The world is going digital: data backup and restore is becoming crucial to corporate institutions and advised to home users


Digital data has been vastly expanded in the past few decades – mainly since the internet became common around the world. The modernization of the industries and technology advancements allowed companies to perform tasks more efficiently, and most of the work is now done via a computer that is connected to a particular network, server, or/and worldwide web.
Since computers became a huge part of everyone’s lives, data stored on them expanded exponentially – important documents, pictures, projects, engineering drawings, and much more are now stored virtually. While some businesses and corporations still choose to have hard copies of such essential documents available, most are going digital – the demand is largely implemented due to customer needs.[1]
As evident, data needs to be protected from outside intrusions, natural disasters, as well as unintentional corruption or removal, i.e., human errors. Hence the need for data backups arises – each of the companies is now using various data retention and backup methods that would allow an easy recovery in case of unforeseen circumstances.
Data backups are essential to corporations and businesses to the point where a company could go under just due to a simple cyberattack without a reliable backup available.[2] However, correct data backup and recovery practices should be used by home users as well, as personal photos, work files, and other important data could disappear in an instant, never to be seen again.
What is data backup and recovery?
In the IT field, the backup and recovery process is described as a combination of technologies and practices that allow making copies of the important data in predetermined periods. This process typically involves copying backup data to its original or a new location, so the lost files can be used in the place of the lost ones. Backups can prevent permanent data loss and eliminate high recovery costs in the case of disaster, human error, or a cyberattack.
While data backup and recovery is highly managed within larger businesses, and sufficient resources are dedicated for the purpose, data backup and recovery to home users is a process that is a lot less complex. Reasons for this include:
- Limited resources and finances;
- Much lower data volumes.
Due to these two factors, data backup and recovery practices vary greatly. In this article, we will look over peculiarities related so such a process, why data backups are essential, and what is the most efficient way of ensuring your important files are never lost forever.
Data loss can occur due to various different reasons
In order to understand why data backups and recovery are important, it is mandatory to know how data loss can occur. In many cases, home users are unaware of the fact that their information can be gone in just a blink of an eye, so knowing how the data can disappear is a crucial step in realizing why data backup & recovery is vital.
Device and hardware failures
Hardware failure is one of the most common reasons why you might permanently lose access to your files, accounting for more than 40% of the data loss cases.[3] Technology is always moving forward, and more advanced devices are produced for corporate and home user consumption.
Despite the warranties, there is no way to assure that a hardware component will not stop working one day. In some cases, however, the reasons for the failure and unrelated to technical aspects of a hardware component but rather incorrect handling, for example, external damage when a device is dropped on the floor.
A failing hard drive or a solid-state drive can result in a full data loss. While such information can still be recovered if a storage device is repaired, a failure sometimes might be critical, resulting in permanent loss of data.
Malware attacks
Malware is a type of software that attempts to perform malicious actions in order to benefit cybercriminals behind it. In most cases, infections such as Remote Access Trojans (RATs),[4] Backdoors, Rootkits, Spyware, and many others are employed by crooks to steal sensitive information, use the host to send spam, proliferate other malware, and perform other malicious activities. These infections can rarely result in personal file compromise, although bugs[5] in malware code can easily result in the operating system failures, ultimately resulting in a data loss.
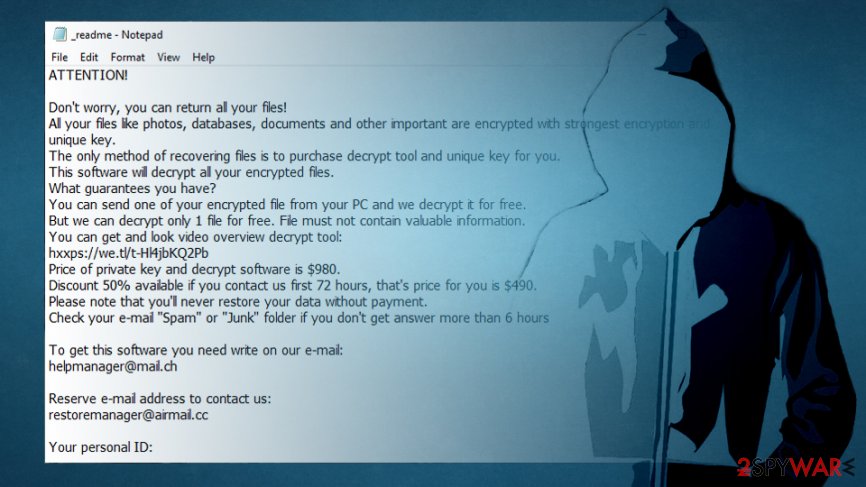
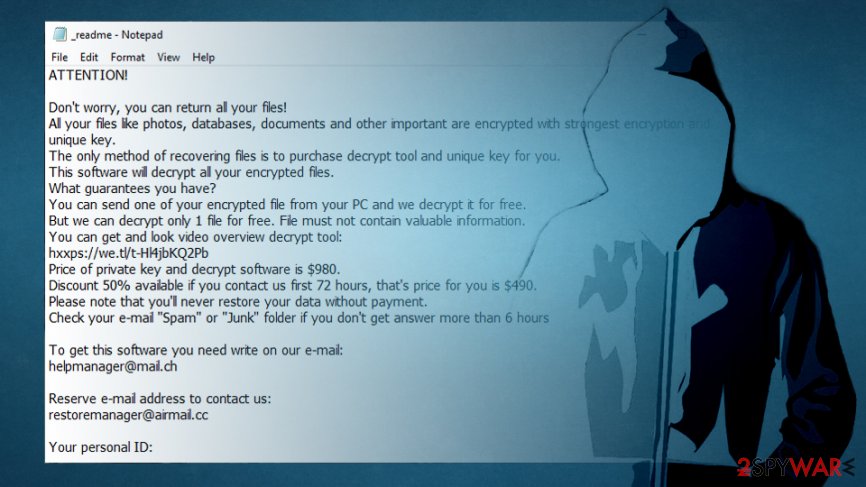
However, the primary threat that can result in a full data compromise is ransomware – a type of malware that is designed to lock up all personal files on the system and then demand ransom to be paid in Bitcoin digital currency for a decryption tool. Since ransomware is most commonly programmed to delete automated Windows backups such as System Restore, easy recovery is not usually an option, since encryption algorithms like RSA cannot be decrypted even by the most powerful supercomputers.
Human errors
Let’s face it: all humans make mistakes, regardless of how careful they are. In these situations, we should rely on technologies that could help us avoid the negative consequences of errors.
There are many ways in which you could lose files and data stored on your computer due to your own mistakes. For example, you could lose your phone, laptop, or another portable device never to see it again. You could also spill a cup of coffee on vital hardware components, and damage them beyond repair. Finally, you could have a low hard disk space that could crash your PC before you manage to save an important document. In other words, unintentional data loss happens all the time.
In these situations, the best way to ensure that your most important files are safe is by restoring them from backups, as this information can be recovered even if the device that stored it initially was lost or destroyed. That is one of the reasons why backup and recovery is so important for home consumers.
Theft
Property theft is an issue that can affect anybody, regardless of their place of residence (although the more secure areas will result in less probability of theft). Evidently, the most common devices to be stolen on a train, on the beach, or another place are laptops, tablets, and phones, as they are portable and often carried to different places, as they were designed for such purpose in the first place.
However, even workstations at the home office can be prone to theft, as house break-ins are not that uncommon. Thieves usually grab everything that can offer the most value, and electric devices such as laptops or desktop computers can provide this value.
Natural disasters
While extreme disasters such as hurricanes, tornadoes, earthquakes, and volcano eruptions can be one of the causes for complete destruction in the property where the data is located, more common situations, such as high-temperature changes or floods can also cause hardware damage. Of course, these situations do not occur very often, but they should never be excluded.
Besides natural disasters mentioned above, there are things like house fires, electrical surges, water pipe breaks, and other daily issues that could potentially kill your computer for good.
In situations like this, virtual backups on a cloud store are the best options, as backup hardware stored in these conditions would be ultimately destroyed.
Physical or virtual backups? Both have advantages and disadvantages
Data backups are not effective when they are stored on the same medium, as it can fail at any time.[6] Essentially, storing data backups on the same platform makes it much less efficient. For example, in the above-mentioned example of a ransomware attack, backups stored on a separate hard drive that is connected to the same PC would result in backed data encryption. As a result, backups would be completely ruined, as malware typically penetrates all the connected devices, servers, and networks in case no appropriate security measures are applied prior to that.
There are many different kinds of data that are stored on a computer. While some such data is not important and can be recovered via the internet (for example, installed applications can be re-downloaded and re-installed) or other sources, personal files are those of the most value. People store invaluable family photos, work documents, school projects, and other data. In some cases, the loss of such files can be devastating in many ways if no backups were retained.
Data storage hardware can be used for backups


There are numerous ways of how data backups could be prepared and how data could be recovered. As previously mentioned, backups should be stored on a different medium than the original files are. For that, a hardware storage device can be used, which include:
- Hard drive (HDD)
- Solid-State drive (SSD)
- External hard drive
- USB Flash
- DVD/CD
- NAS (Network Attached Storage) devices
All of these can could work for you, although which one should be used highly depends on your preferences and availability of access. For example, if you only need to backup a few files that are really important for you, you should rely on a USB flash, as it is fast, simple, and convenient. If you are dealing with a large data dumps, you are better off with using larger storage such as an external hard drive.
Remember, as soon as you copy data that you want to backup, you should immediately physically disconnect the device from the primary system. This way, you will be able to segregate backups and make them effective in case of unforeseen circumstances.
Remote storage is perfect for data backups
Physical devices are not the only solution when it comes to file backups – these have multiple shortcomings, including limited space. Remote, or a virtual data storage, can be an excellent choice in many situations, as it can be potentially unlimited and can also be set up to be performed automatically in the chose periods.
When it comes to online backup, also known as Cloud backup, it is important to note that reputable service would be select. Data is extremely valuable, and incorrectly stored data could be stolen or even sold to third-parties. Thus, when choosing a remote cloud service to backup your files, make sure it encrypts your information and protects it adequately from unauthorized intrusions. Additionally, it is also important to note that most Cloud storage services are not free (besides having a very limited amount of space) and can sometimes be relatively costly, depending on the chosen plan.
Besides Cloud storage, there are also other online mediums that could be used for backup purposes. For example, you can use your email to store some files, even though this method is not particularly efficient. Nevertheless, users who lose everything on their computers for one reason or another can still retrieve some important files if they were sent via email to somebody previously.


No backups were made? Use data recovery software
Data backups are extremely important, as they can help users to recover valuable files easily. Many regular consumers underestimate the importance of backups and rarely take the time and effort in order to ensure the safety of their records. Without backups, there are unable to restore their precious photos, work documents, image files, and other data that they find relevant.
Luckily, several methods sometimes could help you when trying to retrieve data. Its success highly depends on how you lost your files in the first place. In some cases, even ransomware-encrypted files could be restored by data recovery tools.
Data Recovery Pro
Data that is stored on your computer is stored in particular places of your hard drive. Once the command is given to delete a particular file, a certain amount of storage space is released to be used once again. However, due to performance reasons, these files are not deleted from the storage unit immediately.
The file contents remain on the system for as long as no new data is written on top of it. Hence, data recovery software is capable of retrieving working copies of data from storage devices. Due to this, the hard drive or another storage should not be filled with new data until lost files are completely recovered.[7] In other words, attempt to recover lost data straight away and do not wait until your hard drive gets overwritten with new information, deleting the working copies.
Data Recovery Pro is one of the leading email and file recovery solutions out there. It does not use too many computer resources, does not take a lot of space, and is very easy to understand. The app can help to recover videos, pictures, music, archives, documents, databases, and any other file types that were accidentally deleted or lost due to other reasons.
Other features of Data Recovery Pro include:
- Recovers data from external devices, such as USB sticks or iPods;
- Restores emails and their attachments that were deleted or lost;
- Restores files from formatted or partitioned drives;
- Guides through the file restoration process;
- Supports search by keyword function;
- Previews scan results such as videos or music files;
- Might sometimes be used to recover encrypted data.
ShadowExplorer
Since Windows Vista, Microsoft implemented a new, automated backup feature called Shadow Volume Copies, although they only work if System Restore was previously enabled. It allows files to be saved automatically in the background by your Windows operating system. The built-in tool to access these backups is not user-friendly at all, however, as they would have to recover each file individually. Absolutely inefficient!
In these situations, applications like ShadowExplorer are here to help you. It can access the shadow storage with ease in a user-friendly manner and allows you to browse previous versions of files without any restrictions. While this technology is no way an alternative to regular backups, it can still save your day in some cases.[8]
Shadow Copies and ShadowExplorer are in no way a replacement for regular backups! This is very important and can’t be stressed enough. A Shadow Copy is kept on the same disc as the original data. In case of a disc failure all data is lost, including the Shadow Copies. ShadowExplorer is a good addition to regular backups, but not a replacement.
If your files were encrypted by ransomware
Ransomware is one of the most devastating computer infections out there, as encryption algorithms such as RSA or AES are used to lock all the personal files on the system. During this process, a unique key is created and sent off to ransomware authors. To retrieve it, victims are asked to pay a ransom in Bitcoin. Unfortunately, in these kinds of situations, crooks are right, as it is impossible to decipher files when a secure encryption method is used.
Luckily, malware authors sometimes make mistakes that can be used by security researchers to provide users with a free decryption tool. At the same time, these occasions are relatively rare if comparing them to a total volume of new ransomware strains being released every day.[9] Despite this, malware families like CrySiS,[10]TeslaCrypt, Xorist, Jigsaw,[11]GlobeImposter, and many others, were successfully decrypted with the help of law enforcement agencies, cybersecurity companies, projects like No More Ransom, and independent security researchers. Unfortunately, new variants arise every day, and users keep falling victims to it.
What most people who get infected with ransomware don’t realize is that the removal of malware will not restore files to its previous (working) versions. Without backups, there is no secure way to recover data for free, unless security researchers release a working decryptor.
Thus, if you were infected with ransomware, chances of your files being recovered successfully depends on the malware strain. We highly suggest trying all the methods we listed above and also checking websites like nomoreransom.org for free decryption tools.
