Hakbit ransomware – a decryptable malware that might append different file extensions depending on the ransomware version
Hakbit ransomware – malware that urges $300 in Bitcoin as the ransom price
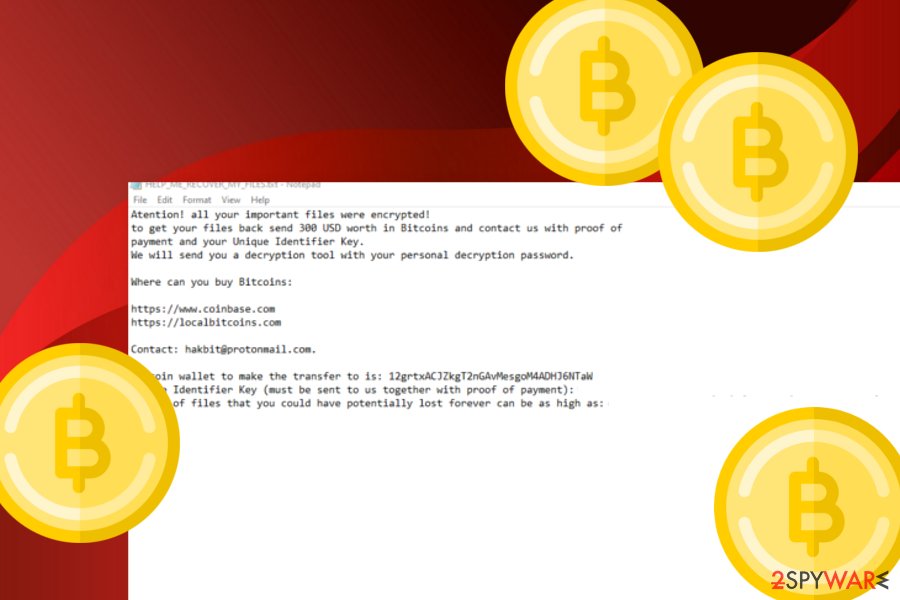
Hakbit ransomware is a Bitcoin-demanding virtual parasite that can add .crypted appendix if an older version and .horse/.turretsyndrome extensions if a newer variant. The infiltration process begins by altering the desktop’s background image and replacing it with wallpaper.bmp that is the HELP_ME_RECOVER_MY_FILES.txt ransom note. The crooks urge for a $300 in BTC payment and proof of the transfer process via [email protected] email, they also provide the 12grtxACJZkgT2nGAvMesgoM4ADHJ6NTaW Bitcoin wallet address. Gladly, there is no need to follow Hakbit virus demands as Emsisoft has already released a decryption tool for the files that have been locked with AES-256 encryption.[1]
| Name | Hakbit ransomware |
|---|---|
| Type | Ransomware virus/file-locking malware |
| Appendix | This dangerous malware string appends the .crypted appendix most of the time. However, newer variants of this ransomware add the .horse and .turretsyndrome extensions |
| Ransom note | The crooks provide all ransom demands in the HELP_ME_RECOVER_MY_FILES.txt message and also place the same text instead of the computer’s original background paper |
| Price | Criminals urge for $300 to be transferred in Bitcoin cryptocurrency. Such currency is asked to remain anonymous and avoid identity revealing |
| Bitcoin wallet | 12grtxACJZkgT2nGAvMesgoM4ADHJ6NTaW is the location where victims are urged to transfer the ransom price |
| The hackers provide [email protected] email address as a way to make contact and require to send evidence of the ransom payment to this email account | |
| Spreading | Ransomware virus can be distributed through many different sources. However, the most popular ones still are software cracks, spam messages, vulnerable RDP |
| Removal | You should use only reliable antivirus software to get rid of the ransom-demanding malware, otherwise, you might make severe mistakes or miss some crucial components |
| Repair | If your antivirus has discovered that the malware has compromised some system entries and components on your Windows computer, you can try repairing some of them with Reimage Reimage Cleaner . There is no 100% guarantee that this tool will help but it definitely is worth giving a try to |
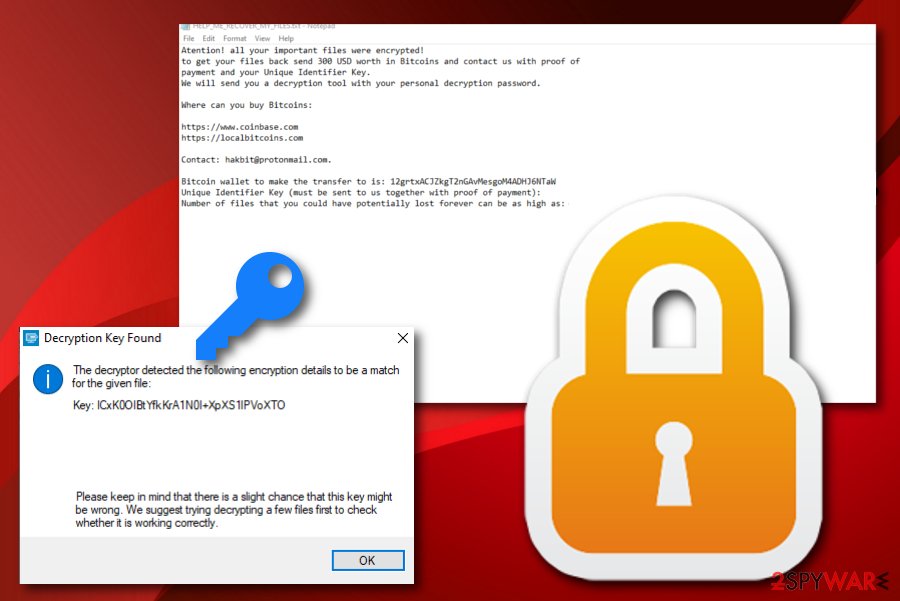
| Decryption key | Gladly, Emsisoft has already released the decryption software for files that are locked by AES encryption by this notorious ransomware virus. You can get it from this direct downloading link. |
Hakbit ransomware is a tricky malware form that can enter the computer system and place itself in the Task Manager and Windows Registry unnoticed. This malicious infection can camouflage as a legitimate machine process such as chrom32.exe, firefox.exe, SkypeApp.exe, opera32.exe, lsass.exe, svchst.exe, crcss.exe, calc.exe, memop.exe, mysqld.exe, spoolcv.exe, ctfmom.exe. This way the victims might even not notice the malware as it stays hidden under an original name.
Furthermore, Hakbit ransomware can get distributed through RDPs, email spam, software cracks, and other places. Hackers often manage to succeed in their attempts which shouts out about a big number of computer systems worldwide. The weaker your computer security is, the bigger the risk of a ransom infection. After successful infiltration, the main signs of ransomware are encrypted files/documents, the changed desktop background, and displayed ransom message.
As we have already mentioned, Hakbit ransomware might be running as a legitimate process on your Windows computer. If you see your Windows Task Manager performing to very similar processes or un unknown task that you have never seen before, there is a big chance that it might be a sign of malware. In this case, run a full malware scan to find out all malicious strings on your machine. If some damaged components have also been spotted, you can try repairing them with Reimage Reimage Cleaner .
Hakbit ransomware is a dangerous malware form that uses AES encryption to lock up files and documents
In addition, Hakbit ransomware might make some alterings to the Windows hosts file[2] to prevent access to security-related websites and receive valuable information towards the malware removal process. If you have found out that the hosts file has been touched and damaged during the malware attack, you should eliminate the component right after Hakbit ransomware removal process, otherwise, access might stay blocked.
Continuously, Hakbit ransomware might aim to delete Shadow Volume Copies of encrypted data by executing PowerShell commands, forcibly launch each time the computer is turned on, inject a module that allows repeatedly scanning the system for new files once in a while, avoid antimalware detection, inject other malicious programs, for example, Trojan horses. After reading this, you should have come to the conclusion that you need to remove Hakbit ransomware ASAP.
The longer you keep Hakbit ransomware on your Windows computer system, the worse the effects might get. Make sure that you choose reliable software to complete the elimination. Also, note that the detection name of the ransomware virus might differ within each different antivirus program that you employ. According to VirusTotal information,[3] this malicious infection has been spotted as malware by 48 AV engines out of the total 68.
When Hakbit ransomware is no longer active on your machine, you can start thinking about data recovery purposes. Keep in mind that there is no need for paying the demanded ransom as you will only lose a big amount of money for nothing. First of all, the decryption software has already been released and can be used at any moment. Second, the cybercriminals might appear to be scammers and trick you into paying the required price in exchange for receiving nothing.
The most popular distribution tactics of ransomware infections
Internet security experts from NoVirus.uk[4] state that ransomware virus can be distributed via multiple sources. However, the most popular spreading places have always been the same and do not seem to be changing for now:
- Email spam. Crooks pretend to be from reliable companies, e.g. FedEx/DHL and drop suspicious messages to random users’ email boxes that come with hazardous attachments or links pretending to be “order information”.
- Software cracks. If you like downloading cracked programs from third-party sources, there is a big chance that you are going to receive some type of malware on your computer.
- P2P networks. If you download and install videos, short clips, or full movies from sources such as The Pirate Bay, eMule, or other torrenting services, there is a big chance that you might receive malware as these pages often lack required security.
- Vulnerable RDP. Ports such as TCP port 3389 are often targeted by hackers do to their weak security level. If there is not password included or a weak one added, the criminals can easily connect to your computer system remotely.
We recommend all users to stay careful while completing online actions. Avoiding visiting unknown sources and downloading products from unsecured locations. Also, check your email properly, do not open any attachments without scanning them with antimalware first. Continuously, always generate strong passwords that contain letters, numbers, and symbols. Finally, keep your antivirus regularly updated so that it operates without any struggles.
Removal possibilities for Hakbit ransomware
If you want to remove Hakbit ransomware from your Windows computer, we insist that you do the process with reliable antimalware software, otherwise, you might cause severe damage to your machine. Besides, the malware might leave numerous damaging components in your Task Manager and Registry that also require cleaning for a full ransomware removal process and avoiding the risk of repeated appearance of Hakbit virus.
After Hakbit ransomware removal you can continue with data recovery purposes. There are some tools added to the end of this article. Also, keep in mind that there is no need for paying the demanded ransom price as the official decryption key is also already released. Furthermore, you should search your computer system for any malicious “leftovers” with software such as SpyHunter 5Combo Cleaner or Malwarebytes and try fixing damaged components with Reimage Reimage Cleaner .
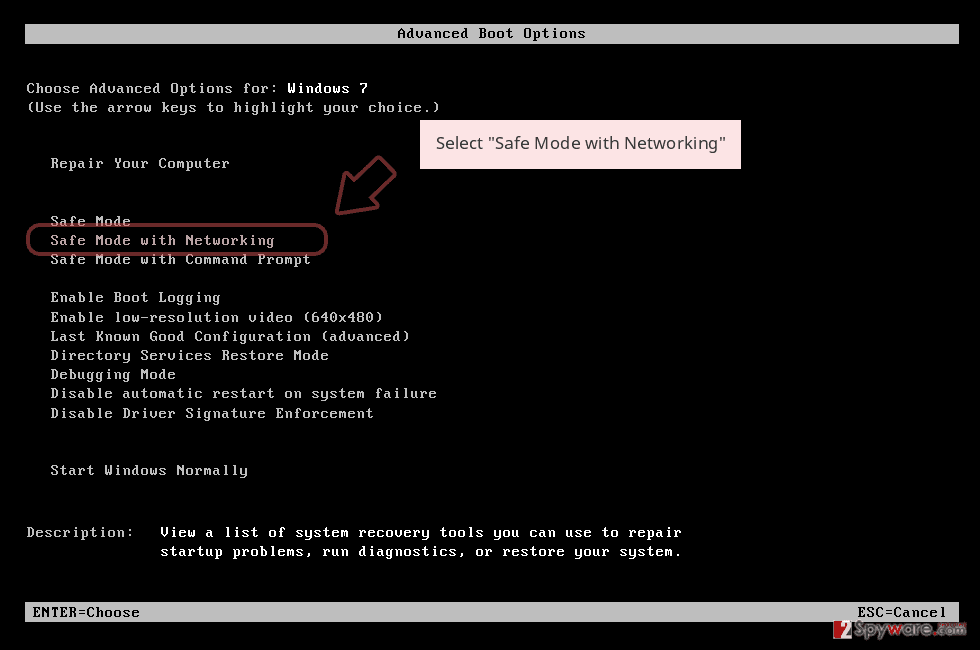
Remove Hakbit using Safe Mode with Networking
To diminish malicious activities on your computer system, you should boot the machine to Safe Mode with Networking
- Windows 7 / Vista / XP
- Click Start → Shutdown → Restart → OK.
- When your computer becomes active, start pressing F8 multiple times until you see the Advanced Boot Options window.
- Select Safe Mode with Networking from the list
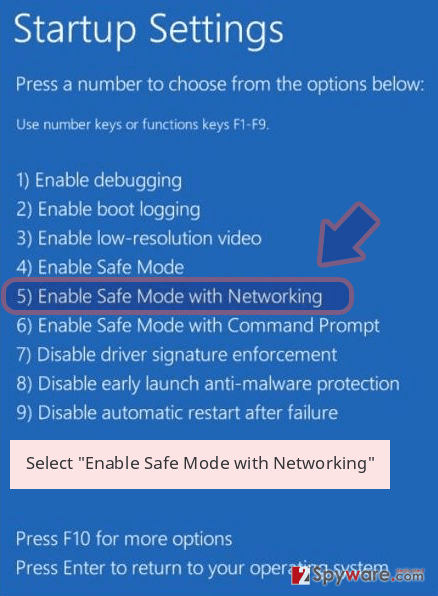
Windows 10 / Windows 8
- Press the Power button at the Windows login screen. Now press and hold Shift, which is on your keyboard, and click Restart..
- Now select Troubleshoot → Advanced options → Startup Settings and finally press Restart.
- Once your computer becomes active, select Enable Safe Mode with Networking in Startup Settings window.
-
Log in to your infected account and start the browser. Download Reimage Reimage Cleaner or other legitimate anti-spyware program. Update it before a full system scan and remove malicious files that belong to your ransomware and complete Hakbit removal.
If your ransomware is blocking Safe Mode with Networking, try further method.
Remove Hakbit using System Restore
To stop malware-laden processes on your machine, employ the following steps to activate System Restore
Bonus: Recover your data
Guide which is presented above is supposed to help you remove Hakbit from your computer. To recover your encrypted files, we recommend using a detailed guide prepared by 2-spyware.com security experts.
If your files are encrypted by Hakbit, you can use several methods to restore them:
Try using Data Recovery Pro for file restoring tasks
Employ this tool if you want to recover some data that has been locked by the ransomware virus
- Download Data Recovery Pro;
- Follow the steps of Data Recovery Setup and install the program on your computer;
- Launch it and scan your computer for files encrypted by Hakbit ransomware;
- Restore them.
Windows Previous Versions feature is suitable for data recovery
Use this method to restore some data files that have been touched by the malware. However, ensure that you have activated System Restore before
- Find an encrypted file you need to restore and right-click on it;
- Select “Properties” and go to “Previous versions” tab;
- Here, check each of available copies of the file in “Folder versions”. You should select the version you want to recover and click “Restore”.
Use Shadow Explorer for data restoring purposes
Try out this software if you have been looking forward to restoring some files. However, note that this technique might not work if the malware has damaged Shadow Copies
- Download Shadow Explorer (http://shadowexplorer.com/);
- Follow a Shadow Explorer Setup Wizard and install this application on your computer;
- Launch the program and go through the drop down menu on the top left corner to select the disk of your encrypted data. Check what folders are there;
- Right-click on the folder you want to restore and select “Export”. You can also select where you want it to be stored.
Download the official decryptor here
Finally, you should always think about the protection of crypto-ransomwares. In order to protect your computer from Hakbit and other ransomwares, use a reputable anti-spyware, such as Reimage Reimage Cleaner , SpyHunter 5Combo Cleaner or Malwarebytes
This entry was posted on 2019-12-03 at 05:43 and is filed under Ransomware, Viruses.

