Edundedpra.club is a browser scam that tries to make that uses social engineering for nefarious purposes
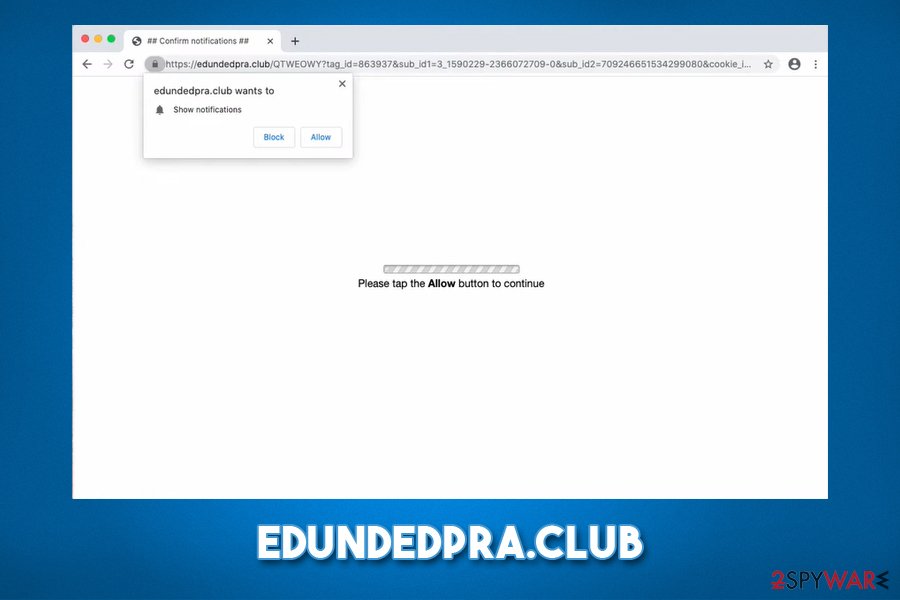
Edundedpra.club is a suspicious website that uses social engineering tricks to make users subscribe for unwanted ads
Edundedpra.club is a suspicious website that uses social engineering tricks to make users subscribe for unwanted ads
Edundedpra.club is a malicious website that tries to trick users into subscribing to notifications, which later cause ads to appear on their desktops. The social engineering[1] technique revolves around making users think that once they click on the “Allow” button, they will be able to access the underlying content of the webpage. However, once they accept the notifications to be shown, they are not presented with anything, but instead, they are delivered Edundedpra.club pop-up ads even when their Google Chrome, Mozilla Firefox, Safari, or MS Edge is turned off.
While in most cases Edundedpra.club virus can be avoided by simply leaving the site, frequent encounters with scam sites might indicate adware infection. In such a case, users will need to locate an eliminate the potentially unwanted program that is hiding within the web browser or Mac/Windows computer.
| Name | Edundedpra.club |
| Type | Push notification virus, adware |
| Infiltration | Pop-up ads are caused by accepting the push notification feature upon entering the site; frequent redirects to suspicious, scam, phishing, and similar sites are typically related to adware, which is distributed via software bundle packages, or fake update prompts/misleading advertisements on various websites |
| Symptoms | Pop-up ads appear at the bottom right corner of the screen even when the web browser is off. Adware infection can cause redirects, sponsored links in search results, unwanted browser changes, and overall increased amount of advertisements on all visited sites |
| Elimination | To stop pop-up notifications, you need to access the settings of your web browser – we provide the instructions below. To eliminate adware, you could employ anti-malware software or use the manual guide below |
| Optimization | You can employ Reimage Reimage Cleaner Intego to optimize and improve the performance of your machine after you get rid of the infection |
Potentially unwanted programs such as adware are typically distributed via software bundle packages – this happens when several applications are compiled into a single installer. By using deception, users are then forced to install apps that they did not intend to in the first place. Hence, bundling often is the main cause of unwanted adware infiltration and Edundedpra.club redirects.
However, it is important to differentiate between the adware infection and Edundedpra.club notifications that are appearing on the screen for a completely different reason. Ads are very versatile, and they can come in many forms, including pop-ups, banners, deals, sponsored links, hyperlinks, offers, etc. These can be related to one of the following:
- Ads that are embedded on the site;
- Ads that are injected as a virtual layer within the web browser;
- Ads that are provided via legitimate features, such as browser notification prompts.
Edundedpra.club ads are typically related to the latter cause and do not immediately mean that some potentially unwanted program is installed on the system. Nonetheless, adware is the one that might bring users to this and many other malicious websites, causing even more commercial content. Keep in mind that you might also be redirected to Edundedpra.club after clicking a link on a random website.
Edundedpra.club is a site that might indicate adware infection
Edundedpra.club is a site that might indicate adware infection
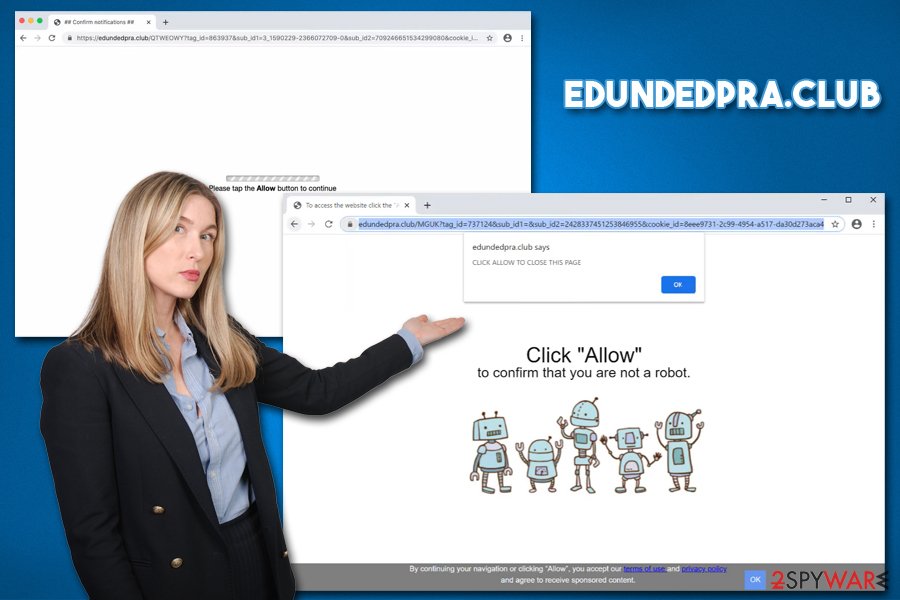
Once users access the Edundedpra.club, they are presented with the following message:
Click ALLOW to confirm that you are not a robot!
The “not a robot” check is a legitimate way of checking that the user is not a bot[2] by many websites. This confuses users and makes them believe that this is just one of such checks. Once they click on “Allow,” they do not see any signs or symptoms immediately, but later might see malicious ads popping up at random times. Since the ads show up seemingly out of nowhere, users are unaware that they need to access their web browser settings to remove Edundedpra.club notifications.
Thus, if you see pop-up ads on your screen, even if the web browser is turned off, you should check the instructions we provide in the Edundedpra.club removal section below. However, in case the ads and other unwanted behavior do not stop after performing these actions, we recommend checking for adware, resetting the web browser, scanning machine with anti-malware, and tools like Reimage Reimage Cleaner Intego.
Ways not to get tricked by malicious actors and keep your browser ad-free
There are several methods of how ads can reach your screen, and sometimes they are unavoidable. The ads itself are not the problem as long as they are not trying to mislead o trick users into installing something that they otherwise would not (e.g., scareware app or malware). Nonetheless, the best way to avoid intrusive and malicious ads is by installing ad-blocking browser extension (make sure you install a reputable one from official sources, as some ad-blockers from suspicious software were actually used to install malware on users’ machines or cause more ads instead).
As previously mentioned, another cause of ads might be adware. These applications are usually of low value to the user and are also distributed in a way that would allow stealthy infiltration. Freeware developers often compile several apps into a single package, which tends to trick unsuspecting users into installing potentially unwanted programs unintentionally.

Edundedpra.club asks to allow notifications upon the site entry

Edundedpra.club asks to allow notifications upon the site entry
To stop such occurrences, you need to be always very aware of what you are doing when installing new programs, especially when they stem from third-party sites. Dieviren.de[3] security experts suggest that you would choose official sources for your downloads, employ reputable anti-malware with PUP detection feature, read user reviews/blog posts, and always pick Advanced/Custom settings during the installation. This way, you would be able to eliminate all the ticks by the pre-ticked boxes and avoid unwanted apps altogether.
Edundedpra.club ads removal instructions
The main trick in the Edundedpra.club removal lies within the permission of displaying notifications via the web browser (even though the ads appear directly on your desktop). All you have to do is access the settings section of your web browser and stop this side from sending you notifications. Here’s how to do it on different browsers:
Google Chrome
- Go to Menu > Settings
- Find Privacy and security section and click on Site Settings
- Under Allow section, you should see Edundedpra.club entry
- Click More Actions and then click on Block
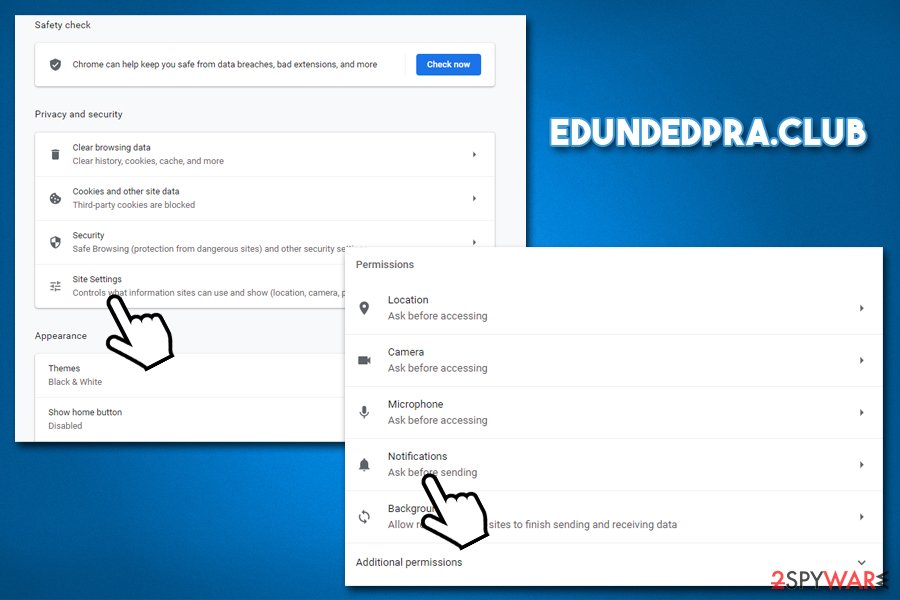
Eliminate Edundedpra.club pop-up ads from via Chrome settings panel
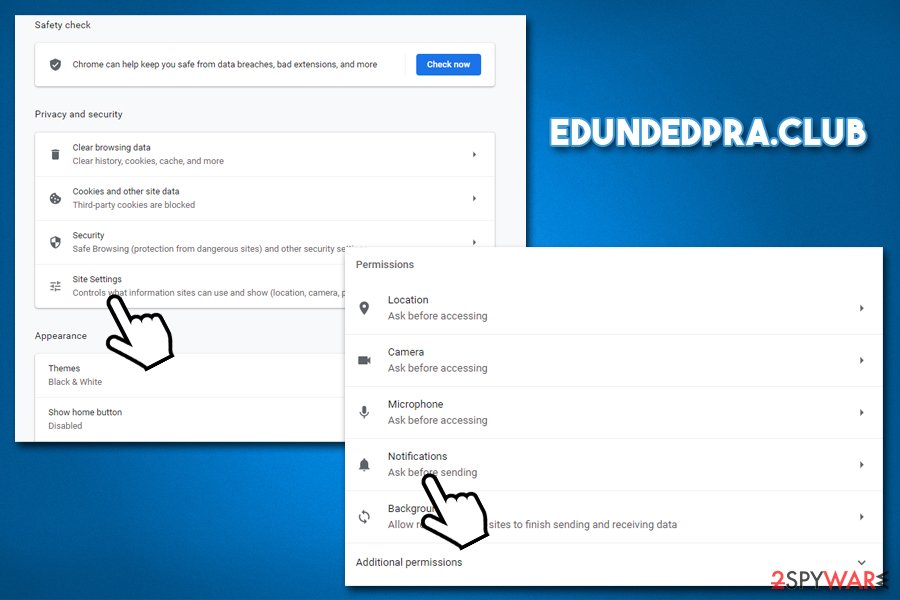
Eliminate Edundedpra.club pop-up ads from via Chrome settings panel
Mozilla Firefox
- Select Menu > Options
- Pick Privacy & Security section
- Under Permissions, click Settings near Notifications section
- In the Settings – Notification Permissions window, click on the drop-down menu next to Edundedpra.club
- Pick Block and then Save Changes.
Safari
- Go to Safari > Preferences…
- Under Websites tab, pick Notifications
- Pick Edundedpra.club and then select Deny
Android (Google Chrome)
- Tap on Settings (three vertical dots) at the top-right of the Chrome web browser
- Pick Notifications
- Scroll down to Sites section
- Locate the Edundedpra.club URL and toggle the button to the left (Off setting).
In case you are still suffering from ads and redirects after you remove Edundedpra.club from the allowed list, you should also check your system for adware. For that, scan the machine with reputable anti-malware software. If the program finds something, you should also reset all the installed web browsers, as explained below.
You may remove virus damage with a help of Reimage Reimage Cleaner Intego. SpyHunter 5Combo Cleaner and Malwarebytes are recommended to detect potentially unwanted programs and viruses with all their files and registry entries that are related to them.
When you work on the domain, site, blog, or different project that requires constant management, content creation, or coding, you may need to connect to the server and content management service more often. It is a hassle when your website is protected from suspicious connections and unauthorized IP addresses.
The best solution for creating a tighter network could be a dedicated/fixed IP address. If you make your IP address static and set to your device, you can connect to the CMS from any location and do not create any additional issues for server or network manager that need to monitor connections and activities. This is how you bypass some of the authentications factors and can remotely use your banking accounts without triggering suspicious with each login.
VPN software providers like Private Internet Access can help you with such settings and offer the option to control the online reputation and manage projects easily from any part of the world. It is better to clock the access to your website from different IP addresses. So you can keep the project safe and secure when you have the dedicated IP address VPN and protected access to the content management system.
While much of the data can be accidentally deleted due to various circumstances, malware is also one of the main culprits that can cause loss of pictures, documents, videos, and other important files. Potentially unwanted programs may clear files that keep the application from running smoothly.
More serious malware infections lead to significant data loss when your documents, system files, or images get locked. Ransomware is the one that is focused on such functions, so your device gets useless without access to needed data. Even though there is little to no possibility to recover after file-locking threats, some applications have features for such recovery in the system.
In some cases, Data Recovery Pro can also help to recover at least some portion of your data after data-locking virus infection or general cyber infection.

