject ransomware into devices with the help of Trojans – the infections that may operate in the disguise of a seemingly-legitimate executable file. However, Trojans can serve as a backdoor allowing criminals to steal logins and initiate brute-force attacks.
Malicious emails or spam is yet another perfect medium to spread. Criminals tend to disguise ransomware payloads under .zip or .exe attachments that are supposedly coming from governmental institutions, well-known companies or even friends of a potential victim. To read the attachment the potential victim may be asked to enable Macros. In this case, the Agree button serves as an allowance to launch ransomware payload.
Lalo ransomware drops multiple malicious files and renders files useless
Lalo ransomware drops multiple malicious files and renders files useless
Software cracks[3] or keygens are by far the most successful working ransomware distribution technique. These tools are widely used as they serve as a key for launching pains software for free. The vast majority of users are aware of the risk that they take by downloading those cracks from torrent websites or other questionable sources as they have started been used for malware dissemination many years ago.
Therefore, to keep files save from Lalo virus and similar infections it’s not only important to install AV tools, staying away from suspicious websites, unknown downloads, online software updates, and similar content is of equal importance.
Manual Lalo removal is impossible
Manual Lalo removal is not possible due to the multiplicity of malicious files on the random system’s folders. These files are typically chained, i.e. manual removal of .exe files will either be blocked or the file will be automatically restored by another related executable. Therefore, to remove Lalo or any of its previous variants you’ll have to use a professional software utility. A full system scan with SpyHunter 5Combo Cleaner or Malwarebytes tool in the Safe Mode environment will eliminate the whole ransomware package.
However, this malicious infection usually compromises Windows registry entries and deletes a multitude of necessary Windows executables. As a consequence, the system may start crashing or even delivering BSODs. Therefore, you should use a professional repair tool capable of fixing ransomware damage. Our recommendation is Reimage Reimage Cleaner Intego.
Remove Lalo using Safe Mode with Networking
You can try to launch the antivirus scanner, but we are pretty sure that the ransomware will keep the AV idle. Therefore, to deactivate ransomware, boot your PC into Safe Mode with Networking:
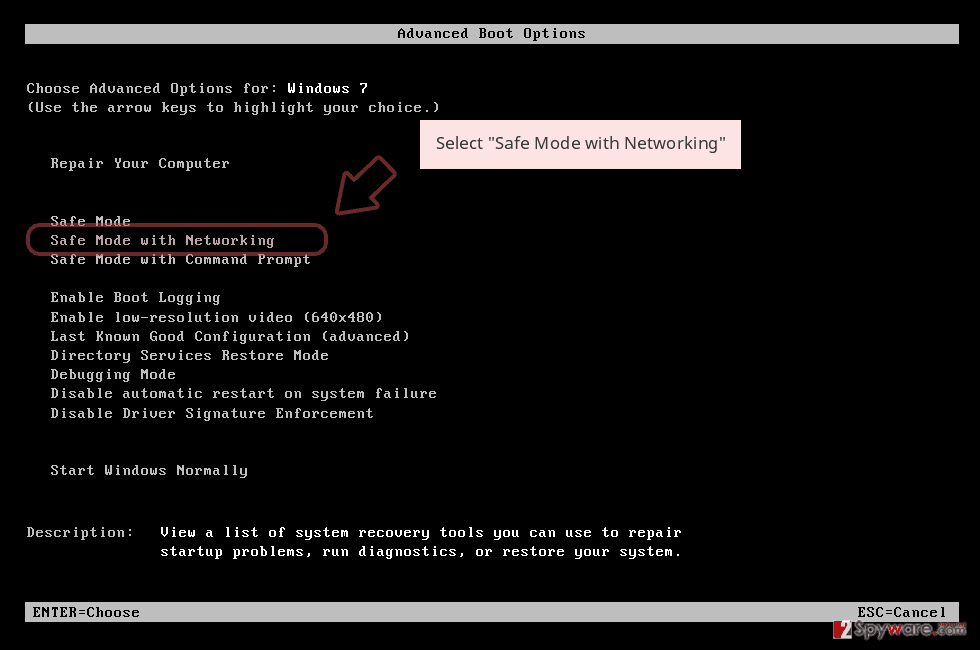
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
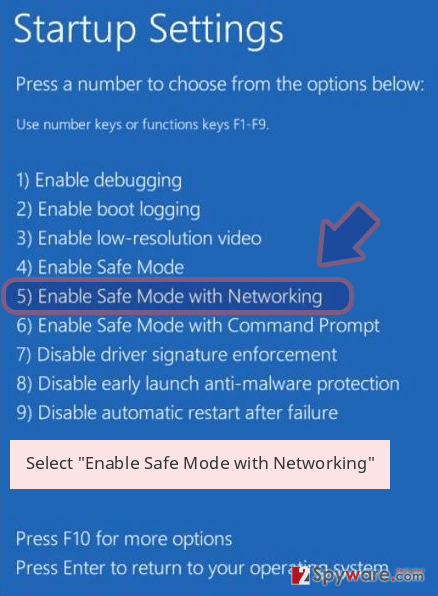
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner Intego or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Lalo removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Lalo using System Restore
System Restore feature can help to get rid of the virus. Use these instructions if help is needed:
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Lalo from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If all important documents on the system were locked with .lalo suffix, you can select from one of the following options: forget about them, pay the ransom to criminals or delete the virus and try to recover the files with the following software:
If your files are encrypted by Lalo, you can use several methods to restore them:
Data recovery Pro – a powerful tool for data recovery and encryption
Data Recovery Pro is the number one solution for people who are facing an issue with a file loss, be it after the system’s crash or ransomware attack.
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Lalo ransomware;
- Restore them.
Check for Windows Previous Versions availability
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
The Shadow Explorer tool might recover data encrypted by Lalo
Volume Shadow Copies might help. However, do not expect much from this option because crooks usually program ransomware to remove all copies. Nevertheless, it’s worth giving a try.
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
No Lalo decryption available yet
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Lalo and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner Intego, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2020-04-15 at 09:17 and is filed under Ransomware, Viruses.

