IEncrypt ransomware is a cryptovirus that employs zero-day exploit and particular bugs Bonjour updater in iTunes for Windows to spread
 IEncrypt ransomware is the threat using zero-day vulnerabilities and demanding up to 800k in Bitcoin from victims for the decryptor. The main targets of the cryptovirus are companies and businesses, hence a large amount of ransom and huge malicious malware campaigns.[1] The ransom note gets placed on the system after the file-locking and gets developed for each separate file. This message is also named according to the original file name: original_filename.PCname_readme.txt.
IEncrypt ransomware is the threat using zero-day vulnerabilities and demanding up to 800k in Bitcoin from victims for the decryptor. The main targets of the cryptovirus are companies and businesses, hence a large amount of ransom and huge malicious malware campaigns.[1] The ransom note gets placed on the system after the file-locking and gets developed for each separate file. This message is also named according to the original file name: original_filename.PCname_readme.txt.
This is a virus that employs the AES encryption algorithm to encode files on the network of the chosen organization. Since IEncrypt or BitPaymer ransomware has been targeting companies directly, after the data-locking procedure, the virus adds file extension in such a pattern: .PCname_of_company, for example, .3v3r1s file marker during the attack on Everis – one of the largest IT consulting companies in Spain. Every affected document, photo or video record becomes unusable.
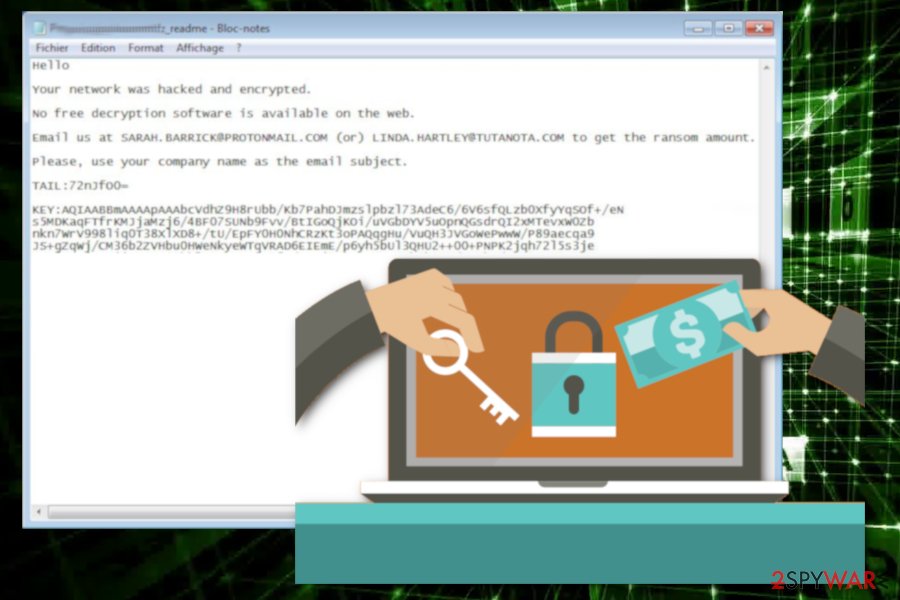
When data is encoded, ransomware places the ransom note for every file. This message is also named according to the original file name: original_filename.PCname_readme.txt. The IEncrypt virus was first discovered by the malware researcher S!Ri[2] who analyzed a given example from the Germany-based company that received MyDocument.doc.kraussmfz_readme.txt and Penguin. jpg.kraussmfz_readme.txt as ransom notes. According to these messages, victims need to contact developers by given email addresses if they want to know how big the ransom amount is.
| Name | IEncrypt ransomware |
|---|---|
| Type | Cryptovirus |
| Main target | Companies and large businesses because these targets can pay hefty amounts of ransom going up to millions of dollars in cryptocurrency |
| File extension | .PCname_of_company or any random characters with the connection to target directly |
| Ransom note | original_filename.PCname_readme.txt is the file that contains a message about encryption, payment options, and contact details that can connect the victim to crooks |
| Contact emails | [email protected]; [email protected]; [email protected]; [email protected] |
| Removal | Use antivirus program to remove IEncrypt ransomware completely and rely on system optimization tools like Reimage for virus damage and possible repair |
This ransomware targets large companies and encrypts files on the network of the organization. IEncrypt ransomware virus uses the AES encryption algorithm for this process and changes the original code of the targeted data. Then all encoded files become useless.
IEncrypt ransomware then adds a file marker to each record and renames encrypted data with a pattern that contains company name. Also, the virus generates a ransom note for each encrypted file and names that text file with a similar pattern that includes the name of the affected company. These ransom notes all contain the identical message.
IEncrypt ransomware ransom note displays the following:
Hello company name,
Your network was hacked and encrypted.
No free decryption software is available on the web.
Email us at [email protected] (or) [email protected] to get the ransom amount.
Please, use your company name as the email subject.
TAIL:LTpTQTE4wIAfNXBI
KEY:-
This message encourages victims to contact IEncrypt ransomware developers to get the opportunity to decrypt their files. However, this is not advisable and you shouldn’t even consider paying the ransom. Since the main target is companies hackers focus on getting money and decryption is not the priority for these cybercriminals.[3]
IEncrypt ransomware is a cryptovirus that encrypts files and marks them with a personalized file extension.
Apple vulnerability and affected Spanish companies
IEncrypt ransomware made headlines with news about recent malware attacks targetting Spanish companies and Apple iTunes version for Windows. The vulnerability in Apple product was abused to deliver the malware via packaged Bonjour updater which comes for iTunes for Windows. The infiltration and the pattern of attack are difficult to detect because malware exploits an unquoted path vulnerability in Bonjour, which is software that organizations may not even know is running on their systems.
The specific zero-day flaw discovered in Bonjour targeted public companies with IEncrypt/BitPaymer ransomware for at least the last six months. Researchers stated the unquoted pats vulnerability that allowed the attacks to happen:
Software developers are using more and more object-oriented programming, and many times when assigning a variable with a path, they assume that using the String type of the variable alone is enough – well it’s not! The path still needs to be surrounded by quotes.
IEncrypt ransomware got terminated and the vulnerability patched, but exploit is too effective since the legitimate process was signed was used. malicious processes got executed with the help of the process signed by a known vendor. Unfortunately, since AV tools want to minimize the conflicts with third-party software application even malicious behavior cannot be indicated as suspicious by anti-malware products.
A few weeks after these reports another company, this time in Spain stated about widespread ransomware attack with the statement for the employees:
We are suffering a massive virus attack on the Everis network. Please keep the PCs off. The network has been disconnected with clients and between offices. We will keep you updated.
One of the largest IT consulting companies suffered this attack on the first Monday in November. Ransomware infection forced the company to shut down all systems until the issue gets resolved completely. Malware marked all the encoded files using the typical company-connected extension .3v4r1s appendix. This is a strong indication that the attack was highly targeted towards the company. The ransom amount for Everis was €750,000 (~USD 835,000). It was unsure which malware affected the company, but based on the highly targeted attack nature, extension pattern, and other unique features it was determined to be IEncrypt ransomware virus. 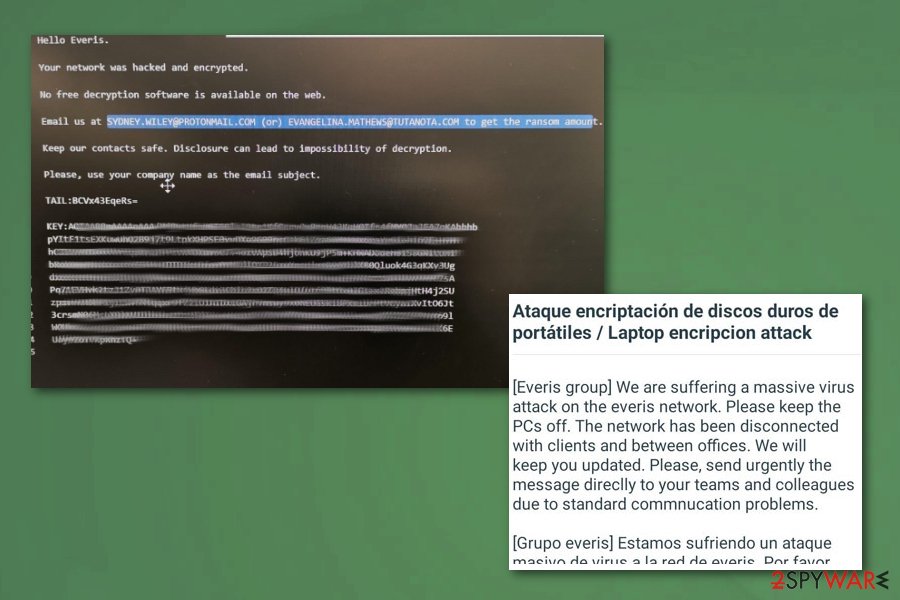
IEncrypt ransomware is the threat targeting large companies and businesses, so a bigger amount can be demanded. IEncrypt ransomware starts by infecting the system and adding files to make sure it is persistent. Detection rate[4] also show that this virus is not easily detectable by antivirus tools. This is a serious threat and you need to get rid of it as soon as you can.
Researchers[5] recommend using reputable tools for the process of IEncrypt ransomware removal. You can employ your antivirus but make sure that your device is rebooted in Safe Mode, this way your chosen tool can work properly.
You should remove IEncrypt ransomware from the system and then focus on system repair and virus damage elimination. Cryptovirus adds various files in system folders and alters registry keys, so use Reimage and clean the system further, change those settings back and fix damaged files.
Ransomware gets on the network via email
Unfortunately, ransomware finds its way on the system with the help of a spam email campaign. An email with infected file attachment may look safe and legitimate but when the employee opens the email and downloads the attached file malicious ransomware payload gets on the system directly or malware designed to spread cryptovirus around install itself on the machine
Email in these malware spreading campaigns can look like sent from a legitimate company, service or even government, Users tend to open these emails willingly and when the document filled with malicious macros gets on the system or the link from the file is opened, malware script gets installed.
You can avoid this cyber infiltration if you pay close attention to emails you get or files you download. Email from PayPal, DHL or eBay can be legitimate if you use the service at the time. However, note that malicious actors hide their products behind well-known names.
Eliminate IEncrypt ransomware with the help of professional tools
Make sure that you remove IEncrypt ransomware as soon as possible because ransomware can affect other parts of your machine if you left it run on the computer. You should use antivirus programs and terminate the malware completely since it can affect more than you notice.
Also, tools like Reimage, SpyHunter 5Combo Cleaner or Malwarebytes might help for the process of cleaning and optimizing the system thoroughly if you want to recover your files after IEncrypt ransomware removal. Data recovery methods can only work on the malware-free and clean machine because ransomware encrypts files again if you add new data on the computer.
Cryptovirus elimination can get difficult even with automatic malware-fighting tools because this cryptovirus can affect the performance of the program. You can reboot your device in Safe Mode and then scan the device thoroughly, this way your anti-malware tool can work smoothly and delete all intruders associated with IEncrypt ransomware virus.
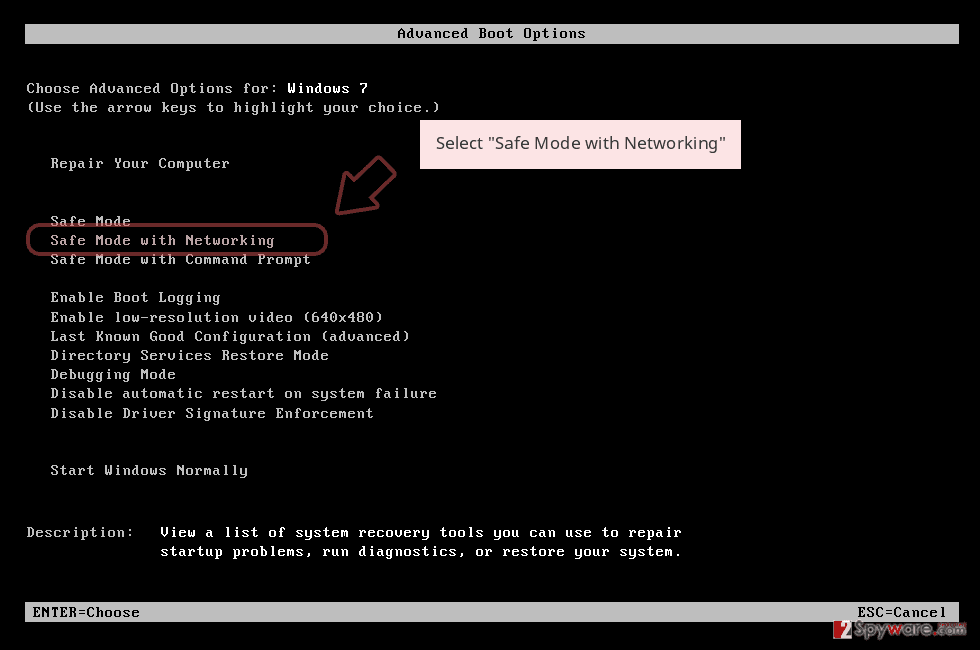
Remove IEncrypt using Safe Mode with Networking
You should reboot the device in Safe Mode with Networking before using the antivirus tool for IEncrypt ransomware removal because this way you can ensure your program runs as smooth as it should
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
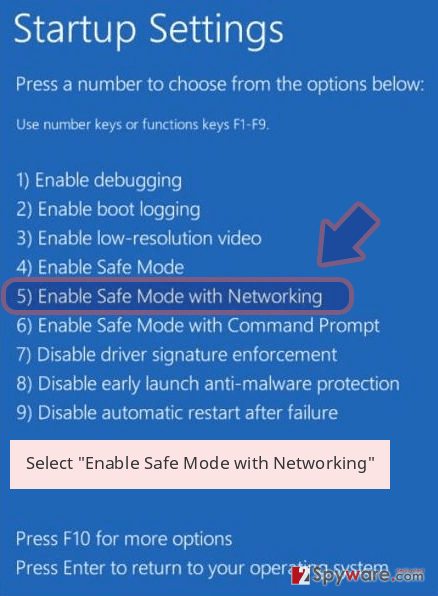
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete IEncrypt removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove IEncrypt using System Restore
System Restore can help remove IEncrypt ransomware by recovering the system in a previous state before the attack
Bonus: Recover your data
Guide which is presented above is supposed to help you remove IEncrypt from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by IEncrypt, you can use several methods to restore them:
Restore your files using Data Recovery Pro
Try Data Recovery Pro for encrypted files but make sure to remove IEncrypt ransomware before. Also, this program can help with accidentally deleted data
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by IEncrypt ransomware;
- Restore them.
Try Windows previous Versions feature as an alternative for data backups
Employ Windows Previous Versions after IEncrypt ransomware termination and recover your encrypted files. However, you can use this feature if System Restore was enabled before
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
ShadowExplorer is yet another option for data recovery when you have no backups
ShadowExplorer can help with encoded files if Shadow Volume Copies remain on the system
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Decryption is not possible
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from IEncrypt and other ransomwares, use a reputable anti-spyware, such as Reimage, SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2019-11-05 at 06:04 and is filed under Ransomware, Viruses.

