GraceWire trojan is the information-stealing malware that gets sent via phishing emails
GraceWire trojan is the product from the Evil Corp hacker group that spreads malware that avoids detection and can directly infect various machines.[1] Thi particular trojan was the final payload dropped in the recent campaign of these Dridex trojan developers. A trojan is set to steal information that later on can be used to directly blackmail people or spread more campaigns, send phishing emails. The virus takes advantage of the same distribution method itself and targets people with a well-known hacking collective method. Since this is not a new threat, and creators have experience in such malware attacks, the trojan can easily take over the machine to find full control processes, activities. The purpose of these stealthy intruders mainly is to obtain the control of the device and gather sensitive information, so infiltration allows spreading other malware on the computer too. Remote control, command execution, system manipulation, and other malware injections are the main issues regarding these stealthy trojans.
| Name | GraceWire virus |
|---|---|
| Type | Info-stealing malware/ Trojan |
| Purpose | The threat is set to steal passwords, other sensitive data, banking credentials, files from the system directly |
| Damage | Stolen information can be used in secondary attacks, sold on the dark web, used for identity theft and other malicious campaigns, lead to serious privacy issues |
| Distribution | Hackers use phishing campaigns to target victims, so social engineering[2] methods allow spreading the malware via macro-malware or other infected files |
| Elimination | GraceWire trojan removal should include programs like anti-malware tools, so all the threat files and programs get deleted fully |
| Repair | You can and need to check the system for additional alterations in the system. Running Reimage Reimage Cleaner Intego can properly help with virus damage and corrupted files or functions |
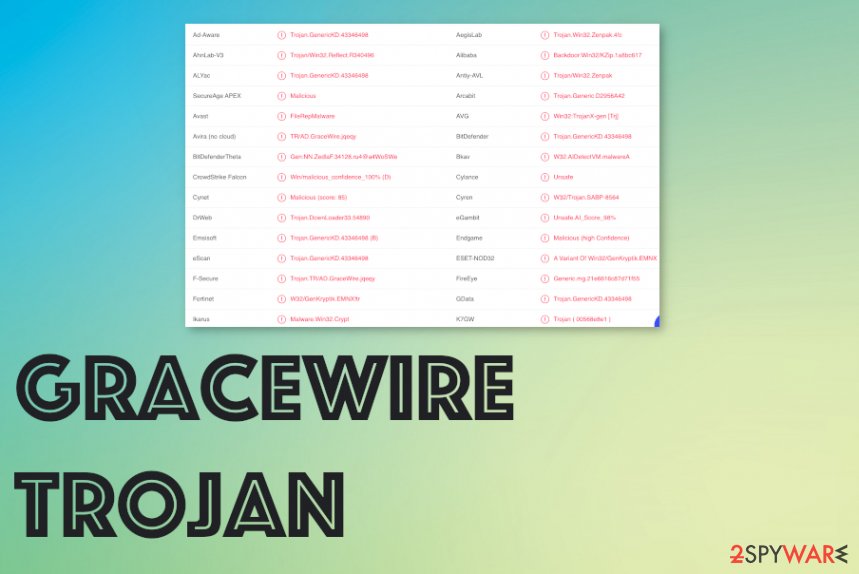
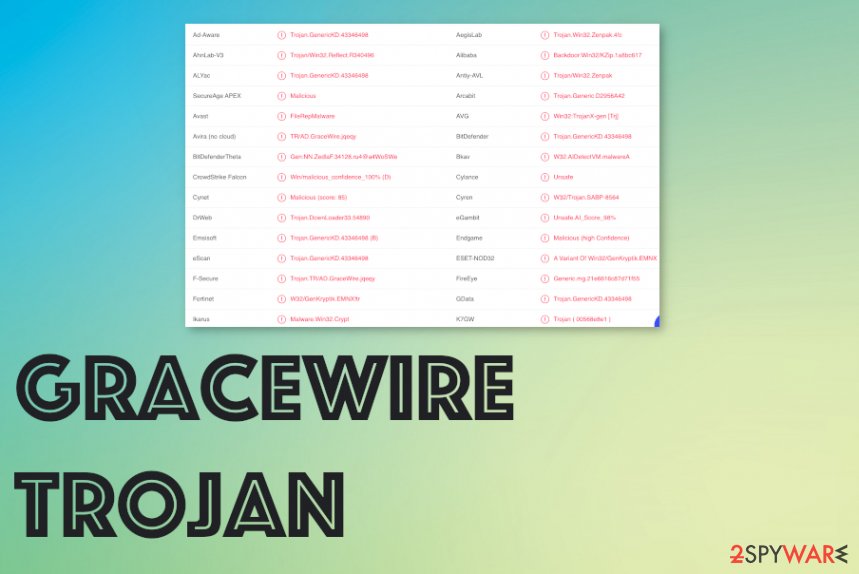
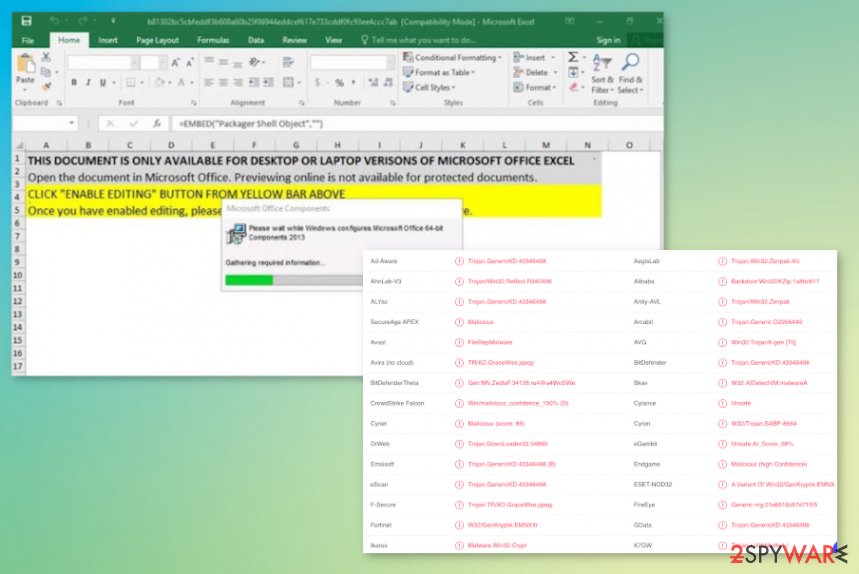
GraceWire trojan is the malware that can perform a number of actions once the machine is affected. Hackers can easily choose from the list of functionalities and run their malware according to their goal. Your anti-malware tool can indicate the threat[3] in various names, so the name of the particular malware is not often shown.
Main detections[4] that are associated with the GraceWire virus in particular: Trojan:Win32/GraceWire!dha; Trojan:Win32/GraceWire; Trojan.Win64.GRACEWIRE.D. You need to additionally scan the machine and check for the proper solution for this threat or any additional infection.
You can remove GraceWire trojan if you find it in time and can run the proper AV tool for the malicious program termination. When the threat gets quarantined or indicated by your AV detection engine, make sure to react as soon as you possibly can. As for the system cleaning, you need to thoroughly check for damaged, affected, corrupted files in system folders too.
GraceWire is stealthy and can run for a while until you detect malicious behavior and can remove this infection. Hackers aim to gather data, inject other scripts, or even gain direct control, so files, programs get added in the background. You cannot find all the alterations yourself, so run Reimage Reimage Cleaner Intego for the optimization purpose. 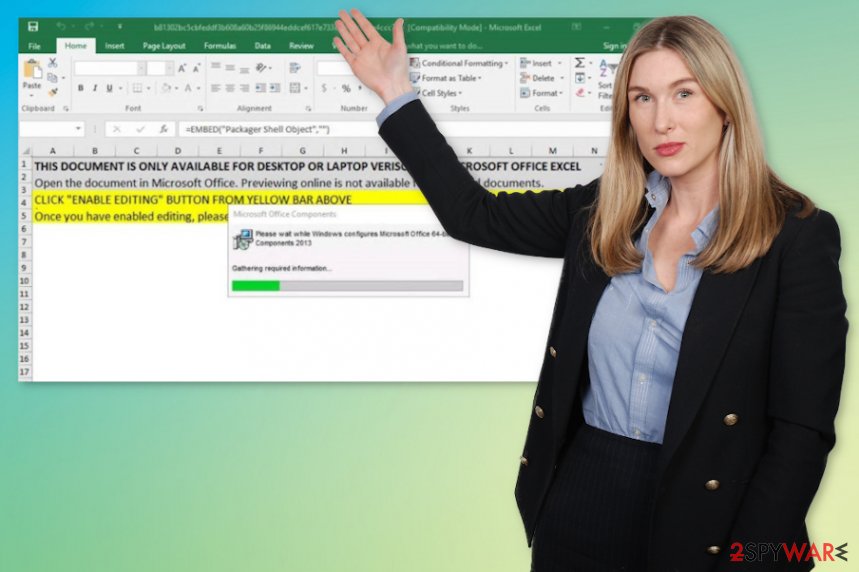
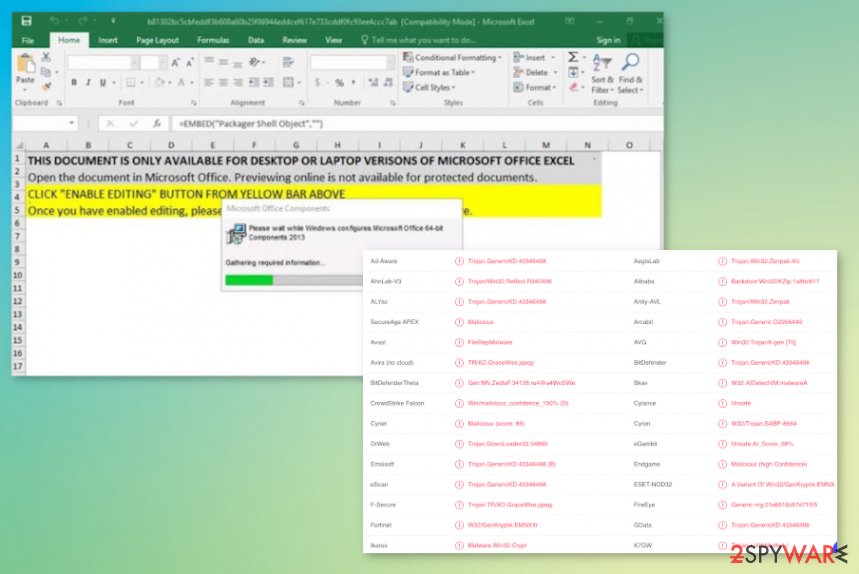
GraceWire – the trojan that spreads via malicious documents with the help of macro-malware scripts.
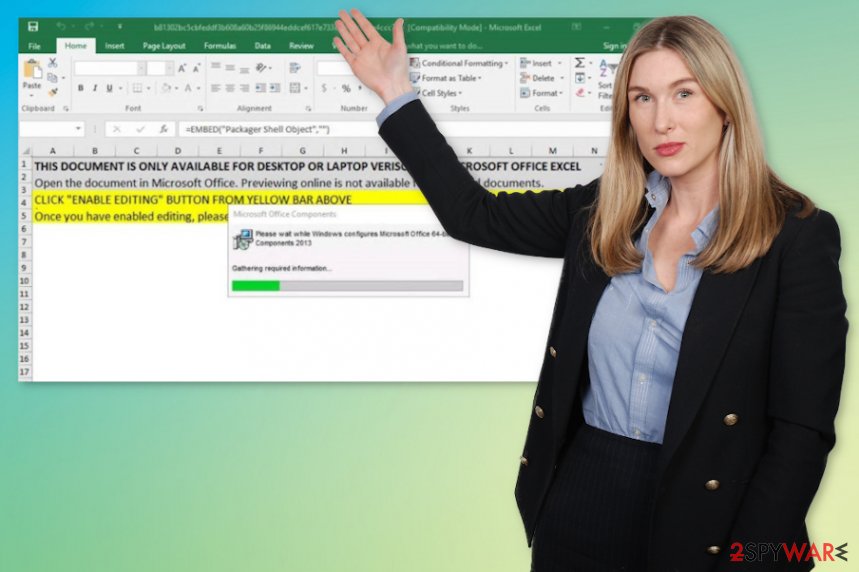
GraceWire – the trojan that spreads via malicious documents with the help of macro-malware scripts.
GraceWire trojan removal processes get difficult when the malware gets to run in the background for long. It can be programmed to drop other malware, so infection is more likely the first step of the more serious ransomware infection attack. You need to react as soon as you can, so the programs like anti-malware tools can find and terminate the intruders.
When you encounter the trojan GraceWire, you need to think that there are many functions this malware piece can have:
- Code execution. This threat can run operations and any commands that attackers program the virus to.
- Data exfiltration. Trojans are collecting various details that belong to the user and steals installed files, details from the web browser.
- Remote control. Hackers can use malware to take over the affected machine.
- Manipulate the behavior. System settings can get configured in the way that attackers need and want.
- Malware injection. Threats like this can drop any virus file on the system once it is running in the background.
The consequences of the infection like this can go from performance issues to the inability to run a program or use features. GraceWire virus can damage your device permanently and leave with the useless machine, lead to privacy issues, or make you a target of the more personalized attack.
GraceWire trojan – the info-stealer that is delivered by the Evil Corp hacker team.
GraceWire trojan – the info-stealer that is delivered by the Evil Corp hacker team.
Bogus emails disguised as important messages distribute trojans and more malware
Social engineering tactics allow hackers to attach malicious files in the formats of MS documents or Excel data, PDFs. recipients of such emails thing that they get important information from a company or service. Since the notification looks legitimate enough, victims enable macros without thinking twice.
The content of the malicious email includes HTML redirects, and the infection started when the malicious script gets injected onto the system. Script-controlled instances can rely on particular topics or file-types. Bogus emails look harmless because it’s notifications resemble popular spam emails and messages from PayPal, eBay, other platforms.
You need to avoid any suspicious emails, notifications from senders you not know or services that you don’t use. Delete any suspicious emails, especially when the message has links or attached files.
You need to terminate GraceWire virus as soon as you can, so the system gets cleaned
To properly remove GraceWire trojan, you need to fully control what is happening on the system. The best option would be to scan the machine using an anti-malware or security tool that checks various places of the machine. When you do so, you can find and delete the threat fully.
SpyHunter 5Combo Cleaner or Malwarebytes are the ones that could help you deal with the GraceWire trojan removal because security software detects and removes various types of malware. Unfortunately, the program is not capable of repairing damage or restoring system functions. For such purposes, you need a tool like Reimage Reimage Cleaner Intego.
The government has many issues in regards to tracking users’ data and spying on citizens, so you should take this into consideration and learn more about shady information gathering practices. Avoid any unwanted government tracking or spying by going totally anonymous on the internet.
You can choose a different location when you go online and access any material you want without particular content restrictions. You can easily enjoy internet connection without any risks of being hacked by using Private Internet Access VPN.
Control the information that can be accessed by government any other unwanted party and surf online without being spied on. Even if you are not involved in illegal activities or trust your selection of services, platforms, be suspicious for your own security and take precautionary measures by using the VPN service.
Computer users can suffer various losses due to cyber infections or their own faulty doings. Software issues created by malware or direct data loss due to encryption can lead to problems with your device or permanent damage. When you have proper up-to-date backups, you can easily recover after such an incident and get back to work.
It is crucial to create updates to your backups after any changes on the device, so you can get back to the point you were working on when malware changes anything or issues with the device causes data or performance corruption. Rely on such behavior and make file backup your daily or weekly habit.
When you have the previous version of every important document or project you can avoid frustration and breakdowns. It comes in handy when malware occurs out of nowhere. Use Data Recovery Pro for the system restoring purpose.
This entry was posted on 2020-07-03 at 06:06 and is filed under Trojans, Viruses.

